Operating systems. History. Function. Organization. Software
... • Process: The activity of executing a program (NOT THE SAME THING AS A PROGRAM!!!) – Program – static set of directions (instructions) – Process – dynamic entity whose properties change as time progresses. It is an instance in execution of a ...
... • Process: The activity of executing a program (NOT THE SAME THING AS A PROGRAM!!!) – Program – static set of directions (instructions) – Process – dynamic entity whose properties change as time progresses. It is an instance in execution of a ...
Document
... • Process: The activity of executing a program (NOT THE SAME THING AS A PROGRAM!!!) – Program – static set of directions (instructions) – Process – dynamic entity whose properties change as time progresses. It is an instance in execution of a ...
... • Process: The activity of executing a program (NOT THE SAME THING AS A PROGRAM!!!) – Program – static set of directions (instructions) – Process – dynamic entity whose properties change as time progresses. It is an instance in execution of a ...
Ch10 - Protection Mechanism
... – Then periodically samples network activity, based on statistical methods, and compares the samples to the baseline ...
... – Then periodically samples network activity, based on statistical methods, and compares the samples to the baseline ...
Computer replacement
... Update Intervals for FACTS System Components The life-expectancy for a FACTS System is 25 to 30 years, and sometimes more. To achieve this lifecycle we need to consider the update intervals for the system components, and how it varies from many years for I/O system to a magnitude of months for some ...
... Update Intervals for FACTS System Components The life-expectancy for a FACTS System is 25 to 30 years, and sometimes more. To achieve this lifecycle we need to consider the update intervals for the system components, and how it varies from many years for I/O system to a magnitude of months for some ...
Presentation
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
B - Chulmleigh ICT Department
... OS, which usually performs a task to help with the upkeep of the system. 12 A program that converts program code to machine code. Examples include compilers and interpreters. ...
... OS, which usually performs a task to help with the upkeep of the system. 12 A program that converts program code to machine code. Examples include compilers and interpreters. ...
Internal Networks and Physical Attacks
... identifies activity that matches suspicious or attack signatures. Once a suspicious or malicious attack pattern is spotted, the system logs, notifies and, in some cases, terminates the session. Intrusion detection utilities can be installed to alert the security administrators when there are attempt ...
... identifies activity that matches suspicious or attack signatures. Once a suspicious or malicious attack pattern is spotted, the system logs, notifies and, in some cases, terminates the session. Intrusion detection utilities can be installed to alert the security administrators when there are attempt ...
security threats: a guide for small and medium
... or laptops. The reasons vary but they may want to be able to install new software or simply to have more control of their machines. The problem with this scenario is that one compromised machine is all that an attacker needs to target an organization. The firm itself does not need to be specifically ...
... or laptops. The reasons vary but they may want to be able to install new software or simply to have more control of their machines. The problem with this scenario is that one compromised machine is all that an attacker needs to target an organization. The firm itself does not need to be specifically ...
Computer and Information Security
... • Access mechanisms, such as cryptography, support confidentiality – Example: encrypting income tax return ...
... • Access mechanisms, such as cryptography, support confidentiality – Example: encrypting income tax return ...
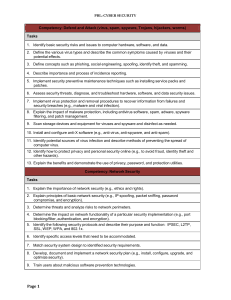
Competency: Defend and Attack (virus, spam, spyware - FBLA-PBL
... 1. Describe authentication process to network devices for users. 2. Discuss the need for authentication and non-repudiation of information (e.g., PKI). 3. Describe the steps to achieve authentication and confidentiality. 4. Provide for user authentication (e.g., assign passwords and access level). 5 ...
... 1. Describe authentication process to network devices for users. 2. Discuss the need for authentication and non-repudiation of information (e.g., PKI). 3. Describe the steps to achieve authentication and confidentiality. 4. Provide for user authentication (e.g., assign passwords and access level). 5 ...
601331-OS-QA-2016
... To differentiate between user and kernel modes in an operating system. Discuss different components for structuring an operating system. Explain the concurrency in the execution of processes, and show the run-time problems arising from the concurrent operation of many separate processes. Provide and ...
... To differentiate between user and kernel modes in an operating system. Discuss different components for structuring an operating system. Explain the concurrency in the execution of processes, and show the run-time problems arising from the concurrent operation of many separate processes. Provide and ...
Chapter 03
... execution, optimization, and maintenance Runtime error detection: race conditions, exceptions, resource & memory leaks, security attack vulnerabilities. ...
... execution, optimization, and maintenance Runtime error detection: race conditions, exceptions, resource & memory leaks, security attack vulnerabilities. ...
Powerpoint with iClicker Questions
... Windows Firewall in XP SP2, Vista, and Win 7 does not filter outgoing traffic by default ...
... Windows Firewall in XP SP2, Vista, and Win 7 does not filter outgoing traffic by default ...
lesson12
... on some type of tape media. – You can also store a backup on a hard drive on another computer connected over a local area network (LAN). ...
... on some type of tape media. – You can also store a backup on a hard drive on another computer connected over a local area network (LAN). ...
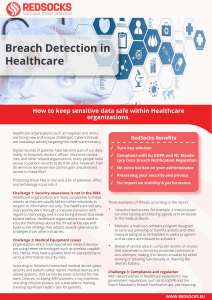
Breach Detection in Healthcare
... The RedSocks Maliciuos Threat Detection (MTD) solution can help healthcare organizations both increase their security posture and address requirements of the GDPR regulations. To ensure that data breaches are always detected at lightning speed RedSocks provides a critical cyber security layer inside ...
... The RedSocks Maliciuos Threat Detection (MTD) solution can help healthcare organizations both increase their security posture and address requirements of the GDPR regulations. To ensure that data breaches are always detected at lightning speed RedSocks provides a critical cyber security layer inside ...
PCS 105 ADVANCED OPERATING SYSTEM Course Objective: Introduction:
... Course Objective: To learn the advanced concepts of operating systems and its implementation. ...
... Course Objective: To learn the advanced concepts of operating systems and its implementation. ...
L03_Processes
... operating system is divided into a number of layers or levels, each built on top of lower layers. The lowest layer is the hardware; the highest is the user interface. Layers are selected such that each uses functions and services of only lower-level layers. ...
... operating system is divided into a number of layers or levels, each built on top of lower layers. The lowest layer is the hardware; the highest is the user interface. Layers are selected such that each uses functions and services of only lower-level layers. ...
Chapter 4-1
... Share via access limitation – each user is checked for access availability of an object Share by compatibilities- dynamic creation of shared objects Limit use of an object- user has varying access to an object Each has a varying level of granularity - Greater granularity creates greater access contr ...
... Share via access limitation – each user is checked for access availability of an object Share by compatibilities- dynamic creation of shared objects Limit use of an object- user has varying access to an object Each has a varying level of granularity - Greater granularity creates greater access contr ...
COS 318: Operating Systems Introduction Jaswinder Pal Singh
... User programs can deal with simpler, high-level concepts Hide complex and unreliable hardware Provide illusions like “sole application running” or “infinite memory” ...
... User programs can deal with simpler, high-level concepts Hide complex and unreliable hardware Provide illusions like “sole application running” or “infinite memory” ...
Module 3: Operating-System Structures
... the original UNIX operating system had limited structuring. The UNIX OS consists of two separable parts. – Systems programs – The kernel • Consists of everything below the system-call interface and above the physical hardware • Provides the file system, CPU scheduling, memory management, and other o ...
... the original UNIX operating system had limited structuring. The UNIX OS consists of two separable parts. – Systems programs – The kernel • Consists of everything below the system-call interface and above the physical hardware • Provides the file system, CPU scheduling, memory management, and other o ...
Whitepaper: Network Penetration Testing
... networks can personify polar differences in characters. It can vary from remote system & password compromise, web server, database, network service, network device, directory and miscellaneous non-configuration to information disclosure to weak cryptography. This array of vulnerabilities propel the ...
... networks can personify polar differences in characters. It can vary from remote system & password compromise, web server, database, network service, network device, directory and miscellaneous non-configuration to information disclosure to weak cryptography. This array of vulnerabilities propel the ...
Diploma in Computer Systems and Network Technology
... This course provides instruction in network design and technologies using the Open Systems Interconnection (OSI) model. Topics include network fundamentals, the OSI model, network operating systems, TCP/IP fundamentals and utilities, network installation and upgrades, network remote access configura ...
... This course provides instruction in network design and technologies using the Open Systems Interconnection (OSI) model. Topics include network fundamentals, the OSI model, network operating systems, TCP/IP fundamentals and utilities, network installation and upgrades, network remote access configura ...
Linux For Beginners - St. Louis UNIX Users Group
... Linux is an independent Unix-like operating system that can be freely modified and redistributed. It works on all major 32-bit and 64-bit computer hardware platforms and is an implementation of the POSIX specification with which all true versions of Unix comply. Linux uses no code from proprietary U ...
... Linux is an independent Unix-like operating system that can be freely modified and redistributed. It works on all major 32-bit and 64-bit computer hardware platforms and is an implementation of the POSIX specification with which all true versions of Unix comply. Linux uses no code from proprietary U ...
Assessing Network Security for Northwind Traders What
... Nonintrusive attack: The intent to gain information about an organization’s network in preparation for a more intrusive attack at a later time Examples of nonintrusive attacks include: Information reconnaissance Port scanning ...
... Nonintrusive attack: The intent to gain information about an organization’s network in preparation for a more intrusive attack at a later time Examples of nonintrusive attacks include: Information reconnaissance Port scanning ...
Operating Systems - sacredheartmalta.org
... Usually, a mainframe (or minicomputer) is used for a multi user OS ...
... Usually, a mainframe (or minicomputer) is used for a multi user OS ...