Document
... Includes IV sequencing (rotates keys more often) Adds a frame integrity-check function that is much stronger than CRC ...
... Includes IV sequencing (rotates keys more often) Adds a frame integrity-check function that is much stronger than CRC ...
Subnet and Packet Tracer Task
... be a subnetwork, links between a router and a switch then out to the computers will also be a subnetwork. • Assign appropriate IP addresses, subnet masks, network addresses(under RIP on the router) and turn needed ports on connecting the router interfaces you decide to use. • Assign IP addresses to ...
... be a subnetwork, links between a router and a switch then out to the computers will also be a subnetwork. • Assign appropriate IP addresses, subnet masks, network addresses(under RIP on the router) and turn needed ports on connecting the router interfaces you decide to use. • Assign IP addresses to ...
Blank Jeopardy
... Circuit boards that connect to the motherboard to add functionality to the computer. ...
... Circuit boards that connect to the motherboard to add functionality to the computer. ...
Intrusion Prevention Systems
... • Computer Networks Basics: OSI stack, subnets, Basic protocols: ARP, ICMP, NAT, DHCP, DNS, TCP/IP • Penetration testing: recon, scanning, exploits (ch. 1-4 of book: ”The basics of Hacking and Penetration Testing”) • IDS/IPS • Firewalls • Network Security Protocols ...
... • Computer Networks Basics: OSI stack, subnets, Basic protocols: ARP, ICMP, NAT, DHCP, DNS, TCP/IP • Penetration testing: recon, scanning, exploits (ch. 1-4 of book: ”The basics of Hacking and Penetration Testing”) • IDS/IPS • Firewalls • Network Security Protocols ...
Chapter 4 – Database management SystemsApplied Computer
... 15. A router’s control panel is usually accessed: a. only by the ISP b. using a Web browser c. by removing the access cover on the back of the router d. by removing the router’s front cover 16. Which of the following uniquely identifies a network adapter? a. SSID b. MAC address c. IP address d. USB ...
... 15. A router’s control panel is usually accessed: a. only by the ISP b. using a Web browser c. by removing the access cover on the back of the router d. by removing the router’s front cover 16. Which of the following uniquely identifies a network adapter? a. SSID b. MAC address c. IP address d. USB ...
Wireless Multi-Client Bridge/AP 2611CB3 PLUS (Deluxe)
... (2.4GHz, 11Mbps) wireless standards. It's the best way to add wireless capability to your existing wired network, or to add bandwidth to your wireless installation. To protect your wireless connectivity, it can encrypt all wireless transmissions through 64/128-bit WEP data encryption and also suppor ...
... (2.4GHz, 11Mbps) wireless standards. It's the best way to add wireless capability to your existing wired network, or to add bandwidth to your wireless installation. To protect your wireless connectivity, it can encrypt all wireless transmissions through 64/128-bit WEP data encryption and also suppor ...
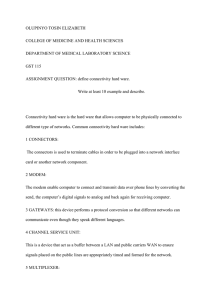
connectivity_hard_ware_1
... The personal computer expansion board with its own unique identifier that plugs into a computer allowing it to be connected to network. 9 BRIGES; Used to connect two different LANs or two segments of the same LAN by forwarding traffic between segments. 10 REPEATER: This is a network device to replic ...
... The personal computer expansion board with its own unique identifier that plugs into a computer allowing it to be connected to network. 9 BRIGES; Used to connect two different LANs or two segments of the same LAN by forwarding traffic between segments. 10 REPEATER: This is a network device to replic ...
Computer network
... • There are various technologies available that you can use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber li ...
... • There are various technologies available that you can use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber li ...
Ch10 - Protection Mechanism
... • Network connectivity using external connections – Usually much simpler and less sophisticated than Internet connections – Simple user name and password schemes are usually the only means of authentication ...
... • Network connectivity using external connections – Usually much simpler and less sophisticated than Internet connections – Simple user name and password schemes are usually the only means of authentication ...
Chapter 4
... Prince of Songkla University and the Asian Institute of Technology (AIT) in 1987 supported by The International Development Plan (IDP), to communicate with the University of Melbourne by e-mail. ...
... Prince of Songkla University and the Asian Institute of Technology (AIT) in 1987 supported by The International Development Plan (IDP), to communicate with the University of Melbourne by e-mail. ...
This morning one of our programmers, Zundra Daniel went up to
... occurred which was the “Page Not Found” error was caused by network connection in the room. However, concerning the other less frequent problems such as repeated questions, and skipping questions it was not immediately obvious to Zundra what were causing these additional problems at the time. Zundra ...
... occurred which was the “Page Not Found” error was caused by network connection in the room. However, concerning the other less frequent problems such as repeated questions, and skipping questions it was not immediately obvious to Zundra what were causing these additional problems at the time. Zundra ...
Powerpoint Slide (Office 97
... Determine goals when crafting packets Identify and use packet crafting tools ...
... Determine goals when crafting packets Identify and use packet crafting tools ...
Module 3 Network Packet Crafting
... Determine goals when crafting packets Identify and use packet crafting tools ...
... Determine goals when crafting packets Identify and use packet crafting tools ...
lecture02
... • Physical components can work however they want, as long as the interface between them is consistent. • Then, different hardware can be connected. ...
... • Physical components can work however they want, as long as the interface between them is consistent. • Then, different hardware can be connected. ...
Internetworking: Concepts, Architecture, and Protocols
... • A router can interconnect networks that use different technologies, including different media and media access techniques, physical addressing schemes, or frame formats. ...
... • A router can interconnect networks that use different technologies, including different media and media access techniques, physical addressing schemes, or frame formats. ...
Simple Blue Template
... today's Internet and is still in dominant use. It was designed to address up to ~4.3 billion (109) Internet hosts. However, the explosive growth of the Internet has led to IPv4 address exhaustion which is estimated to enter its final stage in approximately ...
... today's Internet and is still in dominant use. It was designed to address up to ~4.3 billion (109) Internet hosts. However, the explosive growth of the Internet has led to IPv4 address exhaustion which is estimated to enter its final stage in approximately ...
classful addressing - E Learning UPN Veteran Yogyakarta
... internal testing on a local machine; [You can test this: you should always be able to ping 127.0.0.1, which points to yourself] ...
... internal testing on a local machine; [You can test this: you should always be able to ping 127.0.0.1, which points to yourself] ...
CHAPTER ONE
... From analog signals to digital signals From copper wires to fiber Wireless, wireless, wireless ...
... From analog signals to digital signals From copper wires to fiber Wireless, wireless, wireless ...
What is a Network?
... Network Topics •Network Protocols or Languages •CCITT Providing Standard Address •De Facto Use and Gateways •Central Processing Unit/ Cost Share • File Transfer •Networking Standards •Networking Companies •Internet Access •Chats/ real-time communication ...
... Network Topics •Network Protocols or Languages •CCITT Providing Standard Address •De Facto Use and Gateways •Central Processing Unit/ Cost Share • File Transfer •Networking Standards •Networking Companies •Internet Access •Chats/ real-time communication ...
Unix Networking - bhecker.com • Index page
... tcpdump – Packet sniffing nslookup/dig – DNS Queries ...
... tcpdump – Packet sniffing nslookup/dig – DNS Queries ...
Managing Telecommunications
... The Evolving Telecommunications Scene A New Telecommunications Infrastructure Is Being Built ...
... The Evolving Telecommunications Scene A New Telecommunications Infrastructure Is Being Built ...