Maths lesson plan Subject: Operations with numbers to 100
... Students sit in the circle. The teacher greets children. The child which feels greeted waves her/his hand. - I say ‚hello’ to everyone who stood up with their right leg, - I say ‚hello’ to everyone who is in a good mood, - I say ‚hello’ to everyone who likes walking in the wood, - I say ‚hello’ to e ...
... Students sit in the circle. The teacher greets children. The child which feels greeted waves her/his hand. - I say ‚hello’ to everyone who stood up with their right leg, - I say ‚hello’ to everyone who is in a good mood, - I say ‚hello’ to everyone who likes walking in the wood, - I say ‚hello’ to e ...
National and International Publications
... MODIFYING EARLEY’S ALGORITHM” is published in “CCIS series of Springer”. Research paper entitled “SOME MATHEMATICAL MODELS FOR TRANSFOR MATION OF SENTENCES FROM ONE FORM TO OTHER” is published in Journal “Mathematical Modeling and applied computing”. Research Paper entitled “APPLICATION OF GRAPH THE ...
... MODIFYING EARLEY’S ALGORITHM” is published in “CCIS series of Springer”. Research paper entitled “SOME MATHEMATICAL MODELS FOR TRANSFOR MATION OF SENTENCES FROM ONE FORM TO OTHER” is published in Journal “Mathematical Modeling and applied computing”. Research Paper entitled “APPLICATION OF GRAPH THE ...
ppt
... play to those who might suffer by ignorance. It cannot be too earnestly urged that an acquaintance with real facts will, in the end, be better for all parties. Some time ago, when the reading public was alarmed at being told how London milk is adulterated, timid persons deprecated the exposure, on t ...
... play to those who might suffer by ignorance. It cannot be too earnestly urged that an acquaintance with real facts will, in the end, be better for all parties. Some time ago, when the reading public was alarmed at being told how London milk is adulterated, timid persons deprecated the exposure, on t ...
Information Security - National University of Sciences and
... • Attaches itself to some host program e.g. a word document • Executes when word document is opened • Make copies of itself by attaching itself by other host programs • Can do all sorts of damage • Fill up storage and memory, modify/destroy data, erase hard disk ...
... • Attaches itself to some host program e.g. a word document • Executes when word document is opened • Make copies of itself by attaching itself by other host programs • Can do all sorts of damage • Fill up storage and memory, modify/destroy data, erase hard disk ...
Español 115 – SLU – Primavera 2008 – Composición 2
... very careful not to copy word-for-word from any of these sources. Remember that you will have to keep your language relatively simple, since you are only in your first year of college-level Spanish studies. Try to stick to words you know and grammar structures you are familiar with. In this paper, y ...
... very careful not to copy word-for-word from any of these sources. Remember that you will have to keep your language relatively simple, since you are only in your first year of college-level Spanish studies. Try to stick to words you know and grammar structures you are familiar with. In this paper, y ...
Introduction - Personal Web Pages
... – Vulnerabilities of protocols or security mechanisms (security patch has problems) – By-passing protection walls – Backdoors for systems (Linux password) – Known attacks ignored (push and poll) ...
... – Vulnerabilities of protocols or security mechanisms (security patch has problems) – By-passing protection walls – Backdoors for systems (Linux password) – Known attacks ignored (push and poll) ...
Playing it Safe: Document Destruction Best Practices - Shred-it
... longer needed, through shredding or similar means”2. Best practices in document destruction can be summed up as three general guidelines that are easy to understand and implement: • Shred all and shred regularly – and avoid the risks of human error or poor judgment about what needs to be shredded. D ...
... longer needed, through shredding or similar means”2. Best practices in document destruction can be summed up as three general guidelines that are easy to understand and implement: • Shred all and shred regularly – and avoid the risks of human error or poor judgment about what needs to be shredded. D ...
File - Mrs. Book Loves Math
... R, A, S, or H. Put that letter and your color at the top of your paper (both sides). 3. Every Person will solve the problem on their own paper(you may get help from the members in your group). 4. Only the person whose letter I call will come up and show me their paper. 5. You get one point for a cor ...
... R, A, S, or H. Put that letter and your color at the top of your paper (both sides). 3. Every Person will solve the problem on their own paper(you may get help from the members in your group). 4. Only the person whose letter I call will come up and show me their paper. 5. You get one point for a cor ...
cisco.camre.ac.uk
... While no one would wish to live in a society with a ‘Big Brother ‘figure watching every move, it is natural for people to desire the assurance that the working environment and all systems are safe. ...
... While no one would wish to live in a society with a ‘Big Brother ‘figure watching every move, it is natural for people to desire the assurance that the working environment and all systems are safe. ...
Proposed Part 73 Fuel Cycle Facility Security Rulemaking
... Materials, has been revised subpart-by-subpart over the last 25 years • Lessons learned ((e.g., g threat and implementation)) • Commission directed engagement of a “broad” range of stakeholders ...
... Materials, has been revised subpart-by-subpart over the last 25 years • Lessons learned ((e.g., g threat and implementation)) • Commission directed engagement of a “broad” range of stakeholders ...
Troubleshooting hangs and 49 errors
... Are third-party applications (Chailets) installed? If so, what? State of LED’s on input and output devices (does not apply to all products) If printing appears to cause the problem, what print driver is used? Is the device connected to a network? ...
... Are third-party applications (Chailets) installed? If so, what? State of LED’s on input and output devices (does not apply to all products) If printing appears to cause the problem, what print driver is used? Is the device connected to a network? ...
A Feature-Based Analysis & Comparison of IT Automation Tools
... needs to be configured on its own, and without group policy, to ensure successful configuration using SNMP, and connection to the Spiceworks server. This is crucial since without the correct connection, the whole process becomes void, and will not help the IT Staff. ...
... needs to be configured on its own, and without group policy, to ensure successful configuration using SNMP, and connection to the Spiceworks server. This is crucial since without the correct connection, the whole process becomes void, and will not help the IT Staff. ...
SIRCHIE® TECHNICAL INFORMATION
... Oil Red O is a new chemical latent print developer that answers a long-standing problem facing the lab technician—how to develop latent prints on paper products that are wet or have been wet. Other chemical processes such as Ninhydrin, DFO and Physical Developer have proven to be ineffective under t ...
... Oil Red O is a new chemical latent print developer that answers a long-standing problem facing the lab technician—how to develop latent prints on paper products that are wet or have been wet. Other chemical processes such as Ninhydrin, DFO and Physical Developer have proven to be ineffective under t ...
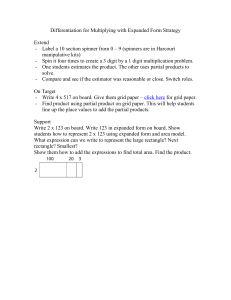
Differentiation for Multiplying with Expanded Form Strategy
... Differentiation for Multiplying with Expanded Form Strategy Extend - Label a 10 section spinner from 0 – 9 (spinners are in Harcourt manipulative kits) - Spin it four times to create a 3 digit by a 1 digit multiplication problem. - One students estimates the product. The other uses partial products ...
... Differentiation for Multiplying with Expanded Form Strategy Extend - Label a 10 section spinner from 0 – 9 (spinners are in Harcourt manipulative kits) - Spin it four times to create a 3 digit by a 1 digit multiplication problem. - One students estimates the product. The other uses partial products ...
Preface
... cryptology, but who lack the time to study one of the many books on computer and information security or cryptology. At the end of 2001, the idea to write an easily accessible encyclopedia on cryptography and information security was proposed. The goal was to make it possible to become familiar with ...
... cryptology, but who lack the time to study one of the many books on computer and information security or cryptology. At the end of 2001, the idea to write an easily accessible encyclopedia on cryptography and information security was proposed. The goal was to make it possible to become familiar with ...
TOP TEN REASONS WHY THE MagEraSURE ME
... Drive Technology, as well as Future Hard Drives based on Perpendicular Magnetic Recorded (PMR ) Technology ~ extends the life of the product well into the future. ...
... Drive Technology, as well as Future Hard Drives based on Perpendicular Magnetic Recorded (PMR ) Technology ~ extends the life of the product well into the future. ...
Three arguments used to promote trade barriers are
... protectionist trade arguments. How do you respond? Three arguments used to promote trade barriers are the national security agreement, the infant industry argument and the dumping argument. Explain each of these arguments and evaluate any flaws of each argument. ...
... protectionist trade arguments. How do you respond? Three arguments used to promote trade barriers are the national security agreement, the infant industry argument and the dumping argument. Explain each of these arguments and evaluate any flaws of each argument. ...
extended probabilistic latent semantic analysis model for topics in
... images with known time stamp. Detecting and tracking of temporal data is an important task in multiple applications, such as finding hot research point from scientific literature, news article series analysis, email surveillance, search query log mining, etc. In contrast to existing works mainly foc ...
... images with known time stamp. Detecting and tracking of temporal data is an important task in multiple applications, such as finding hot research point from scientific literature, news article series analysis, email surveillance, search query log mining, etc. In contrast to existing works mainly foc ...