View File
... running concurrently, resources must be allocated to each of them • Many types of resources - Some (such as CPU cycles, main memory, and file storage) may have special allocation code, others (such as I/O devices) may have general request and release code. ...
... running concurrently, resources must be allocated to each of them • Many types of resources - Some (such as CPU cycles, main memory, and file storage) may have special allocation code, others (such as I/O devices) may have general request and release code. ...
Chapter 32
... changed each hop – Mutable fields are those IP headers that get changed in transit • We don’t want these slight changes to cause authentication errors • So IPsec will only authenticate the immutable fields ...
... changed each hop – Mutable fields are those IP headers that get changed in transit • We don’t want these slight changes to cause authentication errors • So IPsec will only authenticate the immutable fields ...
Document
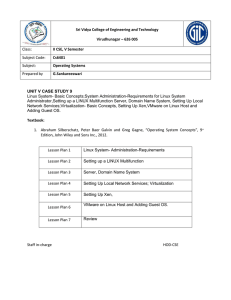
... This course is devoted to to provides a clear description of the main concepts of operating systems and algorithms. This course will introduce a wide range of topics that is not tied to one specific type of operating system. Particular emphasis will be given to the following topics: Operating System ...
... This course is devoted to to provides a clear description of the main concepts of operating systems and algorithms. This course will introduce a wide range of topics that is not tied to one specific type of operating system. Particular emphasis will be given to the following topics: Operating System ...
chap03
... you are using hardware designed for a server from major manufacturers IDE drives are always compatible Make sure that you have the latest drivers for SCSI and RAID controllers With video adapters and NICs, it is best to use ones from major vendors ...
... you are using hardware designed for a server from major manufacturers IDE drives are always compatible Make sure that you have the latest drivers for SCSI and RAID controllers With video adapters and NICs, it is best to use ones from major vendors ...
Introduction - Virginia Tech
... Unix Operating System (process/memory management, file system, I/O) ...
... Unix Operating System (process/memory management, file system, I/O) ...
lecture2
... Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS Simplest: pass the parameters in registers In some cases, may be more parameters than registers Parameters stored in a block, or table, in memory, and address of block p ...
... Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS Simplest: pass the parameters in registers In some cases, may be more parameters than registers Parameters stored in a block, or table, in memory, and address of block p ...
L03 - UMBC
... time while you are using the system. The / (pronounced “slash”) is the root directory in Linux. Files within the same directory must be given unique ...
... time while you are using the system. The / (pronounced “slash”) is the root directory in Linux. Files within the same directory must be given unique ...
MASTER - HubSpot
... outsourcing administration of information assets , networks, or data you must retain legal control of proprietary information and use limited “need to know” access to such assets, networks or data; and (xiii) reference the protection of Customer Information and compliance with the Security Standards ...
... outsourcing administration of information assets , networks, or data you must retain legal control of proprietary information and use limited “need to know” access to such assets, networks or data; and (xiii) reference the protection of Customer Information and compliance with the Security Standards ...
Slide 1
... • The user is legally barred from making copies of the licensed SW. Generally, the license is for the personal use only • Most SW in use in the world is of this type • Examples: Windows, Mac OS, MS Word, Adobe Photoshop, Norton Antivirus ...
... • The user is legally barred from making copies of the licensed SW. Generally, the license is for the personal use only • Most SW in use in the world is of this type • Examples: Windows, Mac OS, MS Word, Adobe Photoshop, Norton Antivirus ...
Microsoft & Linux What Is an Operating System?
... computers along with a common printer server and file server for archival storage, all tied together by a local network. Generally speaking, such a system will have most of the following characteristics that distinguish it from a distributed system: • Each computer has its own private operating syst ...
... computers along with a common printer server and file server for archival storage, all tied together by a local network. Generally speaking, such a system will have most of the following characteristics that distinguish it from a distributed system: • Each computer has its own private operating syst ...
Lecture_1 - bridges to computing
... allows a programmer to write a program that will run on different computers, even if the hardware (memory, CPU, etc.) is different on the two machines. Applications continue to run when hardware upgrades and updates occur because the operating system -- not the application -- is charged with manag ...
... allows a programmer to write a program that will run on different computers, even if the hardware (memory, CPU, etc.) is different on the two machines. Applications continue to run when hardware upgrades and updates occur because the operating system -- not the application -- is charged with manag ...
For clients requiring security in high
... experience, Raven Advisory conducts comprehensive vulnerability assessments of any threat to their clients. With surveillance technology and investigative techniques, Raven accurately identifies potential threats before they pose a problem. Raven will provide clients with elements to attempt penetra ...
... experience, Raven Advisory conducts comprehensive vulnerability assessments of any threat to their clients. With surveillance technology and investigative techniques, Raven accurately identifies potential threats before they pose a problem. Raven will provide clients with elements to attempt penetra ...
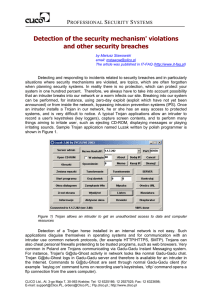
Detection of the security mechanism` violations and other
... Vast majority of IPS and intrusion detection systems (IDS) available in the market have little features allowing detection of security breaches and in particular situations where protections were broken. Usually their functionality in this respect is limited to recognizing known network attacks (exp ...
... Vast majority of IPS and intrusion detection systems (IDS) available in the market have little features allowing detection of security breaches and in particular situations where protections were broken. Usually their functionality in this respect is limited to recognizing known network attacks (exp ...
Linux Operations and Administration
... – Firewall for protecting network resources from users outside the network Linux Operations and Administration ...
... – Firewall for protecting network resources from users outside the network Linux Operations and Administration ...
System Software and Operating Systems
... computing purposes, you may need an operating system which can coordinate a number of CPU’s (processors) asymmetric: different tasks assigned to different CPU’s each with its own memory symmetric: tasks and memory shared equally among CPU’s ...
... computing purposes, you may need an operating system which can coordinate a number of CPU’s (processors) asymmetric: different tasks assigned to different CPU’s each with its own memory symmetric: tasks and memory shared equally among CPU’s ...
The Java Virtual Shell and Kernel
... Operating system shells generally fall into one of two categories: command line and graphical. Command line shells provide a command line interface (CLI) to the operating system, while graphical shells provide a graphical user interface (GUI). In either category the primary purpose of the shell is ...
... Operating system shells generally fall into one of two categories: command line and graphical. Command line shells provide a command line interface (CLI) to the operating system, while graphical shells provide a graphical user interface (GUI). In either category the primary purpose of the shell is ...
Operating Systems: Principles and Practice, Introduction
... – Multiprogramming: run multiple programs at same time – Interactive performance: try to complete ...
... – Multiprogramming: run multiple programs at same time – Interactive performance: try to complete ...
General IT Auditing Techniques
... Nonintrusive attack: The intent to gain information about an organization’s network in preparation for a more intrusive attack at a later time Examples of nonintrusive attacks include: Information reconnaissance Port scanning ...
... Nonintrusive attack: The intent to gain information about an organization’s network in preparation for a more intrusive attack at a later time Examples of nonintrusive attacks include: Information reconnaissance Port scanning ...
System Software and Operating Systems
... computing purposes, you may need an operating system which can coordinate a number of CPU’s (processors) asymmetric: different tasks assigned to different CPU’s each with its own memory symmetric: tasks and memory shared equally among CPU’s ...
... computing purposes, you may need an operating system which can coordinate a number of CPU’s (processors) asymmetric: different tasks assigned to different CPU’s each with its own memory symmetric: tasks and memory shared equally among CPU’s ...
Document
... The Future: How should it be? Computing will be transformed. It's not just that our problems are big, they are big and obvious. It's not just that the solutions are simple, they are simple and right under our noses. It's not just that hardware is more advanced than software; the last big operating- ...
... The Future: How should it be? Computing will be transformed. It's not just that our problems are big, they are big and obvious. It's not just that the solutions are simple, they are simple and right under our noses. It's not just that hardware is more advanced than software; the last big operating- ...
Department of Computer Science and Engineering
... free and open-source software development and distribution. The defining component of Linux is the Linux kernel,[9] an operating system kernel first released on 5 October 1991 by Linus Torvalds.[10][11] The Free Software Foundation uses the name GNU/Linux to describe the operating system, which has ...
... free and open-source software development and distribution. The defining component of Linux is the Linux kernel,[9] an operating system kernel first released on 5 October 1991 by Linus Torvalds.[10][11] The Free Software Foundation uses the name GNU/Linux to describe the operating system, which has ...
A threat can be any person, object, or event that, if realized, could
... An attacker can also impersonate a user. By monitoring the frame transmissions, a hacker can program a rogue radio NIC to mimic a valid one. In this way, the rogue radio NIC steals the ongoing session for which the valid user had logged into. ...
... An attacker can also impersonate a user. By monitoring the frame transmissions, a hacker can program a rogue radio NIC to mimic a valid one. In this way, the rogue radio NIC steals the ongoing session for which the valid user had logged into. ...
Introduction
... Pages of address space distributed among four machines Situation after CPU 1 references page 10 Situation if page 10 is read only and replication is used ...
... Pages of address space distributed among four machines Situation after CPU 1 references page 10 Situation if page 10 is read only and replication is used ...
MINIX 3: status report and current research
... of the system on the fly, without a reboot. We believe it will be possible to replace, for example, the main file system module with a later version while the system is running, without a reboot, and without affecting running processes. While Ksplice [5] can make small patches to Linux on the fly, i ...
... of the system on the fly, without a reboot. We believe it will be possible to replace, for example, the main file system module with a later version while the system is running, without a reboot, and without affecting running processes. While Ksplice [5] can make small patches to Linux on the fly, i ...