Introduction
... You can only patch holes you know about. Patches are often rushed and buggy. Patches often attack only the symptom. Patches are often not applied in time. ...
... You can only patch holes you know about. Patches are often rushed and buggy. Patches often attack only the symptom. Patches are often not applied in time. ...
1 Notification of the Office of the Securities and Exchange
... registration at least once a year. Upon any replacement of mobile devices, review the registration and deregister the old devices to ensure that the use of mobile devices complies with the information security policy. The intermediary may use other registration technology instead if considered appro ...
... registration at least once a year. Upon any replacement of mobile devices, review the registration and deregister the old devices to ensure that the use of mobile devices complies with the information security policy. The intermediary may use other registration technology instead if considered appro ...
Red Teaming: The Art of Ethical Hacking
... [JP1] 2. With respect to classified matter, the condition that prevents unauthorized persons from having access to official information that is safeguarded in the interests of national security. [After JP1] 3. Measures taken by a military unit, an activity or installation to protect itself against a ...
... [JP1] 2. With respect to classified matter, the condition that prevents unauthorized persons from having access to official information that is safeguarded in the interests of national security. [After JP1] 3. Measures taken by a military unit, an activity or installation to protect itself against a ...
SOW
... methods of notification will be provided by WMATA. No price adjustments will be made for any delays resulting from an installation closing. When area radio stations, TV stations or WMATA’s website report that a facility has "delayed reporting" until a particular time, the Contractor's personnel have ...
... methods of notification will be provided by WMATA. No price adjustments will be made for any delays resulting from an installation closing. When area radio stations, TV stations or WMATA’s website report that a facility has "delayed reporting" until a particular time, the Contractor's personnel have ...
Security+ Guide to Network Security Fundamentals, Third Edition
... type of computer, operating system, software, and network connection a computer uses – An attacker who knows that information can more easily determine the weaknesses of the system to attack it ...
... type of computer, operating system, software, and network connection a computer uses – An attacker who knows that information can more easily determine the weaknesses of the system to attack it ...
PPT_ch01 - Mercer University Computer Science Department
... type of computer, operating system, software, and network connection a computer uses – An attacker who knows that information can more easily determine the weaknesses of the system to attack it ...
... type of computer, operating system, software, and network connection a computer uses – An attacker who knows that information can more easily determine the weaknesses of the system to attack it ...
8_19Counter Hack 6 scanning
... Be careful with DoS(Denial-to-Server) and Password Guessing tests! Be aware of limitations of vulnerability scanning tools. ...
... Be careful with DoS(Denial-to-Server) and Password Guessing tests! Be aware of limitations of vulnerability scanning tools. ...
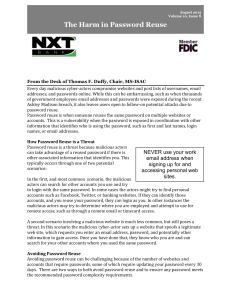
Password Security
... Password managers are applications that can be stored on a computer, smartphone, or in the cloud, and will securely track passwords and where they are used. Most password managers can also generate complex random passwords for each account if you choose to do so. As long as the password to access th ...
... Password managers are applications that can be stored on a computer, smartphone, or in the cloud, and will securely track passwords and where they are used. Most password managers can also generate complex random passwords for each account if you choose to do so. As long as the password to access th ...
Introduction to Computer Security
... Some resurgence with wireless networks Has always been a problem with wireless transmission! Electromagnetic emanations (TEMPEST security) ...
... Some resurgence with wireless networks Has always been a problem with wireless transmission! Electromagnetic emanations (TEMPEST security) ...
chap1-slide - GEOCITIES.ws
... • Computer security was not an issue at the beginning • But with the set off the “information age”, organisation dependent on computers for their functioning • Information became a strategic asset, therefore should be properly protected • Networking as well was booming which result in central mainfr ...
... • Computer security was not an issue at the beginning • But with the set off the “information age”, organisation dependent on computers for their functioning • Information became a strategic asset, therefore should be properly protected • Networking as well was booming which result in central mainfr ...
Slides - School of Information Sciences
... We can’t detect it: Now what? Detection Signature-based antivirus Look for known patterns in malicious code Always a battle with the attacker Great business model! ...
... We can’t detect it: Now what? Detection Signature-based antivirus Look for known patterns in malicious code Always a battle with the attacker Great business model! ...
Good, Fast, and Cost Effective Priceline Tries to Do All Three
... Loosely Coupled – guaranteed messages are a problem – this is not MQ Series —If timed-out, did you get message, was the data received, should you retry? —Credit card Authorizations - need to build duplication detection at the target site to prevent duplicate authorizations —Reliable web services wil ...
... Loosely Coupled – guaranteed messages are a problem – this is not MQ Series —If timed-out, did you get message, was the data received, should you retry? —Credit card Authorizations - need to build duplication detection at the target site to prevent duplicate authorizations —Reliable web services wil ...
An Introduction to NIST Special Publication 800
... federal government in all of its non-defense-related contracts. In addition, where isolating CUI from the campus-computing infrastructure is not possible, an institution must then compare the NIST 800-171 controls with its own already established information security controls. In some cases, it may ...
... federal government in all of its non-defense-related contracts. In addition, where isolating CUI from the campus-computing infrastructure is not possible, an institution must then compare the NIST 800-171 controls with its own already established information security controls. In some cases, it may ...
Types of Attacks - Digital Locker and Personal Web Space
... • Describe various types of computer and network attacks, including denial-of-service, spoofing, hijacking, and password guessing. • Identify the different types of malicious software that exist, including viruses, worms, Trojan horses, logic bombs, time bombs, and rootkits. • Explain how social eng ...
... • Describe various types of computer and network attacks, including denial-of-service, spoofing, hijacking, and password guessing. • Identify the different types of malicious software that exist, including viruses, worms, Trojan horses, logic bombs, time bombs, and rootkits. • Explain how social eng ...
- Learn Group
... Information has accuracy when it is free from mistakes or errors and it has the value that the end user expects. If information has been intentionally or unintentionally modified, it is no longer accurate. Consider, for example, a checking account. You assume that the information contained in your c ...
... Information has accuracy when it is free from mistakes or errors and it has the value that the end user expects. If information has been intentionally or unintentionally modified, it is no longer accurate. Consider, for example, a checking account. You assume that the information contained in your c ...
12_Auth_nemo
... • May only need to know form of response; attacker can tell if guess correct by looking to see if deciphered object is of right form • Example: Kerberos Version 4 used DES, but keys had 20 bits of randomness; Purdue attackers guessed keys quickly because deciphered tickets had a fixed set of bits in ...
... • May only need to know form of response; attacker can tell if guess correct by looking to see if deciphered object is of right form • Example: Kerberos Version 4 used DES, but keys had 20 bits of randomness; Purdue attackers guessed keys quickly because deciphered tickets had a fixed set of bits in ...
Security and Availability of Client Data
... All servers, routers, switches, load balancers, and other critical network equipment are monitored 24 hours a day. The software responsible for monitoring this system performs around one million health checks per hour probing for data integrity and service interruptions. Temperature probes and power ...
... All servers, routers, switches, load balancers, and other critical network equipment are monitored 24 hours a day. The software responsible for monitoring this system performs around one million health checks per hour probing for data integrity and service interruptions. Temperature probes and power ...
Chapter 1
... Illegal taking of another’s property—physical, electronic, or intellectual Value of information suffers when it is copied and taken away without the owner’s knowledge Physical theft can be controlled—wide variety of measures used from locked doors to guards or alarm systems Electronic theft ...
... Illegal taking of another’s property—physical, electronic, or intellectual Value of information suffers when it is copied and taken away without the owner’s knowledge Physical theft can be controlled—wide variety of measures used from locked doors to guards or alarm systems Electronic theft ...
Security Policies, Standards, and Planning
... There are a number of ways to create and manage ISSPs within an organization. Three of the most common are: 1. Create a number of independent ISSP documents, each tailored to a specific issue 2. Create a single comprehensive ISSP document that covers all issues 3. Create a modular ISSP document tha ...
... There are a number of ways to create and manage ISSPs within an organization. Three of the most common are: 1. Create a number of independent ISSP documents, each tailored to a specific issue 2. Create a single comprehensive ISSP document that covers all issues 3. Create a modular ISSP document tha ...
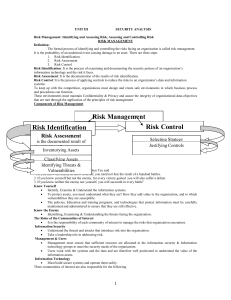
IT2042-UNIT3-Notes
... -The inventory listing is usually available in a data base. - Once stored, the inventory listing must be kept current, often by means of a tool that periodically refreshes the data. Information Asset Classification- In addition to the categories, it is advisable to add another dimension to represent ...
... -The inventory listing is usually available in a data base. - Once stored, the inventory listing must be kept current, often by means of a tool that periodically refreshes the data. Information Asset Classification- In addition to the categories, it is advisable to add another dimension to represent ...
Security+ Guide to Network Security Fundamentals
... attacking other hosts inside or outside the firewall ...
... attacking other hosts inside or outside the firewall ...
PCI Self-Assessment Questionnaire
... verify card-not-present transactions. On a MasterCard payment card this is called CVC2. On a Visa payment card this is called CVV2. ...
... verify card-not-present transactions. On a MasterCard payment card this is called CVC2. On a Visa payment card this is called CVV2. ...
Computer Security And The Law: What You Can Do To Protect
... By documenting the entry points, an organization learns where the potential is for an intrusion. In addition, if these entry points can be protected by other means such as a firewall or intrusion detection system, then the organization is beginning the process of protecting its assets. The services ...
... By documenting the entry points, an organization learns where the potential is for an intrusion. In addition, if these entry points can be protected by other means such as a firewall or intrusion detection system, then the organization is beginning the process of protecting its assets. The services ...
Secure_Email_and_Web_Browsing_SEC
... ► Computer used for criminal purpose: ► Loss of confidential work ► Money extortion (private data encryption) ► Join BotNet to attack other systems on the Internet (DoS) ...
... ► Computer used for criminal purpose: ► Loss of confidential work ► Money extortion (private data encryption) ► Join BotNet to attack other systems on the Internet (DoS) ...
Social engineering (security)

Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional ""con"" in that it is often one of many steps in a more complex fraud scheme.The term ""social engineering"" as an act of psychological manipulation is also associated with the social sciences, but its usage has caught on among computer and information security professionals.