evesecures9
... Up to $250,000 and/or 10 years in jail, if knowing any misuse of patients’ information. ...
... Up to $250,000 and/or 10 years in jail, if knowing any misuse of patients’ information. ...
Principals of Information Security, Fourth Edition
... • Designed to enhance security of customer’s account data • Addresses six areas: – Build and maintain secure networks/systems – Protect cardholder data – Maintain vulnerability management program – Implement strong access control measures – Regularly monitor and test networks – Maintain information ...
... • Designed to enhance security of customer’s account data • Addresses six areas: – Build and maintain secure networks/systems – Protect cardholder data – Maintain vulnerability management program – Implement strong access control measures – Regularly monitor and test networks – Maintain information ...
Access Security Requirements
... responsibility to implement these controls. If you do not understand these requirements or need assistance, it is your responsibility to get an outside service provider to assist you. ID reserves the right to make changes to these Access Security Requirements without prior notification. The informat ...
... responsibility to implement these controls. If you do not understand these requirements or need assistance, it is your responsibility to get an outside service provider to assist you. ID reserves the right to make changes to these Access Security Requirements without prior notification. The informat ...
what is ec security?
... Assurance that stored data has not been modified without authorization; a message that was sent is the same message that was received availability Assurance that access to data, the Web site, or other EC data service is timely, available, reliable, and restricted to unauthorized users Copyright © 20 ...
... Assurance that stored data has not been modified without authorization; a message that was sent is the same message that was received availability Assurance that access to data, the Web site, or other EC data service is timely, available, reliable, and restricted to unauthorized users Copyright © 20 ...
Chapter 9
... The probability that a vulnerability will be known and used. – social engineering A type of nontechnical attack that uses some ruse to trick users into revealing information or performing an action that compromises a computer or network. Copyright © 2011 Pearson Education, Inc. Publishing as Prentic ...
... The probability that a vulnerability will be known and used. – social engineering A type of nontechnical attack that uses some ruse to trick users into revealing information or performing an action that compromises a computer or network. Copyright © 2011 Pearson Education, Inc. Publishing as Prentic ...
C06.InformationSecur.. - SIUE Computer Science
... A phishing scam combines both fraudulent e-mail and Web sites in order to trick a person into providing private information that can be used for identity theft. ...
... A phishing scam combines both fraudulent e-mail and Web sites in order to trick a person into providing private information that can be used for identity theft. ...
PowerPoint-10b - Community College of Rhode Island
... What is Information Security? • Information Security: Task of guarding digital information • Information must be protective -on the devices that store, manipulate, and transmit the information through products, people, and procedures. ...
... What is Information Security? • Information Security: Task of guarding digital information • Information must be protective -on the devices that store, manipulate, and transmit the information through products, people, and procedures. ...
Blueprint For Security Chapter 6
... detect when intruder creates, modifies, or deletes files Most HIDSs work on the principle of configuration or change management Advantage over NIDS: can usually be installed so that it can access information encrypted when traveling over network Principles of Information Security, 2nd edition ...
... detect when intruder creates, modifies, or deletes files Most HIDSs work on the principle of configuration or change management Advantage over NIDS: can usually be installed so that it can access information encrypted when traveling over network Principles of Information Security, 2nd edition ...
Internet and Network Attacks
... In case of system failure or corrupted files, restore files by copying to original location ...
... In case of system failure or corrupted files, restore files by copying to original location ...
Discovering Computers 2008
... In case of system failure or corrupted files, restore files by copying to original location ...
... In case of system failure or corrupted files, restore files by copying to original location ...
Lottery`s Log Management Business Objectives
... Transaction Information • All transactions should be written to a master transaction file that cannot be altered prior to being received by the Lottery • Requirement met by: – Transaction Master File – ICS system ...
... Transaction Information • All transactions should be written to a master transaction file that cannot be altered prior to being received by the Lottery • Requirement met by: – Transaction Master File – ICS system ...
Spear Phishing Attacks—Why They are Successful and How to Stop
... The assault began with spear phishing attacks that sent targeted users an email with a Microsoft Excel file attachment that leveraged a zero-day flaw in Adobe Flash. It is clear that not only was RSA the focus of the attack, but only four individuals within RSA were the recipients of the malicious e ...
... The assault began with spear phishing attacks that sent targeted users an email with a Microsoft Excel file attachment that leveraged a zero-day flaw in Adobe Flash. It is clear that not only was RSA the focus of the attack, but only four individuals within RSA were the recipients of the malicious e ...
Computer Security: Principles and Practice, 1/e
... multiple security events, that constitutes a security incident in which an intruder gains, or attempts to gain, access to a system (or system resource) without having authorization to do so. • Intrusion detection: a security service that monitors and analyzes system events for the purpose of finding ...
... multiple security events, that constitutes a security incident in which an intruder gains, or attempts to gain, access to a system (or system resource) without having authorization to do so. • Intrusion detection: a security service that monitors and analyzes system events for the purpose of finding ...
Presentation Title
... authorized recipients. This presentation may contain information that is confidential, proprietary or otherwise legally protected, and it may not be further copied, distributed or publicly displayed without the express written permission of Gartner, Inc. or its affiliates. © 2010 Gartner, Inc. and/o ...
... authorized recipients. This presentation may contain information that is confidential, proprietary or otherwise legally protected, and it may not be further copied, distributed or publicly displayed without the express written permission of Gartner, Inc. or its affiliates. © 2010 Gartner, Inc. and/o ...
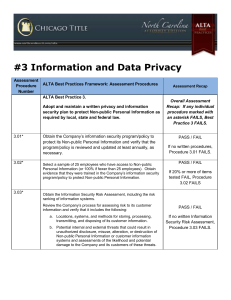
ALTA Assessment Procedures
... a. For the sample of employees tested in Assessment Procedure 3.02 above, test the user access provisioning process to determine if access is approved in accordance with policy prior to granting. o Obtain evidence (invoice/documentation in personnel files, etc.) that 5 year Background Checks were co ...
... a. For the sample of employees tested in Assessment Procedure 3.02 above, test the user access provisioning process to determine if access is approved in accordance with policy prior to granting. o Obtain evidence (invoice/documentation in personnel files, etc.) that 5 year Background Checks were co ...
ch02
... Mail bombing: also a DoS; attacker routes large quantities of e-mail to target Sniffers: program or device that monitors data traveling over network; can be used both for legitimate purposes and for stealing information from a network Social engineering: using social skills to convince people ...
... Mail bombing: also a DoS; attacker routes large quantities of e-mail to target Sniffers: program or device that monitors data traveling over network; can be used both for legitimate purposes and for stealing information from a network Social engineering: using social skills to convince people ...
OSI Security Architecture
... • The OSI security architecture focuses on 3 aspects: security attacks, mechanisms, and services. 1. Security attack: Any action that compromises the security of information owned by an organization. 2. Security service: A processing or communication service that enhances the security of the data pr ...
... • The OSI security architecture focuses on 3 aspects: security attacks, mechanisms, and services. 1. Security attack: Any action that compromises the security of information owned by an organization. 2. Security service: A processing or communication service that enhances the security of the data pr ...
Chapter 3 - Faculty Personal Homepage
... • What are some characteristics of common computer criminals, including their objectives, available resources, willingness to accept risk, and frequency of attack? • What are the key elements of a multilayer process for managing security vulnerabilities, based on the concept of reasonable assurance? ...
... • What are some characteristics of common computer criminals, including their objectives, available resources, willingness to accept risk, and frequency of attack? • What are the key elements of a multilayer process for managing security vulnerabilities, based on the concept of reasonable assurance? ...
PowerPoint Slides
... Employee monitoring is using computers to observe employee computer use Legal for employers to use ...
... Employee monitoring is using computers to observe employee computer use Legal for employers to use ...
Systeemanalyse in Ontwerpprojecten
... that people are only authorized to access (read, write and execute) certain data, information and programs • Big organizations often apply role-based access control where rights are linked to the different roles people do have: a hard problem to keep it simple (why?) • In governments and military or ...
... that people are only authorized to access (read, write and execute) certain data, information and programs • Big organizations often apply role-based access control where rights are linked to the different roles people do have: a hard problem to keep it simple (why?) • In governments and military or ...
Financial Reporting: The Institutional Setting
... Then, it is important to “Implement measures which will protect your assets in a cost-effective manner [and] review the process continuously and make improvements each time a weakness is found.” Every enterprise should have a security policy comprised of the specific rules applicable to those given ...
... Then, it is important to “Implement measures which will protect your assets in a cost-effective manner [and] review the process continuously and make improvements each time a weakness is found.” Every enterprise should have a security policy comprised of the specific rules applicable to those given ...
CSC 482/582: Computer Security
... Launch DOS attack Upgrade attack and control software Virus writers sell botnets to spammers for $0.10/compromised PC ...
... Launch DOS attack Upgrade attack and control software Virus writers sell botnets to spammers for $0.10/compromised PC ...
US SAFE WEB Act - Higher Education Compliance Alliance
... powers. The main benefit was adding language which allows the FTC to collaborate with foreign agencies. Although there may be examples of where the FTC has collaborated with foreign agencies, this report is limited to the FTC’s use of existing laws (FTC Act and US SAFE WEB Act) to begin exerting aut ...
... powers. The main benefit was adding language which allows the FTC to collaborate with foreign agencies. Although there may be examples of where the FTC has collaborated with foreign agencies, this report is limited to the FTC’s use of existing laws (FTC Act and US SAFE WEB Act) to begin exerting aut ...
Information security in a youth organisation?
... The information security policy is one solution • to ensure security on the three criteria (CID) • that is not limited to computers • for all information and resources ...
... The information security policy is one solution • to ensure security on the three criteria (CID) • that is not limited to computers • for all information and resources ...
chap12
... time you fill out with information form or click from public advertisement on sources Web Merchants Merchants sell sell the Marketing firms contents of their sell your databases to electronic profile national marketing Next to any company firms and Internet p.12.27 that requests it advertising firms ...
... time you fill out with information form or click from public advertisement on sources Web Merchants Merchants sell sell the Marketing firms contents of their sell your databases to electronic profile national marketing Next to any company firms and Internet p.12.27 that requests it advertising firms ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.