Networks 1 (LAN)
... Explain the advantages of networking stand- alone into a local area network Describe the hardware needed to connect stand-alone computers into a LAN, including hub\switches, wireless access points Explain the different roles of computers in a client server and peer-topeer network Describe, using dia ...
... Explain the advantages of networking stand- alone into a local area network Describe the hardware needed to connect stand-alone computers into a LAN, including hub\switches, wireless access points Explain the different roles of computers in a client server and peer-topeer network Describe, using dia ...
Basic Service Set (BSS)
... • ESS stations must have the same SSID • The BSSID is the “name” of the BSS (not same as SSID) • APs can be positioned so that cells overlap to facilitate roaming – Wireless devices choose AP based on signal strength – Stations going from one BSS to another will deal with Handoff Wired LAN ...
... • ESS stations must have the same SSID • The BSSID is the “name” of the BSS (not same as SSID) • APs can be positioned so that cells overlap to facilitate roaming – Wireless devices choose AP based on signal strength – Stations going from one BSS to another will deal with Handoff Wired LAN ...
Assignment-3
... networks, they learn which are the fastest routes and use them first The router looks at the destination address of each packet sent from the source location. It checks its table to see where this address is there and sends each packet to that address The router has two basic jobs: To make sur ...
... networks, they learn which are the fastest routes and use them first The router looks at the destination address of each packet sent from the source location. It checks its table to see where this address is there and sends each packet to that address The router has two basic jobs: To make sur ...
Wireless Network Elements[edit source | editbeta]
... WPAN for interconnecting a headset to a laptop. ZigBee also supports WPAN applications.[4] Wi-Fi PANs are becoming commonplace (2010) as equipment designers start to integrate Wi-Fi into a variety of consumer electronic devices. Intel "My WiFi" and Windows 7 "virtual Wi-Fi" capabilities have made Wi ...
... WPAN for interconnecting a headset to a laptop. ZigBee also supports WPAN applications.[4] Wi-Fi PANs are becoming commonplace (2010) as equipment designers start to integrate Wi-Fi into a variety of consumer electronic devices. Intel "My WiFi" and Windows 7 "virtual Wi-Fi" capabilities have made Wi ...
CS 494/594 Computer and Network Security - UTK-EECS
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
CS 494/594 Computer and Network Security - UTK-EECS
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
Network Topology - Department of Computing
... affect other communications in the network Disadv: Failure of hub/switch can bring the network down, also called SPF( Single Point of Failure) ...
... affect other communications in the network Disadv: Failure of hub/switch can bring the network down, also called SPF( Single Point of Failure) ...
pres
... Packet Capturing (pcap) • Kernel modules – passively capture network traffic and pass them to user space processes through a well-defined Application Programming Interface (API) ...
... Packet Capturing (pcap) • Kernel modules – passively capture network traffic and pass them to user space processes through a well-defined Application Programming Interface (API) ...
Networking - Jui-Sheng (Rayson) Chou, PE, Ph.D.
... to share via a message to facilitate communication ...
... to share via a message to facilitate communication ...
Wireless Expands M D to More of the Plant
... limited only by imagination, budget, and cybersecurity concerns. Most anything in M&D that can be hardwired can now be done with wireless (Fig 1), even if plants are not quite ready to give up “the landline.” Probably the best way to think about wireless at the plant level is this: You don’t have to ...
... limited only by imagination, budget, and cybersecurity concerns. Most anything in M&D that can be hardwired can now be done with wireless (Fig 1), even if plants are not quite ready to give up “the landline.” Probably the best way to think about wireless at the plant level is this: You don’t have to ...
Network Engineer
... platform voice, video and data. Administration of an enterprise network environment including the installation, monitoring, maintenance, support, and optimization of all network hardware, software, and LAN/WAN links. Implement and manage Cisco products including, Cisco switches, Cisco Enterpr ...
... platform voice, video and data. Administration of an enterprise network environment including the installation, monitoring, maintenance, support, and optimization of all network hardware, software, and LAN/WAN links. Implement and manage Cisco products including, Cisco switches, Cisco Enterpr ...
NT Security Overview
... organization will have access to the network. In most businesses or organizations there are employees, staff, management and officers. Some can be trusted to access all of the network and others do not have the trust level to access any of the network. The administrator must decide who has access an ...
... organization will have access to the network. In most businesses or organizations there are employees, staff, management and officers. Some can be trusted to access all of the network and others do not have the trust level to access any of the network. The administrator must decide who has access an ...
Chapter 10: Electronic Commerce Security
... today as Caesar Cyphers. The simplest replaces A with B, B with C etc. This is called a one-rotate code. The following is encrypted using a simple Caesar rotation cypher. See if you can decrypt it: ...
... today as Caesar Cyphers. The simplest replaces A with B, B with C etc. This is called a one-rotate code. The following is encrypted using a simple Caesar rotation cypher. See if you can decrypt it: ...
Blue Asterisk template - Connected Security Expo
... Who has access to what, when and how they can have access? There are many IoT devices within the system with access interfaces: cameras, switches, routers, radios, UPS’s, PDUs, NVRs, DVRs, clients, servers, etc. ...
... Who has access to what, when and how they can have access? There are many IoT devices within the system with access interfaces: cameras, switches, routers, radios, UPS’s, PDUs, NVRs, DVRs, clients, servers, etc. ...
Week_Thirteen_ppt
... • As a result, you can have up to twelve access points set to different channels in the same area without them interfering with each other. • This makes access point channel assignment much easier and significantly increases the throughput the wireless LAN can deliver within a given area. • In addit ...
... • As a result, you can have up to twelve access points set to different channels in the same area without them interfering with each other. • This makes access point channel assignment much easier and significantly increases the throughput the wireless LAN can deliver within a given area. • In addit ...
Printed_Networks and Protocols CE00997-3 WEEK 6..
... spectrum to provide access to a network, typically covering only the network operator's own property. Typically Wi-Fi is used by an end user to access their own network, which may or may not be connected to the Internet. If WiMAX provides services analogous to a cellphone, Wi-Fi is more analogous to ...
... spectrum to provide access to a network, typically covering only the network operator's own property. Typically Wi-Fi is used by an end user to access their own network, which may or may not be connected to the Internet. If WiMAX provides services analogous to a cellphone, Wi-Fi is more analogous to ...
what is a network?
... Server has to send a file to a computer the file passes through the Hub. The Hub broadcasts the file to all the computers, but only the computer it was intended for accepts the file. Switch – A Switch looks like a Hub and does the same job. The advantage of a Switch is that the switch has a processo ...
... Server has to send a file to a computer the file passes through the Hub. The Hub broadcasts the file to all the computers, but only the computer it was intended for accepts the file. Switch – A Switch looks like a Hub and does the same job. The advantage of a Switch is that the switch has a processo ...
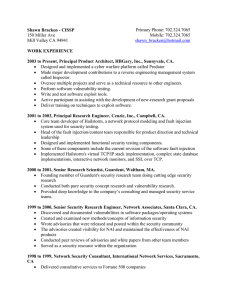
Shawn Bracken - CISSP103 Chester StMenlo Park, CA 94025
... Supported HP-UX Trusted Systems secure accounting/auditing and kernel configuration Our team was the 3rd layer support known as "backline" which handled the more difficult and time-consuming calls. Most customers were large production systems requiring high uptime. 1997 to 1998, Network Securi ...
... Supported HP-UX Trusted Systems secure accounting/auditing and kernel configuration Our team was the 3rd layer support known as "backline" which handled the more difficult and time-consuming calls. Most customers were large production systems requiring high uptime. 1997 to 1998, Network Securi ...
PPT
... - internet – cloud - messages can be seen/modified by anyone • Not best model for all security issues • In security analysis - Adversary can only read messages directly addressed to him/her - can spoof addresses ...
... - internet – cloud - messages can be seen/modified by anyone • Not best model for all security issues • In security analysis - Adversary can only read messages directly addressed to him/her - can spoof addresses ...
File - IT Essentials Pc: Hardware/ software
... 6. Explain what is Phishing and give an example: Phishing is where the attacker pretends to represent a legitimate outside organization, such as a bank. 7. How is a virus transferred to another computer? email, file transfers, and instant messaging. 8. Explain how does a virus typically work? The v ...
... 6. Explain what is Phishing and give an example: Phishing is where the attacker pretends to represent a legitimate outside organization, such as a bank. 7. How is a virus transferred to another computer? email, file transfers, and instant messaging. 8. Explain how does a virus typically work? The v ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.





![Wireless Network Elements[edit source | editbeta]](http://s1.studyres.com/store/data/004984970_1-755673b30cfbd69af14b55cbbc12e8e5-300x300.png)