Breaking Trust On The Internet
... used for different purposes depending upon the requirement. • Easy and cheap communication • Share files with others easily. • Loads of information • Financial Transaction • services ...
... used for different purposes depending upon the requirement. • Easy and cheap communication • Share files with others easily. • Loads of information • Financial Transaction • services ...
20121101
... Karl’s Changes • What follows would be the changes I’d make at RSA. • Note, they are a commercial company and do not have the open requirements higher education has. Two different beasts. • If I were to implement these, very likely I’d be doing a different job… ...
... Karl’s Changes • What follows would be the changes I’d make at RSA. • Note, they are a commercial company and do not have the open requirements higher education has. Two different beasts. • If I were to implement these, very likely I’d be doing a different job… ...
Abstract - Compassion Software Solutions
... Malicious URLs have been widely used to mount various cyber attacks including spamming, phishing and malware. Phishing is a security attack that involves obtaining sensitive or otherwise private data by presenting oneself as a trustworthy entity. Phishes often exploit users’ trust on the appearance ...
... Malicious URLs have been widely used to mount various cyber attacks including spamming, phishing and malware. Phishing is a security attack that involves obtaining sensitive or otherwise private data by presenting oneself as a trustworthy entity. Phishes often exploit users’ trust on the appearance ...
ICBA Encourages Consumers to Protect their Data during Cyber
... Remain cautious of someone who isn’t who they say they are or if the name and area don’t match what appears on caller ID. This is often how spoofing occurs. ...
... Remain cautious of someone who isn’t who they say they are or if the name and area don’t match what appears on caller ID. This is often how spoofing occurs. ...
Prevent Online Fraud and Identity Theft
... information from Identity Theft is crucial. There are many ways the unscrupulous can gain access to information such as your name, Social Security Number, credit card or bank account numbers, or other identifying information to commit fraud or other crimes. E-Mail Phishing - Involves you receiving a ...
... information from Identity Theft is crucial. There are many ways the unscrupulous can gain access to information such as your name, Social Security Number, credit card or bank account numbers, or other identifying information to commit fraud or other crimes. E-Mail Phishing - Involves you receiving a ...
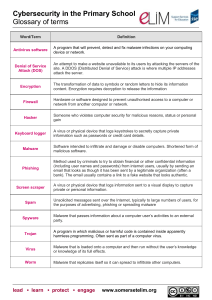
Open ended challenge rationale
... Someone who violates computer security for malicious reasons, status or personal gain ...
... Someone who violates computer security for malicious reasons, status or personal gain ...
1 Introduction To Information Technology
... Defining Information Technology • Information Technologies are systems of hardware and/or software that capture, process, exchange, store and/or present information using electrical, magnetic and/or electromagnetic energy. ...
... Defining Information Technology • Information Technologies are systems of hardware and/or software that capture, process, exchange, store and/or present information using electrical, magnetic and/or electromagnetic energy. ...
• Overview of Cyber Security & need of cyber security • Introduction
... COMPUTER SCIENCE AND ENGINEERING DEPARTMENT Name of Course ...
... COMPUTER SCIENCE AND ENGINEERING DEPARTMENT Name of Course ...
Intimidation Attack
... Usually targets someone they sense is frustrated with their current job position The victim wants to prove how smart or knowledgeable they are and provides sensitive information or even access to the systems or data Attacker may pretend to be law enforcement, the victim feels honored to be hel ...
... Usually targets someone they sense is frustrated with their current job position The victim wants to prove how smart or knowledgeable they are and provides sensitive information or even access to the systems or data Attacker may pretend to be law enforcement, the victim feels honored to be hel ...
Preventing Social Engineering
... Don’t answer survey calls Check that vendor calls are legitimate ...
... Don’t answer survey calls Check that vendor calls are legitimate ...
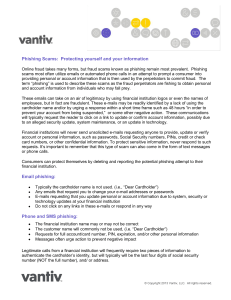
Phishing Scams - Corner Stone Credit Union
... to an alleged security update, system maintenance, or an update in technology. Financial institutions will never send unsolicited e-mails requesting anyone to provide, update or verify account or personal information, such as passwords, Social Security numbers, PINs, credit or check card numbers, or ...
... to an alleged security update, system maintenance, or an update in technology. Financial institutions will never send unsolicited e-mails requesting anyone to provide, update or verify account or personal information, such as passwords, Social Security numbers, PINs, credit or check card numbers, or ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.