policies - NY Capital Region Chapter
... Application Firewalls look inside network information sent and determine if packet is permitted or not, and then take configured action. WebSense will block all Nazi sites ...
... Application Firewalls look inside network information sent and determine if packet is permitted or not, and then take configured action. WebSense will block all Nazi sites ...
International Telecommunication Union
... Scope: The project will develop a standard for high speed (>100 Mbps at the physical layer) communication devices via alternating current electric power lines, so called Broadband over Power Line (BPL) devices. The standard will use trannsmission frequencies below 100 MHz. This standard will be usab ...
... Scope: The project will develop a standard for high speed (>100 Mbps at the physical layer) communication devices via alternating current electric power lines, so called Broadband over Power Line (BPL) devices. The standard will use trannsmission frequencies below 100 MHz. This standard will be usab ...
NPTF - FINAL RATE SETTING
... If we receive a report of a system that is scanning the network, we often find it is connecting to a specific command-and-control server and we can then put that IP address information into Arbor and find other hosts that are connecting to it. This allows us to proactively identify compromised hosts ...
... If we receive a report of a system that is scanning the network, we often find it is connecting to a specific command-and-control server and we can then put that IP address information into Arbor and find other hosts that are connecting to it. This allows us to proactively identify compromised hosts ...
Slide 1
... Advanced modeling of reinforcement learning, which configure service coverage and system capacity dynamically to balance traffic loads among cells by being aware of the system ...
... Advanced modeling of reinforcement learning, which configure service coverage and system capacity dynamically to balance traffic loads among cells by being aware of the system ...
Networks
... Network Media LANs use a variety of media to carry network signals. Twisted pair–Two insulated wires twisted around each other. The same type of wire as that used for telephones. Coaxial cable– Consists of an insulated center wire surrounded by a layer of braided wire. The same type of wire as ...
... Network Media LANs use a variety of media to carry network signals. Twisted pair–Two insulated wires twisted around each other. The same type of wire as that used for telephones. Coaxial cable– Consists of an insulated center wire surrounded by a layer of braided wire. The same type of wire as ...
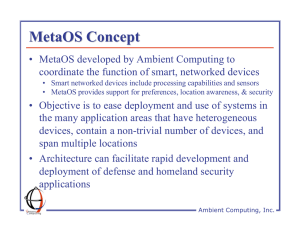
MetaOS Concept • MetaOS developed by Ambient Computing to
... • Hub (kernel) manages domain, communicates with devices or programs via edge software (device drivers) using publish-subscribe approach • Hub, edge, and device are typically on different network-connected processors • XML messages used for various registration, notification, operation, and informat ...
... • Hub (kernel) manages domain, communicates with devices or programs via edge software (device drivers) using publish-subscribe approach • Hub, edge, and device are typically on different network-connected processors • XML messages used for various registration, notification, operation, and informat ...
Community Wireless Services: how to solve the business and
... And delivers services and applications facilitated by a large cache at each node and an intelligent network ...
... And delivers services and applications facilitated by a large cache at each node and an intelligent network ...
Chapter 9
... Securing Traffic with IPSec IPSec allows us to protect our network from within IPSec secures the IP protocol IPSec has two principle goals: To protect the contents of IP packets To provide defense against network attacks through packet filtering and the enforcement of trusted communicatio ...
... Securing Traffic with IPSec IPSec allows us to protect our network from within IPSec secures the IP protocol IPSec has two principle goals: To protect the contents of IP packets To provide defense against network attacks through packet filtering and the enforcement of trusted communicatio ...
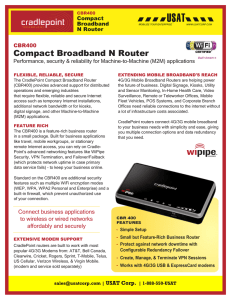
CBR400 Compact Broadband N Router
... Offices need reliable connections to the internet without a lot of infrastructure costs associated. CradlePoint routers connect 4G/3G mobile broadband to your business needs with simplicity and ease, giving you multiple connection options and data redundancy that you need. ...
... Offices need reliable connections to the internet without a lot of infrastructure costs associated. CradlePoint routers connect 4G/3G mobile broadband to your business needs with simplicity and ease, giving you multiple connection options and data redundancy that you need. ...
Extended Learning Module C
... packet of data to all other connected devices A switch has more intelligence than a hub and can forward data to a specified device. The switch is used within a given network to move information. Unlike a switch, a router (or bridge) is a special communications processor used to route packets of data ...
... packet of data to all other connected devices A switch has more intelligence than a hub and can forward data to a specified device. The switch is used within a given network to move information. Unlike a switch, a router (or bridge) is a special communications processor used to route packets of data ...
powerpoint
... lab (and all of the ICT I labs) are considered LAN segments because the computers in each lab are connected together in a kind of smaller network. • The computer workstations in each ICT I lab and each ICT II lab are connected by ethernet cables. The cables plug into the network card in each compute ...
... lab (and all of the ICT I labs) are considered LAN segments because the computers in each lab are connected together in a kind of smaller network. • The computer workstations in each ICT I lab and each ICT II lab are connected by ethernet cables. The cables plug into the network card in each compute ...
Dark Matter and Dark Energy - Hitoshi Murayama Home Page
... 8AB Course Center (B5, B10 Hearst Field Annex) 7ABC Course Center (A20, A25 Hearst Field Annex) ...
... 8AB Course Center (B5, B10 Hearst Field Annex) 7ABC Course Center (A20, A25 Hearst Field Annex) ...
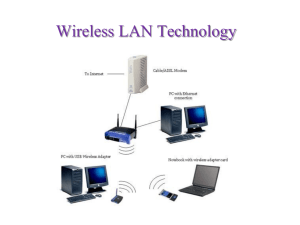
5 10 Wired Network Basics - Web Design John Cabot University
... Slower than wired networks Security concerns ...
... Slower than wired networks Security concerns ...
PPT - CS
... response to incoming messages. • It is important that the server know for sure who the client is! • The simple solution is to send the user name and password with every request ...
... response to incoming messages. • It is important that the server know for sure who the client is! • The simple solution is to send the user name and password with every request ...
Understanding and Installing Firewalls
... users who valued openness for sharing and collaboration was ended by a number of major internet security breaches which occurred in the late 1980s: Clifford Stoll's discovery of German spies tampering with his system. Bill Cheswick's "Evening with Berferd" 1992 in which he set up a simple electronic ...
... users who valued openness for sharing and collaboration was ended by a number of major internet security breaches which occurred in the late 1980s: Clifford Stoll's discovery of German spies tampering with his system. Bill Cheswick's "Evening with Berferd" 1992 in which he set up a simple electronic ...
Introduction - Personal Web Pages
... – Trojan war story (Trojan horse): USB keys (Digital photo frame and SCADA) – Corrupted internal worker – Vulnerabilities of protocols or security mechanisms (security patch has problems) – By-passing protection walls – Backdoors for systems (Linux password) – Known attacks ignored (push and poll) ...
... – Trojan war story (Trojan horse): USB keys (Digital photo frame and SCADA) – Corrupted internal worker – Vulnerabilities of protocols or security mechanisms (security patch has problems) – By-passing protection walls – Backdoors for systems (Linux password) – Known attacks ignored (push and poll) ...
Reading Organizer Instructor Version
... or knowledge. This information is sent to advertisers or others on the Internet and can include passwords and account numbers. Spyware is usually installed unknowingly when downloading a file, installing another program or clicking a popup. It can slow down a computer and make changes to internal se ...
... or knowledge. This information is sent to advertisers or others on the Internet and can include passwords and account numbers. Spyware is usually installed unknowingly when downloading a file, installing another program or clicking a popup. It can slow down a computer and make changes to internal se ...
sec overview
... Network error messages do not make IP more reliable Essential when diagnosing network problems Each Message includes a type field and related code field Threat - bogus ICMP messages or broadcast storms when ...
... Network error messages do not make IP more reliable Essential when diagnosing network problems Each Message includes a type field and related code field Threat - bogus ICMP messages or broadcast storms when ...
IEEE 802.16 Standard
... – Buildings equipped with subscriber and base stations, SS & BS – Users connect to SS via conventional network ...
... – Buildings equipped with subscriber and base stations, SS & BS – Users connect to SS via conventional network ...
Slide 1
... • The goal of TridiumTalk is to share with the Niagara community timely content on sales, products and technical topics. Each session will last between 45-60 minutes and will be a mix of presentation, demonstrations and Q&A. • This session and past sessions will be posted on our community web site a ...
... • The goal of TridiumTalk is to share with the Niagara community timely content on sales, products and technical topics. Each session will last between 45-60 minutes and will be a mix of presentation, demonstrations and Q&A. • This session and past sessions will be posted on our community web site a ...
communications and networks - Home
... Competencies (Page 2 of 2) Describe different types of networks, including local area, metropolitan area, and wide area networks Describe network architectures, including configurations and strategies Describe organizational uses of Internet technologies, including intranets, extranets, and firewal ...
... Competencies (Page 2 of 2) Describe different types of networks, including local area, metropolitan area, and wide area networks Describe network architectures, including configurations and strategies Describe organizational uses of Internet technologies, including intranets, extranets, and firewal ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.