XML: Part - Houston Community College System
... • Can provide the information in a publicly accessible directory, called a Certificate Repository (CR) • Some organizations set up a Registration Authority (RA) to handle some CA, tasks such as processing certificate requests and authenticating users Security+ Guide to Network Security Fundamentals, ...
... • Can provide the information in a publicly accessible directory, called a Certificate Repository (CR) • Some organizations set up a Registration Authority (RA) to handle some CA, tasks such as processing certificate requests and authenticating users Security+ Guide to Network Security Fundamentals, ...
Novel Approach to Discover Effective Patterns For Text Mining
... assignment strategy. The optimal feature set size for wordbased indexing was found to be surprisingly low (10 to 15 features) despite the large training sets. The extraction of new text features by syntactic analysis and feature clustering was investigated on the Reuters data set. Syntactic indexing ...
... assignment strategy. The optimal feature set size for wordbased indexing was found to be surprisingly low (10 to 15 features) despite the large training sets. The extraction of new text features by syntactic analysis and feature clustering was investigated on the Reuters data set. Syntactic indexing ...
Guidelines for unfair means
... midterm, end term, quizzes, practical which are considered as part of assessment/evaluation by the instructor while awarding grades in a subject. Unfair means shall include the following: 1. During examination time having in possession or access to a. Any paper, book, note or any other unauthorised ...
... midterm, end term, quizzes, practical which are considered as part of assessment/evaluation by the instructor while awarding grades in a subject. Unfair means shall include the following: 1. During examination time having in possession or access to a. Any paper, book, note or any other unauthorised ...
Green-Aware Security
... 5. the integration of third-party Web application can lead to many possible hazards, and creates new security breaches; 6. to provide the proper degree of interactivity and sophisticated user-interfaces, specific design patterns are adopted. But, they increase the risk of attacks such as request for ...
... 5. the integration of third-party Web application can lead to many possible hazards, and creates new security breaches; 6. to provide the proper degree of interactivity and sophisticated user-interfaces, specific design patterns are adopted. But, they increase the risk of attacks such as request for ...
DATA SHEET PMEG1020EV Ultra low V MEGA Schottky barrier
... Export control ⎯ This document as well as the item(s) described herein may be subject to export control regulations. Export might require a prior authorization from national authorities. Quick reference data ⎯ The Quick reference data is an extract of the product data given in the Limiting values an ...
... Export control ⎯ This document as well as the item(s) described herein may be subject to export control regulations. Export might require a prior authorization from national authorities. Quick reference data ⎯ The Quick reference data is an extract of the product data given in the Limiting values an ...
ppt
... 9. Why might you use client IP affinity instead of no affinity for load balancing? What is the trade off? If you have resources which are cached at the server (e.g. an SSL session) which are expensive to re-establish at a fresh server, you may use client IP affinity to insure that requests from the ...
... 9. Why might you use client IP affinity instead of no affinity for load balancing? What is the trade off? If you have resources which are cached at the server (e.g. an SSL session) which are expensive to re-establish at a fresh server, you may use client IP affinity to insure that requests from the ...
DATA SHEET PMEG2015EV Low V MEGA Schottky barrier
... any of these products are for illustrative purposes only. NXP Semiconductors makes no representation or warranty that such applications will be suitable for the specified use without further testing or modification. ...
... any of these products are for illustrative purposes only. NXP Semiconductors makes no representation or warranty that such applications will be suitable for the specified use without further testing or modification. ...
slides - CIS @ Temple University
... This course explains these components of a search engine in more detail Often many possible approaches and techniques for a given component ◦ Focus is on the most important alternatives ◦ explain a small number of approaches in detail rather ...
... This course explains these components of a search engine in more detail Often many possible approaches and techniques for a given component ◦ Focus is on the most important alternatives ◦ explain a small number of approaches in detail rather ...
DATA SHEET PMEG2010EV Low V MEGA Schottky barrier
... Export control ⎯ This document as well as the item(s) described herein may be subject to export control regulations. Export might require a prior authorization from national authorities. ...
... Export control ⎯ This document as well as the item(s) described herein may be subject to export control regulations. Export might require a prior authorization from national authorities. ...
Fractions at Key Stage 2
... Put children into groups of 5and challenge them to share 9 A4 sheets of paper equally between them. Discuss the different solutions to the problem, for example one group might distribute one sheet to each person and then cut the remaining four in half and give each person a half then do the same wit ...
... Put children into groups of 5and challenge them to share 9 A4 sheets of paper equally between them. Discuss the different solutions to the problem, for example one group might distribute one sheet to each person and then cut the remaining four in half and give each person a half then do the same wit ...
the accompanying resource
... Put children into groups of 5and challenge them to share 9 A4 sheets of paper equally between them. Discuss the different solutions to the problem, for example one group might distribute one sheet to each person and then cut the remaining four in half and give each person a half then do the same wit ...
... Put children into groups of 5and challenge them to share 9 A4 sheets of paper equally between them. Discuss the different solutions to the problem, for example one group might distribute one sheet to each person and then cut the remaining four in half and give each person a half then do the same wit ...
Lesson 2
... say it is either 0, 1, 2, 3, 4 or 5. What you want to get them to understand is that any tens digit will work as long as the ones digit is 0, 2, 4, 6, or 8.) Is 72 an even number? (Yes) Why? (The ones digit is a 2.) Is 35,356 an even number? (Yes.) Why? (The ones digit is a 6.) Is 445 an even number ...
... say it is either 0, 1, 2, 3, 4 or 5. What you want to get them to understand is that any tens digit will work as long as the ones digit is 0, 2, 4, 6, or 8.) Is 72 an even number? (Yes) Why? (The ones digit is a 2.) Is 35,356 an even number? (Yes.) Why? (The ones digit is a 6.) Is 445 an even number ...
Solution to In-Text Exercise 20.3: First we compute the marginal
... Solving for S, we obtain S = 35. A store’s marginal benefit is greater than marginal cost when S < 35 and less than marginal cost when S > 35. If security is left to the independent decisions of the stores, they will provide 35 person-hours of security patrols in total. If the total were less than 3 ...
... Solving for S, we obtain S = 35. A store’s marginal benefit is greater than marginal cost when S < 35 and less than marginal cost when S > 35. If security is left to the independent decisions of the stores, they will provide 35 person-hours of security patrols in total. If the total were less than 3 ...
view presentation
... Application breaches today are primarily the result of poor coding, yet security embedded in SDLC processes continues to be an afterthought Simply maintaining patches on COTS can address a number of vulnerabilities, however, few organizations stay ahead of the curve ...
... Application breaches today are primarily the result of poor coding, yet security embedded in SDLC processes continues to be an afterthought Simply maintaining patches on COTS can address a number of vulnerabilities, however, few organizations stay ahead of the curve ...
DATA SHEET BAT960 Schottky barrier diode
... Export control ⎯ This document as well as the item(s) described herein may be subject to export control regulations. Export might require a prior authorization from national authorities. ...
... Export control ⎯ This document as well as the item(s) described herein may be subject to export control regulations. Export might require a prior authorization from national authorities. ...
Lecture1
... 0 Steganalysis is about developing techniques that can analyze text, images, video and detect hidden messages - May use data mining techniques to detect hidden patters 0 Steganograophy makes the task of the Cyber crime expert difficult as he/she ahs to analyze for hidden information - Communication ...
... 0 Steganalysis is about developing techniques that can analyze text, images, video and detect hidden messages - May use data mining techniques to detect hidden patters 0 Steganograophy makes the task of the Cyber crime expert difficult as he/she ahs to analyze for hidden information - Communication ...
Global Information Assurance Certification (GIAC) develops and administers the premier
... GSE: The Certification Like No Other Only the true security elite hold a GIAC Security Expert certification (GSE). For good reason. It’s the most prestigious, most demanding certification in the information security industry. The GSE’s performancebased, hands-on nature sets it apart from any other c ...
... GSE: The Certification Like No Other Only the true security elite hold a GIAC Security Expert certification (GSE). For good reason. It’s the most prestigious, most demanding certification in the information security industry. The GSE’s performancebased, hands-on nature sets it apart from any other c ...
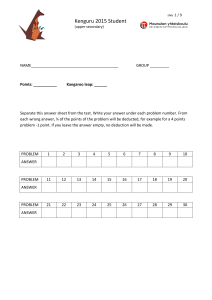
Kenguru 2015 Student
... Jasper wants to represent the same data with a circular chart using the same colours. What would the circular chart look like? ...
... Jasper wants to represent the same data with a circular chart using the same colours. What would the circular chart look like? ...