LAB 1 Basic Networking Commands
... and alter network configuration. To see all, type hh ntcmds.chm in your terminal window, and to see all options for a command line, type –h, /?, -help, or ? ...
... and alter network configuration. To see all, type hh ntcmds.chm in your terminal window, and to see all options for a command line, type –h, /?, -help, or ? ...
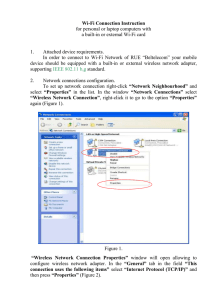
инструкция
... PLEASE NOTE: Should you choose connection to the wireless network “byfly WIFI” and the message “No or limited connectivity” is displayed in the window containing the list of available wireless network connections, or the authorization page fails to download when entering the necessary address in th ...
... PLEASE NOTE: Should you choose connection to the wireless network “byfly WIFI” and the message “No or limited connectivity” is displayed in the window containing the list of available wireless network connections, or the authorization page fails to download when entering the necessary address in th ...
Chapter 1
... Scalability – scales from small to large networks. Can add almost unlimited number of hosts. Flexibility – Can easily change IP configurations when the infrastructure changes. ...
... Scalability – scales from small to large networks. Can add almost unlimited number of hosts. Flexibility – Can easily change IP configurations when the infrastructure changes. ...
Wired (Ethernet) Instructions for Windows XP
... 10. From the Trusted Root Certification Authorities list, make sure Entrust.net Secure Server Certification Authority is checked. 11. Choose Secured password (EAP-MSCHAP v2) for the Authentication Method. Make sure the box labeled Enable Fast Reconnect is checked. Click on the Configure... button. ...
... 10. From the Trusted Root Certification Authorities list, make sure Entrust.net Secure Server Certification Authority is checked. 11. Choose Secured password (EAP-MSCHAP v2) for the Authentication Method. Make sure the box labeled Enable Fast Reconnect is checked. Click on the Configure... button. ...
A threat can be any person, object, or event that, if realized, could
... networks from authorized network users, inadvertently opening doors for intruders. Incorrectly configured APs: Radio waves broadcast by wireless base stations are relatively powerful, and residential neighbors or adjacent businesses may connect to each other's wireless networks. Many APs are initial ...
... networks from authorized network users, inadvertently opening doors for intruders. Incorrectly configured APs: Radio waves broadcast by wireless base stations are relatively powerful, and residential neighbors or adjacent businesses may connect to each other's wireless networks. Many APs are initial ...
1. Computer Networks - missions
... A router translates information from one network to another Wireless LANs Some networks are wireless. Wireless LANs use high frequency radio signals, infrared light beams, or lasers to communicate between the workstations and the file server or hubs. Wi-Fi Wireless Fidelity synonym for wireless ...
... A router translates information from one network to another Wireless LANs Some networks are wireless. Wireless LANs use high frequency radio signals, infrared light beams, or lasers to communicate between the workstations and the file server or hubs. Wi-Fi Wireless Fidelity synonym for wireless ...
Networking
... • They do what they can – Anti Virus, Perimeter Firewall, compliance requirements • Viruses and malware are spreading and evolving, attack patterns are changing • Since 2008 viruses have taken off, come in through mobile device with corporate email • Do it yourself hacker kits, identify what they wa ...
... • They do what they can – Anti Virus, Perimeter Firewall, compliance requirements • Viruses and malware are spreading and evolving, attack patterns are changing • Since 2008 viruses have taken off, come in through mobile device with corporate email • Do it yourself hacker kits, identify what they wa ...
Wired communication standards solutions
... between e-mail servers and used by e-mail client software to send messages to the server, but never used to retrieve e-mail from a server? A IMAP4 B POP3 C ...
... between e-mail servers and used by e-mail client software to send messages to the server, but never used to retrieve e-mail from a server? A IMAP4 B POP3 C ...
PPT network components
... Additional Information about Firewalls • Most home network routers have built in firewall. • The term “firewall” originated from firefighting, where a firewall is a barrier established to prevent the spread of a fire. • A firewall works with the proxy server making request on behalf of workstation ...
... Additional Information about Firewalls • Most home network routers have built in firewall. • The term “firewall” originated from firefighting, where a firewall is a barrier established to prevent the spread of a fire. • A firewall works with the proxy server making request on behalf of workstation ...
44_ExploringNetworkProperties
... Often called a redirector because it can redirect commands to a remote computer on the network. Each manufacturer of network operating systems have their own client components. ...
... Often called a redirector because it can redirect commands to a remote computer on the network. Each manufacturer of network operating systems have their own client components. ...
Hacking
... Applications on a system use ports to listen for network traffic or send it out. 216 ports available, some for known services such as http (80), ftp, ... Port scans send various type of IP packages to target on different ports. Reaction tells them whether the port is open (an application liste ...
... Applications on a system use ports to listen for network traffic or send it out. 216 ports available, some for known services such as http (80), ftp, ... Port scans send various type of IP packages to target on different ports. Reaction tells them whether the port is open (an application liste ...
Networks Local area network
... • WAN – A WAN (Wide Area Network) as the name implies allows you to connect to other computers over a wider area (i.e. the whole ...
... • WAN – A WAN (Wide Area Network) as the name implies allows you to connect to other computers over a wider area (i.e. the whole ...
Test 3 Emerge Terms
... Bluetooth: enables digital devices to communicate directly with each other wirelessly over short distances. Cascading Style Sheets (CSS): allows easy application of visual styles for fonts, colors, layouts, and other page attributes to create visual themes for webpages and sites. Cellular Network: r ...
... Bluetooth: enables digital devices to communicate directly with each other wirelessly over short distances. Cascading Style Sheets (CSS): allows easy application of visual styles for fonts, colors, layouts, and other page attributes to create visual themes for webpages and sites. Cellular Network: r ...
EFF / TCPA Roundtable - Oxford Internet Institute
... copyright bill (S) off to jail with the president of Upenn show down and maybe stop the value of the net the de-evolution of the net to TV ...
... copyright bill (S) off to jail with the president of Upenn show down and maybe stop the value of the net the de-evolution of the net to TV ...
Document
... • 5. Open a browser in the General PC and input http://192.168.11.1 (your gateway IP address). You will see the login window for the Buffalo Configuration Interface. • 6. Input the username and password to login. The default user name is root. Refer to the figure in the next page. ...
... • 5. Open a browser in the General PC and input http://192.168.11.1 (your gateway IP address). You will see the login window for the Buffalo Configuration Interface. • 6. Input the username and password to login. The default user name is root. Refer to the figure in the next page. ...
Chapter 36 Network Management & SNMP
... – Eg. to encode an integer, ASN.1 sends a pair of values: a ...
... – Eg. to encode an integer, ASN.1 sends a pair of values: a ...
Mobile Communication
... Network measurement and Management Ad hoc and sensor networks Multimedia QoS and traffic Management Network protocols for Mobile Networks Internetworking of WLAN & Cellular Networks ...
... Network measurement and Management Ad hoc and sensor networks Multimedia QoS and traffic Management Network protocols for Mobile Networks Internetworking of WLAN & Cellular Networks ...
Digital Literacy – Computer Basics – Common Computer Terminology
... A group of computers and associated devices that are linked together to facilitate sharing information is called a ___________. The main computer on a network is called a _________. You use a ______________to access the hardware and software on a network. ___________are commonly used as communicatio ...
... A group of computers and associated devices that are linked together to facilitate sharing information is called a ___________. The main computer on a network is called a _________. You use a ______________to access the hardware and software on a network. ___________are commonly used as communicatio ...
Networking Your Office
... become a communications highway for millions of users. The Internet was initially restricted to military and academic institutions, but now it is for any and all forms of information and commerce. Internet Web sites now provide personal, educational, political, and economic resources to anyone. ...
... become a communications highway for millions of users. The Internet was initially restricted to military and academic institutions, but now it is for any and all forms of information and commerce. Internet Web sites now provide personal, educational, political, and economic resources to anyone. ...
What is the internet - New Mexico State University
... Who Pays for It? No one pays for "it"; there is no Internet, Inc. that collects fees from all Internet networks or users. Everyone pays for their part. The NSF pays for NSFNET. NASA pays for the NASA Science Internet. Networks get together and decide how to connect themselves together and f ...
... Who Pays for It? No one pays for "it"; there is no Internet, Inc. that collects fees from all Internet networks or users. Everyone pays for their part. The NSF pays for NSFNET. NASA pays for the NASA Science Internet. Networks get together and decide how to connect themselves together and f ...
1 Course Outline Computing Science Department Faculty of Science
... Students learn about computer network design principles and concepts, network architecture, Open Systems Interconnection (OSI) model, error detection and recovery, local area networks, bridges, routers and gateways, network naming and addressing, routing protocols, internetworking, wireless networks ...
... Students learn about computer network design principles and concepts, network architecture, Open Systems Interconnection (OSI) model, error detection and recovery, local area networks, bridges, routers and gateways, network naming and addressing, routing protocols, internetworking, wireless networks ...
Network Architectures - Computing Sciences
... conversation with an internal device, thus limiting an attacker’s options to cause mischief ...
... conversation with an internal device, thus limiting an attacker’s options to cause mischief ...
Midterm Test - 18Jul08 - Solutions
... 27. The ____ Worldwide Interoperability for Microwave Access (WiMax) standard, comes in two flavors. a. 802.3 c. 802.11 b. 802.5 d. 802.16 28. Coaxial cable is often called “________coax ____________” for short. 29. The type of data transmission that occurs in a computer bus is called ____ transmis ...
... 27. The ____ Worldwide Interoperability for Microwave Access (WiMax) standard, comes in two flavors. a. 802.3 c. 802.11 b. 802.5 d. 802.16 28. Coaxial cable is often called “________coax ____________” for short. 29. The type of data transmission that occurs in a computer bus is called ____ transmis ...
Presentation
... • The Network Opera4ons Centers Provide a variety of services. The Chennai server, for example provides Billing and Authen4ca4on Services, NMS services monitoring devices across our hotels as ...
... • The Network Opera4ons Centers Provide a variety of services. The Chennai server, for example provides Billing and Authen4ca4on Services, NMS services monitoring devices across our hotels as ...