Chorusamoeba
... to directory. Each file entry in the director has three protection domain User presents a directory server with a ASCII name , capability and the server then checks the capability corresponding to the name User can any one of the directory servers, if one is down it can use ...
... to directory. Each file entry in the director has three protection domain User presents a directory server with a ASCII name , capability and the server then checks the capability corresponding to the name User can any one of the directory servers, if one is down it can use ...
Document
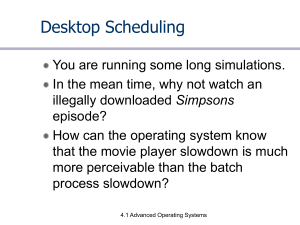
... is not so much technology. Instead, it is the set of security policies implemented and enforced. Most systems could run as true multiuser systems but it is a fact that a system used by only one user will be very akward to use if it is run like a full multi-user system with separate identities and ro ...
... is not so much technology. Instead, it is the set of security policies implemented and enforced. Most systems could run as true multiuser systems but it is a fact that a system used by only one user will be very akward to use if it is run like a full multi-user system with separate identities and ro ...
operating system
... After studying this chapter, the student should be able to: Understand the role of the operating system. Understand the process of bootstrapping to load the operating system into memory. List the components of an operating system. Discuss the role of the memory manager. Discuss the role of ...
... After studying this chapter, the student should be able to: Understand the role of the operating system. Understand the process of bootstrapping to load the operating system into memory. List the components of an operating system. Discuss the role of the memory manager. Discuss the role of ...
Introduction
... Situation after CPU 1 references page 10 Situation if page 10 is read only and replication is used ...
... Situation after CPU 1 references page 10 Situation if page 10 is read only and replication is used ...
CMPU1022 Operating Systems 1
... operating systems have evolved over years and the impact this has had on modern operating systems. ...
... operating systems have evolved over years and the impact this has had on modern operating systems. ...
Introduction
... Distributed Shared Memory Systems • The goal is to provide a virtual shared memory machine, running on a multicomputer, for which applications can be written using the shared memory model even though this is not present. • A pagebased distributed shared memory (DSM) is to use the virtual memory cap ...
... Distributed Shared Memory Systems • The goal is to provide a virtual shared memory machine, running on a multicomputer, for which applications can be written using the shared memory model even though this is not present. • A pagebased distributed shared memory (DSM) is to use the virtual memory cap ...
cs459 - Operating Systems: Introduction
... 2. A firmware bootstrap loader executes to: a. Execute diagnostics b. Loads a boot block from a fixed disk location 3. The boot block then loads the entire operating system into memory 4. The Operating system initializes itself and begins to execute ...
... 2. A firmware bootstrap loader executes to: a. Execute diagnostics b. Loads a boot block from a fixed disk location 3. The boot block then loads the entire operating system into memory 4. The Operating system initializes itself and begins to execute ...
Chorusamoeba
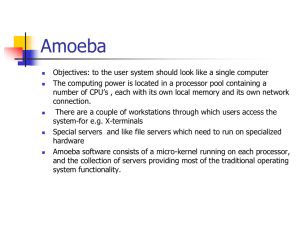
... When a process is executing, all of its segments are in memory. No swapping or paging. Amoeba can only run programs that fit in physical memory. Advantage: simplicity and high performance. ...
... When a process is executing, all of its segments are in memory. No swapping or paging. Amoeba can only run programs that fit in physical memory. Advantage: simplicity and high performance. ...
VMS-Spr-2001-sect-1-group
... between banks take place on systems running VMS • 90% of CPU manufacturers use VMS to run their assembly lines • A large portion of stock transfers and many cellular phone billing services run on VMS systems • VMS is the top rated healthcare operating system for real-time, mission critical computing ...
... between banks take place on systems running VMS • 90% of CPU manufacturers use VMS to run their assembly lines • A large portion of stock transfers and many cellular phone billing services run on VMS systems • VMS is the top rated healthcare operating system for real-time, mission critical computing ...
The Amoeba Distributed Operating System
... 3. A directory server maps ascii strings onto capabilities. 4. Directories contain (string, capability) pairs. 5. Directories are not immutable. 6. Operations for managing replicated files in a consistent way are provided. ...
... 3. A directory server maps ascii strings onto capabilities. 4. Directories contain (string, capability) pairs. 5. Directories are not immutable. 6. Operations for managing replicated files in a consistent way are provided. ...
Operating Systems Concepts
... Computer systems : organizations and structure. Operating systems: history, structure and operations. 2. Computer-system structure Computer-system operation. I/O structure Storage structure and hierarchy Network structure 3. Operating system structures System components and structures ...
... Computer systems : organizations and structure. Operating systems: history, structure and operations. 2. Computer-system structure Computer-system operation. I/O structure Storage structure and hierarchy Network structure 3. Operating system structures System components and structures ...
UNIX Operating System
... Utilized by Linux and UNIX OS to create an artificial root directory. Creating a temporary root directory prevents a program from accessing or modifying files outside the directory hierarchy starting at its root. Chroot affects only the current process and its child processes. The files need to be p ...
... Utilized by Linux and UNIX OS to create an artificial root directory. Creating a temporary root directory prevents a program from accessing or modifying files outside the directory hierarchy starting at its root. Chroot affects only the current process and its child processes. The files need to be p ...
Final Year Project Electronic & Computer Engineering
... Installed Linux on computer Installed Real-Time Application Interface Got the first 3 out of first 4 experiments loading and one of the more advanced experiments also Created a Live CD of Ubuntu that will boot and fully function but not running of my kernel with built in RTAI ...
... Installed Linux on computer Installed Real-Time Application Interface Got the first 3 out of first 4 experiments loading and one of the more advanced experiments also Created a Live CD of Ubuntu that will boot and fully function but not running of my kernel with built in RTAI ...
ppt - Purdue University :: Computer Science
... programs running in the computer such as math library, string library, window library, c library etc. It has to do all of the above in a secure and reliable manner. ...
... programs running in the computer such as math library, string library, window library, c library etc. It has to do all of the above in a secure and reliable manner. ...
Ch. 14 : UNIX Operating System with Linux
... Linux can run +1 program at a time using one or several processors. Operate on Intel’s x86 processors & other platforms including Alpha, Sparc, certain 6800 platforms, certain MIPS machines, and Power PCs. Allows several users to work on the same machine at same time. Linux supports pipes, IPC, sock ...
... Linux can run +1 program at a time using one or several processors. Operate on Intel’s x86 processors & other platforms including Alpha, Sparc, certain 6800 platforms, certain MIPS machines, and Power PCs. Allows several users to work on the same machine at same time. Linux supports pipes, IPC, sock ...
DS-Chap01
... Distributed Object-based Systems Distributed File Systems Distributed Document-based systems Distributed Coordination-based Systems ...
... Distributed Object-based Systems Distributed File Systems Distributed Document-based systems Distributed Coordination-based Systems ...
Introduction
... Mainframe operating systems Server operating systems Multiprocessor operating systems Personal computer operating systems Real-time operating systems Embedded operating systems Smart card operating systems ...
... Mainframe operating systems Server operating systems Multiprocessor operating systems Personal computer operating systems Real-time operating systems Embedded operating systems Smart card operating systems ...
Introduction
... In an open middleware-based distributed system, the protocols used by each middleware layer should be the same, as well as the interfaces they offer to applications. ...
... In an open middleware-based distributed system, the protocols used by each middleware layer should be the same, as well as the interfaces they offer to applications. ...
The Active Streams Approach to adaptive distributed systems
... The Linux scheduler partitions time into epochs. In each epoch, every process has a time slice of how long it may run. When there are no ready processes with a time slice left, a new epoch is started. The order within the epoch is set according to the dynamic priority. – The dynamic priority is a nu ...
... The Linux scheduler partitions time into epochs. In each epoch, every process has a time slice of how long it may run. When there are no ready processes with a time slice left, a new epoch is started. The order within the epoch is set according to the dynamic priority. – The dynamic priority is a nu ...
Distributed Systems [Jan 14
... protocols used by each middleware layer should be the same, as well as the interfaces they offer to applications ...
... protocols used by each middleware layer should be the same, as well as the interfaces they offer to applications ...
Rearchitecting System Software for the Cloud - Muli Ben
... application specialization and driver reliability, exposing I/O devices directly to applications improves efficiency, since there is less non-useful work to do, and it provides applications with the opportunity to adapt to the underlying resource availability. The nom operating system has no kernel- ...
... application specialization and driver reliability, exposing I/O devices directly to applications improves efficiency, since there is less non-useful work to do, and it provides applications with the opportunity to adapt to the underlying resource availability. The nom operating system has no kernel- ...
System - Regis University: Academic Web Server for Faculty
... which is a given computer architecture’s native unit of data. A word is made up of one or more bytes. For example, a computer that has 64-bit registers and 64bit memory addressing typically has 64-bit (8-byte) words. A computer executes many operations in its native word size rather than a byte at a ...
... which is a given computer architecture’s native unit of data. A word is made up of one or more bytes. For example, a computer that has 64-bit registers and 64bit memory addressing typically has 64-bit (8-byte) words. A computer executes many operations in its native word size rather than a byte at a ...
Unit I Operating Systems in Distributed Environments
... has the basic routines of an OS. • Some OS use the microkernel concept, this have the function to coordinate to the other parts of an OS such as : I/O Devices, Process, Memory and File Systems. • The structure of and OS could be different but in most of the time are very similar because some OS use ...
... has the basic routines of an OS. • Some OS use the microkernel concept, this have the function to coordinate to the other parts of an OS such as : I/O Devices, Process, Memory and File Systems. • The structure of and OS could be different but in most of the time are very similar because some OS use ...
Operating Systems
... user no longer has direct access to processor job is submitted to computer operator who batches them together and places them on an input device program branches back to the monitor when finished ...
... user no longer has direct access to processor job is submitted to computer operator who batches them together and places them on an input device program branches back to the monitor when finished ...
The Java Virtual Shell and Kernel
... Abstract: Our aim is to develop a shell and kernel in Java that will be able to run on most of the available operating systems that supports Java Runtime Environment. The shell and kernel would be designed in such a way that the beneath platform (operating system and hardware) should not impact on t ...
... Abstract: Our aim is to develop a shell and kernel in Java that will be able to run on most of the available operating systems that supports Java Runtime Environment. The shell and kernel would be designed in such a way that the beneath platform (operating system and hardware) should not impact on t ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.