Presentation
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
The Need for Information Security
... with intent to destroy or steal information • Hoaxes: transmission of a virus hoax with a real virus attached; more devious form of attack • Back door: gaining access to system or network using known or previously unknown/newly discovered access ...
... with intent to destroy or steal information • Hoaxes: transmission of a virus hoax with a real virus attached; more devious form of attack • Back door: gaining access to system or network using known or previously unknown/newly discovered access ...
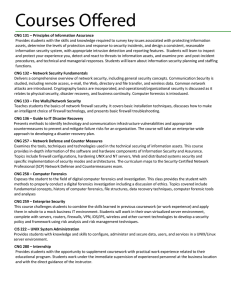
INTRODUCTION TO INFORMATION SYSTEMS TECHNOLOGY
... A security system that implement an access control policy between two networks ...
... A security system that implement an access control policy between two networks ...
Hacker Ethics presentation
... system (not known if he was spying on it, which would violate the hacker ethics.) If he was caught the first time, Mitnick should have kept a lower profile. Hackers get exposed to the mainstream, mostly by the government, when they disregard the secrecy set forth by the hacker ethic. ...
... system (not known if he was spying on it, which would violate the hacker ethics.) If he was caught the first time, Mitnick should have kept a lower profile. Hackers get exposed to the mainstream, mostly by the government, when they disregard the secrecy set forth by the hacker ethic. ...
Chapter 2: Attackers and Their Attacks
... ability and is usually highly successful Social engineering relies on tricking and deceiving someone to access a system People are often willing to help or already know the person Requires some knowledge of how the organization is run ...
... ability and is usually highly successful Social engineering relies on tricking and deceiving someone to access a system People are often willing to help or already know the person Requires some knowledge of how the organization is run ...
CNG 131 – Principles of Information Assurance Provides students
... studied, including remote access, e-mail, the Web, directory and file transfer, and wireless data. Common network attacks are introduced. Cryptography basics are incorporated, and operational/organizational security is discussed as it relates to physical security, disaster recovery, and business con ...
... studied, including remote access, e-mail, the Web, directory and file transfer, and wireless data. Common network attacks are introduced. Cryptography basics are incorporated, and operational/organizational security is discussed as it relates to physical security, disaster recovery, and business con ...
Countering Evolving Threats in Distributed Applications
... 3. Set up a covert channel for leaking sensitive information – Only ad-hoc techniques leading to an arms race – Timing channels: perturb timing of actions indiscriminately – Storage channels: “null out” values of all unused storage elements Slide 4/13 ...
... 3. Set up a covert channel for leaking sensitive information – Only ad-hoc techniques leading to an arms race – Timing channels: perturb timing of actions indiscriminately – Storage channels: “null out” values of all unused storage elements Slide 4/13 ...
Cyber Challenges
... • Perceived high cost with low benefit • A highly interactive environment • More powerful computing devices ...
... • Perceived high cost with low benefit • A highly interactive environment • More powerful computing devices ...
The Need for Security
... Outdated hardware or software Reliability problems Management problem Should have plan in place ...
... Outdated hardware or software Reliability problems Management problem Should have plan in place ...
Chapter 1: Security Problems in Computing
... The answer is that yes there is a problem and always has been since the early days when we discovered the operating system and allowed more than one programmer at a time access to the same computer. Easier access to computers has facilitated much of modern commerce, including e-mail and just-in-time ...
... The answer is that yes there is a problem and always has been since the early days when we discovered the operating system and allowed more than one programmer at a time access to the same computer. Easier access to computers has facilitated much of modern commerce, including e-mail and just-in-time ...
Alice and Bob Get Physical: Insights into Physical Layer Security
... About the Talk Although conventional cryptographic security mechanisms are essential to the overall problem of securing wireless networks, these techniques do not directly leverage the unique properties of the wireless domain to address security threats. The properties of the wireless medium are a p ...
... About the Talk Although conventional cryptographic security mechanisms are essential to the overall problem of securing wireless networks, these techniques do not directly leverage the unique properties of the wireless domain to address security threats. The properties of the wireless medium are a p ...
View Presentation - InfoSec Nashville
... Health Insurance Credentials – Health insurance credentials are $20 each. They include names (more than one for spouse & family coverage), date(s) of birth, contract number, group number, type of plan (Individual/Group, HMO/PPO, deductible and copay information), and insurer contact information for ...
... Health Insurance Credentials – Health insurance credentials are $20 each. They include names (more than one for spouse & family coverage), date(s) of birth, contract number, group number, type of plan (Individual/Group, HMO/PPO, deductible and copay information), and insurer contact information for ...
FootPrinting - PSU
... a complete profile of an organization’s security posture using a set of tools and techniques. The profile usually includes detailed information about IP addresses and blocks, range of domain names, remote access, intranet structure, systems connected to the Internet …etc. ...
... a complete profile of an organization’s security posture using a set of tools and techniques. The profile usually includes detailed information about IP addresses and blocks, range of domain names, remote access, intranet structure, systems connected to the Internet …etc. ...
TMDE Web Site
... • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
... • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
recr_presentation_oldest - Computer Science and Engineering
... • Language and Information Technologies (LIT Lab) – Machine Learning applied to NLP and Information Retrieval ...
... • Language and Information Technologies (LIT Lab) – Machine Learning applied to NLP and Information Retrieval ...
Chapter 5 Protecting Information Resources
... Blended threats (e.g., worm launched by Trojan) Rootkits Denial-of-service attacks Social engineering ...
... Blended threats (e.g., worm launched by Trojan) Rootkits Denial-of-service attacks Social engineering ...
Swipe Card Access
... The Id+ card will be used as the key to access to student offices in the HUB-Robeson Center. Security of the office is the responsibility of the card holder accessing the office and is liable for any damage or loss of equipment. A person is not allowed to use another person’s Id+ card to gain access ...
... The Id+ card will be used as the key to access to student offices in the HUB-Robeson Center. Security of the office is the responsibility of the card holder accessing the office and is liable for any damage or loss of equipment. A person is not allowed to use another person’s Id+ card to gain access ...
Lect 1 - Intro
... • The property of being genuine and able to be verified • Confidence in the validity of a transmission, verifiability of a message originator, inputs arriving from trusted sources • Verifiability of a user’s identity Accountability: • Actions can be uniquely traced to their originator • Essential f ...
... • The property of being genuine and able to be verified • Confidence in the validity of a transmission, verifiability of a message originator, inputs arriving from trusted sources • Verifiability of a user’s identity Accountability: • Actions can be uniquely traced to their originator • Essential f ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.