Strawcutter
... packets and less time needed to capture enough packets. Other weaknesses include shared keys, no per-packet authentication, vulnerability to disassociation attacks, no user identification or authentication, no central authentication. The next security protocol, WPA (Wi-Fi Protected Access) was imple ...
... packets and less time needed to capture enough packets. Other weaknesses include shared keys, no per-packet authentication, vulnerability to disassociation attacks, no user identification or authentication, no central authentication. The next security protocol, WPA (Wi-Fi Protected Access) was imple ...
ghostcam android
... connected to a network it is necessary to start Control centre of networks and the general access. Then to press on It will be connected to a network: For this purpose also it is intended Automatic updating (fig. 5.12, at the left). By default updating function is activated, so as soon as you are co ...
... connected to a network it is necessary to start Control centre of networks and the general access. Then to press on It will be connected to a network: For this purpose also it is intended Automatic updating (fig. 5.12, at the left). By default updating function is activated, so as soon as you are co ...
Ch10aProtectionMechanisms
... laws that protect the individual user’s right to access content Tool usage and configuration must comply with an explicitly articulated policy, and the policy must provide for valid exceptions ...
... laws that protect the individual user’s right to access content Tool usage and configuration must comply with an explicitly articulated policy, and the policy must provide for valid exceptions ...
Review Questions on Documentary – The Internet Behind the Web
... Who envisioned the underlying idea of Internet in the 1950 and what did he envision? During the cold war, US President had signed a contract to start a new agency working on defense researches. What is the full name of this agency and what is its contribution in the history of Internet? Who applied ...
... Who envisioned the underlying idea of Internet in the 1950 and what did he envision? During the cold war, US President had signed a contract to start a new agency working on defense researches. What is the full name of this agency and what is its contribution in the history of Internet? Who applied ...
CSCI6268L10 - Computer Science
... – Open Shortest Path First, Link-State Protocol – These protocols assume “modest sized” networks – A routing protocol decides how to forward packets based on routing tables ...
... – Open Shortest Path First, Link-State Protocol – These protocols assume “modest sized” networks – A routing protocol decides how to forward packets based on routing tables ...
CSCI6268L10 - Computer Science
... – Open Shortest Path First, Link-State Protocol – These protocols assume “modest sized” networks – A routing protocol decides how to forward packets based on routing tables ...
... – Open Shortest Path First, Link-State Protocol – These protocols assume “modest sized” networks – A routing protocol decides how to forward packets based on routing tables ...
Communication by Computer
... I just got this message from one of my friends. Sure enough my address book was infected, which means yours will be also. The virus (called jdbgmgr.exe) is not detected by Norton or McAfee anti-virus systems. The virus sits quietly for 14 days before damaging the system. It's sent automatically by t ...
... I just got this message from one of my friends. Sure enough my address book was infected, which means yours will be also. The virus (called jdbgmgr.exe) is not detected by Norton or McAfee anti-virus systems. The virus sits quietly for 14 days before damaging the system. It's sent automatically by t ...
Network Layer
... services to exchange the individual pieces of data over the network between identified end devices. To accomplish this end-to-end transport, Layer 3 uses four basic processes: Addressing Encapsulation Routing Decapsulation ...
... services to exchange the individual pieces of data over the network between identified end devices. To accomplish this end-to-end transport, Layer 3 uses four basic processes: Addressing Encapsulation Routing Decapsulation ...
Computer Security
... addresses, protocol commands, historical comparisons, and contents of packet Uses a state engine and state table Monitor connection-oriented and connectionless protocols Expensive and complex to administer 3rd generation firewall ...
... addresses, protocol commands, historical comparisons, and contents of packet Uses a state engine and state table Monitor connection-oriented and connectionless protocols Expensive and complex to administer 3rd generation firewall ...
PPT
... • The Internet and Web: What’s the Difference? The Internet is the physical connection of millions of networks. The Web uses the Internet for its existence The Web consists of hypertext embedded on Web pages that are hosted on Web sites Web browsers display a Web document and enable users to link t ...
... • The Internet and Web: What’s the Difference? The Internet is the physical connection of millions of networks. The Web uses the Internet for its existence The Web consists of hypertext embedded on Web pages that are hosted on Web sites Web browsers display a Web document and enable users to link t ...
Local-area network
... • Various configurations, called topologies, have been used to administer LANs – Ring topology A configuration that connects all nodes in a closed loop on which messages travel in one direction – Star topology A configuration that centers around one node to which all others are connected and through ...
... • Various configurations, called topologies, have been used to administer LANs – Ring topology A configuration that connects all nodes in a closed loop on which messages travel in one direction – Star topology A configuration that centers around one node to which all others are connected and through ...
Kuliah Komunikasi Data
... defines the way in which computers, printers, and other devices are connected. A network topology describes the layout of the wire and devices as well as the paths used by data transmissions. ...
... defines the way in which computers, printers, and other devices are connected. A network topology describes the layout of the wire and devices as well as the paths used by data transmissions. ...
Setup Eduroam Access
... (eg [email protected]) into the User Name field and then enter your password d. If you are a member of staff - Enter your University e-mail address (eg. [email protected]) into the User Name field and then enter your password 2. If you tick the ‘remember this network’ box you will be automat ...
... (eg [email protected]) into the User Name field and then enter your password d. If you are a member of staff - Enter your University e-mail address (eg. [email protected]) into the User Name field and then enter your password 2. If you tick the ‘remember this network’ box you will be automat ...
September 9 - fog.ccsf.edu
... interact with a computer through a point and click system. • Dragging the mouse moves the cursor/pointer on the screen. • Variations on a mouse ...
... interact with a computer through a point and click system. • Dragging the mouse moves the cursor/pointer on the screen. • Variations on a mouse ...
for ResNet - University of Michigan
... Sqld does an ARP lookup on the router to determine the MAC address Sqld queries the Group Server to determine if user is allowed to access this specific network Sqld attempts to associate username with prestuffed user location data; if this is not successful, it attempts to fill this data by doing a ...
... Sqld does an ARP lookup on the router to determine the MAC address Sqld queries the Group Server to determine if user is allowed to access this specific network Sqld attempts to associate username with prestuffed user location data; if this is not successful, it attempts to fill this data by doing a ...
Chap9.doc
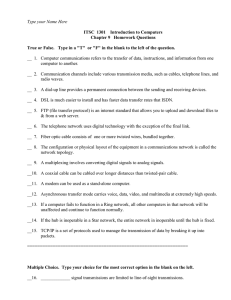
... __ 4. DSL is much easier to install and has faster data transfer rates that ISDN. __ 5. FTP (file transfer protocol) is an internet standard that allows you to upload and download files to & from a web server. __ 6. The telephone network uses digital technology with the exception of the final link. ...
... __ 4. DSL is much easier to install and has faster data transfer rates that ISDN. __ 5. FTP (file transfer protocol) is an internet standard that allows you to upload and download files to & from a web server. __ 6. The telephone network uses digital technology with the exception of the final link. ...
Chapter 1/Tutorial
... of incoming messages to the target system essentially forces it to shut down, thereby denying service to the system to legitimate users. select target break into hosts around the network .(botent) send packets toward target from compromised hosts ...
... of incoming messages to the target system essentially forces it to shut down, thereby denying service to the system to legitimate users. select target break into hosts around the network .(botent) send packets toward target from compromised hosts ...
No Slide Title
... central hub. Nodes communicate across the network by passing data through the hub ...
... central hub. Nodes communicate across the network by passing data through the hub ...
CSCI6268L10 - Computer Science
... – Open Shortest Path First, Link-State Protocol – These protocols assume “modest sized” networks – A routing protocol decides how to forward packets based on routing tables ...
... – Open Shortest Path First, Link-State Protocol – These protocols assume “modest sized” networks – A routing protocol decides how to forward packets based on routing tables ...