CommView for WiFi
... WEP key is required to decrypt WEP-encrypted packets; a WPA passphrase is required for decrypting WPA/WPA2encrypted packets in PSK (Pre-Shared Key) mode. ...
... WEP key is required to decrypt WEP-encrypted packets; a WPA passphrase is required for decrypting WPA/WPA2encrypted packets in PSK (Pre-Shared Key) mode. ...
Tonga Institute of Higher Education IT 141
... It detects collision, deletes the colliding signals, resets network and prepares to retransmit data How fast? Original carried data over a coaxial cable bus topology at 10 Mbps. Today, up to 40 or 100 Gbps Ethernet is popular because it is easy to understand, available almost everywhere, allows fl ...
... It detects collision, deletes the colliding signals, resets network and prepares to retransmit data How fast? Original carried data over a coaxial cable bus topology at 10 Mbps. Today, up to 40 or 100 Gbps Ethernet is popular because it is easy to understand, available almost everywhere, allows fl ...
Westermo Group
... All connections need to be authenticated before accepted All data passing through the tunnel is encrypted IPsec VPN via untrusted Network ...
... All connections need to be authenticated before accepted All data passing through the tunnel is encrypted IPsec VPN via untrusted Network ...
Deployed and Emerging Security Systems for the Internet
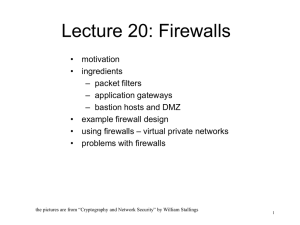
... packet filtering and application layer gateway makes firewall more effective • multiple layers of defense protect against the compromise of one router/gateway – multiple routers allow NAT-based network hiding ...
... packet filtering and application layer gateway makes firewall more effective • multiple layers of defense protect against the compromise of one router/gateway – multiple routers allow NAT-based network hiding ...
The Internet and Security
... – Look for ports/applications that should not be open – ISS, freeware from www.nessus.org ...
... – Look for ports/applications that should not be open – ISS, freeware from www.nessus.org ...
Wireless Communications Research Overview
... IEEE standards often adopted Process fraught with inefficiencies and conflicts ...
... IEEE standards often adopted Process fraught with inefficiencies and conflicts ...
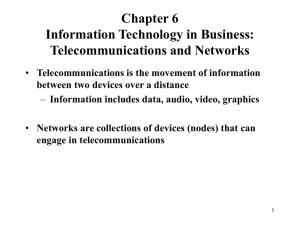
Networks
... connected together by what are called gateways - these make the system act as if it was one huge network. Many networks in industry, business, higher education and government institutions are all connected to the Internet although anybody can now get connected to the system with the appropriate hard ...
... connected together by what are called gateways - these make the system act as if it was one huge network. Many networks in industry, business, higher education and government institutions are all connected to the Internet although anybody can now get connected to the system with the appropriate hard ...
Intrusion Detection Systems
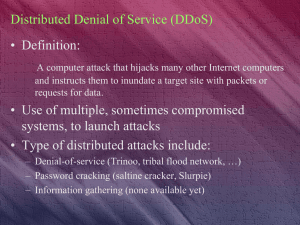
... - victim stores number sent by user - attacker never finished 3 way handshake - attacker initiates large number of SYN requests - victim reaches its half-open connection limit - Denial of service - Prevention – modification to handshake protocol to be stateless ...
... - victim stores number sent by user - attacker never finished 3 way handshake - attacker initiates large number of SYN requests - victim reaches its half-open connection limit - Denial of service - Prevention – modification to handshake protocol to be stateless ...
Wireless LAN
... – Can be used with either Win95/98 or Win NT – Must be used on a computer with both Wireless and wired network connections – Can use remote administration to set parameters or monitor network ...
... – Can be used with either Win95/98 or Win NT – Must be used on a computer with both Wireless and wired network connections – Can use remote administration to set parameters or monitor network ...
ECE 117-2426
... and has high quality equal‐length bus routing in timing critical areas. The production environment and quality control are the same as those of modern high‐speed motherboards. ...
... and has high quality equal‐length bus routing in timing critical areas. The production environment and quality control are the same as those of modern high‐speed motherboards. ...
05. Example Networks..
... Wireless LANs: 802.11 • IEEE committee that standardized the wired LANs was given the task of drawing up a wireless LAN standard – result 802.11 • Common known as WiFi • The proposed standard had to work in two modes: – In the presence of a base station – In the absence of a base station ...
... Wireless LANs: 802.11 • IEEE committee that standardized the wired LANs was given the task of drawing up a wireless LAN standard – result 802.11 • Common known as WiFi • The proposed standard had to work in two modes: – In the presence of a base station – In the absence of a base station ...
Chapter6
... point (AP) Basic Service Set (BSS) (aka “cell”) in infrastructure mode contains: wireless hosts access point (AP): base station ad hoc mode: hosts only ...
... point (AP) Basic Service Set (BSS) (aka “cell”) in infrastructure mode contains: wireless hosts access point (AP): base station ad hoc mode: hosts only ...
for networks
... Wireless Networks • In order to communicate with a network using a wireless device, you must be close enough to an access point (AP). The access point is a device that is connected to a wired network. – If a household has a wired connection to the Internet (cable or DSL) then wireless devices can a ...
... Wireless Networks • In order to communicate with a network using a wireless device, you must be close enough to an access point (AP). The access point is a device that is connected to a wired network. – If a household has a wired connection to the Internet (cable or DSL) then wireless devices can a ...
Here are the PowerPoint slides with links - Auto
... their competitors walked into one of their offices and installed a plugbot (theplugbot.com). The plugbot was able to sniff a domain password and send it over the built-in cellular modem. From there, the attacker established remote access to the corporate data server. A few months later, Widget Corp' ...
... their competitors walked into one of their offices and installed a plugbot (theplugbot.com). The plugbot was able to sniff a domain password and send it over the built-in cellular modem. From there, the attacker established remote access to the corporate data server. A few months later, Widget Corp' ...
Enterprise Wireless LAN (WLAN) Management
... – Careless employee brings AP from home, attaches it to the corporate network – Bypasses security measures like 802.1x, allows unauthorized clients to gain access – Once rogue network is installed, physical proximity is no longer needed ...
... – Careless employee brings AP from home, attaches it to the corporate network – Bypasses security measures like 802.1x, allows unauthorized clients to gain access – Once rogue network is installed, physical proximity is no longer needed ...
report_698430005
... Benefits expected by the operator deploying an IMS infrastructure ◦ To use a common functional infrastructure for services control ◦ Allows the operator to better control resources, especially significant in the mobile domain for packet switching services ◦ Service triggering toward application serv ...
... Benefits expected by the operator deploying an IMS infrastructure ◦ To use a common functional infrastructure for services control ◦ Allows the operator to better control resources, especially significant in the mobile domain for packet switching services ◦ Service triggering toward application serv ...
Today`s Topics
... Star Topology: uses a central wiring device (hub) Ring Topology: all nodes are attached in a circular wiring arrangement ...
... Star Topology: uses a central wiring device (hub) Ring Topology: all nodes are attached in a circular wiring arrangement ...
FirstNet: Tech Terms 101
... Broadband: refers to the wide bandwidth characteristics of a transmission medium, such as coaxial cable, optical fiber, twisted pair, DSL local telephone networks or wireless, and its ability to transport multiple signals or traffic types simultaneously. Wireless: the transfer of information (e.g.: ...
... Broadband: refers to the wide bandwidth characteristics of a transmission medium, such as coaxial cable, optical fiber, twisted pair, DSL local telephone networks or wireless, and its ability to transport multiple signals or traffic types simultaneously. Wireless: the transfer of information (e.g.: ...
Local area Network
... single VLAN, they can share resources and bandwidth as if they were connected to the same segment. The resources of other departments can be invisible to the marketing VLAN members, accessible to all, or accessible only to specified individuals, at the IT manager's discretion. ...
... single VLAN, they can share resources and bandwidth as if they were connected to the same segment. The resources of other departments can be invisible to the marketing VLAN members, accessible to all, or accessible only to specified individuals, at the IT manager's discretion. ...
the agenda - CambridgeWireless
... these new network models promise nothing less than a revolution not only in the way networks are architected and operated, and in the types of services they can offer, but even in the structure and ecosystems of the industry itself. This talk takes a forward view of how these new possibilities can b ...
... these new network models promise nothing less than a revolution not only in the way networks are architected and operated, and in the types of services they can offer, but even in the structure and ecosystems of the industry itself. This talk takes a forward view of how these new possibilities can b ...
4121 Access Point 802.11b Ethernet-Speed Price-Performance Wireless Networking
... and throughput. As signal strength decreases the transmit rate also decreases, ensuring maximum range while maintaining data integrity. High-speed roaming additionally ensures Spectrum24 High Rate clients seek the best possible data rate for fastest throughput. Mobile IP, International Roaming ...
... and throughput. As signal strength decreases the transmit rate also decreases, ensuring maximum range while maintaining data integrity. High-speed roaming additionally ensures Spectrum24 High Rate clients seek the best possible data rate for fastest throughput. Mobile IP, International Roaming ...
Network Edge Protection: A Technical Deep
... many logons. Our goal was to make it so that once an employee gains access to our intranet home page, he or she doesn’t have to log on again to use another application.” – Wendy Lou, IT Security Architect, Northwest Airlines ...
... many logons. Our goal was to make it so that once an employee gains access to our intranet home page, he or she doesn’t have to log on again to use another application.” – Wendy Lou, IT Security Architect, Northwest Airlines ...
comparisons of wired and wireless networks: a review
... between different devices and computer systems. Most wired networks use Ethernet cables to transfer data between connected PCs. In a small wired network, a single router may be used to connect all the computers. Larger networks often involve multiple routers or switches that connect to each other. O ...
... between different devices and computer systems. Most wired networks use Ethernet cables to transfer data between connected PCs. In a small wired network, a single router may be used to connect all the computers. Larger networks often involve multiple routers or switches that connect to each other. O ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.