lec01
... Approached Bill Gates to see if he can build one Gates approached Seattle computer products, bought 86DOS and created MS-DOS Goal: finish quickly and run existing CP/M software OS becomes subroutine library and command executive ...
... Approached Bill Gates to see if he can build one Gates approached Seattle computer products, bought 86DOS and created MS-DOS Goal: finish quickly and run existing CP/M software OS becomes subroutine library and command executive ...
Operating Systems Overview - Physics, Computer Science and
... z A program that controls the execution of application programs z An interface between the user and hardware z Masks the details of the hardware ...
... z A program that controls the execution of application programs z An interface between the user and hardware z Masks the details of the hardware ...
CC4201519521
... techniques such as network sockets, file system and shared files for inter-process communication. But android operating system also provides new mechanism for IPC such as Binder, Services, Intents and ContentProviders. All these mechanism allows developers to verify the identity of application and a ...
... techniques such as network sockets, file system and shared files for inter-process communication. But android operating system also provides new mechanism for IPC such as Binder, Services, Intents and ContentProviders. All these mechanism allows developers to verify the identity of application and a ...
XML Security Standards — Overview for the Non - Events
... Physical order of elements determines processing order of signatures and encryptions Signed and encrypted data can appear anywhere in envelope A toolkit, not a protocol ...
... Physical order of elements determines processing order of signatures and encryptions Signed and encrypted data can appear anywhere in envelope A toolkit, not a protocol ...
CS 4410/4411 Systems Programming and Operating Systems
... • Multiprogramming systems increased utilization – Developed in the 1960s – Keeps multiple runnable jobs loaded in memory – Overlaps I/O processing of a job with computation of another – Benefits from I/O devices that can operate asynchronously – Requires the use of interrupts and DMA – Optim ...
... • Multiprogramming systems increased utilization – Developed in the 1960s – Keeps multiple runnable jobs loaded in memory – Overlaps I/O processing of a job with computation of another – Benefits from I/O devices that can operate asynchronously – Requires the use of interrupts and DMA – Optim ...
CS204 Operating Systems
... 2. To impart the key design issues of an operating system Syllabus Basic concepts of Operating System, its structure, Process management, inter-process communication, process synchronization, CPU Scheduling, deadlocks, Memory Management, swapping, segmentation, paging, Storage Management - disk sche ...
... 2. To impart the key design issues of an operating system Syllabus Basic concepts of Operating System, its structure, Process management, inter-process communication, process synchronization, CPU Scheduling, deadlocks, Memory Management, swapping, segmentation, paging, Storage Management - disk sche ...
OSI Security Architecture
... means for protecting personal privacy and proprietary information. A loss of confidentiality is the unauthorized disclosure of information. • Integrity (covers both data and system integrity): Guarding against improper information modification or destruction, and includes ensuring information non-re ...
... means for protecting personal privacy and proprietary information. A loss of confidentiality is the unauthorized disclosure of information. • Integrity (covers both data and system integrity): Guarding against improper information modification or destruction, and includes ensuring information non-re ...
OPERATING SYSTEM
... some task such as writing a letter. In this instance there is one keyboard and one monitor that you interact with. Operating systems such as Windows 95, Windows NT Workstation and Windows 2000 professional are essentially single user operating systems. They provide you the capability to perform ta ...
... some task such as writing a letter. In this instance there is one keyboard and one monitor that you interact with. Operating systems such as Windows 95, Windows NT Workstation and Windows 2000 professional are essentially single user operating systems. They provide you the capability to perform ta ...
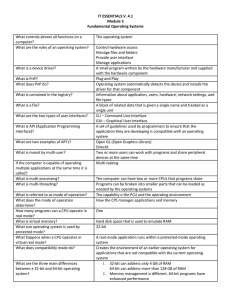
IT ESSENTIALS V. 4.1 Module 5 Fundamental Operating Systems
... Shares files and folders on a small network with limited security 1. Microsoft Windows 2. Apple Mac OS 3. Unix/Linux Unix Linus Torvalds The source code can be distributed and changed by anyone as a free download or from other developers 1. Supports multiple users 2. Runs multi-user applications 3. ...
... Shares files and folders on a small network with limited security 1. Microsoft Windows 2. Apple Mac OS 3. Unix/Linux Unix Linus Torvalds The source code can be distributed and changed by anyone as a free download or from other developers 1. Supports multiple users 2. Runs multi-user applications 3. ...
Enhanced Guide to Managing & Maintaining Your PC, 3e
... primary memory (RAM) and secondary storage? How many and what kinds of applications are written to work with the OS? How powerful must the hardware be to make efficient use of the OS? How does the OS perform in a network? ...
... primary memory (RAM) and secondary storage? How many and what kinds of applications are written to work with the OS? How powerful must the hardware be to make efficient use of the OS? How does the OS perform in a network? ...
Self-Managing Techniques for Shared Server Resources
... File system, device drivers, network stack Applications interact via message-passing ...
... File system, device drivers, network stack Applications interact via message-passing ...
system call
... The program that receives, interprets and executes the next command action/statement may be: command-line interpreter or shell - to process typed commands Graphical User Interface (Windows, Icons, Menus, Pointers) based system - to process control actions ...
... The program that receives, interprets and executes the next command action/statement may be: command-line interpreter or shell - to process typed commands Graphical User Interface (Windows, Icons, Menus, Pointers) based system - to process control actions ...
Information Assurance Presentation
... Number Five: Fail to realize how much money their information and organizational reputations are worth. Number Four: Rely primarily on a firewall. Number Three: Fail to deal with the operational aspects of security: make a few fixes and then not allow the follow through necessary to ensure the ...
... Number Five: Fail to realize how much money their information and organizational reputations are worth. Number Four: Rely primarily on a firewall. Number Three: Fail to deal with the operational aspects of security: make a few fixes and then not allow the follow through necessary to ensure the ...
OPERATING SYSTEMS UNIT I Syllabus: Operating Systems
... 2. Explain how protection is provided for the hardware resources by the operating system. 3. What are the system components of an operating system and explain them? 4. What are the various process scheduling concepts? 5. List five services provided by an operating system. Explain how each provides c ...
... 2. Explain how protection is provided for the hardware resources by the operating system. 3. What are the system components of an operating system and explain them? 4. What are the various process scheduling concepts? 5. List five services provided by an operating system. Explain how each provides c ...
Sai Uday Kiran Ravi`s presentation on Application Security on
... point, Overshadow also maintains its own protected table of the application’s signal handlers. Problems related to the OS managing process identity by using an independent process identity in conjunction with the secure ...
... point, Overshadow also maintains its own protected table of the application’s signal handlers. Problems related to the OS managing process identity by using an independent process identity in conjunction with the secure ...
system call - efreidoc.fr
... The program that receives, interprets and executes the next command action/statement may be: command-line interpreter or shell - to process typed commands Graphical User Interface (Windows, Icons, Menus, Pointers) based system - to process control actions ...
... The program that receives, interprets and executes the next command action/statement may be: command-line interpreter or shell - to process typed commands Graphical User Interface (Windows, Icons, Menus, Pointers) based system - to process control actions ...
Dilma M. da Silva IBM TJ Watson Research Center - IC
... with no leaking of information between clients Labels and Event Processes in the Asbestos Operating System (UCLA, MIT, NYU) Enforce isolation between kernel modules (helps detect bugs, limit their damage) Mondrix: Memory Isolation for Linux using Modriaan Memory Protection (UT-Austin, MIT, Purdue) ...
... with no leaking of information between clients Labels and Event Processes in the Asbestos Operating System (UCLA, MIT, NYU) Enforce isolation between kernel modules (helps detect bugs, limit their damage) Mondrix: Memory Isolation for Linux using Modriaan Memory Protection (UT-Austin, MIT, Purdue) ...
WSO2006-overview-con..
... with no leaking of information between clients Labels and Event Processes in the Asbestos Operating System (UCLA, MIT, NYU) Enforce isolation between kernel modules (helps detect bugs, limit their damage) Mondrix: Memory Isolation for Linux using Modriaan Memory Protection (UT-Austin, MIT, Purdue) ...
... with no leaking of information between clients Labels and Event Processes in the Asbestos Operating System (UCLA, MIT, NYU) Enforce isolation between kernel modules (helps detect bugs, limit their damage) Mondrix: Memory Isolation for Linux using Modriaan Memory Protection (UT-Austin, MIT, Purdue) ...
Artificial Intelligence for Cyber Security (AICS)
... that can be used to induce more secure behavior. Another promising approach is to design automated tools that can perform the task of the human in the loop. This approach mitigates security issues arising from sub-optimal security decision taken by humans. Further, automated tools can be formally sp ...
... that can be used to induce more secure behavior. Another promising approach is to design automated tools that can perform the task of the human in the loop. This approach mitigates security issues arising from sub-optimal security decision taken by humans. Further, automated tools can be formally sp ...
Open Source Software
... • The primary difference between Linux and many other popular contemporary operating systems is that the Linux kernel and other components are free and open source software. Linux is not the only such operating system, although it is the best-known and most widely used. • As an operating system unde ...
... • The primary difference between Linux and many other popular contemporary operating systems is that the Linux kernel and other components are free and open source software. Linux is not the only such operating system, although it is the best-known and most widely used. • As an operating system unde ...
Good practice guide: General advice on securing operating
... “Memory protection is a system that prevents one process from corrupting the memory of another process running on the same computer at the same time”. [1] Many attacks, such as buffer overflow attacks, are designed to bypass this protection. The attacker may attempt to get a vulnerable piece of softw ...
... “Memory protection is a system that prevents one process from corrupting the memory of another process running on the same computer at the same time”. [1] Many attacks, such as buffer overflow attacks, are designed to bypass this protection. The attacker may attempt to get a vulnerable piece of softw ...
File
... • FEATURES OF MAC OS • WINDOWS OS • FEATURES OF WINDOWS OS • LINUX OS • FEATURES OF LINUX OS ...
... • FEATURES OF MAC OS • WINDOWS OS • FEATURES OF WINDOWS OS • LINUX OS • FEATURES OF LINUX OS ...
Security+ Guide to Network Security Fundamentals
... Configure DHCP server to force stations with new MAC addresses on the network to register with the DHCP server Implement latest software and patches ...
... Configure DHCP server to force stations with new MAC addresses on the network to register with the DHCP server Implement latest software and patches ...