01-Intro
... 3. Try all the words in an electronic dictionary(60,000). 4. Collect information about the user’s hobbies, family names, birthday, etc. 5. Try user’s phone number, social security number, street address, etc. 6. Try all license plate numbers (123XYZ). These can be automated and run off-line if the p ...
... 3. Try all the words in an electronic dictionary(60,000). 4. Collect information about the user’s hobbies, family names, birthday, etc. 5. Try user’s phone number, social security number, street address, etc. 6. Try all license plate numbers (123XYZ). These can be automated and run off-line if the p ...
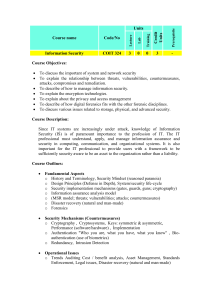
Course name Code/No Units Credit Units Prerequisite Lecture Lab
... To discuss the important of system and network security To explain the relationship between threats, vulnerabilities, countermeasures, attacks, compromises and remediation. To describe of how to manage information security. To explain the encryption technologies. To explain about the privacy and acc ...
... To discuss the important of system and network security To explain the relationship between threats, vulnerabilities, countermeasures, attacks, compromises and remediation. To describe of how to manage information security. To explain the encryption technologies. To explain about the privacy and acc ...
Computer Crimes - Crime Prevention HQ
... ● Forward letter to the U.S. Secret Service as they are spearheading the effort against these scams. ● Consumers or businesses that claim to have lost money in a Nigerian scam should call their local Secret Service office ● More information at FDLE website: http://www.fdle.state.fl.us/Fc3/nigerian.h ...
... ● Forward letter to the U.S. Secret Service as they are spearheading the effort against these scams. ● Consumers or businesses that claim to have lost money in a Nigerian scam should call their local Secret Service office ● More information at FDLE website: http://www.fdle.state.fl.us/Fc3/nigerian.h ...
Information Systems and Networks
... A major problem with software is the presence of hidden bugs or program code defects Zero defects cannot be achieved in larger programs. Complete testing simply is not possible. Fully testing programs that contain thousands of choices and millions of paths would require thousands of years Flaws in c ...
... A major problem with software is the presence of hidden bugs or program code defects Zero defects cannot be achieved in larger programs. Complete testing simply is not possible. Fully testing programs that contain thousands of choices and millions of paths would require thousands of years Flaws in c ...
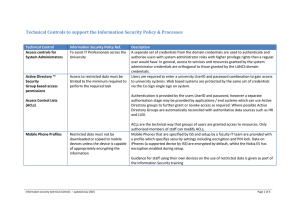
Technical Controls to support the Information
... • Bandwidth Usage • IP Address Furthermore, when a user connects to the network, the PASS system makes an informed decision about what level of network access to allow them based on various criteria such as machine status (i.e. whether known to be virus infected user rights and departmental preferen ...
... • Bandwidth Usage • IP Address Furthermore, when a user connects to the network, the PASS system makes an informed decision about what level of network access to allow them based on various criteria such as machine status (i.e. whether known to be virus infected user rights and departmental preferen ...
Privacy Policy - Groesbeck Investment Management
... use of, and access to, customer information. The following policies apply to current and former clients of Groesbeck Investment Management. In order to conduct and process your business in an accurate and efficient manner, we must collect non-public personal information about you. We limit the colle ...
... use of, and access to, customer information. The following policies apply to current and former clients of Groesbeck Investment Management. In order to conduct and process your business in an accurate and efficient manner, we must collect non-public personal information about you. We limit the colle ...
Assignment #2 S.Popovic
... Compromised the LA bus transfer system to get free bus rides. Evading the FBI Gaining full admin privileges to a IBM minicomputer at the computer learning center in LA in order to win a bet. Hacked Motorola, NEC, Nokia, and Sun Microsystems. At the time of his arrest, Kevin was the most-wanted compu ...
... Compromised the LA bus transfer system to get free bus rides. Evading the FBI Gaining full admin privileges to a IBM minicomputer at the computer learning center in LA in order to win a bet. Hacked Motorola, NEC, Nokia, and Sun Microsystems. At the time of his arrest, Kevin was the most-wanted compu ...
Annex 1
... on known security flaws in hardware and software. Using almost any search engine on the internet, average internet users can quickly find information describing how to break into various systems by exploiting known security weaknesses. Attackers may also breach security by using automated tools to p ...
... on known security flaws in hardware and software. Using almost any search engine on the internet, average internet users can quickly find information describing how to break into various systems by exploiting known security weaknesses. Attackers may also breach security by using automated tools to p ...
Abstract
... incoming credit card transaction is not accepted by the trained HMM with sufficiently high probability, it is considered to be fraudulent. At the same time, we try to ensure that genuine transactions are not rejected. In the new card module, the customer gives there information to enroll a new card. ...
... incoming credit card transaction is not accepted by the trained HMM with sufficiently high probability, it is considered to be fraudulent. At the same time, we try to ensure that genuine transactions are not rejected. In the new card module, the customer gives there information to enroll a new card. ...
Access Security Requirements
... 3.1 Develop and follow procedures to ensure that data is protected throughout its entire information lifecycle (from creation, transformation, use, storage, and secure destruction0 regardless of the media used to store the data (i.e., tape, disk, paper, etc.) 3.2 All credit reporting agency data is ...
... 3.1 Develop and follow procedures to ensure that data is protected throughout its entire information lifecycle (from creation, transformation, use, storage, and secure destruction0 regardless of the media used to store the data (i.e., tape, disk, paper, etc.) 3.2 All credit reporting agency data is ...
E-Commerce Technology Risk and Security
... While attackers were still on systems an average of 156 days before being detected, elimination of stored data greatly reduces the data loss exposure. ...
... While attackers were still on systems an average of 156 days before being detected, elimination of stored data greatly reduces the data loss exposure. ...
Leaders` Forum, March 16, 2006 - University of Western Ontario
... service specific protection • Provides systems administrators with a quarantined network for new or infected machines • Provides systems ...
... service specific protection • Provides systems administrators with a quarantined network for new or infected machines • Provides systems ...
Introduction to Operations Security (OPSEC)
... Do not discuss critical information with anyone who does not have a “need-to-know.” Safeguard sensitive information the same way you would protect classified information. Use common sense and camouflage sensitive information. By providing OPSEC training to all employees, every employee becomes a “se ...
... Do not discuss critical information with anyone who does not have a “need-to-know.” Safeguard sensitive information the same way you would protect classified information. Use common sense and camouflage sensitive information. By providing OPSEC training to all employees, every employee becomes a “se ...
spear-phishing attacks
... Some of the most notorious cyber crimes in recent history — such as the attacks on major banks, media companies and even security firms — started with just one person clicking on a spear-phishing email. Spear phishing is on the rise because it works. Traditional security defenses simply do not detec ...
... Some of the most notorious cyber crimes in recent history — such as the attacks on major banks, media companies and even security firms — started with just one person clicking on a spear-phishing email. Spear phishing is on the rise because it works. Traditional security defenses simply do not detec ...
PowerPoint Presentation - Lead
... • Is the process of preventing and detecting unauthorized use of your computer • Prevention measures help you to stop unauthorized users from accessing any part of your computer system. • Detection helps you to determine whether or not someone attempted to break into your system, if they were succes ...
... • Is the process of preventing and detecting unauthorized use of your computer • Prevention measures help you to stop unauthorized users from accessing any part of your computer system. • Detection helps you to determine whether or not someone attempted to break into your system, if they were succes ...
Skating on Stilts
... – Fewer than 60% patched and updated software on a regular schedule – User name and password the most common form of login/authentication – more than three-quarters of SCADA/ICS systems are connected to an IP network or the Internet • nearly half of those admitted that these connections create unres ...
... – Fewer than 60% patched and updated software on a regular schedule – User name and password the most common form of login/authentication – more than three-quarters of SCADA/ICS systems are connected to an IP network or the Internet • nearly half of those admitted that these connections create unres ...
Social engineering - Information Systems
... Implement a security plan to prevent break-ins Have a plan if break-ins do occur Make backups! Only allow access to key employees Change passwords frequently Keep stored information secure Use antivirus software Use biometrics for access to computing resources Hire trustworthy empl ...
... Implement a security plan to prevent break-ins Have a plan if break-ins do occur Make backups! Only allow access to key employees Change passwords frequently Keep stored information secure Use antivirus software Use biometrics for access to computing resources Hire trustworthy empl ...
Security Requirements
... those that have access to information that they are not suppose to gain access to. “In 1999, some students at the University of the South Pacific managed to get access to the system and retrieve a list of all students email passwords. This allowed them to send abusive messages to others using othe ...
... those that have access to information that they are not suppose to gain access to. “In 1999, some students at the University of the South Pacific managed to get access to the system and retrieve a list of all students email passwords. This allowed them to send abusive messages to others using othe ...
Security Risks - Bannerman High School
... – Encrypting data being sent across networks is a sensible precaution e.g. when paying for something bought on-line you have to send your card details. – Websites that collect your card details should have https in their address: that means they are using encryption to send your information. ...
... – Encrypting data being sent across networks is a sensible precaution e.g. when paying for something bought on-line you have to send your card details. – Websites that collect your card details should have https in their address: that means they are using encryption to send your information. ...
Click to
... The message usually says that you need to "update" or "validate" your account information. It might threaten some dire consequence if you don't respond. The message directs you to a Web site that looks just like a legitimate organization's site, but it isn't. The purpose of the bogus site? To trick ...
... The message usually says that you need to "update" or "validate" your account information. It might threaten some dire consequence if you don't respond. The message directs you to a Web site that looks just like a legitimate organization's site, but it isn't. The purpose of the bogus site? To trick ...
New Law Requires Businesses in California to Report Electronic Break-Ins
... information” is defined as an individual’s first name or first initial and last name in combination with one or more of the following: (1) social security number; (2) driver’s license number or California Identification Card number; or (3) account number, credit card or debit card number, in combina ...
... information” is defined as an individual’s first name or first initial and last name in combination with one or more of the following: (1) social security number; (2) driver’s license number or California Identification Card number; or (3) account number, credit card or debit card number, in combina ...
Computer Security: Principles and Practice, 1/e
... • guarding against improper information modification or destruction, • including ensuring information nonrepudiation and authenticity ...
... • guarding against improper information modification or destruction, • including ensuring information nonrepudiation and authenticity ...
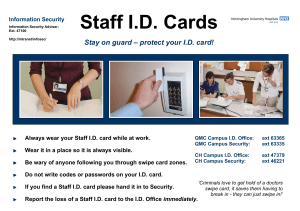
Staff ID Cards Poster
... Do not write codes or passwords on your I.D. card. If you find a Staff I.D. card please hand it in to Security. Report the loss of a Staff I.D. card to the I.D. Office immediately. ...
... Do not write codes or passwords on your I.D. card. If you find a Staff I.D. card please hand it in to Security. Report the loss of a Staff I.D. card to the I.D. Office immediately. ...
Newfield National Bank > Home
... call the victim and pretend to be Internal Revenue Service (IRS) agents. In addition, there are malicious actors who use the tax season to spread malware and phishing emails. Tax scams where the malicious actor files the return in the victim’s name include both identity theft and identity fraud, as ...
... call the victim and pretend to be Internal Revenue Service (IRS) agents. In addition, there are malicious actors who use the tax season to spread malware and phishing emails. Tax scams where the malicious actor files the return in the victim’s name include both identity theft and identity fraud, as ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.