Wi-Fi structure
... – The router will typically be your “default gateway” to the Internet and will provide the IP address indicating that to all clients. – If your router’s IP address is 192.168.0.1, all computers using 192.168.0.2 to 192.168.0.254 will use that router to access the Internet. ...
... – The router will typically be your “default gateway” to the Internet and will provide the IP address indicating that to all clients. – If your router’s IP address is 192.168.0.1, all computers using 192.168.0.2 to 192.168.0.254 will use that router to access the Internet. ...
Wireless Network Security
... • Use longer WEP encryption keys, which makes the data analysis task more difficult. If your WLAN equipment supports 128-bit WEP keys. • Change your WEP keys frequently. There are devices that support "dynamic WEP" which is off the standard but allows different WEP keys to be assigned to each user. ...
... • Use longer WEP encryption keys, which makes the data analysis task more difficult. If your WLAN equipment supports 128-bit WEP keys. • Change your WEP keys frequently. There are devices that support "dynamic WEP" which is off the standard but allows different WEP keys to be assigned to each user. ...
Presentation
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
glossary - Homework Market
... (IP). The IP part of TCP/IP; the protocol used to route a data packet from its source to its destination over the Internet. The unique 32 bit number assigned to each computer connected to the Internet and used by the TCP/IP protocol to route packets of data to their destinations. The number is usual ...
... (IP). The IP part of TCP/IP; the protocol used to route a data packet from its source to its destination over the Internet. The unique 32 bit number assigned to each computer connected to the Internet and used by the TCP/IP protocol to route packets of data to their destinations. The number is usual ...
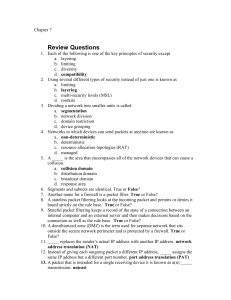
Chapter07
... spyware attacks. Second, antispyware can be set to provide both continuous realtime monitoring as well as perform a complete scan of the entire computer system at one time. And like antivirus software, antispyware provides good visual tools regarding the system scan. However, antispyware s can also ...
... spyware attacks. Second, antispyware can be set to provide both continuous realtime monitoring as well as perform a complete scan of the entire computer system at one time. And like antivirus software, antispyware provides good visual tools regarding the system scan. However, antispyware s can also ...
Networking Components
... Wireless AP Diagram In this scenario multiple wireless devices connect to the network via the wireless access point. This connection is setup for wired and wireless network. ...
... Wireless AP Diagram In this scenario multiple wireless devices connect to the network via the wireless access point. This connection is setup for wired and wireless network. ...
research and evaluate ubnt wifi antenna for a 5 km
... "range extender amplifiers" Specially shaped directional antennas can be used to increase the range of a ...
... "range extender amplifiers" Specially shaped directional antennas can be used to increase the range of a ...
A Router
... hardware designed to allow computers to communicate over a computer network. • Provides a low-level addressing system through the use of MAC addresses. It allows users to connect to each other either by using cables or wirelessly. • The NIC is both an OSI layer 1 (physical layer) and layer 2 (data l ...
... hardware designed to allow computers to communicate over a computer network. • Provides a low-level addressing system through the use of MAC addresses. It allows users to connect to each other either by using cables or wirelessly. • The NIC is both an OSI layer 1 (physical layer) and layer 2 (data l ...
Network Forensics Tracking Hackers Through Cyberspace.
... 2. For clients, identify the WAP that the station is associated with (by SSID) 3. Leverage commercial enterprise wireless mapping software ...
... 2. For clients, identify the WAP that the station is associated with (by SSID) 3. Leverage commercial enterprise wireless mapping software ...
Security “Tidbits” - The Stanford University InfoLab
... Big programs have many exploitable bugs. Choose good passwords. Don’t shut down mail servers: did prevent worm from spreading but also shut down defense CERT was created to respond to attacks ...
... Big programs have many exploitable bugs. Choose good passwords. Don’t shut down mail servers: did prevent worm from spreading but also shut down defense CERT was created to respond to attacks ...
Abstract for ITU seminar on BWA for rural & remote... In order to bridge the digital divide between urban and... rural wireless solution is envisaged in India, which offers mobility...
... existing rural wire-line systems, as well as any other switching systems using the standard interfaces. Along-with this they also support VOIP features for interfacing to a centralized soft-switch using an IP/MPLS network. This rural solution utilizes standard wireless broadband technologies (Wi-Fi ...
... existing rural wire-line systems, as well as any other switching systems using the standard interfaces. Along-with this they also support VOIP features for interfacing to a centralized soft-switch using an IP/MPLS network. This rural solution utilizes standard wireless broadband technologies (Wi-Fi ...
Computer Networks - Career Center Construction Technology
... • In addition to these types, the following characteristics are also used to categorize different types of networks: • topology : The geometric arrangement of a computer system. Common topologies include a bus, star, and ring. See the Network topology diagrams in the Quick Reference section of Web ...
... • In addition to these types, the following characteristics are also used to categorize different types of networks: • topology : The geometric arrangement of a computer system. Common topologies include a bus, star, and ring. See the Network topology diagrams in the Quick Reference section of Web ...
Security challenges in the lighting use case
... Security challenges in Smart Lighting Paul Chilton NXP Semiconductors ...
... Security challenges in Smart Lighting Paul Chilton NXP Semiconductors ...
here - iTrust
... Step 1 – Starting monitor mode • You are required to sniff the wireless traffic to determine which network do you want to gain access to. • For wireless networks, we will be using a suite of tools called Aircrackng. • To go into monitor mode, use the command ‘sudo airmon-ng start XXX’ where XXX is ...
... Step 1 – Starting monitor mode • You are required to sniff the wireless traffic to determine which network do you want to gain access to. • For wireless networks, we will be using a suite of tools called Aircrackng. • To go into monitor mode, use the command ‘sudo airmon-ng start XXX’ where XXX is ...
Web Services Using Visual .NET
... The proposed system would be able to listen to the network and capture packets which are over the network. Further analyze the packets, check for the source and the destination address, check for the protocol, its checksum and much more. Ability to capture packets from both the wired and the wireles ...
... The proposed system would be able to listen to the network and capture packets which are over the network. Further analyze the packets, check for the source and the destination address, check for the protocol, its checksum and much more. Ability to capture packets from both the wired and the wireles ...
Wireless Security
... A reconnaissance process used to intercept network traffic. Need a capture card or network card configurable into ...
... A reconnaissance process used to intercept network traffic. Need a capture card or network card configurable into ...
Slide 1
... Solution: Buffer packets using PSM at APs for IS networks, and end hosts for AH networks. ...
... Solution: Buffer packets using PSM at APs for IS networks, and end hosts for AH networks. ...
Slides - My E-town
... Access points associate a computer with a MAC address But MAC addresses can be spoofed! ...
... Access points associate a computer with a MAC address But MAC addresses can be spoofed! ...