No Slide Title
... packet only if the packet is heard by the receiving PC and the receiving PC will then send its CTS packet ...
... packet only if the packet is heard by the receiving PC and the receiving PC will then send its CTS packet ...
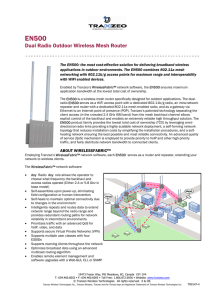
Dual Radio Outdoor Wireless Mesh Router
... Enabled by Tranzeo’s WirelessFabric™ network software, the EN500 ensures maximum application bandwidth at the lowest total cost of ownership. The EN500 is a wireless mesh router specifically designed for outdoor applications. The dualradio EN500 serves as a WiFi access point with a dedicated 802.11b ...
... Enabled by Tranzeo’s WirelessFabric™ network software, the EN500 ensures maximum application bandwidth at the lowest total cost of ownership. The EN500 is a wireless mesh router specifically designed for outdoor applications. The dualradio EN500 serves as a WiFi access point with a dedicated 802.11b ...
Connecting a Computer/ Smartphone/Tablet to the Wireless Network
... Device to the Wireless Network To connect a gaming (Playstation, Xbox, etc) or streaming (Roku, Apple TV, etc) device to the wireless network, open the list of wireless networks and select ccsu-gaming. Your device should connect to the ccsu-gaming wireless network automatically. If it does not, you ...
... Device to the Wireless Network To connect a gaming (Playstation, Xbox, etc) or streaming (Roku, Apple TV, etc) device to the wireless network, open the list of wireless networks and select ccsu-gaming. Your device should connect to the ccsu-gaming wireless network automatically. If it does not, you ...
firstclass
... Accessory devices (printers, fax machines, backup devices, etc.) Originally connected thru workstations or servers, now directly network connected Originally dumb, now intelligent enough to do some real damage ...
... Accessory devices (printers, fax machines, backup devices, etc.) Originally connected thru workstations or servers, now directly network connected Originally dumb, now intelligent enough to do some real damage ...
Review of Underlying Network Technologies
... With hundreds or thousands of networks, no way to write all possible application programs Intermediate application programs between the source and destination must operate correctly ...
... With hundreds or thousands of networks, no way to write all possible application programs Intermediate application programs between the source and destination must operate correctly ...
Internet
... The router directs the packets to their destination. The packets are reassembled at their destination-computer which then responds to any request. A message is sent from the destination computer to the sending computer in order to request that any missing or corrupt packets be resent. ...
... The router directs the packets to their destination. The packets are reassembled at their destination-computer which then responds to any request. A message is sent from the destination computer to the sending computer in order to request that any missing or corrupt packets be resent. ...
Session5-Group4-Networking
... In computing, a protocol is a set of rules which is used by computers to communicate with each other across a network. A protocol is a convention or standard that controls or enables the connection, communication, and data transfer between computing endpoints. In its simplest form, a protocol can be ...
... In computing, a protocol is a set of rules which is used by computers to communicate with each other across a network. A protocol is a convention or standard that controls or enables the connection, communication, and data transfer between computing endpoints. In its simplest form, a protocol can be ...
MPLS Based Web Switching
... Integrated WLAN and GPRS cards allow High-speed access indoors (802.11a supports 54Mbps) Wide-area connectivity via emerging wide-area data services (GPRS / 3G) Ongoing research on seamless roaming between LAN/WAN ...
... Integrated WLAN and GPRS cards allow High-speed access indoors (802.11a supports 54Mbps) Wide-area connectivity via emerging wide-area data services (GPRS / 3G) Ongoing research on seamless roaming between LAN/WAN ...
presentation source
... Concept: a group of NT machines that share “a security server” - the primary domain controller (PDC VS BDCs) – Windows for Workgroups and Windows 95 can join by selecting as workgroup name the domain name – Users with Windows 95 clients can log on NT server net similarly to NT workstations. – user ...
... Concept: a group of NT machines that share “a security server” - the primary domain controller (PDC VS BDCs) – Windows for Workgroups and Windows 95 can join by selecting as workgroup name the domain name – Users with Windows 95 clients can log on NT server net similarly to NT workstations. – user ...
intro
... Between different geographical locations Between different networks Between different communication devices Between different applications ...
... Between different geographical locations Between different networks Between different communication devices Between different applications ...
Presentation_Sharmistha_Roy
... protocols require system wide changes which are difficult to implement. Example of Cisco 7xxx routers where a long password would lead to buffer overflow attscks ...
... protocols require system wide changes which are difficult to implement. Example of Cisco 7xxx routers where a long password would lead to buffer overflow attscks ...
Lecture1onInternet - IntroductionToComputing
... since the packets are transmitted independently, it is likely that at least part of the message will arrive (even if some failures occur within the network) software at the destination can recognize which packets are missing and request retransmission ...
... since the packets are transmitted independently, it is likely that at least part of the message will arrive (even if some failures occur within the network) software at the destination can recognize which packets are missing and request retransmission ...
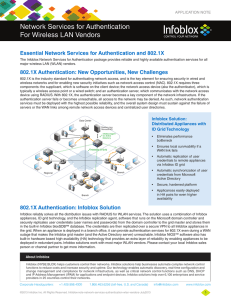
Network Services for Authentication For Wireless LAN
... 802.1X is the industry standard for authenticating network access, and is the key element for ensuring security in wired and wireless networks and for enabling new security initiatives such as network access control (NAC). 802.1X requires three components: the supplicant, which is software on the cl ...
... 802.1X is the industry standard for authenticating network access, and is the key element for ensuring security in wired and wireless networks and for enabling new security initiatives such as network access control (NAC). 802.1X requires three components: the supplicant, which is software on the cl ...
tr-5a series - Baltic Networks
... Enabled by Tranzeo’s WirelessFabric™ network software, the EN404 ensures maximum application bandwidth at the lowest total cost of ownership. The EN404 is a wireless mesh router specifically designed for outdoor applications. The dual-radio EN404 serves as a WiFi access point with a dedicated 802.11 ...
... Enabled by Tranzeo’s WirelessFabric™ network software, the EN404 ensures maximum application bandwidth at the lowest total cost of ownership. The EN404 is a wireless mesh router specifically designed for outdoor applications. The dual-radio EN404 serves as a WiFi access point with a dedicated 802.11 ...
Enabling Simultaneous Connections to Multiple Wireless Networks
... • give more time to networks that have seen more traffic • not starve networks with low traffic ...
... • give more time to networks that have seen more traffic • not starve networks with low traffic ...
Network - McGraw Hill Higher Education
... standards, or protocols, so that they can work together B5-3 ...
... standards, or protocols, so that they can work together B5-3 ...
Virtualization Group
... – What does it mean to do things ‘in the network’ – Does topology matter? • It does for data synthesis • Maybe for location based services • But BW is free, so we can tunnel things lots of ...
... – What does it mean to do things ‘in the network’ – Does topology matter? • It does for data synthesis • Maybe for location based services • But BW is free, so we can tunnel things lots of ...
Lecture 1 Installing Linux, VMware, Reconnaissance, Network
... • Domain Name Transfers (nslookup) are used to list hosts • Invalid flags on TCP packets are used to detect the OS ...
... • Domain Name Transfers (nslookup) are used to list hosts • Invalid flags on TCP packets are used to detect the OS ...
Test your knowledge
... To avoid unauthorised network access, should include firewall. The recommended security ways should include: ...
... To avoid unauthorised network access, should include firewall. The recommended security ways should include: ...
What*s inside your network?
... significantly owned by a European government Filtered the traffic by the target IP addresses Monitored traffic included all perimeter firewalls and network and host intrusion systems About 200 of the end point assets participated in the attack ...
... significantly owned by a European government Filtered the traffic by the target IP addresses Monitored traffic included all perimeter firewalls and network and host intrusion systems About 200 of the end point assets participated in the attack ...
Document
... message to all computers in the entire LAN, it is decided by this higher level device. This allows parallel communication to occur within the LAN without being effected by the higher level. To do this, the router needs to have a Dynamic Host Configuration Protocol (DHCP) ability. DHCP assigns each d ...
... message to all computers in the entire LAN, it is decided by this higher level device. This allows parallel communication to occur within the LAN without being effected by the higher level. To do this, the router needs to have a Dynamic Host Configuration Protocol (DHCP) ability. DHCP assigns each d ...
Chapter 2
... not send from their connected station • If two signals are on the line at once, neither signal will make sense and a collision occurs • When a collision is detected, the host interface aborts transmission and waits (how long?) for the line to be idle before it sends again; CSMA/CD ...
... not send from their connected station • If two signals are on the line at once, neither signal will make sense and a collision occurs • When a collision is detected, the host interface aborts transmission and waits (how long?) for the line to be idle before it sends again; CSMA/CD ...
Chapter 4
... enough “noise” that would prevent a device from sending or receiving packets. 20. Explain how CSMA/CA is used with IEEE 802.11 WLANs. Because the wireless medium is shared among all devices, there must be rules for cooperation among the wireless devices. The 802.11 standard uses a procedure known as ...
... enough “noise” that would prevent a device from sending or receiving packets. 20. Explain how CSMA/CA is used with IEEE 802.11 WLANs. Because the wireless medium is shared among all devices, there must be rules for cooperation among the wireless devices. The 802.11 standard uses a procedure known as ...