Types of Attacks - Digital Locker and Personal Web Space
... – Systems prior to XP and Server 2003 are vulnerable. – Used by a variety of exploit tools and malware. – No patch is available. • Options to counter the vulnerability – Upgrade systems to Windows XP or newer version – Only allow trusted users access to TCP ports 139 and 445 ...
... – Systems prior to XP and Server 2003 are vulnerable. – Used by a variety of exploit tools and malware. – No patch is available. • Options to counter the vulnerability – Upgrade systems to Windows XP or newer version – Only allow trusted users access to TCP ports 139 and 445 ...
Adaptive image retrieval based on the spatial organization of
... oriented toward representing the color content of images by using histograms. This is probably due to the ability of color histograms to concisely represent the global aspect of natural images and to the striking impression of global coherence given by series of images having similar color content. ...
... oriented toward representing the color content of images by using histograms. This is probably due to the ability of color histograms to concisely represent the global aspect of natural images and to the striking impression of global coherence given by series of images having similar color content. ...
Seven Habits of Effective Research Paper Writers
... models) to provide real-time event communication by dedicating thread resources with minimal locking overhead in the critical path of event propagation. Second, we analyze the results of empirical benchmarks of the performance and predictability of TAO’s Real-time Notification Service. These results ...
... models) to provide real-time event communication by dedicating thread resources with minimal locking overhead in the critical path of event propagation. Second, we analyze the results of empirical benchmarks of the performance and predictability of TAO’s Real-time Notification Service. These results ...
PPT_ch01 - Mercer University Computer Science Department
... type of computer, operating system, software, and network connection a computer uses – An attacker who knows that information can more easily determine the weaknesses of the system to attack it ...
... type of computer, operating system, software, and network connection a computer uses – An attacker who knows that information can more easily determine the weaknesses of the system to attack it ...
Security+ Guide to Network Security Fundamentals, Third Edition
... type of computer, operating system, software, and network connection a computer uses – An attacker who knows that information can more easily determine the weaknesses of the system to attack it ...
... type of computer, operating system, software, and network connection a computer uses – An attacker who knows that information can more easily determine the weaknesses of the system to attack it ...
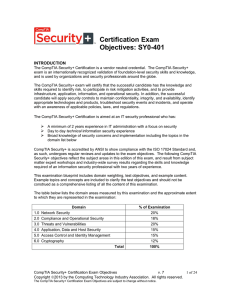
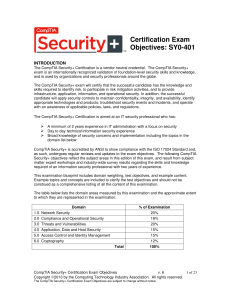
CompTIA Security (SY0-401)
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
Adaptive image retrieval based on the spatial organization of colors
... the cultural abstraction content since it models the artistic composition [20,12]. Such a feature can be used for illustration, generation of ideas, aesthetic decoration, and learning [14]. Within one semantic category reached with metadata, for instance, a journalist may pursue its illustration nee ...
... the cultural abstraction content since it models the artistic composition [20,12]. Such a feature can be used for illustration, generation of ideas, aesthetic decoration, and learning [14]. Within one semantic category reached with metadata, for instance, a journalist may pursue its illustration nee ...
Describing Patterns
... Look for repeated flowers to find a pattern. The lei starts with a carnation, two orchids, another carnation, and then two orchids again. Notice that the carnations alternate between yellow and red. ANSWER The last flower on the lei is a red carnation, so the next three flowers should be two orchids ...
... Look for repeated flowers to find a pattern. The lei starts with a carnation, two orchids, another carnation, and then two orchids again. Notice that the carnations alternate between yellow and red. ANSWER The last flower on the lei is a red carnation, so the next three flowers should be two orchids ...
Introduction
... • Protected against unauthorized physical and logical access • Available for operation and use as information systems, designated as confidential and protected Further details regarding SSAE 16 may be found on the AICPA website. ...
... • Protected against unauthorized physical and logical access • Available for operation and use as information systems, designated as confidential and protected Further details regarding SSAE 16 may be found on the AICPA website. ...
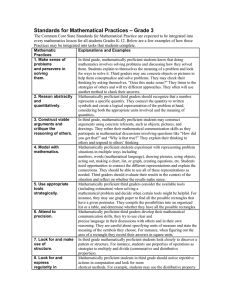
Standards for Mathematical Practices – Grade 3
... situations in multiple ways including numbers, words (mathematical language), drawing pictures, using objects, acting out, making a chart, list, or graph, creating equations, etc. Students need opportunities to connect the different representations and explain the connections. They should be able to ...
... situations in multiple ways including numbers, words (mathematical language), drawing pictures, using objects, acting out, making a chart, list, or graph, creating equations, etc. Students need opportunities to connect the different representations and explain the connections. They should be able to ...
Real-Time Georgia…….
... Download “White Paper” – “Real-Time Georgia” @ www.valentina.net/vaza/GITI.pdf ...
... Download “White Paper” – “Real-Time Georgia” @ www.valentina.net/vaza/GITI.pdf ...
SG 17 is
... Importance of telecommunication/ICT security standardization (4/4) For on-going credibility, we need performance measures that provide some indication of the effectiveness of our standards. In the past there has been too much focus on quantity (i.e. how many standards are produced) than on the qu ...
... Importance of telecommunication/ICT security standardization (4/4) For on-going credibility, we need performance measures that provide some indication of the effectiveness of our standards. In the past there has been too much focus on quantity (i.e. how many standards are produced) than on the qu ...
openwetware.org
... Enzymes are regulated by genes and are limited. Regulation of cellular import and export. The cell is using the metabolites to fulfill specific processes. If a model of the information from the paper was to be made, it would require expanding the equation to hold these concepts. ...
... Enzymes are regulated by genes and are limited. Regulation of cellular import and export. The cell is using the metabolites to fulfill specific processes. If a model of the information from the paper was to be made, it would require expanding the equation to hold these concepts. ...
PCs_MACs_MSWord_Line_numbers
... Adding Line Numbers to Code Lines After Inserting a Section Break Just Before the First Line of Code PCs (Microsoft Word 2007 and 2013): 1. On the Page Layout tab, in the Page Setup group, click Line Numbers 2. Do one of the following: To number consecutively throughout the document, click Continuou ...
... Adding Line Numbers to Code Lines After Inserting a Section Break Just Before the First Line of Code PCs (Microsoft Word 2007 and 2013): 1. On the Page Layout tab, in the Page Setup group, click Line Numbers 2. Do one of the following: To number consecutively throughout the document, click Continuou ...
Red Teaming: The Art of Ethical Hacking
... and postal shipping. The reach of these computer networks exceeds the bounds of cyberspace. They also control physical objects such as electrical transformers, trains, pipeline pumps, chemical vats, and radars… A spectrum of malicious actors can and do conduct attacks against our critical informatio ...
... and postal shipping. The reach of these computer networks exceeds the bounds of cyberspace. They also control physical objects such as electrical transformers, trains, pipeline pumps, chemical vats, and radars… A spectrum of malicious actors can and do conduct attacks against our critical informatio ...
Security Policies, Standards, and Planning
... a. This section of the policy statement addresses who can use the technology governed by the policy and what it can be used for. b. This section defines “fair and responsible use” of equipment and other organizational assets and should also address key legal issues, such as protection of personal in ...
... a. This section of the policy statement addresses who can use the technology governed by the policy and what it can be used for. b. This section defines “fair and responsible use” of equipment and other organizational assets and should also address key legal issues, such as protection of personal in ...
The Role of People in Security
... Overview of Baselines • The process of establishing a system’s security state is called baselining. • The resulting product is a security baseline that allows the system to run safely and securely. • Once the process has been completed, any similar systems can be configured with the same baseline to ...
... Overview of Baselines • The process of establishing a system’s security state is called baselining. • The resulting product is a security baseline that allows the system to run safely and securely. • Once the process has been completed, any similar systems can be configured with the same baseline to ...