CBA Software - Hoxie Public Schools
... other software to communicate with each other. There are many brands and versions of operating ...
... other software to communicate with each other. There are many brands and versions of operating ...
xwindows - WordPress.com
... X Windows The X Windows System, also referred to as ‘X’ or “X11”, is the standard graphical engine for Unix and Linux. The X Window System is the basis for graphical user interfaces. Linux also often confusingly is used to refer to systems like Debian, Ubuntu, Redhat, CentOs, Suse, and many more. T ...
... X Windows The X Windows System, also referred to as ‘X’ or “X11”, is the standard graphical engine for Unix and Linux. The X Window System is the basis for graphical user interfaces. Linux also often confusingly is used to refer to systems like Debian, Ubuntu, Redhat, CentOs, Suse, and many more. T ...
Design of MS-DOS
... - Basis of many other Disk(based) Operating Systems. • The first personal computer DOS, called Personal Computer Disk Operating System, was developed for IBM by Microsoft Corporation. • MS retained the rights to market a Microsoft version, called MS-DOS. PC-DOS and MS-DOS are almost identical and mo ...
... - Basis of many other Disk(based) Operating Systems. • The first personal computer DOS, called Personal Computer Disk Operating System, was developed for IBM by Microsoft Corporation. • MS retained the rights to market a Microsoft version, called MS-DOS. PC-DOS and MS-DOS are almost identical and mo ...
Module Operating Systems (Server)
... 8. Write, compile and run multithreaded C/C++ programs on a Linux platform using the ThreadMentor library 9. Configure and compile the Linux kernel ...
... 8. Write, compile and run multithreaded C/C++ programs on a Linux platform using the ThreadMentor library 9. Configure and compile the Linux kernel ...
Introduction - Stanford Secure Computer Systems Group
... Different system contexts • A system can typically be in one of several contexts • User-level – running an application • Kernel process context - Running kernel code on behalf of a particular process - E.g., performing system call - Also exception (mem. fault, numeric exception, etc.) - Or executin ...
... Different system contexts • A system can typically be in one of several contexts • User-level – running an application • Kernel process context - Running kernel code on behalf of a particular process - E.g., performing system call - Also exception (mem. fault, numeric exception, etc.) - Or executin ...
Monolithic, Mikrokernel and Exokernel
... Microkernel systems Pure microkernel designs Hybrid microkernel designs ...
... Microkernel systems Pure microkernel designs Hybrid microkernel designs ...
UNIX-like Operating Systems
... were very diverse — each OS specific to particular hardware, used radically different models of commands and procedures, Typically, each time the manufacturer brought out a new machine, there would be a new OS. ...
... were very diverse — each OS specific to particular hardware, used radically different models of commands and procedures, Typically, each time the manufacturer brought out a new machine, there would be a new OS. ...
Assignment 3
... system fetches the page containing the address and restarts the faulting instruction, which now completes success fully. ...
... system fetches the page containing the address and restarts the faulting instruction, which now completes success fully. ...
Operating Systems Review
... same time. a) threading b) task switching c) multitasking 6. Software programs that allow the operating system and applications to use specific hardware (like a printer), are called______ a) b) c) d) ...
... same time. a) threading b) task switching c) multitasking 6. Software programs that allow the operating system and applications to use specific hardware (like a printer), are called______ a) b) c) d) ...
Unit I Introduction
... has the basic routines of an OS. • Some OS use the microkernel concept, this have the function to coordinate to the other parts of an OS such as : I/O Devices, Process, Memory and File Systems. • The structure of and OS could be different but in most of the time are very similar because some OS use ...
... has the basic routines of an OS. • Some OS use the microkernel concept, this have the function to coordinate to the other parts of an OS such as : I/O Devices, Process, Memory and File Systems. • The structure of and OS could be different but in most of the time are very similar because some OS use ...
03-os-design
... mode to the supervisor mode. It is used to implement system calls. An alternative to trap is using messages to get service from the operating system. ...
... mode to the supervisor mode. It is used to implement system calls. An alternative to trap is using messages to get service from the operating system. ...
Operating System Overview
... • Kernel (a.k.a. supervisory or privileged) level • All instructions are available • Total control possible so OS must say “Mine, all mine” (Daffy Duck) ...
... • Kernel (a.k.a. supervisory or privileged) level • All instructions are available • Total control possible so OS must say “Mine, all mine” (Daffy Duck) ...
CTE214 Operating Systems Syllabus
... Lab applications are done at the computer lab using desktop computers that are connected to our department’s server system and thus access to the University network and Internet. This syllabus (hence, the course) is designed for a typical vocational school student where the goal is to introduce the ...
... Lab applications are done at the computer lab using desktop computers that are connected to our department’s server system and thus access to the University network and Internet. This syllabus (hence, the course) is designed for a typical vocational school student where the goal is to introduce the ...
Chapter 6 Introduction to Network Operating Systems
... essential to add to a Linux system regardless of whether it is configured as a workstation or a server. • Text editors are essential for performing any type of maintenance tasks that a user or an administrator may need to do. • Some examples of text editors available in Linux are vi, jed, pico, or E ...
... essential to add to a Linux system regardless of whether it is configured as a workstation or a server. • Text editors are essential for performing any type of maintenance tasks that a user or an administrator may need to do. • Some examples of text editors available in Linux are vi, jed, pico, or E ...
Chapter 6 Introduction to Network Operating Systems
... essential to add to a Linux system regardless of whether it is configured as a workstation or a server. • Text editors are essential for performing any type of maintenance tasks that a user or an administrator may need to do. • Some examples of text editors available in Linux are vi, jed, pico, or E ...
... essential to add to a Linux system regardless of whether it is configured as a workstation or a server. • Text editors are essential for performing any type of maintenance tasks that a user or an administrator may need to do. • Some examples of text editors available in Linux are vi, jed, pico, or E ...
Chapter 6 Introduction to Network Operating Systems
... essential to add to a Linux system regardless of whether it is configured as a workstation or a server. • Text editors are essential for performing any type of maintenance tasks that a user or an administrator may need to do. • Some examples of text editors available in Linux are vi, jed, pico, or E ...
... essential to add to a Linux system regardless of whether it is configured as a workstation or a server. • Text editors are essential for performing any type of maintenance tasks that a user or an administrator may need to do. • Some examples of text editors available in Linux are vi, jed, pico, or E ...
Interfacing with the Operating System
... your hard disk, but to any sequence of bytes that can be written to an i/o device. – So we can write a file to a printer (or any other output device, such as an audio device). – We can read from our floppy drive, hard drive, CD player etc. ...
... your hard disk, but to any sequence of bytes that can be written to an i/o device. – So we can write a file to a printer (or any other output device, such as an audio device). – We can read from our floppy drive, hard drive, CD player etc. ...
Operating system - Department of Computer Science
... processor. This allows the operating system to perform certain functions on a regular basis, like scheduling z Hardware Failure Interrupts: Generated by a failure (e.g. power failure or memory parity error). z Traps (Software Interrupts): Generated by some condition that occurs as a result of an ins ...
... processor. This allows the operating system to perform certain functions on a regular basis, like scheduling z Hardware Failure Interrupts: Generated by a failure (e.g. power failure or memory parity error). z Traps (Software Interrupts): Generated by some condition that occurs as a result of an ins ...
Introduction to OS - faculty.cs.tamu.edu
... Time Sharing (mid 1960s on)! •! OS interleaves execution of multiple user programs with time quantum! –! CTSS (1961): time quantum 0.2 sec! •! User returns to own the machine! •! New aspects and issues:! –! On-line file systems! –! resource protection! –! virtual memory! –! sophisticated process sch ...
... Time Sharing (mid 1960s on)! •! OS interleaves execution of multiple user programs with time quantum! –! CTSS (1961): time quantum 0.2 sec! •! User returns to own the machine! •! New aspects and issues:! –! On-line file systems! –! resource protection! –! virtual memory! –! sophisticated process sch ...
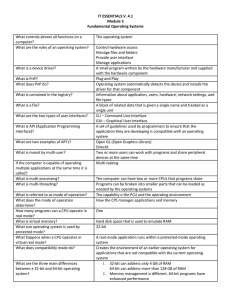
IT ESSENTIALS V. 4.1 Module 5 Fundamental Operating Systems
... How the CPS manages applications and memory One Hard disk space that is used to emulate RAM 32-bit A real-mode application runs within a protected-mode operating system Creates the environment of an earlier operating system for applications that are not compatible with the current operating system 1 ...
... How the CPS manages applications and memory One Hard disk space that is used to emulate RAM 32-bit A real-mode application runs within a protected-mode operating system Creates the environment of an earlier operating system for applications that are not compatible with the current operating system 1 ...
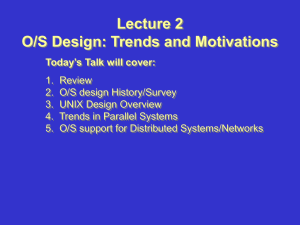
Lecture 2
... 3. If possible, use or modify existing tools rather write a new one. 4. Create the design first, then start with a small prototype and add features incrementally. ...
... 3. If possible, use or modify existing tools rather write a new one. 4. Create the design first, then start with a small prototype and add features incrementally. ...
operating systems structures
... Operating Systems I (CSC 406) I/O Operations: A running program may require I/O, which may involve a file or an I/O device. For efficiency and protection user usually cannot control I/O devices directly. The OS provides a means to do I/O. ƒ File System Manipulation: Programs need to read, write fil ...
... Operating Systems I (CSC 406) I/O Operations: A running program may require I/O, which may involve a file or an I/O device. For efficiency and protection user usually cannot control I/O devices directly. The OS provides a means to do I/O. ƒ File System Manipulation: Programs need to read, write fil ...
Operating System for Parallel Computing
... The main goal of our research is the development of a distributed operating system providing processes with location-independent execution and communication environment and supporting the migration of processes between network nodes. The process migration facility will allow to significantly improve ...
... The main goal of our research is the development of a distributed operating system providing processes with location-independent execution and communication environment and supporting the migration of processes between network nodes. The process migration facility will allow to significantly improve ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.