What is the internet
... Who Pays for It? No one pays for "it"; there is no Internet, Inc. that collects fees from all Internet networks or users. Everyone pays for their part. The NSF pays for NSFNET. NASA pays for the NASA Science Internet. Networks get together and decide how to connect themselves together and f ...
... Who Pays for It? No one pays for "it"; there is no Internet, Inc. that collects fees from all Internet networks or users. Everyone pays for their part. The NSF pays for NSFNET. NASA pays for the NASA Science Internet. Networks get together and decide how to connect themselves together and f ...
LANs and WLANs
... • Wireless networks are much more susceptible to unauthorized access and use than wired networks • LAN jacking, or war driving, is the practice of intercepting wireless signals by cruising through an area ...
... • Wireless networks are much more susceptible to unauthorized access and use than wired networks • LAN jacking, or war driving, is the practice of intercepting wireless signals by cruising through an area ...
Firewalls
... prevent denial of service attacks: SYN flooding: attacker establishes many bogus TCP connections, no resources left for “real” connections prevent illegal modification/access of internal data. e.g., attacker replaces CIA’s homepage with something else allow only authorized access to inside netwo ...
... prevent denial of service attacks: SYN flooding: attacker establishes many bogus TCP connections, no resources left for “real” connections prevent illegal modification/access of internal data. e.g., attacker replaces CIA’s homepage with something else allow only authorized access to inside netwo ...
What is an IP address?
... Use of different physical media Preservation of address space Security ...
... Use of different physical media Preservation of address space Security ...
Network Security - University of Northampton
... Router Considerations The router is the very first line of defense. It provides packet routing, It can also be configured to block or filter the forwarding of packet types that are known to be vulnerable or used maliciously, such as ICMP ...
... Router Considerations The router is the very first line of defense. It provides packet routing, It can also be configured to block or filter the forwarding of packet types that are known to be vulnerable or used maliciously, such as ICMP ...
System Security - Wright State engineering
... IP address: a.b.c.d, 4-bytes. IP packet contains the IP addresses of sender and receiver. Everything in the clear. IP spoofing replaces the IP address of (usually) the sender or (in rare cases) the destination with a different address. Services that authenticate based on the IP addresses are v ...
... IP address: a.b.c.d, 4-bytes. IP packet contains the IP addresses of sender and receiver. Everything in the clear. IP spoofing replaces the IP address of (usually) the sender or (in rare cases) the destination with a different address. Services that authenticate based on the IP addresses are v ...
CHAPTER 7 - McGraw Hill Higher Education
... channels into a single service Peer-to-Peer (P2P)—A computer network that relies on the computing power and bandwidth of the participants in the network rather than a centralized server Voice over IP (VoIP)—Uses IP technology to transmit telephone calls Internet Protocol TV (IPTV)—Distributes ...
... channels into a single service Peer-to-Peer (P2P)—A computer network that relies on the computing power and bandwidth of the participants in the network rather than a centralized server Voice over IP (VoIP)—Uses IP technology to transmit telephone calls Internet Protocol TV (IPTV)—Distributes ...
Document
... connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer digital da ...
... connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer digital da ...
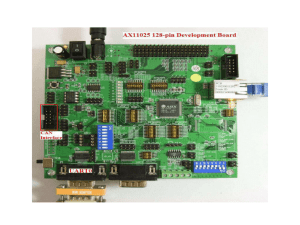
Assignment-3
... segments. It generally contains more intelligence than a hub. It operates in full-duplex mode at ...
... segments. It generally contains more intelligence than a hub. It operates in full-duplex mode at ...
ITGS
... disk, and other machines are able to access them • With more than a few users, the lack of a server to aid in security and storage becomes a problem ...
... disk, and other machines are able to access them • With more than a few users, the lack of a server to aid in security and storage becomes a problem ...
TCP/IP Concepts, Addressing and Services
... With subnetting, you can divide your network into smaller networks by using some of the host ID bits (in the IP address) as part of Network ID. It is achieved by the clever use of Subnet mask. Routers are used to send traffic between two subnets. These devices are identified as Gateway address. ...
... With subnetting, you can divide your network into smaller networks by using some of the host ID bits (in the IP address) as part of Network ID. It is achieved by the clever use of Subnet mask. Routers are used to send traffic between two subnets. These devices are identified as Gateway address. ...
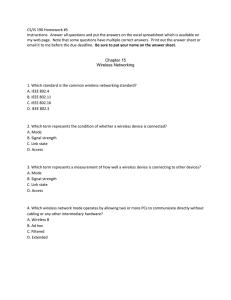
Homework #5 was due April 3
... 8. Which term defines the most basic infrastructure mode network – a BSS of one WAP and one or more wireless nodes? A. Basic Service Set (BSS) B. Basic Service Set Identifier (BSSID) C. Independent Basic Service Set (IBSS) D. Extended Service Set (ESS) ...
... 8. Which term defines the most basic infrastructure mode network – a BSS of one WAP and one or more wireless nodes? A. Basic Service Set (BSS) B. Basic Service Set Identifier (BSSID) C. Independent Basic Service Set (IBSS) D. Extended Service Set (ESS) ...
CH 8 – Review - WordPress.com
... Botnets are created using self-propagating software, which means that the software can – reproduce itself A good defense to prevent your computer from becoming a zombie is to – install and run antivirus software Bluetooth is an – electronics standard The typical range for consumer Bluetooth devices ...
... Botnets are created using self-propagating software, which means that the software can – reproduce itself A good defense to prevent your computer from becoming a zombie is to – install and run antivirus software Bluetooth is an – electronics standard The typical range for consumer Bluetooth devices ...
New 802.11 Security Standards
... SSID (service set identifier) – Identifies the 802.11 devices that belong to a Basic Service Set (BSS). – A BSS is analogous to a LAN segment in wired terms – SSID is meant as a method to identify what Service Set you want to communicate with; not as a security layer authentication – Even when using ...
... SSID (service set identifier) – Identifies the 802.11 devices that belong to a Basic Service Set (BSS). – A BSS is analogous to a LAN segment in wired terms – SSID is meant as a method to identify what Service Set you want to communicate with; not as a security layer authentication – Even when using ...
Chapter 14 Network Security - Cambridge Regional College
... Introduction to Firewalls and Proxies • Administrators use Network Address Translation (NAT) to alter the source address of packets originating from a secure LAN. • This allows secure LANs to be addressed using private IP addresses. • Private IP addresses are not routed on the Internet. • An outsid ...
... Introduction to Firewalls and Proxies • Administrators use Network Address Translation (NAT) to alter the source address of packets originating from a secure LAN. • This allows secure LANs to be addressed using private IP addresses. • Private IP addresses are not routed on the Internet. • An outsid ...
投影片 1
... The Internet Protocol (IP) layer can help data get to its destination even if the source and destination computers are on different local networks. As the name suggests, the Internet Protocol enables computers on the Internet to communicate with each other. Three protocols often used along with ...
... The Internet Protocol (IP) layer can help data get to its destination even if the source and destination computers are on different local networks. As the name suggests, the Internet Protocol enables computers on the Internet to communicate with each other. Three protocols often used along with ...
- LearnGroup
... an interconnected set of networks where each of the constituent networks retains its identity ...
... an interconnected set of networks where each of the constituent networks retains its identity ...
Wireless and going mobile
... Considered to be effectively non-line-ofsite, if used at enough power. Can use bounces, not just resist them. In principle, can be low power, once made small enough. Fourth Generation (4G) communications, including cell phones. Darned fast!!!! 30 Mbps or more! Mars! ...
... Considered to be effectively non-line-ofsite, if used at enough power. Can use bounces, not just resist them. In principle, can be low power, once made small enough. Fourth Generation (4G) communications, including cell phones. Darned fast!!!! 30 Mbps or more! Mars! ...
Bell Canada Holdings Strategic Plan 2004
... Understanding and enabling a pervasive mobile broadband world - Handling of tremendous growth in traffic and in number of connected machines & “things”, & cooperative networks and environments ...
... Understanding and enabling a pervasive mobile broadband world - Handling of tremendous growth in traffic and in number of connected machines & “things”, & cooperative networks and environments ...
Chapter 3 slides
... growth in the number of host computers, networks, and web servers connected to the Internet. ◦ In realistic, expect to include several billion nodes and hundreds of millions of active hosts. ◦ These numbers indicate the future changes in size and load that the Internet must handle. ◦ network technol ...
... growth in the number of host computers, networks, and web servers connected to the Internet. ◦ In realistic, expect to include several billion nodes and hundreds of millions of active hosts. ◦ These numbers indicate the future changes in size and load that the Internet must handle. ◦ network technol ...
Document - Oman College of Management & Technology
... • Each domain can create or change whatever belongs to it. – CUHK can create any new domain, cse – CSE can buy a new computer and name it as – robin, orchid, any other name. ...
... • Each domain can create or change whatever belongs to it. – CUHK can create any new domain, cse – CSE can buy a new computer and name it as – robin, orchid, any other name. ...