PDF
... A tagged TLB tags each entry with an address space label, avoiding flushes A Pentium CPU can emulate a tagged TLB for small address spaces ...
... A tagged TLB tags each entry with an address space label, avoiding flushes A Pentium CPU can emulate a tagged TLB for small address spaces ...
Server Installation - Information Technology Gate
... you are using hardware designed for a server from major manufacturers IDE drives are always compatible Make sure that you have the latest drivers for SCSI and RAID controllers With video adapters and NICs, it is best to use ones from major vendors ...
... you are using hardware designed for a server from major manufacturers IDE drives are always compatible Make sure that you have the latest drivers for SCSI and RAID controllers With video adapters and NICs, it is best to use ones from major vendors ...
PPT - CS
... • The client workstation where the user is trying to log in sends the user name U to the server. • The Kerberos server does the following: – It looks up the user’s password p, and uses a one-way function to create an encryption key Kp from it. – It generates a new session key Ks for this login sessi ...
... • The client workstation where the user is trying to log in sends the user name U to the server. • The Kerberos server does the following: – It looks up the user’s password p, and uses a one-way function to create an encryption key Kp from it. – It generates a new session key Ks for this login sessi ...
Slide 1
... – Hides the messy details which must be performed – Presents user with a virtual machine, easier to use ...
... – Hides the messy details which must be performed – Presents user with a virtual machine, easier to use ...
Intro to Operating Systems
... Fourth Generation (1980- present) Personal Computers Up to this point all operating systems were ...
... Fourth Generation (1980- present) Personal Computers Up to this point all operating systems were ...
Data Security Manager
... To assist in taking timely action resulting from any risk assessment recommendations. This may involve liaison with other department such as estates or planning etc. It is essential to keep the Chief Information Officer informed if there are any issues of non-compliance. ...
... To assist in taking timely action resulting from any risk assessment recommendations. This may involve liaison with other department such as estates or planning etc. It is essential to keep the Chief Information Officer informed if there are any issues of non-compliance. ...
OS API
... A file handle is a small integer, valid only within a single process, to operate on the device or file Pathname: a name in the file system. In unix, devices are put under /dev. E.g. /dev/ttya is the first serial port, /dev/sda the first SCSI drive Flags: read only, read/write, append etc… Mode may b ...
... A file handle is a small integer, valid only within a single process, to operate on the device or file Pathname: a name in the file system. In unix, devices are put under /dev. E.g. /dev/ttya is the first serial port, /dev/sda the first SCSI drive Flags: read only, read/write, append etc… Mode may b ...
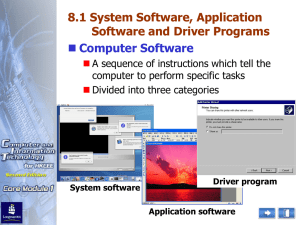
System Software, Application Software and Driver Programs
... Network operating system Run on network servers that provide Centralized storage facilities Peripheral devices sharing services Communications capabilities for computers ...
... Network operating system Run on network servers that provide Centralized storage facilities Peripheral devices sharing services Communications capabilities for computers ...
Linux Intro Comparison
... Supports virtual consoles. Supports various file systems for storing data. Provides complete implementation of TCP/IP networking software. Include device drivers for many Ethernet cards. ...
... Supports virtual consoles. Supports various file systems for storing data. Provides complete implementation of TCP/IP networking software. Include device drivers for many Ethernet cards. ...
Monitoring and Auditing AIS - McGraw
... • Compliance tests of IT general and application controls • Operating system and network vulnerability assessments • Application security testing and source code security scans • Penetration Testing Two approaches: • Auditing around the computer (the black-box approach) • Auditing through the comput ...
... • Compliance tests of IT general and application controls • Operating system and network vulnerability assessments • Application security testing and source code security scans • Penetration Testing Two approaches: • Auditing around the computer (the black-box approach) • Auditing through the comput ...
Essentials of Security
... If an attacker can persuade you to run his program on your computer, it is not your computer anymore ...
... If an attacker can persuade you to run his program on your computer, it is not your computer anymore ...
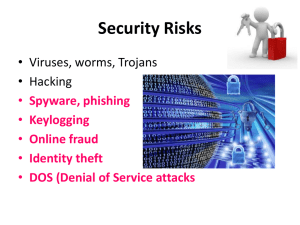
Security Risks - Bannerman High School
... • A firewall is a system designed to check the data coming into or going out of a network. • It : – only allows access to authorised users and applications – prevents unauthorised access to a network. ...
... • A firewall is a system designed to check the data coming into or going out of a network. • It : – only allows access to authorised users and applications – prevents unauthorised access to a network. ...
CISSP Guide to Security Essentials, Ch4
... Information Flow Security Model • Based upon flow of information rather than on access controls • Data objects are assigned to a class or level of security • Flow of objects are controlled by security policy that specifies where objects of various levels are permitted to flow ...
... Information Flow Security Model • Based upon flow of information rather than on access controls • Data objects are assigned to a class or level of security • Flow of objects are controlled by security policy that specifies where objects of various levels are permitted to flow ...
DOC Security Model for the Next-Generation Secure Computing Base
... software, and operating system levels. Increasing existing security measures, such as adding more firewalls and creating password protection schemes, can slow data delivery and frustrate users. Using only software-based security measures to protect existing computers is starting to reach the point o ...
... software, and operating system levels. Increasing existing security measures, such as adding more firewalls and creating password protection schemes, can slow data delivery and frustrate users. Using only software-based security measures to protect existing computers is starting to reach the point o ...
ppt
... How can the kernel be eliminated from the call path on SMMPs with user-level threads? To a thread URPC is synchronous, but to the thread library it is asynchronous … explain. Why do kernel thread switches have long term cache and TLB effects that user thread switches do not? ...
... How can the kernel be eliminated from the call path on SMMPs with user-level threads? To a thread URPC is synchronous, but to the thread library it is asynchronous … explain. Why do kernel thread switches have long term cache and TLB effects that user thread switches do not? ...
SE 4C03 Winter 2004
... There is no free lunch. One must sacrifice security for convenience and vise versa. Windows operating systems are most likely to be attacked because of its vulnerability due to its complexity. It is made complicated because of the convenience windows wants to provide, however, that became its downfa ...
... There is no free lunch. One must sacrifice security for convenience and vise versa. Windows operating systems are most likely to be attacked because of its vulnerability due to its complexity. It is made complicated because of the convenience windows wants to provide, however, that became its downfa ...
Applied Cybersecurity
... In today’s world, organizations must be prepared to defend against threats in cyberspace. Decision makers must be familiar with the basic principles and best practices of cybersecurity to best protect their enterprises. In this course, experts from academia, the military, and industry share their kn ...
... In today’s world, organizations must be prepared to defend against threats in cyberspace. Decision makers must be familiar with the basic principles and best practices of cybersecurity to best protect their enterprises. In this course, experts from academia, the military, and industry share their kn ...
Operating Systems History
... has the basic routines of an OS. • Some OS use the microkernel concept, this have the function to coordinate to the other parts of an OS such as : I/O Devices, Process, Memory and File Systems. • The structure of and OS could be different but in most of the time are very similar because some OS use ...
... has the basic routines of an OS. • Some OS use the microkernel concept, this have the function to coordinate to the other parts of an OS such as : I/O Devices, Process, Memory and File Systems. • The structure of and OS could be different but in most of the time are very similar because some OS use ...
Cyber Security Education Consortium 2008 Retreat
... Systems by terrorists & foreign governments • Evidence that nation-states have been taking remote control of Control Systems • Denial by some companies that there is a problem • Some companies are now starting to see the need and address the issues ...
... Systems by terrorists & foreign governments • Evidence that nation-states have been taking remote control of Control Systems • Denial by some companies that there is a problem • Some companies are now starting to see the need and address the issues ...
Security+ Guide to Network Security Fundamentals
... Vulnerabilities associated with common services installed on computer systems (WWW services, FTP, DNS) and best practices in protecting against threats to these services Maintenance and upgrade of computer ...
... Vulnerabilities associated with common services installed on computer systems (WWW services, FTP, DNS) and best practices in protecting against threats to these services Maintenance and upgrade of computer ...
ECSP – EC-Council Certified Secure Programmer
... The course prepares candidates for the ECSP-Java (312-93) and ECSP.NET (312-94) exams. ...
... The course prepares candidates for the ECSP-Java (312-93) and ECSP.NET (312-94) exams. ...
Protection in General-Purpose Operating Systems
... Use of Passwords Passwords are mutually agreed-upon code words, assumed to be known only to the user and the system. The use of of passwords is fairly straightforward. A user enters some piece of identification, such as a name or an assigned user ID, if the identification matches that on file for t ...
... Use of Passwords Passwords are mutually agreed-upon code words, assumed to be known only to the user and the system. The use of of passwords is fairly straightforward. A user enters some piece of identification, such as a name or an assigned user ID, if the identification matches that on file for t ...
The Advanced Penetration Testing Boot Camp
... Ability to support any host based, network based, inline or span port security technology that the customer requires to be installed into their cloud environment. Support of IPSEC VPN’s ...
... Ability to support any host based, network based, inline or span port security technology that the customer requires to be installed into their cloud environment. Support of IPSEC VPN’s ...