talk
... • The code that manages physical (hardware) resources • Provides users (application programmers) with “logical” well-behaved environment • O.S. defines a set of logical resources (objects) and a set of well-defined operations on those objects (i.e., an interface to use those objects) • Provides mech ...
... • The code that manages physical (hardware) resources • Provides users (application programmers) with “logical” well-behaved environment • O.S. defines a set of logical resources (objects) and a set of well-defined operations on those objects (i.e., an interface to use those objects) • Provides mech ...
Chapter 2: Operating-System Structures
... – Easier to extend a microkernel – Easier to port the operating system to new architectures – More reliable (less code is running in kernel mode) – More secure • Detriments: – Performance overhead of user space to kernel space communication ...
... – Easier to extend a microkernel – Easier to port the operating system to new architectures – More reliable (less code is running in kernel mode) – More secure • Detriments: – Performance overhead of user space to kernel space communication ...
ARM Based Customizing an Operating System for the Single Board
... Cubieboard is a single-board computer, made in china. The Cubieboard team managed to run an Apache Hadoop Computer cluster using the Lubuntu GNU/Linux distribution. It's a new PCB model adopted with Allwinner A20 main chip, just like Cubieboard2. But it is enhanced with some features, such as 2GB me ...
... Cubieboard is a single-board computer, made in china. The Cubieboard team managed to run an Apache Hadoop Computer cluster using the Lubuntu GNU/Linux distribution. It's a new PCB model adopted with Allwinner A20 main chip, just like Cubieboard2. But it is enhanced with some features, such as 2GB me ...
The advent of trusted* computer operating systems
... In the early 1970s the Air Force/Electronics Systems Division (ESD) conducted in-depth analyses of the requirements for trusted systems. 5 The concepts which emerged from their efforts today are the basis for most major trusted computer system developments. The basic concept is a Reference Monitor o ...
... In the early 1970s the Air Force/Electronics Systems Division (ESD) conducted in-depth analyses of the requirements for trusted systems. 5 The concepts which emerged from their efforts today are the basis for most major trusted computer system developments. The basic concept is a Reference Monitor o ...
Server Security Policy
... During initial installation, ensure that file systems with user-writeable directories such as /home, /tmp, /var/tmp are mounted on separate partitions. Ensure that third party applications should be installed on separate file systems under /opt. ...
... During initial installation, ensure that file systems with user-writeable directories such as /home, /tmp, /var/tmp are mounted on separate partitions. Ensure that third party applications should be installed on separate file systems under /opt. ...
Operating Systems I
... “The Power Behind the Scenes” A control program the manages all the resources of the computer on which it runs. ...
... “The Power Behind the Scenes” A control program the manages all the resources of the computer on which it runs. ...
Trusted Operating Systems
... • Set of subjects and another set of objects • Each subject s has a fixed security clearance C(s) • Each object o has a fixed security class C(o) ...
... • Set of subjects and another set of objects • Each subject s has a fixed security clearance C(s) • Each object o has a fixed security class C(o) ...
Security - Computer Science Department
... – Your system may be secure, then the environment changes ...
... – Your system may be secure, then the environment changes ...
Principles of Operating System
... • The second is also called a kernel; this is the definition we will use • The kernel itself is an executable; on Linux, this executable is located at /boot/vmlinuz ...
... • The second is also called a kernel; this is the definition we will use • The kernel itself is an executable; on Linux, this executable is located at /boot/vmlinuz ...
FEARLESS - Cyber Security Research and Education Institute
... Data Privacy, Secure Web Services, Secure Cloud Computing, Hardware Security, CISSP Modules ...
... Data Privacy, Secure Web Services, Secure Cloud Computing, Hardware Security, CISSP Modules ...
슬라이드 1
... the GNU project, Linux was ready for the actual showdown. It was licensed under GNU General Public License, thus ensuring that the source codes will be free for all to copy, study and to change. Students and computer programmers grabbed it. Soon, commercial vendors moved in. Linux itself was, and is ...
... the GNU project, Linux was ready for the actual showdown. It was licensed under GNU General Public License, thus ensuring that the source codes will be free for all to copy, study and to change. Students and computer programmers grabbed it. Soon, commercial vendors moved in. Linux itself was, and is ...
Web Application Security Vulnerabilities Yen
... the latest patches to these products. Review all code that accepts input from users via the HTTP request and ensure that it provides appropriate size checking on all such ...
... the latest patches to these products. Review all code that accepts input from users via the HTTP request and ensure that it provides appropriate size checking on all such ...
operating systems
... Refers to a computer system's ability to support more than one process (program) at the same time. Multiprocessing operating systems enable several programs to run concurrently. UNIX is one of the most widely used multiprocessing systems. Refers to the utilization of multiple CPUs in a single comput ...
... Refers to a computer system's ability to support more than one process (program) at the same time. Multiprocessing operating systems enable several programs to run concurrently. UNIX is one of the most widely used multiprocessing systems. Refers to the utilization of multiple CPUs in a single comput ...
The Operating System
... Coordinates all software activity within a computer system: The master control program that runs the computer. The first program loaded when the computer is turned on, its main part, the "kernel," resides in memory at all times. The operating system sets the standards for all application programs th ...
... Coordinates all software activity within a computer system: The master control program that runs the computer. The first program loaded when the computer is turned on, its main part, the "kernel," resides in memory at all times. The operating system sets the standards for all application programs th ...
Systems II
... Protection refers to a mechanism for controlling the access of programs, processes or users to the resources defined by a computer system The processes in an operating system must be protected from one another’s activities Various mechanisms can be used to ensure that the files, memory segments, ...
... Protection refers to a mechanism for controlling the access of programs, processes or users to the resources defined by a computer system The processes in an operating system must be protected from one another’s activities Various mechanisms can be used to ensure that the files, memory segments, ...
Securing Distribution Automation
... for Smart Grid security. While there exist many enterprise-level products for password management, to our knowledge there are none that have been designed to meet the requirements of distributed field devices. Typical enterprise password management systems are designed to support devices such as rou ...
... for Smart Grid security. While there exist many enterprise-level products for password management, to our knowledge there are none that have been designed to meet the requirements of distributed field devices. Typical enterprise password management systems are designed to support devices such as rou ...
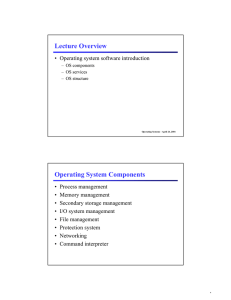
Lecture Overview Operating System Components
... • The virtual-machine concept provides complete protection of system resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. • A virtual-machine system is a perfect vehicle for operating-systems research and d ...
... • The virtual-machine concept provides complete protection of system resources since each virtual machine is isolated from all other virtual machines. This isolation, however, permits no direct sharing of resources. • A virtual-machine system is a perfect vehicle for operating-systems research and d ...
Avaya™ G700 Media Gateway Security - Issue 1.0
... their respective owners. The information provided in this paper is subject to change without notice. The configurations, technical data, and recommendations provided in this paper are believed to be accurate and dependable, but are presented without express or implied warranty. Users are responsible ...
... their respective owners. The information provided in this paper is subject to change without notice. The configurations, technical data, and recommendations provided in this paper are believed to be accurate and dependable, but are presented without express or implied warranty. Users are responsible ...
Slides
... – Easier to extend a microkernel – Easier to port the operating system to new architectures – More reliable (less code is running in kernel mode) – More secure • Detriments: – Performance overhead of user space to kernel space communication ...
... – Easier to extend a microkernel – Easier to port the operating system to new architectures – More reliable (less code is running in kernel mode) – More secure • Detriments: – Performance overhead of user space to kernel space communication ...
windows and linux operating systems from a security perspective
... An operating system, also called OS,is a collection of system programs, tools, and utilities that manage computer hardware resources and offer common services for client application software [1]. The operating system is the first program to execute upon booting a computer and is thus considered the ...
... An operating system, also called OS,is a collection of system programs, tools, and utilities that manage computer hardware resources and offer common services for client application software [1]. The operating system is the first program to execute upon booting a computer and is thus considered the ...
Hassan Al-Makso`s presentation on Making OS Reliable and Secure
... 55 percent of the nonfatal ones Drivers can execute privileged instructions they should not Execute The Nooks team had to write large numbers of wrappers manually, and they could contain faults ...
... 55 percent of the nonfatal ones Drivers can execute privileged instructions they should not Execute The Nooks team had to write large numbers of wrappers manually, and they could contain faults ...
this list describes some of these commonly used basic tenets
... Most server operating systems have some form of auto-configuration utility available. Bastille is available for Linux, Windows 2003 has the Server Configuration Wizard. But beyond using canned tools, you should research hardening your operating system. Make sure you are not running services that yo ...
... Most server operating systems have some form of auto-configuration utility available. Bastille is available for Linux, Windows 2003 has the Server Configuration Wizard. But beyond using canned tools, you should research hardening your operating system. Make sure you are not running services that yo ...
PPT - ICGEB
... Until the mid 1990’s the only workstation capable for bioinformatics of visualizing protein structure data in real time were SGI and Sun Unix Workstation Command line richness with a graphical user interface – provides options and possibilities Many pre-built software prepackaged with various Linux ...
... Until the mid 1990’s the only workstation capable for bioinformatics of visualizing protein structure data in real time were SGI and Sun Unix Workstation Command line richness with a graphical user interface – provides options and possibilities Many pre-built software prepackaged with various Linux ...
Unit-5 - Ipemgzb.ac.in
... the major design goal of UNIX compatibility. Its history has been one of collaboration by many users from all around the world, corresponding almost exclusively over the Internet. It has been designed to run efficiently and reliably on common PC hardware, but also runs on a variety of other platform ...
... the major design goal of UNIX compatibility. Its history has been one of collaboration by many users from all around the world, corresponding almost exclusively over the Internet. It has been designed to run efficiently and reliably on common PC hardware, but also runs on a variety of other platform ...
Security Requirements
... program. Once the valid program runs the hidden code starts and may damaged or delete files remember “Melissa” ...
... program. Once the valid program runs the hidden code starts and may damaged or delete files remember “Melissa” ...