T210 Gas-insulated substations 800 kV 50 kA
... Grid-GIS-L3-T210 800 kV GIS-72505-2015_03-EN. Information contained in this document is indicative only. No representation or warranty is given or should be relied on that it is complete or correct or will apply to any particular project. This will depend on the technical and commercial circumstance ...
... Grid-GIS-L3-T210 800 kV GIS-72505-2015_03-EN. Information contained in this document is indicative only. No representation or warranty is given or should be relied on that it is complete or correct or will apply to any particular project. This will depend on the technical and commercial circumstance ...
This summer math booklet was developed to provide
... as three hundred and fifty, because "and" means a decimal point). Also, the term "point" in mathematics is a geometry term and should not be used in naming numbers (for example, 3.5 is not three "point" five, but rather three and five tenths). ...
... as three hundred and fifty, because "and" means a decimal point). Also, the term "point" in mathematics is a geometry term and should not be used in naming numbers (for example, 3.5 is not three "point" five, but rather three and five tenths). ...
Authentication and Remote Access
... • A hardware device that counts as both something-youhave and something-you-know. • A number is displayed on the screen that is used in conjunction with a user ID. • The number changes at a constant interval. • Even if someone finds the token, they won’t know the corresponding user ID. ...
... • A hardware device that counts as both something-youhave and something-you-know. • A number is displayed on the screen that is used in conjunction with a user ID. • The number changes at a constant interval. • Even if someone finds the token, they won’t know the corresponding user ID. ...
Network Security Policy in the Work Place
... – According to zdnet.com, a technology news website, nearly half of all companies globally have been hit with a Distributed Denial of Service (DDoS) attack in the past year. – A DDoS attack attempts to overload a company system – such as a web server, by sending so many communication requests that l ...
... – According to zdnet.com, a technology news website, nearly half of all companies globally have been hit with a Distributed Denial of Service (DDoS) attack in the past year. – A DDoS attack attempts to overload a company system – such as a web server, by sending so many communication requests that l ...
DATA SHEET PMEG2010AEB 20 V, 1 A ultra low V MEGA
... Export control ⎯ This document as well as the item(s) described herein may be subject to export control regulations. Export might require a prior authorization from national authorities. Quick reference data ⎯ The Quick reference data is an extract of the product data given in the Limiting values an ...
... Export control ⎯ This document as well as the item(s) described herein may be subject to export control regulations. Export might require a prior authorization from national authorities. Quick reference data ⎯ The Quick reference data is an extract of the product data given in the Limiting values an ...
Issue 43 Key RSC Discussion
... active for the ESSID the STA is associating to, the GTK is identified in message 3 of the 4-way handshake, along with the current receive sequence counter (KeyRSC) for messages protected under that key. Since the WTP maintains the active KeyRSC, the AC currently has no way to know precisely what the ...
... active for the ESSID the STA is associating to, the GTK is identified in message 3 of the 4-way handshake, along with the current receive sequence counter (KeyRSC) for messages protected under that key. Since the WTP maintains the active KeyRSC, the AC currently has no way to know precisely what the ...
Fujitsu`s Security Technology Based on Practical Knowledge
... one of those Websites to set up a trap that will let him or her infiltrate the victim’s system. As described above, these attacks are typically executed without arousing the victim’s suspicions of the attack. In addition, the malware in these attacks tends to be more difficult to detect using conven ...
... one of those Websites to set up a trap that will let him or her infiltrate the victim’s system. As described above, these attacks are typically executed without arousing the victim’s suspicions of the attack. In addition, the malware in these attacks tends to be more difficult to detect using conven ...
tip of the month for coaches
... General correspondence includes letters, postcards and institutional note cards All institutional staff members may prepare general correspondence Include a single (8.5x11 in.) sheet of institutional letterhead. No restrictions on the design/content of one side of the sheet. Opposite side is b ...
... General correspondence includes letters, postcards and institutional note cards All institutional staff members may prepare general correspondence Include a single (8.5x11 in.) sheet of institutional letterhead. No restrictions on the design/content of one side of the sheet. Opposite side is b ...
Security+ Guide to Network Security Fundamentals, Third
... There are several reasons why it is difficult to defend against today’s attacks Information security may be defined as that which protects the integrity, confidentiality, and availability of information on the devices that store, manipulate, and transmit the information through products, people, and ...
... There are several reasons why it is difficult to defend against today’s attacks Information security may be defined as that which protects the integrity, confidentiality, and availability of information on the devices that store, manipulate, and transmit the information through products, people, and ...
Akademisches Auslandsamt Universitätsstr. 30 95440 Bayreuth
... pass- and fail- basis; no grades are issued for these courses. L=Lecture, S=Seminar, WE=Written Examination, PR=Presentation, Paper: about 1500 words for 2 Points; about 8000 words for 6-10 points. ** These grades will become available as soon as the final exams will have been corrected. *** Analysi ...
... pass- and fail- basis; no grades are issued for these courses. L=Lecture, S=Seminar, WE=Written Examination, PR=Presentation, Paper: about 1500 words for 2 Points; about 8000 words for 6-10 points. ** These grades will become available as soon as the final exams will have been corrected. *** Analysi ...
Manual
... Limited Warranty: Fellowes, Inc. (“Fellowes”) warrants the parts of the machine to be free of defects in material and workmanship and provides service and support for 2 years from the date of purchase by the original consumer. Fellowes warrants the cutting blades of the machine to be free from defec ...
... Limited Warranty: Fellowes, Inc. (“Fellowes”) warrants the parts of the machine to be free of defects in material and workmanship and provides service and support for 2 years from the date of purchase by the original consumer. Fellowes warrants the cutting blades of the machine to be free from defec ...
DATA SHEET PMEG2020AEA 20 V, 2 A very low V MEGA
... Applications ⎯ Applications that are described herein for any of these products are for illustrative purposes only. NXP Semiconductors makes no representation or warranty that such applications will be suitable for the specified use without further testing or modification. ...
... Applications ⎯ Applications that are described herein for any of these products are for illustrative purposes only. NXP Semiconductors makes no representation or warranty that such applications will be suitable for the specified use without further testing or modification. ...
National Initiative For Cybersecurity Education (NICE)
... American Association for Motor Vehicle Administrators o AAMVA leads a consortium of private industry and government partners to implement and pilot the Cross Sector Digital Identity Initiative (CSDII) Criterion Systems o Allows consumers to selectively share shopping and other preferences and in ...
... American Association for Motor Vehicle Administrators o AAMVA leads a consortium of private industry and government partners to implement and pilot the Cross Sector Digital Identity Initiative (CSDII) Criterion Systems o Allows consumers to selectively share shopping and other preferences and in ...
Cyber Security in Evolving Enterprise
... Incursions on Military Networks were up 55% Last Year 29 October 2009 ...
... Incursions on Military Networks were up 55% Last Year 29 October 2009 ...
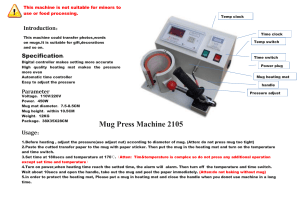
Mug Press Machine 2105 - Heat Press Machine,Heat Transfer
... and time switch. 3.Set time at 180secs and temperature at 170℃.(Atten: Tim&temperature is complex so do not press any additional operation except set time and temperature) 4.Turn on power,when heating time reach the setted time, the alarm will alarm. Then turn off the temperature and time switch. Wa ...
... and time switch. 3.Set time at 180secs and temperature at 170℃.(Atten: Tim&temperature is complex so do not press any additional operation except set time and temperature) 4.Turn on power,when heating time reach the setted time, the alarm will alarm. Then turn off the temperature and time switch. Wa ...
II.I Selected Database Issues: 1
... server. It intercepts all requests to the Web server to see if it can fulfill them itself if not then it forwards them on. two main purposes: 1. Improve Performance: It saves the results of all requests for a certain amount of time. Much faster. 2. Filter requests: an organisation may want to preven ...
... server. It intercepts all requests to the Web server to see if it can fulfill them itself if not then it forwards them on. two main purposes: 1. Improve Performance: It saves the results of all requests for a certain amount of time. Much faster. 2. Filter requests: an organisation may want to preven ...
Whitepaper: Network Penetration Testing
... Discovery involves using the automated tools and manual techniques to identify the live hosts present in the network, determining the target system’s operating system through banner grabbing, presence of open ports, services running, & versions of the services, technology information, protocols and ...
... Discovery involves using the automated tools and manual techniques to identify the live hosts present in the network, determining the target system’s operating system through banner grabbing, presence of open ports, services running, & versions of the services, technology information, protocols and ...
What Cyber Criminals Know Most People Don`t?
... Identify, if possible, the root cause of the intrusion (e.g., the firm’s system was compromised, the individual account was hacked, the customer was the victim of identity theft) and determine whether the intrusion is isolated to one account. ...
... Identify, if possible, the root cause of the intrusion (e.g., the firm’s system was compromised, the individual account was hacked, the customer was the victim of identity theft) and determine whether the intrusion is isolated to one account. ...
Slide 1
... Web applications are characterized by multiculturalism, continuous change, fast pace and competitiveness, high demands on user adaptivity, Thus, the complexity of securing such Web applications has increased significantly ...
... Web applications are characterized by multiculturalism, continuous change, fast pace and competitiveness, high demands on user adaptivity, Thus, the complexity of securing such Web applications has increased significantly ...