TNS03%20Introduction%20to%20Network%20Security
... For a Trojan horse to spread, you must invite these programs onto your computers. For example, by opening an email attachment or downloading and running a file from the Internet. ...
... For a Trojan horse to spread, you must invite these programs onto your computers. For example, by opening an email attachment or downloading and running a file from the Internet. ...
Curriculum Vitae - ASU People Search
... Solved catch the flag challenges including directory traversal, buffer overflow and Path based vulnerabilities. ...
... Solved catch the flag challenges including directory traversal, buffer overflow and Path based vulnerabilities. ...
Simple TCP/IP Services
... • Security scanning is the process of methodically assessing a system to find known vulnerabilities • Create a list of all known vulnerabilities for your operating system • Check whether each vulnerability exists on your system • Document vulnerabilities that are found • Rank those found by severity ...
... • Security scanning is the process of methodically assessing a system to find known vulnerabilities • Create a list of all known vulnerabilities for your operating system • Check whether each vulnerability exists on your system • Document vulnerabilities that are found • Rank those found by severity ...
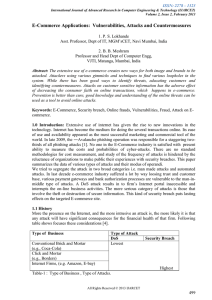
Survey of online attacks on E-Commerce sites
... (3) Ignorance in encrypting hard drives and USB storage disks. Simply encrypting computer hard drives can eliminate a huge portion of information risks. (4) Assuming that patches are under control :There are typically hundreds of missing patches on both workstations and servers. In many situations, ...
... (3) Ignorance in encrypting hard drives and USB storage disks. Simply encrypting computer hard drives can eliminate a huge portion of information risks. (4) Assuming that patches are under control :There are typically hundreds of missing patches on both workstations and servers. In many situations, ...
Access Control Policies
... Host based anitvirus software can also be used to recognize the known signatures Do some sort of integrity check ...
... Host based anitvirus software can also be used to recognize the known signatures Do some sort of integrity check ...
The Top Ten of Security
... – The “reading room” for SANS, a large computer security training organization. ...
... – The “reading room” for SANS, a large computer security training organization. ...
Principal Security Engineer– PAE4IT A. PRIMARY ROLE Working
... 30 Perform analysis of security threats on supported research and education networks. Develop alert, notification, and other information product based on that analysis. Collect, disseminate, and analyze information regarding active network security threats. Respond to requests for security analysis; ...
... 30 Perform analysis of security threats on supported research and education networks. Develop alert, notification, and other information product based on that analysis. Collect, disseminate, and analyze information regarding active network security threats. Respond to requests for security analysis; ...
Introduction to Information Security Chapter N
... Attacks (continued) Mail bombing: also a DoS; attacker routes large quantities of e-mail to target Sniffers: program or device that monitors data traveling over network; can be used both for legitimate purposes and for stealing information from a network Social engineering: using social skill ...
... Attacks (continued) Mail bombing: also a DoS; attacker routes large quantities of e-mail to target Sniffers: program or device that monitors data traveling over network; can be used both for legitimate purposes and for stealing information from a network Social engineering: using social skill ...
Introduction to Information Security Chapter N
... Attacks (continued) Mail bombing: also a DoS; attacker routes large quantities of e-mail to target Sniffers: program or device that monitors data traveling over network; can be used both for legitimate purposes and for stealing information from a network Social engineering: using social skill ...
... Attacks (continued) Mail bombing: also a DoS; attacker routes large quantities of e-mail to target Sniffers: program or device that monitors data traveling over network; can be used both for legitimate purposes and for stealing information from a network Social engineering: using social skill ...
Introduction to Information Security Chapter N
... Attacks (continued) Mail bombing: also a DoS; attacker routes large quantities of e-mail to target Sniffers: program or device that monitors data traveling over network; can be used both for legitimate purposes and for stealing information from a network Social engineering: using social skill ...
... Attacks (continued) Mail bombing: also a DoS; attacker routes large quantities of e-mail to target Sniffers: program or device that monitors data traveling over network; can be used both for legitimate purposes and for stealing information from a network Social engineering: using social skill ...
Identity Theft
... capturing the information in a data storage device through a practice known as "skimming." They may swipe your card for an actual purchase or attach the device to an ATM machine where you may enter or swipe your card. They may steal your wallet or purse. They may complete a "change of address form" ...
... capturing the information in a data storage device through a practice known as "skimming." They may swipe your card for an actual purchase or attach the device to an ATM machine where you may enter or swipe your card. They may steal your wallet or purse. They may complete a "change of address form" ...
Chapter 1 Study Outline
... Biometric systems can also fail: an attacker may force an authentic user to use the biometric scanner and thus gain entry to the system. ...
... Biometric systems can also fail: an attacker may force an authentic user to use the biometric scanner and thus gain entry to the system. ...
Chapter 4
... An attacker can pretend to be an access point and send a forged disassociation frame to a wireless device. This will cause the device to disassociate from the access point. Sending repeated disassociation frames an attacker can continuously prevent any device from communicating with the AP. 17. Expl ...
... An attacker can pretend to be an access point and send a forged disassociation frame to a wireless device. This will cause the device to disassociate from the access point. Sending repeated disassociation frames an attacker can continuously prevent any device from communicating with the AP. 17. Expl ...
Threats and Attacks
... § Threat: Generic term for objects, people who pose a potential danger to an asset (via attacks) § Threat agent: Specific object, person who poses such a danger (by carrying out an attack) § DDoS attacks are a threat; if a hacker carries out a DDoS attack, he’s a threat agent ...
... § Threat: Generic term for objects, people who pose a potential danger to an asset (via attacks) § Threat agent: Specific object, person who poses such a danger (by carrying out an attack) § DDoS attacks are a threat; if a hacker carries out a DDoS attack, he’s a threat agent ...
Form 140-1
... omissions. Use of any information obtained via GYPSDnet is at your own risk. Grande Yellowhead Public School Division specifically denies any responsibility for the accuracy or quality of information obtained through this service. ...
... omissions. Use of any information obtained via GYPSDnet is at your own risk. Grande Yellowhead Public School Division specifically denies any responsibility for the accuracy or quality of information obtained through this service. ...
Chapter 1: Introduction to security
... • Guessing of keys: To gain access to encrypted data and passwords (brute-force attack) • Viruses/ malicious code: programs which capture or destroy data • Port scanning: To discover potential available attack points • DNS interrogation • Social engineering ...
... • Guessing of keys: To gain access to encrypted data and passwords (brute-force attack) • Viruses/ malicious code: programs which capture or destroy data • Port scanning: To discover potential available attack points • DNS interrogation • Social engineering ...
Crypto in data security
... • The science of codes and passwords • Need to prove the identity of the sender and the recipient • The message In the meantime • Should not change the content of the message to make sure ...
... • The science of codes and passwords • Need to prove the identity of the sender and the recipient • The message In the meantime • Should not change the content of the message to make sure ...
Protecting against spear-phishing
... without taking into account the increasingly heavy fines being issued for lax security.4 This was evident in July 2009 when HSBC, the largest bank in the UK, was fined £3.2m for losing confidential customer information. Adding to the overall security challenge is the proliferation of mobile devices. ...
... without taking into account the increasingly heavy fines being issued for lax security.4 This was evident in July 2009 when HSBC, the largest bank in the UK, was fined £3.2m for losing confidential customer information. Adding to the overall security challenge is the proliferation of mobile devices. ...
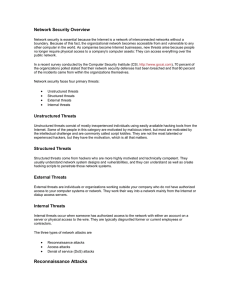
Network Security Overview
... system or application being attacked. Another form of access attacks involves privilege escalation. This is done by legitimate users who have a lower level of access privileges or intruders who have gained lower-privileged access. The intent is to get information or execute procedures that are unaut ...
... system or application being attacked. Another form of access attacks involves privilege escalation. This is done by legitimate users who have a lower level of access privileges or intruders who have gained lower-privileged access. The intent is to get information or execute procedures that are unaut ...
Computer Security Presentation
... September [2004], a 600% increase over the 250 spotted a year ago. Of those, 45% were Trojan horses attempting to steal personal data, the company said. The company also reported a “surge in zombie networks,” saying it had found 400 programs in the past month compared with 17 a year ago. ...
... September [2004], a 600% increase over the 250 spotted a year ago. Of those, 45% were Trojan horses attempting to steal personal data, the company said. The company also reported a “surge in zombie networks,” saying it had found 400 programs in the past month compared with 17 a year ago. ...
ISEC0511
... The process of exploiting vulnerabilities and launching an attack on computers is called hacking. Hackers hack computers, networks, and telephone systems for profit, sometimes even for fun. ...
... The process of exploiting vulnerabilities and launching an attack on computers is called hacking. Hackers hack computers, networks, and telephone systems for profit, sometimes even for fun. ...
Security on the Internet - Australian Federal Police
... A scam might come in the form of an email, contact from an unknown person through websites such as dating sites, online forums or social networking sites. Scams are usually designed to either steal your money or trick you into revealing personal information. They use techniques to manipulate you and ...
... A scam might come in the form of an email, contact from an unknown person through websites such as dating sites, online forums or social networking sites. Scams are usually designed to either steal your money or trick you into revealing personal information. They use techniques to manipulate you and ...
Taxonomy of Computer Security Incidents
... • Failed six satisfying properties = Bad Taxonomy. • Lists can be never ending. ...
... • Failed six satisfying properties = Bad Taxonomy. • Lists can be never ending. ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.