Why Cryptography is Harder Than It Looks
... prevented • Targeted attacks can only be withstood up to a point • The problems with cryptography are not in the algorithms and protocols, but the implementation – Weakness are found at human interaction level ...
... prevented • Targeted attacks can only be withstood up to a point • The problems with cryptography are not in the algorithms and protocols, but the implementation – Weakness are found at human interaction level ...
Forms of Network Attacks
... Randomize the attention of your internal Information Systems staff so that they do not see the intrusion immediately, which allows the attacker to make more attacks during the diversion. Send invalid data to applications or network services, which causes abnormal termination or behavior of the appli ...
... Randomize the attention of your internal Information Systems staff so that they do not see the intrusion immediately, which allows the attacker to make more attacks during the diversion. Send invalid data to applications or network services, which causes abnormal termination or behavior of the appli ...
security protocols for wireless sensor network
... inserting a new node into a network which has been cloned from an existing node, such cloning being a relatively simple task with current sensor node hardware. • This new node can act exactly like the old node or it can have some extra behavior, such as transmitting information of interest directly ...
... inserting a new node into a network which has been cloned from an existing node, such cloning being a relatively simple task with current sensor node hardware. • This new node can act exactly like the old node or it can have some extra behavior, such as transmitting information of interest directly ...
Factsheet - KFSensor
... Intrusion detection plays a vital role in ensuring the integrity of a network's security. Network intrusion detection systems (NIDS) have long been seen as the most effective means of detecting attacks. However they do have significant weaknesses. The increasing quantity and diversity of legitimate ...
... Intrusion detection plays a vital role in ensuring the integrity of a network's security. Network intrusion detection systems (NIDS) have long been seen as the most effective means of detecting attacks. However they do have significant weaknesses. The increasing quantity and diversity of legitimate ...
Module Title: Code: Level: Credits:
... Upon completion of this module, students will be able to: 1. Have a good understanding of the OSI Reference Model and in particular have a good knowledge of Layers 1-3. 2. Analyze the requirements for a given organizational structure and select the most appropriate networking architecture and techno ...
... Upon completion of this module, students will be able to: 1. Have a good understanding of the OSI Reference Model and in particular have a good knowledge of Layers 1-3. 2. Analyze the requirements for a given organizational structure and select the most appropriate networking architecture and techno ...
Wireless
... few bytes of the frame body. The receiving station uses this IV along with the shared secret key supplied by the user of the receiving station to decrypt the payload portion of the frame body. In most cases the sending station will use a different IV for each frame (this is not required by the 802.1 ...
... few bytes of the frame body. The receiving station uses this IV along with the shared secret key supplied by the user of the receiving station to decrypt the payload portion of the frame body. In most cases the sending station will use a different IV for each frame (this is not required by the 802.1 ...
Wireless N 150Mbps - Atlantis-Land
... WebShare 242 WN supports 4 x 10/100 Mbps auto-negotiating Fast Ethernet ports for connection to your PC or LAN and downstream (with built-in ADSL2+ modem) rate up to 24Mbps. Power by NAT technology, dozens of network users can surf on the Internet and share the ADSL connection simultaneously by usin ...
... WebShare 242 WN supports 4 x 10/100 Mbps auto-negotiating Fast Ethernet ports for connection to your PC or LAN and downstream (with built-in ADSL2+ modem) rate up to 24Mbps. Power by NAT technology, dozens of network users can surf on the Internet and share the ADSL connection simultaneously by usin ...
4th Edition: Chapter 1 - United States Naval Academy
... access network at transmission rate R link transmission rate, aka link capacity, aka link bandwidth packet transmission ...
... access network at transmission rate R link transmission rate, aka link capacity, aka link bandwidth packet transmission ...
CIT 016 Review for Final
... cannot enter the secure network For extra security, some networks use a DMZ with two firewalls The types of servers that should be located in the DMZ include: ...
... cannot enter the secure network For extra security, some networks use a DMZ with two firewalls The types of servers that should be located in the DMZ include: ...
Network Access Control
... If your machine is not running a Windows operating system, please consult with the Support Center on how to rebuild for your operating system. To recover from this compromise it is necessary to completely rebuild the computer. When a computer is compromised in this manner, anything on the system can ...
... If your machine is not running a Windows operating system, please consult with the Support Center on how to rebuild for your operating system. To recover from this compromise it is necessary to completely rebuild the computer. When a computer is compromised in this manner, anything on the system can ...
Security of the Internet of Things - Cyber
... - but the current security mechanisms are still in the research stage [95-99] ...
... - but the current security mechanisms are still in the research stage [95-99] ...
MetroFi Cupertino - Wireless Internet Institute
... Overlapping/common objectives of serving residents & the community with affordable broadband service led to success Regardless of the business model, the service will be perceived as a partnership by the community – therefore, taking a proactive and collaborative stance will be of mutual benefit and ...
... Overlapping/common objectives of serving residents & the community with affordable broadband service led to success Regardless of the business model, the service will be perceived as a partnership by the community – therefore, taking a proactive and collaborative stance will be of mutual benefit and ...
TIM158-2013-Lectures 10-11
... • N+1 means one backup per type • N+N means one backup per component ...
... • N+1 means one backup per type • N+N means one backup per component ...
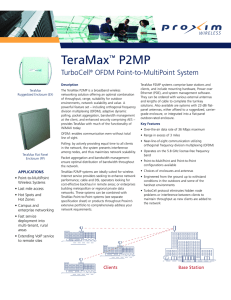
TeraMax™ P2MP
... • Campus and enterprise networking • Fast service deployment into multi-tenant, rural areas • Extending VoIP service to remote sites ...
... • Campus and enterprise networking • Fast service deployment into multi-tenant, rural areas • Extending VoIP service to remote sites ...
INET01 - BNRG - University of California, Berkeley
... • Push services towards edges: caches, content distribution, localization • Construct service networks from third parties or confederations: greater support among mobile operators than conventional ISPs • Manage redirection, not routes: key to service-level peering • New applications-specific protoc ...
... • Push services towards edges: caches, content distribution, localization • Construct service networks from third parties or confederations: greater support among mobile operators than conventional ISPs • Manage redirection, not routes: key to service-level peering • New applications-specific protoc ...
Charting Plus System Specifications
... Charting Plus data at the speeds required by a busy office. MediNotes recommends the use of 802.11a or g (54+ MBs) to increase the data transfer bandwidth, or the use of terminal services or Citrix with slower wireless systems. Supported Backup Types In the event that you must submit your database t ...
... Charting Plus data at the speeds required by a busy office. MediNotes recommends the use of 802.11a or g (54+ MBs) to increase the data transfer bandwidth, or the use of terminal services or Citrix with slower wireless systems. Supported Backup Types In the event that you must submit your database t ...
Charles Whitfield Jr
... Monitoring the network’s performance, operating and maintaining a diagnostic modem network and performing first level corrective maintenance for related communication hardware and software problems. ...
... Monitoring the network’s performance, operating and maintaining a diagnostic modem network and performing first level corrective maintenance for related communication hardware and software problems. ...
Networking - The Art of Zombie
... Routers connect computers and peripherals to one another, either through Cat 5e Ethernet cables or through a wireless connection. The modem connects your router to the internet. Once you connect your router to the modem, you're then able to share that internet connection with all of the computers on ...
... Routers connect computers and peripherals to one another, either through Cat 5e Ethernet cables or through a wireless connection. The modem connects your router to the internet. Once you connect your router to the modem, you're then able to share that internet connection with all of the computers on ...
View File
... e.g., by finding user names and passwords Trojan horses: Pretend to be a utility. Convince users to install on PC. Spyware: Collect personal information Hoax: Use emotion to propagate, e.g., child's last wish. Trap Door: Undocumented entry point for debugging purposes Logic Bomb: Instructions that t ...
... e.g., by finding user names and passwords Trojan horses: Pretend to be a utility. Convince users to install on PC. Spyware: Collect personal information Hoax: Use emotion to propagate, e.g., child's last wish. Trap Door: Undocumented entry point for debugging purposes Logic Bomb: Instructions that t ...
slides
... Bluetooth enables a variety of devices, including cell phones, PDAs, wireless keyboards and mice, PCs, and printers, to interact wirelessly with each other within a small 30-foot (10-meter) area. In addition to the links shown, Bluetooth can be used to network similar devices to send data from one P ...
... Bluetooth enables a variety of devices, including cell phones, PDAs, wireless keyboards and mice, PCs, and printers, to interact wirelessly with each other within a small 30-foot (10-meter) area. In addition to the links shown, Bluetooth can be used to network similar devices to send data from one P ...
the importance of securing workstations
... a user in Accounting will still be able to spoof the address of someone else in Accounting, but he shouldn’t be able to use an IP address that belongs to Marketing, HR, or IT. System administrators may need to access workstations throughout the organization. If possible, this access should be restri ...
... a user in Accounting will still be able to spoof the address of someone else in Accounting, but he shouldn’t be able to use an IP address that belongs to Marketing, HR, or IT. System administrators may need to access workstations throughout the organization. If possible, this access should be restri ...
AGENDA
... WiNG Express only require access points • Controller code included in every access point • No controller appliance required • No access point licenses required • APs include limited lifetime warranty Comparison of existing competitive 11ac offerings June 2014 ...
... WiNG Express only require access points • Controller code included in every access point • No controller appliance required • No access point licenses required • APs include limited lifetime warranty Comparison of existing competitive 11ac offerings June 2014 ...
David Cowen, CISSP
... - Co author Hacking Exposed: Computer Forensics - Co author Anti Hacker Toolkit, 3 rd edition -Expert in Unix security, Windows Security, web security and network security penetration studies -Extensive security experience in the following systems: Windows NT (3.51 and 4.0), Windows 2000, Windows 95 ...
... - Co author Hacking Exposed: Computer Forensics - Co author Anti Hacker Toolkit, 3 rd edition -Expert in Unix security, Windows Security, web security and network security penetration studies -Extensive security experience in the following systems: Windows NT (3.51 and 4.0), Windows 2000, Windows 95 ...
Chapter 1 Exploring the Network
... network infrastructure can vary greatly in terms of size, number of users, and number and types of services that are supported on it. The network infrastructure must grow and adjust to support the way the network is used. The routing and switching platform is the foundation of any network ...
... network infrastructure can vary greatly in terms of size, number of users, and number and types of services that are supported on it. The network infrastructure must grow and adjust to support the way the network is used. The routing and switching platform is the foundation of any network ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.