PPT - pantherFILE
... • Without trust, information systems cannot be built—too complex • Trust abuse – security holes come from what you trust – Trust in a system could be defined as the level of confidence in its integrity. – Nevertheless, just like it is hard to provide computer security with reasonable guarantees, it ...
... • Without trust, information systems cannot be built—too complex • Trust abuse – security holes come from what you trust – Trust in a system could be defined as the level of confidence in its integrity. – Nevertheless, just like it is hard to provide computer security with reasonable guarantees, it ...
SAFEnet Becomes First PACS Platform to
... of federal, state and local governments because they cost-effectively deliver the most flexible, reliable and advanced unified security solution available in the industry. The same holds true with commercial organizations across the nation who regularly do business with the Federal Government and Do ...
... of federal, state and local governments because they cost-effectively deliver the most flexible, reliable and advanced unified security solution available in the industry. The same holds true with commercial organizations across the nation who regularly do business with the Federal Government and Do ...
Network Security Chapter 14
... ____ 15. A ____ policy is designed to produce a standardized framework for classifying information assets. a. classification of information c. service level agreement b. change management d. disposal and destruction ____ 16. ____ refers to a methodology for making changes and keeping track of those ...
... ____ 15. A ____ policy is designed to produce a standardized framework for classifying information assets. a. classification of information c. service level agreement b. change management d. disposal and destruction ____ 16. ____ refers to a methodology for making changes and keeping track of those ...
JRA1.4 AAs in eduGAIN
... with existing architectures (to simplify technical adoption of such a solution by all the participants to the federation). ● Leverage the existing federations in building the reciprocal trust, needed to guarantee security. ...
... with existing architectures (to simplify technical adoption of such a solution by all the participants to the federation). ● Leverage the existing federations in building the reciprocal trust, needed to guarantee security. ...
Fraudulent Emails, Websites and Phishing Variations Fraudulent
... message. Fraudsters may have the ability to spoof their caller ID so it could appear that the telephone call is coming from a legitimate company. Fraudsters may also have identifying customer information, such as your name, which they may use to make the call appear more authentic. If you are uncomf ...
... message. Fraudsters may have the ability to spoof their caller ID so it could appear that the telephone call is coming from a legitimate company. Fraudsters may also have identifying customer information, such as your name, which they may use to make the call appear more authentic. If you are uncomf ...
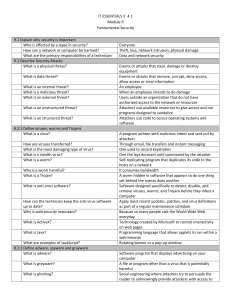
IT ESSENTIALS V. 4.1 Module 9 Fundamental Security 9.1 Explain
... An infected computer located at difference geographical locations used to launch denial of service attacks Junk mail, unsolicited email No subject line, incomplete return address, return email not sent by user, computer generated email A person who is able to gain access by tricking people into prov ...
... An infected computer located at difference geographical locations used to launch denial of service attacks Junk mail, unsolicited email No subject line, incomplete return address, return email not sent by user, computer generated email A person who is able to gain access by tricking people into prov ...
slides - University of Cambridge Computer Laboratory
... – pattern of activity from China much more complex than needed for deniability – pattern of intelligence priorities disclosed by Canadian compromise of the Chinese control server ...
... – pattern of activity from China much more complex than needed for deniability – pattern of intelligence priorities disclosed by Canadian compromise of the Chinese control server ...
Phishing/Email Scams - Minot State University
... Phishing/Email Scams Phishing is the use of email and fraudulent web sites to trick people into disclosing personal financial or identity information, such as credit card or Social Security numbers, user names, passwords and addresses. Although most "phishes" come as email, phishing scams can also c ...
... Phishing/Email Scams Phishing is the use of email and fraudulent web sites to trick people into disclosing personal financial or identity information, such as credit card or Social Security numbers, user names, passwords and addresses. Although most "phishes" come as email, phishing scams can also c ...
Preface
... Claude Shannon in 1949, as the foundation of modern cryptology. However, at that time, cryptographic research was mostly restricted to government agencies and the military. That situation gradually changed with the expanding telecommunication industry. Communication systems that were completely cont ...
... Claude Shannon in 1949, as the foundation of modern cryptology. However, at that time, cryptographic research was mostly restricted to government agencies and the military. That situation gradually changed with the expanding telecommunication industry. Communication systems that were completely cont ...
Information Security
... What is Information Security? • Information Security is: – To protect the confidentiality, integrity and availability of information assets – It includes the systems and hardware that use, store, and transmit the information ...
... What is Information Security? • Information Security is: – To protect the confidentiality, integrity and availability of information assets – It includes the systems and hardware that use, store, and transmit the information ...
ITS_8_Security Vocab Answers
... A type of software that is capable of recording every keystroke you make on a keyboard and placing it into a log file, which is usually encrypted. A keylogger may be used legitimately by the owner of the computer system, or set as spyware for unauthorized surveillance. Phishing Sending an e-mail to ...
... A type of software that is capable of recording every keystroke you make on a keyboard and placing it into a log file, which is usually encrypted. A keylogger may be used legitimately by the owner of the computer system, or set as spyware for unauthorized surveillance. Phishing Sending an e-mail to ...
Victims who were Hacked PowerPoint Presentation
... stealing info from a person that allows you to access anything in their name ...
... stealing info from a person that allows you to access anything in their name ...
Introduction - Personal Web Pages
... – In CA, there is a webpage listing all people that donate to Proposition 8 ballot measure ...
... – In CA, there is a webpage listing all people that donate to Proposition 8 ballot measure ...
DO NOT - Middlebury College
... Sophos anti-virus does offer some web protections which help to prevent the download activity of FakeAV. ...
... Sophos anti-virus does offer some web protections which help to prevent the download activity of FakeAV. ...
Federal Bio
... Mr. Crane is a contributing author of multiple books, including “SPECIAL OPS: Host and Network Security for Microsoft, UNIX and Oracle”. He is also an adjunct professor in the Carnegie Mellon University Masters of Information System Management program, where he co-instructs the courses “Hacking Expo ...
... Mr. Crane is a contributing author of multiple books, including “SPECIAL OPS: Host and Network Security for Microsoft, UNIX and Oracle”. He is also an adjunct professor in the Carnegie Mellon University Masters of Information System Management program, where he co-instructs the courses “Hacking Expo ...
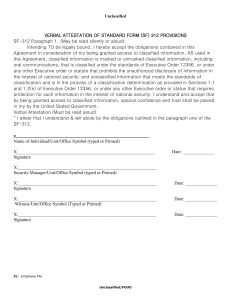
Verbal Attestation of Standard form SF
... Intending TO be legally bound, I hereby accept the obligations contained in this Agreement in consideration of my being granted access to classified information. AS used in this Agreement, classified information is marked or unmarked classified information, including oral communications, that is cla ...
... Intending TO be legally bound, I hereby accept the obligations contained in this Agreement in consideration of my being granted access to classified information. AS used in this Agreement, classified information is marked or unmarked classified information, including oral communications, that is cla ...
chapter 5 – basic security
... resources and private information, such as bank account numbers or passwords. ...
... resources and private information, such as bank account numbers or passwords. ...
Malicious Cryptography : Exposing Cryptovirology
... Terms such as cryptovirology, malware, kleptogram, or kleptography may be unfamiliar to the reader, but the basic concepts associated with them certainly are familiar. Everyone knows—often from sad experience—about viruses, Trojan horses, and worms and many have had a password “harvested” by a piece ...
... Terms such as cryptovirology, malware, kleptogram, or kleptography may be unfamiliar to the reader, but the basic concepts associated with them certainly are familiar. Everyone knows—often from sad experience—about viruses, Trojan horses, and worms and many have had a password “harvested” by a piece ...
Document
... Sophos anti-virus does offer some web protections which help to prevent the download activity of FakeAV. ...
... Sophos anti-virus does offer some web protections which help to prevent the download activity of FakeAV. ...
Uniqua Consulting Gmbh - Data Mining Analyst
... Data Mining Analyst – Luanda, Angola The successful candidate will work in a dynamic team of talented analysts that enjoy the opportunity to work in a young organization with very high potential. He or she will analyze and characterize data to help protect networks from an ever present threat and to ...
... Data Mining Analyst – Luanda, Angola The successful candidate will work in a dynamic team of talented analysts that enjoy the opportunity to work in a young organization with very high potential. He or she will analyze and characterize data to help protect networks from an ever present threat and to ...
Phishing and whaling – Don`t get hooked!
... Phishing is an attempt to obtain sensitive information such as usernames, passwords, credit card details or money transfers usually by masquerading as a trustworthy entity or person. Like the word fishing, it is a technique that uses bait to catch the victim. Phishing emails often contain links to w ...
... Phishing is an attempt to obtain sensitive information such as usernames, passwords, credit card details or money transfers usually by masquerading as a trustworthy entity or person. Like the word fishing, it is a technique that uses bait to catch the victim. Phishing emails often contain links to w ...
Cybersecurity - Queen`s Wiki
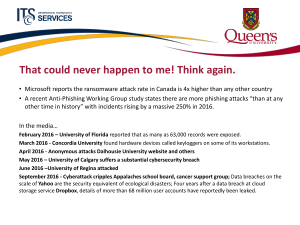
... That could never happen to me! Think again. • Microsoft reports the ransomware attack rate in Canada is 4x higher than any other country • A recent Anti-Phishing Working Group study states there are more phishing attacks “than at any other time in history” with incidents rising by a massive 250% in ...
... That could never happen to me! Think again. • Microsoft reports the ransomware attack rate in Canada is 4x higher than any other country • A recent Anti-Phishing Working Group study states there are more phishing attacks “than at any other time in history” with incidents rising by a massive 250% in ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.