Introduction to Information Security Chapter N
... Sniffers - a program and/or device that can monitor data traveling over a network. Sniffers can be used both for legitimate network management functions and for stealing information from a network Social Engineering - within the context of information security, the process of using social skills ...
... Sniffers - a program and/or device that can monitor data traveling over a network. Sniffers can be used both for legitimate network management functions and for stealing information from a network Social Engineering - within the context of information security, the process of using social skills ...
CEH
... “looking for system administrator to manage Solaris 10 network” This means that the company has Solaris networks on site E.g., www.jobsdb.com ...
... “looking for system administrator to manage Solaris 10 network” This means that the company has Solaris networks on site E.g., www.jobsdb.com ...
Guidelines at a Glance - American Bankers Association
... guidelines are separate and apart from the privacy regulations and notice requirements contained in Section 501 of GLBA. A bank’s information security program must be designed to ensure the security and confidentiality of customer information, protect against any anticipated threats or hazards to th ...
... guidelines are separate and apart from the privacy regulations and notice requirements contained in Section 501 of GLBA. A bank’s information security program must be designed to ensure the security and confidentiality of customer information, protect against any anticipated threats or hazards to th ...
Defense - Northwestern Networks Group
... Not really all to clever, but achieves a success rate of 8.4% (141 victim servers of 1686 target victims). This shows that even a very naive attack strategy can successfully achieve co-residency with a target instance (over a large target set, limits relevancy) ...
... Not really all to clever, but achieves a success rate of 8.4% (141 victim servers of 1686 target victims). This shows that even a very naive attack strategy can successfully achieve co-residency with a target instance (over a large target set, limits relevancy) ...
No Slide Title - ECE Users Pages - Georgia Institute of Technology
... • Novice or newbies – not sure how code works, run kiddy scripts • Experienced hacker – understand the software and are able to create attack code. • Expert hacker – develop tool sets for attack, create code quickly for exposed vulnerabilities. ECE 4883 - Internetwork Security ...
... • Novice or newbies – not sure how code works, run kiddy scripts • Experienced hacker – understand the software and are able to create attack code. • Expert hacker – develop tool sets for attack, create code quickly for exposed vulnerabilities. ECE 4883 - Internetwork Security ...
Assessing Network Security for Northwind Traders What
... attacker to deny his victim’s access to a resource DoS attacks can be divided into three categories: Flooding attacks Resource starvation attacks Disruption of service Note: Denial-of-service attacks should not be launched against your own live production network ...
... attacker to deny his victim’s access to a resource DoS attacks can be divided into three categories: Flooding attacks Resource starvation attacks Disruption of service Note: Denial-of-service attacks should not be launched against your own live production network ...
evesecuref5
... Provide near real time threat analysis of current attacks Early Warning - allows most real-time attacks (viruses, worms and DDoS attacks) to be addressed and mitigated before a hacker releases them Once help desk lights up is usually when most security departments discover that there has been a brea ...
... Provide near real time threat analysis of current attacks Early Warning - allows most real-time attacks (viruses, worms and DDoS attacks) to be addressed and mitigated before a hacker releases them Once help desk lights up is usually when most security departments discover that there has been a brea ...
Authentication and Access Control
... Involves using someone’s personal information, such as social security numbers, to establish bank or credit card accounts that are then left unpaid, leaving the victim with the debts and destroy their credit rating National, state, and local legislation continues to be enacted to deal with this ...
... Involves using someone’s personal information, such as social security numbers, to establish bank or credit card accounts that are then left unpaid, leaving the victim with the debts and destroy their credit rating National, state, and local legislation continues to be enacted to deal with this ...
Computer and Information Security
... • Is the web site I am downloading information from a legitimate one, or a fake? • How do I ensure that the person I just did a financial transaction denies having done it tomorrow or at a later time? • I want to buy some thing online, but I don’t want to let them charge my credit card before they d ...
... • Is the web site I am downloading information from a legitimate one, or a fake? • How do I ensure that the person I just did a financial transaction denies having done it tomorrow or at a later time? • I want to buy some thing online, but I don’t want to let them charge my credit card before they d ...
Chapter. 01
... link, or the disabling of the file management system. DOS - Denial of Service Attacks have ...
... link, or the disabling of the file management system. DOS - Denial of Service Attacks have ...
security threats: a guide for small and medium
... system administrator decided to wipe out the main database. This proved to be disastrous for the company which ended up asking users to retrieve their content from Google’s cache. The company’s management team may also have administrative privileges on their personal computers or laptops. The reason ...
... system administrator decided to wipe out the main database. This proved to be disastrous for the company which ended up asking users to retrieve their content from Google’s cache. The company’s management team may also have administrative privileges on their personal computers or laptops. The reason ...
InterScan Messaging Security Solutions
... – Goal = to acquire a valid email list for the company – Can use the list later for a targeted attack, such as a phishing, virus, spyware, or spam attack • Bounced Mail Attacks – Spoofs a legitimate company by inserting its domain as the email sender – When the receiving servers bounce the email, th ...
... – Goal = to acquire a valid email list for the company – Can use the list later for a targeted attack, such as a phishing, virus, spyware, or spam attack • Bounced Mail Attacks – Spoofs a legitimate company by inserting its domain as the email sender – When the receiving servers bounce the email, th ...
Workstar iGuard
... presents his smartcard to get authorized (such as during high-traffic period), or requires the high-security fingerprint verification (such as after office hours or during weekends and holidays). 2. Access Rights: When you can easily and conveniently assign different access rights to your employees, ...
... presents his smartcard to get authorized (such as during high-traffic period), or requires the high-security fingerprint verification (such as after office hours or during weekends and holidays). 2. Access Rights: When you can easily and conveniently assign different access rights to your employees, ...
Information Privacy What is information privacy?
... What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
... What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
03-WAS Common Threats - Professional Data Management
... • In the field of computer security, phishing is the criminally fraudulent process of attempting to acquire sensitive information such as usernames, passwords and credit card details by masquerading as a trustworthy entity in an electronic communication. ...
... • In the field of computer security, phishing is the criminally fraudulent process of attempting to acquire sensitive information such as usernames, passwords and credit card details by masquerading as a trustworthy entity in an electronic communication. ...
Chapter11
... for you in its database and sends that number to your browser. Browser in turn creates a cookie file based on that number and stores cookie file on your hard disk. ...
... for you in its database and sends that number to your browser. Browser in turn creates a cookie file based on that number and stores cookie file on your hard disk. ...
Babu Madhav Institute of Information Technology, UTU 2017
... 7. ___________________________ attacks are used to commit financial crimes. 8. The first stage of web jacking is _____________________. 9. An illegal intrusion , posing as a genuine user is known as ______________________. 10. _________________ mean visual deception. 11. ___________________ are the ...
... 7. ___________________________ attacks are used to commit financial crimes. 8. The first stage of web jacking is _____________________. 9. An illegal intrusion , posing as a genuine user is known as ______________________. 10. _________________ mean visual deception. 11. ___________________ are the ...
Babu Madhav Institute of Information Technology, UTU 2015
... 7. ___________________________ attacks are used to commit financial crimes. 8. The first stage of web jacking is _____________________. 9. An illegal intrusion , posing as a genuine user is known as ______________________. 10. _________________ mean visual deception. 11. ___________________ are the ...
... 7. ___________________________ attacks are used to commit financial crimes. 8. The first stage of web jacking is _____________________. 9. An illegal intrusion , posing as a genuine user is known as ______________________. 10. _________________ mean visual deception. 11. ___________________ are the ...
Chapter 4
... 6. A logic bomb is a computer program that lies dormant until it is triggered by a specific logical event. Once triggered, the program can perform any number of malicious activities. Logic bombs are extremely difficult to detect before they are triggered since they are often embedded in large comput ...
... 6. A logic bomb is a computer program that lies dormant until it is triggered by a specific logical event. Once triggered, the program can perform any number of malicious activities. Logic bombs are extremely difficult to detect before they are triggered since they are often embedded in large comput ...
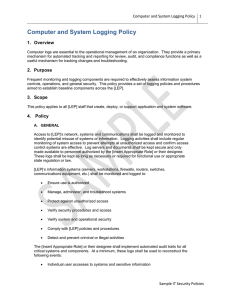
Computer and System Logging Policy
... Access to [LEP]’s network, systems and communications shall be logged and monitored to identify potential misuse of systems or information. Logging activities shall include regular monitoring of system access to prevent attempts at unauthorized access and confirm access control systems are effective ...
... Access to [LEP]’s network, systems and communications shall be logged and monitored to identify potential misuse of systems or information. Logging activities shall include regular monitoring of system access to prevent attempts at unauthorized access and confirm access control systems are effective ...
security - Binus Repository
... • Reduce the potential liability from misuse of corporate information and assets • Eliminate costly and archaic investigation/auditing procedures • Increase information systems’ reliability and availability by conducting investigations while systems are online. ...
... • Reduce the potential liability from misuse of corporate information and assets • Eliminate costly and archaic investigation/auditing procedures • Increase information systems’ reliability and availability by conducting investigations while systems are online. ...
General IT Auditing Techniques
... attacker to deny his victim’s access to a resource DoS attacks can be divided into three categories: Flooding attacks Resource starvation attacks Disruption of service Note: Denial-of-service attacks should not be launched against your own live production network ...
... attacker to deny his victim’s access to a resource DoS attacks can be divided into three categories: Flooding attacks Resource starvation attacks Disruption of service Note: Denial-of-service attacks should not be launched against your own live production network ...
Playing it Safe: Document Destruction Best Practices - Shred-it
... All organisations possess important confidential information about their own operations and about their customers which increases the risk for becoming a target for identity theft and fraud. In spite of economic pressures, according to research into data security breaches carried out by IBM1, 64% of ...
... All organisations possess important confidential information about their own operations and about their customers which increases the risk for becoming a target for identity theft and fraud. In spite of economic pressures, according to research into data security breaches carried out by IBM1, 64% of ...
Discovering Computers Fundamentals 3rd Edition
... Internet and Network Attacks What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
... Internet and Network Attacks What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.