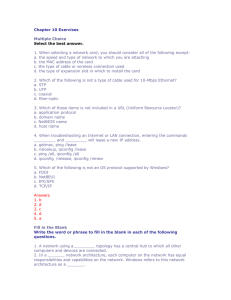
Chapter 10 Exercises
... called a DHCP (Dynamic Host Configuration Protocol) server. When a PC first connects to the network, it attempts to lease an address from the DHCP server. If the attempt fails, it uses a process called IP autoconfiguration and assigns itself an Automatic Private IP Address (APIPA) in the address ran ...
... called a DHCP (Dynamic Host Configuration Protocol) server. When a PC first connects to the network, it attempts to lease an address from the DHCP server. If the attempt fails, it uses a process called IP autoconfiguration and assigns itself an Automatic Private IP Address (APIPA) in the address ran ...
15-744: Computer Networking
... Mobility/Wireless Network Energy Network Debugging Overlay Networks P2P applications ...
... Mobility/Wireless Network Energy Network Debugging Overlay Networks P2P applications ...
Week-13.1.1
... use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer dig ...
... use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer dig ...
Class_3_-_Subarea_V
... • Switch – Much like a bridge, a switch reads the destination and forwards it down the correct path. May be linked to numerous networks enabling more pathways then a bridge ...
... • Switch – Much like a bridge, a switch reads the destination and forwards it down the correct path. May be linked to numerous networks enabling more pathways then a bridge ...
Computer network
... Connections between computing devices can be physical using wires or cables or wireless using radio waves or infrared signals Can you name some of the devices in a computer network? ...
... Connections between computing devices can be physical using wires or cables or wireless using radio waves or infrared signals Can you name some of the devices in a computer network? ...
802.11 Security/Bluetooth
... • War-driving: drive around Bay area, see what 802.11 networks available? – More than 9000 accessible from public roadways – 85% use no encryption/authentication – packet-sniffing and various attacks easy! • Securing 802.11 – encryption, authentication – first attempt at 802.11 security: Wired Equiv ...
... • War-driving: drive around Bay area, see what 802.11 networks available? – More than 9000 accessible from public roadways – 85% use no encryption/authentication – packet-sniffing and various attacks easy! • Securing 802.11 – encryption, authentication – first attempt at 802.11 security: Wired Equiv ...
policies - NY Capital Region Chapter
... Hacker gains access to network after a few weeks of “brute force” attacks ...
... Hacker gains access to network after a few weeks of “brute force” attacks ...
What Is Highly Critical Wireless Networking (HCWN)
... A Highly Critical Wireless Network (HCWN) may consist of several interconnected communications devices used to support a critical function. HCWN are commercial wireless systems that use the TCPIP digital protocols, which are beginning to dominate our communications infrastructure and reshape our ind ...
... A Highly Critical Wireless Network (HCWN) may consist of several interconnected communications devices used to support a critical function. HCWN are commercial wireless systems that use the TCPIP digital protocols, which are beginning to dominate our communications infrastructure and reshape our ind ...
Presentation: the internet layer, IP, the Internet Protocol
... There are two transport layer protocols, TCP and UDP. Web applications use TCP because it checks for errors and controls speed. ...
... There are two transport layer protocols, TCP and UDP. Web applications use TCP because it checks for errors and controls speed. ...
Network Components Presentation
... Connects different types of network together. Software at a node (on the network). Which directs messages down different routes. According to their desired destination. ...
... Connects different types of network together. Software at a node (on the network). Which directs messages down different routes. According to their desired destination. ...
Week-10.3-2
... use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer dig ...
... use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer dig ...
ppt
... If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission ...
... If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission ...
Understanding Internetworking Infrastructure
... Cyberwar: War in which a country’s information systems could be paralyzed from a massive attack by destructive software. Virus: Software that can attach itself to (“infect”) other computer programs without the owner of the program being aware of the infection. ...
... Cyberwar: War in which a country’s information systems could be paralyzed from a massive attack by destructive software. Virus: Software that can attach itself to (“infect”) other computer programs without the owner of the program being aware of the infection. ...
Analyzing the Internet - IIT College of Science
... New applications for old laws • Gravity models used to model the volume of S->D traffic in a network (PSTN, Internet) • Poisson distribution: telephone call arrivals, packet arrivals, web ...
... New applications for old laws • Gravity models used to model the volume of S->D traffic in a network (PSTN, Internet) • Poisson distribution: telephone call arrivals, packet arrivals, web ...
Name: Shaikh Fahad Saeed ID: 200800652
... multiple access, CDMA-200, TDSCDMA-Time-Division synchronous code division multiple-access technologies and 3G also has the superior voice quality and up to 2M ...
... multiple access, CDMA-200, TDSCDMA-Time-Division synchronous code division multiple-access technologies and 3G also has the superior voice quality and up to 2M ...
Lecture5_IP_NAT
... Router receives one IP Address Either dynamically assigns addresses to all the nodes behind the router, or it is assigned statically using nonroutable addresses ...
... Router receives one IP Address Either dynamically assigns addresses to all the nodes behind the router, or it is assigned statically using nonroutable addresses ...
Week-2
... be identified uniquely on that network. – Computers connected to networks that form part of the Internet must have globally unique identification. ...
... be identified uniquely on that network. – Computers connected to networks that form part of the Internet must have globally unique identification. ...