www.itgovernance.co.uk/training
... People are your weakest link – Strengthen awareness to improve the robustness of your ISMS Training aids are a tool for getting general staff involved in discussing and understanding the sometimes complex data security issues which might impinge on how they work – and to do so in a low impact, low p ...
... People are your weakest link – Strengthen awareness to improve the robustness of your ISMS Training aids are a tool for getting general staff involved in discussing and understanding the sometimes complex data security issues which might impinge on how they work – and to do so in a low impact, low p ...
Support: Ticket, Process, and Expectations
... Malware and Key Loggers can record keystrokes and report them to a 3rd party ...
... Malware and Key Loggers can record keystrokes and report them to a 3rd party ...
Chapter 1 THE INFORMATION AGE IN WHICH YOU LIVE Changing
... o Web log – one line of information for every visitor to a Web site o Clickstream – records information about you during a Web surfing session such as what Web sites you visited, how long you were there, what ads you looked at, and what you bought. o Anonymous Web browsing (AWB) – hides your identit ...
... o Web log – one line of information for every visitor to a Web site o Clickstream – records information about you during a Web surfing session such as what Web sites you visited, how long you were there, what ads you looked at, and what you bought. o Anonymous Web browsing (AWB) – hides your identit ...
Click to add title - toostusuudised.ee
... 4 They are well-funded and well-staffed, perhaps operating with the support of military or state intelligence organizations. 5 They are more likely to target organizations of strategic importance, such as government agencies, defense contractors, high profile manufacturers, critical infrastructure o ...
... 4 They are well-funded and well-staffed, perhaps operating with the support of military or state intelligence organizations. 5 They are more likely to target organizations of strategic importance, such as government agencies, defense contractors, high profile manufacturers, critical infrastructure o ...
Introduction - GMU Computer Science
... • Installs spyware that watches for POST data, such as usernames and passwords, which is then sent onto a third party system • Installs spyware that dredges the host PC for information from caches and cookies • “Urgent” messages that the user’s account has been compromised, and they need to take som ...
... • Installs spyware that watches for POST data, such as usernames and passwords, which is then sent onto a third party system • Installs spyware that dredges the host PC for information from caches and cookies • “Urgent” messages that the user’s account has been compromised, and they need to take som ...
Policy Template
... volunteers; or suspension or expulsion in the case of a student. Additionally, individuals are subject to loss of [AGENCY] Information Resources access privileges, civil, and criminal prosecution. ...
... volunteers; or suspension or expulsion in the case of a student. Additionally, individuals are subject to loss of [AGENCY] Information Resources access privileges, civil, and criminal prosecution. ...
Safeguarding of Unclassified Controlled Technical Information (UCTI)
... Contractors that don’t have all of the NIST controls implemented must submit a written explanation of how 1) the required security control(s) is not applicable, or 2) an alternative control or protective measure is used to achieve equivalent protection. This means all 51 controls must be addressed, ...
... Contractors that don’t have all of the NIST controls implemented must submit a written explanation of how 1) the required security control(s) is not applicable, or 2) an alternative control or protective measure is used to achieve equivalent protection. This means all 51 controls must be addressed, ...
Document
... code that replicates itself or inserts copies or new versions of itself in other programs. Worm Worms are parasitic computer programs that replicate, but unlike viruses, do not infect other computer program files. Worms can create copies on the same computer, or can send the copies to other comput ...
... code that replicates itself or inserts copies or new versions of itself in other programs. Worm Worms are parasitic computer programs that replicate, but unlike viruses, do not infect other computer program files. Worms can create copies on the same computer, or can send the copies to other comput ...
Slide 1 - IITK - Indian Institute of Technology Kanpur
... • Hide the Service Set ID or SSID :Sometimes changing the SSID is also not full proof as hackers have advanced methods to intrude into a wireless network if the SSID is known. To prevent such cases the SSID needs to be hidden. Router configuration softwares allow the SSID to be hidden and the steps ...
... • Hide the Service Set ID or SSID :Sometimes changing the SSID is also not full proof as hackers have advanced methods to intrude into a wireless network if the SSID is known. To prevent such cases the SSID needs to be hidden. Router configuration softwares allow the SSID to be hidden and the steps ...
Information Security in the New Millennium
... Information must be available in a timely fashion. We must also establish and maintain the authenticity (correct attribution) of documents we create, send and ...
... Information must be available in a timely fashion. We must also establish and maintain the authenticity (correct attribution) of documents we create, send and ...
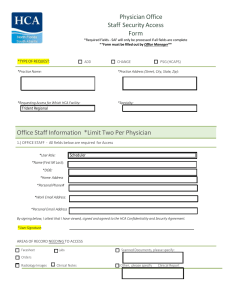
Physician Office Staff Security Access Form Office Staff Information
... patients’ health information. Additionally, the Company must assure the confidentiality of its human resources, payroll, fiscal, research, internal reporting, strategic planning information, credentialing, intellectual property, or any information that contains Social Security numbers, health insura ...
... patients’ health information. Additionally, the Company must assure the confidentiality of its human resources, payroll, fiscal, research, internal reporting, strategic planning information, credentialing, intellectual property, or any information that contains Social Security numbers, health insura ...
"O brave new world, that has such people in`t
... Beyond the company's own site, individual employees or customers may have visited any number of danger spots that lets criminals in. Germano noted that attacks on small businesses (which may link to larger suppliers or customers) have more than doubled over the past year. "Companies want to be frien ...
... Beyond the company's own site, individual employees or customers may have visited any number of danger spots that lets criminals in. Germano noted that attacks on small businesses (which may link to larger suppliers or customers) have more than doubled over the past year. "Companies want to be frien ...
E-Commerce and Bank Security
... User passwords when retrieving sensitive information from the database server ...
... User passwords when retrieving sensitive information from the database server ...
policies - NY Capital Region Chapter
... Firewalls allow or block traffic according to configured Access Control List (ACL) Firewalls typically block traffic from the Internet into a private network ...
... Firewalls allow or block traffic according to configured Access Control List (ACL) Firewalls typically block traffic from the Internet into a private network ...
PROTECTING INFORMATION RESOURCES
... It turns out that scammers have been posing as small businesses to improperly access data about individuals. The scammers would open accounts with ChoicePoint masquerading as small businesses and then improperly use the sensitive personal data for identity fraud. 145,000 American consumer records at ...
... It turns out that scammers have been posing as small businesses to improperly access data about individuals. The scammers would open accounts with ChoicePoint masquerading as small businesses and then improperly use the sensitive personal data for identity fraud. 145,000 American consumer records at ...
CS 494/594 Computer and Network Security - UTK-EECS
... Threats, Vulnerabilities, Attacks How to address these problems? Control: an action, device, procedure, or technique that removes or reduces a vulnerability, and subsequently blocks threats and attacks This class focuses on the various controls and how they enhance a system’s security ...
... Threats, Vulnerabilities, Attacks How to address these problems? Control: an action, device, procedure, or technique that removes or reduces a vulnerability, and subsequently blocks threats and attacks This class focuses on the various controls and how they enhance a system’s security ...
CS 494/594 Computer and Network Security - UTK-EECS
... Threats, Vulnerabilities, Attacks How to address these problems? Control: an action, device, procedure, or technique that removes or reduces a vulnerability, and subsequently blocks threats and attacks This class focuses on the various controls and how they enhance a system’s security ...
... Threats, Vulnerabilities, Attacks How to address these problems? Control: an action, device, procedure, or technique that removes or reduces a vulnerability, and subsequently blocks threats and attacks This class focuses on the various controls and how they enhance a system’s security ...
module 2 network security unit 1
... employees, contractors and business partners. • Make sure employees know how to secure their home wireless networks. Malicious software that infects their devices at home can infect the company network via an open VPN connection, and • Before granting mobile devices full access to the network, check ...
... employees, contractors and business partners. • Make sure employees know how to secure their home wireless networks. Malicious software that infects their devices at home can infect the company network via an open VPN connection, and • Before granting mobile devices full access to the network, check ...
Types of Surveillance Technology Currently Used by Governments
... Internet user receives e-mail appearing to be legitimate and from reputable company, asking user to reply with updated credit card information Clicking on link sends user to fake Website, where user provides ...
... Internet user receives e-mail appearing to be legitimate and from reputable company, asking user to reply with updated credit card information Clicking on link sends user to fake Website, where user provides ...
slides
... – “Treat security as an important part of doing business. It is not less important than features and performance” (Bill Gates) – “The missing component in most security products is what Global 5000 buyers most want, the ability to manage business risk, innovation, and agility. Despite this, security ...
... – “Treat security as an important part of doing business. It is not less important than features and performance” (Bill Gates) – “The missing component in most security products is what Global 5000 buyers most want, the ability to manage business risk, innovation, and agility. Despite this, security ...
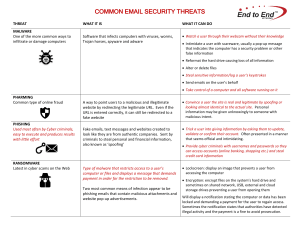
COMMON EMAIL SECURITY THREATS
... Watch a user through their webcam without their knowledge Intimidate a user with scareware, usually a pop-up message that indicates the computer has a security problem or other false information Reformat the hard drive causing loss of all information Alter or delete files Steal sensitive i ...
... Watch a user through their webcam without their knowledge Intimidate a user with scareware, usually a pop-up message that indicates the computer has a security problem or other false information Reformat the hard drive causing loss of all information Alter or delete files Steal sensitive i ...
Chap013
... What two issues does the article suggest about Credibility? Why would Enron (or any) executives engage in such activities? How can people be encouraged to follow acceptable ethical/moral business practices? ...
... What two issues does the article suggest about Credibility? Why would Enron (or any) executives engage in such activities? How can people be encouraged to follow acceptable ethical/moral business practices? ...
Applied Cybersecurity
... best protect their enterprises. In this course, experts from academia, the military, and industry share their knowledge to give participants the principles, the state of the practice, and strategies for the future. Sessions will address information security, ethical and legal practices, and mitigati ...
... best protect their enterprises. In this course, experts from academia, the military, and industry share their knowledge to give participants the principles, the state of the practice, and strategies for the future. Sessions will address information security, ethical and legal practices, and mitigati ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.