Principal Security Engineer– PAE4IT A. PRIMARY ROLE Working
... providesreports and recommendations on appropriate tactical and strategic security actions. Have expertise and provide input that could have a direct impact on important technology decisions made at the highest levels of the university 5 Develop and maintain contacts at high levels such as organizat ...
... providesreports and recommendations on appropriate tactical and strategic security actions. Have expertise and provide input that could have a direct impact on important technology decisions made at the highest levels of the university 5 Develop and maintain contacts at high levels such as organizat ...
PAPER TITLE
... paper, in a separate section entitled “REFERENCES”. The adequate format for various kinds of publications is exemplified at the end of this text. Citations in the paper are indicated by reference numbers within brackets [1]. ...
... paper, in a separate section entitled “REFERENCES”. The adequate format for various kinds of publications is exemplified at the end of this text. Citations in the paper are indicated by reference numbers within brackets [1]. ...
us-16-Price-Building-a-Product-Security-Incident
... • What Leadership needs to know about business risk • What Customers need to know about product security • DOCUMENT at time of investigation even if you don’t use the data until much later ...
... • What Leadership needs to know about business risk • What Customers need to know about product security • DOCUMENT at time of investigation even if you don’t use the data until much later ...
AtomicEye Attack Surface Manager
... Networks and endpoints are in constant flux, so it is a never-ending job to ensure that security configurations and controls are enforced. AtomicEye ASM automates these procedures on every endpoint, every day. Moreover, when a vulnerability is identified, AtomicEye ASM manages the remediation proces ...
... Networks and endpoints are in constant flux, so it is a never-ending job to ensure that security configurations and controls are enforced. AtomicEye ASM automates these procedures on every endpoint, every day. Moreover, when a vulnerability is identified, AtomicEye ASM manages the remediation proces ...
Syllabus 2016 – 2017 State Board Curriculum Class 4
... value, The different break ups of a number, Number comes before and after, Ascending and Descending order, Even and Odd numbers, International numerals. 2. Geometrical Figures-Angles, Circle, Vertex and side. 3. Addition-With carrying over- Addition of Four-digit numbers. 4. Subtraction-four and fiv ...
... value, The different break ups of a number, Number comes before and after, Ascending and Descending order, Even and Odd numbers, International numerals. 2. Geometrical Figures-Angles, Circle, Vertex and side. 3. Addition-With carrying over- Addition of Four-digit numbers. 4. Subtraction-four and fiv ...
Course Learning Objectives:
... 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and verification algorithms. (ABET Outcomes: c, e, k) 3. Analyze existing authentication and key agreement protocols, identify the weaknesses of these protocols. (ABET Outcomes: c, e, ...
... 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and verification algorithms. (ABET Outcomes: c, e, k) 3. Analyze existing authentication and key agreement protocols, identify the weaknesses of these protocols. (ABET Outcomes: c, e, ...
I can…
... Every team has one sheet of paper and each student has a different colored pencil. A problem is given to the group. Person 1 writes the first step of the solution process, explaining aloud, and passes the paper on to Person 2. Person 2 makes any corrections and adds the next step, explaining aloud, ...
... Every team has one sheet of paper and each student has a different colored pencil. A problem is given to the group. Person 1 writes the first step of the solution process, explaining aloud, and passes the paper on to Person 2. Person 2 makes any corrections and adds the next step, explaining aloud, ...
Jensen3
... • Conditions required to be met by the hash function for an effective traitor tracing algorithm, as specified by Chor et al., are not mentioned. – Traitor tracing algorithm needs to identify at least one traitor and reduce possibilities of a false positives. – For a k-resilient open user scheme the ...
... • Conditions required to be met by the hash function for an effective traitor tracing algorithm, as specified by Chor et al., are not mentioned. – Traitor tracing algorithm needs to identify at least one traitor and reduce possibilities of a false positives. – For a k-resilient open user scheme the ...
Pharmacology Science
... Lectures (study days) plus facilitated online discussions using problem based learning and application of concepts to the students own clinical practice. How much time will I need to commit to the paper? This is dependent on your other commitments and the speed at which you learn and work, but on av ...
... Lectures (study days) plus facilitated online discussions using problem based learning and application of concepts to the students own clinical practice. How much time will I need to commit to the paper? This is dependent on your other commitments and the speed at which you learn and work, but on av ...
Final - BOUN CmpE
... of Beethoven, we can assign it to the “music” class (by using some data about the document) among the set of classes {music, sport, ...}. Design a very simple artificial neural network (ANN) that learns the class of a document. First decide on the features you will use for learning, and then the str ...
... of Beethoven, we can assign it to the “music” class (by using some data about the document) among the set of classes {music, sport, ...}. Design a very simple artificial neural network (ANN) that learns the class of a document. First decide on the features you will use for learning, and then the str ...
ECON 7818-001 Econometrics II
... You can buy some of this products and additional ones, like STATA or SAS, from the University at a reasonable student price. During the semester we will spend some time teaching SAS. You should plan to get started on your paper as soon as possible. The final draft is due one week before the final e ...
... You can buy some of this products and additional ones, like STATA or SAS, from the University at a reasonable student price. During the semester we will spend some time teaching SAS. You should plan to get started on your paper as soon as possible. The final draft is due one week before the final e ...
Diagnosis as Planning Revisited: An Abridged Report
... In the spirit of past contributions to the formal characterization of diagnosis (e.g., (Reiter, 1987; de Kleer et al., 1992)) this paper presents a formal characterization of diagnosis of discrete dynamical systems, appealing to the situation calculus. It then proceeds to establish a correspondence ...
... In the spirit of past contributions to the formal characterization of diagnosis (e.g., (Reiter, 1987; de Kleer et al., 1992)) this paper presents a formal characterization of diagnosis of discrete dynamical systems, appealing to the situation calculus. It then proceeds to establish a correspondence ...
Security
... Hardware protection, e.g. memory protection, features are a must for overall protection scheme. January 2017 ...
... Hardware protection, e.g. memory protection, features are a must for overall protection scheme. January 2017 ...
Appendix IV: Log-Log Plotting Introduction It is often useful to plot
... analyzing data. Such plots allow one to infer whether the relationship between the two variables is of the form y = axn within experimental error. When y = axn, then log y = n log x + log a and a plot of log y versus log x is a straight line with a slope equal to n and an intercept equal to log a. L ...
... analyzing data. Such plots allow one to infer whether the relationship between the two variables is of the form y = axn within experimental error. When y = axn, then log y = n log x + log a and a plot of log y versus log x is a straight line with a slope equal to n and an intercept equal to log a. L ...
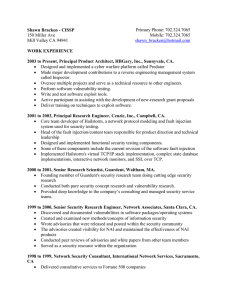
Shawn Bracken - CISSP103 Chester StMenlo Park, CA 94025
... 1999 to 2000, Senior Security Research Engineer, Network Associates, Santa Clara, CA. Discovered and documented vulnerabilities in software packages/operating systems Created and examined new methods/concepts of information security Wrote advisories that were released and posted within the sec ...
... 1999 to 2000, Senior Security Research Engineer, Network Associates, Santa Clara, CA. Discovered and documented vulnerabilities in software packages/operating systems Created and examined new methods/concepts of information security Wrote advisories that were released and posted within the sec ...
Careers in Forensics
... An entomologist studies life cycles of insects to help determine the approximate time of death of a victim in a murder investigation. ...
... An entomologist studies life cycles of insects to help determine the approximate time of death of a victim in a murder investigation. ...
Something Security
... • Common critiques: (i) over-extended definitions ‘meaningless’ and/or ‘too complicated’ (eg for comparative risk assessment, executive handling); (ii) critique of ‘securitization’ • BUT: - main risks for West objectively moving down the spectrum; non-securitizing can also mean ignoring/downplaying ...
... • Common critiques: (i) over-extended definitions ‘meaningless’ and/or ‘too complicated’ (eg for comparative risk assessment, executive handling); (ii) critique of ‘securitization’ • BUT: - main risks for West objectively moving down the spectrum; non-securitizing can also mean ignoring/downplaying ...