Networking in Linux
... Routers ports (book page 398). If no ports found means security is in place. If you find ports open you may be able to identify the type of device (routers, switches, hubs) and their manufacturers. ...
... Routers ports (book page 398). If no ports found means security is in place. If you find ports open you may be able to identify the type of device (routers, switches, hubs) and their manufacturers. ...
IETF 報告 UDLR-WG
... Configuring Network Interface • Network Interface has global unique IP Address • Host is belong to a network - Network Interface has netmask ...
... Configuring Network Interface • Network Interface has global unique IP Address • Host is belong to a network - Network Interface has netmask ...
Tobias Herber (530) 723-6691
... - Administered Windows 2003-2012, CentOS, and vSphere ESXi servers - Created custom solution for legacy apps using Windows XP Mode - Set up IT infrastructure in new building, including a dual server rack, 12 physical servers, patch panel, managed/unmanaged switches, UPS, NAS, and wireless AP's Septe ...
... - Administered Windows 2003-2012, CentOS, and vSphere ESXi servers - Created custom solution for legacy apps using Windows XP Mode - Set up IT infrastructure in new building, including a dual server rack, 12 physical servers, patch panel, managed/unmanaged switches, UPS, NAS, and wireless AP's Septe ...
Understanding and Installing Firewalls
... In 1988, an employee at the NASA Ames Research Center in California sent a memo by email to his colleagues [2] that read, "We are currently under attack from an Internet VIRUS! It has hit Berkeley, UC San Diego, Lawrence Livermore, Stanford, and NASA Ames." The Morris Worm spread itself through mult ...
... In 1988, an employee at the NASA Ames Research Center in California sent a memo by email to his colleagues [2] that read, "We are currently under attack from an Internet VIRUS! It has hit Berkeley, UC San Diego, Lawrence Livermore, Stanford, and NASA Ames." The Morris Worm spread itself through mult ...
Slide 1
... Avoiding Network Duplication • Can commercial communications providers effectively and economically provide the services that utilities need to power their Smart Grid communications? ...
... Avoiding Network Duplication • Can commercial communications providers effectively and economically provide the services that utilities need to power their Smart Grid communications? ...
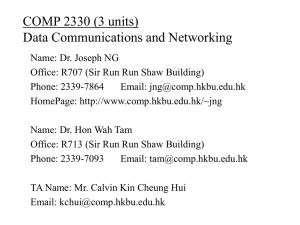
Class Notes #1
... exchange information with each other in a meaningful way. – Computer networks may link computers that are all of the same type (homogeneous networks), or they may link computers of several different types (heterogeneous networks) – Size of the network: same room, same floor, same building, same camp ...
... exchange information with each other in a meaningful way. – Computer networks may link computers that are all of the same type (homogeneous networks), or they may link computers of several different types (heterogeneous networks) – Size of the network: same room, same floor, same building, same camp ...
intro-to-ethical-hacking-week-2
... Works to keep localized traffic inside and only passes traffic intended for targets outside the local network Boundary between “Routable” and “NonRoutable” IP addressing ...
... Works to keep localized traffic inside and only passes traffic intended for targets outside the local network Boundary between “Routable” and “NonRoutable” IP addressing ...
PowerPoint Presentation - Securing a Wireless 802.11b Network
... All an attacker needs is a laptop computer, a wireless card and some software A directional antenna will increase the range over which the attacker can access your network Directional antenna can be made from a Pringles potato chip can! Attackers drive around with their computers looking for ope ...
... All an attacker needs is a laptop computer, a wireless card and some software A directional antenna will increase the range over which the attacker can access your network Directional antenna can be made from a Pringles potato chip can! Attackers drive around with their computers looking for ope ...
Assignment3-LeonardEhalt
... • A Network Interface Card (NIC) is installed in your computer to connect, or interface, your computer to the network. • It provides the physical, electrical, and electronic connections to the network media. • A NIC either is an expansion card or is built right into the computer’s motherboard. • The ...
... • A Network Interface Card (NIC) is installed in your computer to connect, or interface, your computer to the network. • It provides the physical, electrical, and electronic connections to the network media. • A NIC either is an expansion card or is built right into the computer’s motherboard. • The ...
802.11 frame - Department of Computer and Information Science
... containing AP’s name and MAC address selects AP to associate with may perform authentication will typically run DHCP to get IP address in AP’s subnet ...
... containing AP’s name and MAC address selects AP to associate with may perform authentication will typically run DHCP to get IP address in AP’s subnet ...
Overview - La Revue MODULAD
... – No insertion of own packets, just listen! – Obtain information from the captured data ...
... – No insertion of own packets, just listen! – Obtain information from the captured data ...
Power Point - Toronto Users Group
... • Alternative A, preferred by Cisco (only 2 pairs required) ...
... • Alternative A, preferred by Cisco (only 2 pairs required) ...
Chapter 8 - Chabot College
... • A software report would be used to determine what programs are installed on a particular computer. • Network policy should be used to select network passwords. • User policies refer to documentation that outlines what is and what is not permissible on the network. • Configuration error is NOT used ...
... • A software report would be used to determine what programs are installed on a particular computer. • Network policy should be used to select network passwords. • User policies refer to documentation that outlines what is and what is not permissible on the network. • Configuration error is NOT used ...
No Slide Title
... Length of cable runs (affects type of cabling) Cable runs must not violate fire breaks Plenum cable required if hot air returns ...
... Length of cable runs (affects type of cabling) Cable runs must not violate fire breaks Plenum cable required if hot air returns ...
Introduction - start [kondor.etf.rs]
... In 1974, TCP/IP model has been established by Cerf and Kahn, and incorporated into Berkeley UNIX. Because of the large number of hosts, domain name system (DNS) was created in 1980s. ...
... In 1974, TCP/IP model has been established by Cerf and Kahn, and incorporated into Berkeley UNIX. Because of the large number of hosts, domain name system (DNS) was created in 1980s. ...
Out Of The Blue - Joshua`s Learning Log
... Network security refers to any activities designed to protect your network. Specifically, these activities protect the usability, reliability, integrity, and safety of your network and data. Effective network security targets a variety of threats and stops them from entering or spreading on your net ...
... Network security refers to any activities designed to protect your network. Specifically, these activities protect the usability, reliability, integrity, and safety of your network and data. Effective network security targets a variety of threats and stops them from entering or spreading on your net ...
powerpoint
... Radio waves (WiFi - Wireless local area network that uses radio signals to transmit data) • Satellites (GPS) ...
... Radio waves (WiFi - Wireless local area network that uses radio signals to transmit data) • Satellites (GPS) ...
IP address
... ■ The location (subnet) of the interface (host) in the network ● The IP address is the only “name” carried in an IP ...
... ■ The location (subnet) of the interface (host) in the network ● The IP address is the only “name” carried in an IP ...
Practice questions for exam
... 47. You are designing a corporate network. List at least four of the most important network design criteria you should have in mind. 48. Explain what tier-1, tier-2, and tier-3 networks are. 49. Explain the difference between a service, a primitive and a protocol. 50. Explain the difference between ...
... 47. You are designing a corporate network. List at least four of the most important network design criteria you should have in mind. 48. Explain what tier-1, tier-2, and tier-3 networks are. 49. Explain the difference between a service, a primitive and a protocol. 50. Explain the difference between ...
TS/SCI cleared Network Administrator for AF JWICS
... - Perform installation, troubleshooting, maintenance, and repair of network switches and routers, power, and computer data circuits and related apparatus/peripherals required to maintain network infrastructure. - Provide core network services configuration, installation, and administration of data s ...
... - Perform installation, troubleshooting, maintenance, and repair of network switches and routers, power, and computer data circuits and related apparatus/peripherals required to maintain network infrastructure. - Provide core network services configuration, installation, and administration of data s ...
Wireless/Mobile Computing and Networking
... (Linksys WRT54G, < $30) as building blocks for indoor wireless sensor network (WSN) applications • Use SNMP as the basic interaction protocol among wireless sensor network nodes • Provide a SQL interface and distributed query processing system to sensor data stored on WSN nodes • Support dynamic cha ...
... (Linksys WRT54G, < $30) as building blocks for indoor wireless sensor network (WSN) applications • Use SNMP as the basic interaction protocol among wireless sensor network nodes • Provide a SQL interface and distributed query processing system to sensor data stored on WSN nodes • Support dynamic cha ...
Internet Protocol, IP Addressing and Datagrams
... entries in a local routing table • Each entry consists of: – destination address – subnet mask 32 bit value that specifies the boundary between network prefix and suffix ...
... entries in a local routing table • Each entry consists of: – destination address – subnet mask 32 bit value that specifies the boundary between network prefix and suffix ...
High-speed digital telecommunications networks that are national or
... – A shared network service technology that packages data into bundles – Does not use error-correction – Cheaper and faster than packet-switching ...
... – A shared network service technology that packages data into bundles – Does not use error-correction – Cheaper and faster than packet-switching ...









![Introduction - start [kondor.etf.rs]](http://s1.studyres.com/store/data/000507900_1-4612cc6372b2ee158f9c52bcf8aea7c5-300x300.png)