Computer Communication Networks HW8 2009/01/08 39. A network
... 39. A network on the Internet has a subnet mask of 255.255.240.0. What is the maximum number of hosts it can handle? Ans: The mask is 20 bits long, so the network part is 20 bits. The remaining 12 bits are for the host, so 4096 host addresses exist. 45. Many companies have a policy of having two (or ...
... 39. A network on the Internet has a subnet mask of 255.255.240.0. What is the maximum number of hosts it can handle? Ans: The mask is 20 bits long, so the network part is 20 bits. The remaining 12 bits are for the host, so 4096 host addresses exist. 45. Many companies have a policy of having two (or ...
WHY NEED NETWORKING? NETWORKING NETWORK
... that occur when traditional backbone routers can't meet the demands of fast, switched networks. ...
... that occur when traditional backbone routers can't meet the demands of fast, switched networks. ...
No Slide Title
... Length of cable runs (affects type of cabling) Cable runs must not violate fire breaks Plenum cable required if hot air returns ...
... Length of cable runs (affects type of cabling) Cable runs must not violate fire breaks Plenum cable required if hot air returns ...
Network Layer Security
... end system/router can authenticate user/app prevent address spoofing attacks by tracking ...
... end system/router can authenticate user/app prevent address spoofing attacks by tracking ...
Wireless Networks and Mobile Communication Systems NET 332D
... Microwave is also used for satellite communications. › Radio Range: Frequencies in the range 30 MHz to 1 GHz are suitable for omnidirectional applications. › The infrared portion of the spectrum. This covers, roughly, from 3 × 1011 to 2 × 1014 Hz. Infrared is useful in local point-to-point and multi ...
... Microwave is also used for satellite communications. › Radio Range: Frequencies in the range 30 MHz to 1 GHz are suitable for omnidirectional applications. › The infrared portion of the spectrum. This covers, roughly, from 3 × 1011 to 2 × 1014 Hz. Infrared is useful in local point-to-point and multi ...
01-Intro
... Tap a phone line - but this requires a very special modem. Use a “Trojan Horse” or “Bot” program, with a “key catcher”to record key stokes. Social Engineering - phone or email and pretend to be “PC support.” ...
... Tap a phone line - but this requires a very special modem. Use a “Trojan Horse” or “Bot” program, with a “key catcher”to record key stokes. Social Engineering - phone or email and pretend to be “PC support.” ...
Overview of Operating Systems Security Features
... Overview of Operating Systems Security Features - LINUX Introduction A key advantage of LINUX desktop operating system (OS) is its low cost and ease of customization to environment and/or solutions specific requirements, but this can also present security risks. A LINUX desktop that is part of the G ...
... Overview of Operating Systems Security Features - LINUX Introduction A key advantage of LINUX desktop operating system (OS) is its low cost and ease of customization to environment and/or solutions specific requirements, but this can also present security risks. A LINUX desktop that is part of the G ...
Information Security - National University of Sciences and
... someone else to access/take control of your system • Facilitates hacking of system • Hacking: To enter somebody system/account in an illegal way ...
... someone else to access/take control of your system • Facilitates hacking of system • Hacking: To enter somebody system/account in an illegal way ...
UNIT 5. Instruction to Computer Networks
... memory and hard disk space than clients • Run Network Operating System that can manage not only data, but also users, groups, security, and applications on the network • Servers often have a more stringent requirement on its performance and reliability ...
... memory and hard disk space than clients • Run Network Operating System that can manage not only data, but also users, groups, security, and applications on the network • Servers often have a more stringent requirement on its performance and reliability ...
computer networks
... • Nodes that gather information they sense. • Can be part of cars or phones, etc.. Or may be small separate devices. • Example: car gather data: location, speed, vibration, and fuel efficiency and upload this information to a database. • Those data can help find potholes, plan trips around congested ...
... • Nodes that gather information they sense. • Can be part of cars or phones, etc.. Or may be small separate devices. • Example: car gather data: location, speed, vibration, and fuel efficiency and upload this information to a database. • Those data can help find potholes, plan trips around congested ...
When you have two or more computers connected to each
... security or sharing rights. If many computers are connected a hub may be used to connect all these computers and/or devices. Client/Server - Probably the most common LAN types used by companies today, they are called "client/server" because they consist of the server (which stores the files or runs ...
... security or sharing rights. If many computers are connected a hub may be used to connect all these computers and/or devices. Client/Server - Probably the most common LAN types used by companies today, they are called "client/server" because they consist of the server (which stores the files or runs ...
The Network - Communication Management Services
... > 416 MHz Intel ® PXA 270 processor > 128 MB Flash / 64 SD RAM – New Windows® Memory Architecture > MSM 6500 chipset by Qualcomm® ...
... > 416 MHz Intel ® PXA 270 processor > 128 MB Flash / 64 SD RAM – New Windows® Memory Architecture > MSM 6500 chipset by Qualcomm® ...
iwlan: an implementation model for high density smart intranet
... application which is an instant messaging tool was integrated into iWLAN model for SMART communication for paperless transfers.The Access points interfaces with the controllers and RADIUS server for internet access. The wireless access point and RADIUS server fill the roles of the 802.11 authenticat ...
... application which is an instant messaging tool was integrated into iWLAN model for SMART communication for paperless transfers.The Access points interfaces with the controllers and RADIUS server for internet access. The wireless access point and RADIUS server fill the roles of the 802.11 authenticat ...
shuffling:improving data security in ad hoc networks based
... routing. In this, the original message to secure is split into shares that are encrypted and combined then transmitted along different disjointed existing paths between sender and receiver. Even if an attacker succeeds to obtain one or more transmitted shares, the probability that the original messa ...
... routing. In this, the original message to secure is split into shares that are encrypted and combined then transmitted along different disjointed existing paths between sender and receiver. Even if an attacker succeeds to obtain one or more transmitted shares, the probability that the original messa ...
Computer network
... Internet Connections • There are various technologies available that you can use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A ...
... Internet Connections • There are various technologies available that you can use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A ...
Wireless Security
... Uses CRC for internal integrity protection. Uses RC4 to encrypt network traffic. ...
... Uses CRC for internal integrity protection. Uses RC4 to encrypt network traffic. ...
Convergence Technology Chapter Objectives
... Comon types of NICs Purpose and operation of hubs and repeaters Purpose and operation of bridges and swtiches How routers connect dissimilar networks Explain how to connect LAN or WANs via a modem What components are necessary for access and carrier network connectivity ...
... Comon types of NICs Purpose and operation of hubs and repeaters Purpose and operation of bridges and swtiches How routers connect dissimilar networks Explain how to connect LAN or WANs via a modem What components are necessary for access and carrier network connectivity ...
module 2 network security unit 1
... network, either for the purpose of attacking them or for network security assessment. Scanning procedures, such as ping sweeps and port scans, return information about which IP addresses map to live hosts that are active on the Internet and what services they offer. Another scanning method, inverse ...
... network, either for the purpose of attacking them or for network security assessment. Scanning procedures, such as ping sweeps and port scans, return information about which IP addresses map to live hosts that are active on the Internet and what services they offer. Another scanning method, inverse ...
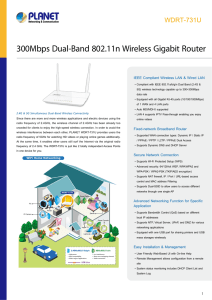
300Mbps Dual-Band 802.11n Wireless Gigabit Router
... The WDRT-731U supports NAT function allowing multiple users to access Internet via a single legal IP. It also provides Virtual Server for the specific LAN PC to act as an application server and offer certain service to the clients on the Internet. In addition, the powerful firewall protects your Int ...
... The WDRT-731U supports NAT function allowing multiple users to access Internet via a single legal IP. It also provides Virtual Server for the specific LAN PC to act as an application server and offer certain service to the clients on the Internet. In addition, the powerful firewall protects your Int ...
Review Questions
... 17. A variation of NAT that is commonly found on home routers is _______. A. Network address IP transformation (NAIPT) B. Port address translation (PAT) C. Network proxy translation (NPT) D. Subnet transformation (ST) 18. If a device is determined to have an out-of-date virus signature file then Net ...
... 17. A variation of NAT that is commonly found on home routers is _______. A. Network address IP transformation (NAIPT) B. Port address translation (PAT) C. Network proxy translation (NPT) D. Subnet transformation (ST) 18. If a device is determined to have an out-of-date virus signature file then Net ...
Plum
... client/server networks where users login in to access the server. The server is run by an administrator who ensures that backups are done on a regular basis. • Business may also use intranets or private web sites not accessible to the public in order to make information and files available online. ...
... client/server networks where users login in to access the server. The server is run by an administrator who ensures that backups are done on a regular basis. • Business may also use intranets or private web sites not accessible to the public in order to make information and files available online. ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.