DIR-657 A1 Sales Guide - D-Link
... Family Home Users who want to a better performance to share media streaming and data transmission simultaneously. ...
... Family Home Users who want to a better performance to share media streaming and data transmission simultaneously. ...
Curriculum Vitae - ASU People Search
... Implemented Automated and Precise Cross Site Script (XSS) generator for Web Application testing in python. Simulated malicious web server client to identify vulnerabilities in code of python based Web Server. Solved catch the flag challenges including directory traversal, buffer overflow and P ...
... Implemented Automated and Precise Cross Site Script (XSS) generator for Web Application testing in python. Simulated malicious web server client to identify vulnerabilities in code of python based Web Server. Solved catch the flag challenges including directory traversal, buffer overflow and P ...
SDconnect - Sklad66.com
... acoustic signal warns the mechanic if he leaves the radio range of the workshop with the mobile unit. The unit is also equipped with an improved selfdiagnosis feature. This enables the mechanic to better detect possible malfunctions of the multiplexer. Simplicity of Use SDconnect is easy to operate ...
... acoustic signal warns the mechanic if he leaves the radio range of the workshop with the mobile unit. The unit is also equipped with an improved selfdiagnosis feature. This enables the mechanic to better detect possible malfunctions of the multiplexer. Simplicity of Use SDconnect is easy to operate ...
End to end and up and down
... End to end signalling • MAC layer doesn’t have the end to end picture • Lowest layer that can have end to end signalling is the network • Connections are established at network layer, with requirements pushed downwards into the MAC using SBM ...
... End to end signalling • MAC layer doesn’t have the end to end picture • Lowest layer that can have end to end signalling is the network • Connections are established at network layer, with requirements pushed downwards into the MAC using SBM ...
- clicktechsolution.com
... Remote antennas connected using an antenna cable. Coax cable used for RF has a high signal loss, should not be mounted more than a 1 or 2 meters away from the device. Placement: consider building construction, ceiling height, obstacles, and aesthetics. Different materials (cement, steel) have ...
... Remote antennas connected using an antenna cable. Coax cable used for RF has a high signal loss, should not be mounted more than a 1 or 2 meters away from the device. Placement: consider building construction, ceiling height, obstacles, and aesthetics. Different materials (cement, steel) have ...
“The thin-client model is an alternative to the traditional approach of
... and costs of keeping your desktop systems hardware up-to-date so that you can run the latest software, you can see the potential benefits of only needing to update one PC and observe the effects on all the others! Thin-client systems are also generally more secure and reliable than their fat-client ...
... and costs of keeping your desktop systems hardware up-to-date so that you can run the latest software, you can see the potential benefits of only needing to update one PC and observe the effects on all the others! Thin-client systems are also generally more secure and reliable than their fat-client ...
NETWORK PLANNING TASK FORCE “FY `06 FALL SESSIONS”
... Establish a supported firewall product, matched with for-fee, vendor-provided firewall administrator training. Provide a for-fee firewall consulting service to select and configure a firewall. Publish a list of approved and qualified firewall consulting services. ...
... Establish a supported firewall product, matched with for-fee, vendor-provided firewall administrator training. Provide a for-fee firewall consulting service to select and configure a firewall. Publish a list of approved and qualified firewall consulting services. ...
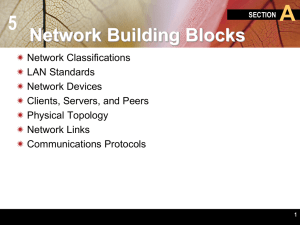
Communications and Networks
... nodes, and so forth, forming a treelike structure. • Also known as a hierarchical network ...
... nodes, and so forth, forming a treelike structure. • Also known as a hierarchical network ...
Hacking Overview Pres.
... reptile.rug.ac.be/~coder/sniffit/sniffit.html To gain access to packages, use spoofed ARP (Address Resolution Protocol) to reroute traffic. ...
... reptile.rug.ac.be/~coder/sniffit/sniffit.html To gain access to packages, use spoofed ARP (Address Resolution Protocol) to reroute traffic. ...
No Slide Title
... – runs on all devices inside network – carries local connectivity information – provides • shortest path route through network • default route for non-BGP speakers • relatively fast convergence time (~1 sec) ...
... – runs on all devices inside network – carries local connectivity information – provides • shortest path route through network • default route for non-BGP speakers • relatively fast convergence time (~1 sec) ...
Chapter07.pdf
... Web sites that need to be found at the same address – Dynamic IP address are used by most other users and are temporarily assigned by your ISP • Dial‐up users get a new IP every time • DSL/Cable users have an always‐on connection with the IP address remaining the same for days, weeks, or months ...
... Web sites that need to be found at the same address – Dynamic IP address are used by most other users and are temporarily assigned by your ISP • Dial‐up users get a new IP every time • DSL/Cable users have an always‐on connection with the IP address remaining the same for days, weeks, or months ...
3 - network - Web Design John Cabot University
... Slower than wired networks Security concerns ...
... Slower than wired networks Security concerns ...
Understanding Networks II
... infrared light instead of cables or wires to connect computers or other devices. • Connections are made using a wireless NIC, which includes an antenna to send and receive signals. • Wireless devices can communicate directly, or they can connect to a LAN by way of a wireless access point (AP). ...
... infrared light instead of cables or wires to connect computers or other devices. • Connections are made using a wireless NIC, which includes an antenna to send and receive signals. • Wireless devices can communicate directly, or they can connect to a LAN by way of a wireless access point (AP). ...
Basic Networking Hardware
... A local area network that transmits over the air typically in an unlicensed frequency such as the 2.4GHz band. A wireless LAN does not require lining up devices for line of sight transmission. Wireless access points (base stations) are connected to an Ethernet hub or server and transmit a radio freq ...
... A local area network that transmits over the air typically in an unlicensed frequency such as the 2.4GHz band. A wireless LAN does not require lining up devices for line of sight transmission. Wireless access points (base stations) are connected to an Ethernet hub or server and transmit a radio freq ...
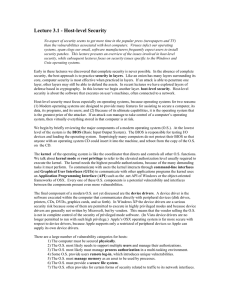
Lecture 3.1 - Host
... core, computer security is most effective when practiced in layers. If an attack is able to penetrate one layer, other layers may still be able to defend the assets. In recent lectures we have explored layers of defense based in cryptography. In this lecture we begin another layer. host-level securi ...
... core, computer security is most effective when practiced in layers. If an attack is able to penetrate one layer, other layers may still be able to defend the assets. In recent lectures we have explored layers of defense based in cryptography. In this lecture we begin another layer. host-level securi ...
IEEE 802.11 based WLANs
... Basic Service Set (BSS) (aka “cell”) in infrastructure mode hub, switch contains: or router wireless hosts access point (AP): base station AP ad hoc mode: hosts only ...
... Basic Service Set (BSS) (aka “cell”) in infrastructure mode hub, switch contains: or router wireless hosts access point (AP): base station AP ad hoc mode: hosts only ...
The Top Seven Security Problems of 802.11 Wireless
... not using strong security measures, such as VPNs or 802.1x. Problem #2: "Rogue" Access Points Easy access to wireless LANs is coupled with easy deployment. When combined, these two characteristics can cause headaches for network administrators and security officers. Any user can run to a nearby comp ...
... not using strong security measures, such as VPNs or 802.1x. Problem #2: "Rogue" Access Points Easy access to wireless LANs is coupled with easy deployment. When combined, these two characteristics can cause headaches for network administrators and security officers. Any user can run to a nearby comp ...
Chapter 7
... Web sites that need to be found at the same address – Dynamic IP address are used by most other users and are temporarily assigned by your ISP • Dial-up users get a new IP every time • DSL/Cable users have an always-on connection with the IP address remaining the same for days, weeks, or months ...
... Web sites that need to be found at the same address – Dynamic IP address are used by most other users and are temporarily assigned by your ISP • Dial-up users get a new IP every time • DSL/Cable users have an always-on connection with the IP address remaining the same for days, weeks, or months ...
Digital IDs
... to network services and resources. • List the Internet security safeguards that protect networks by detecting intrusions and defeating attacks. • Define the methods for digitally signing and encrypting network transmissions. • Describe publishing a Web securely with the SFTP protocol. ...
... to network services and resources. • List the Internet security safeguards that protect networks by detecting intrusions and defeating attacks. • Define the methods for digitally signing and encrypting network transmissions. • Describe publishing a Web securely with the SFTP protocol. ...
Document
... • Allows the computer system to communicate with the network • Every device that is connected to the LAN will need a NIC, for example, computer, printer and scanner. • It take the data sent by your computer – stores it in its own memory locations, – then adapts it ensuring it follows the communicati ...
... • Allows the computer system to communicate with the network • Every device that is connected to the LAN will need a NIC, for example, computer, printer and scanner. • It take the data sent by your computer – stores it in its own memory locations, – then adapts it ensuring it follows the communicati ...
Intrusion Detection Prevention Systems
... Prepared by: Abeer Saif Supervised by: Dr. Lo’ai Tawalbeh ...
... Prepared by: Abeer Saif Supervised by: Dr. Lo’ai Tawalbeh ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.