Unix – Linux
... environment that is separated from other users sharing the computer’s resources. – Access is through a verification process known as logging-in: Enter a user-id and password. – The OS creates an environment known as the “shell” for the user after the login is complete. ...
... environment that is separated from other users sharing the computer’s resources. – Access is through a verification process known as logging-in: Enter a user-id and password. – The OS creates an environment known as the “shell” for the user after the login is complete. ...
Chapter 2
... icon - a picture that represents a program, hardware device, or data object (file) ...
... icon - a picture that represents a program, hardware device, or data object (file) ...
Operating Systems (OS)
... Example of open operating system: UNIX System V Example of open specifications: POSIX (Portable Operating System Interface) ...
... Example of open operating system: UNIX System V Example of open specifications: POSIX (Portable Operating System Interface) ...
Traditional UNIX kernels
... • Intended for small servers, workstations, desktops, and handhelds • Cost: Free ...
... • Intended for small servers, workstations, desktops, and handhelds • Cost: Free ...
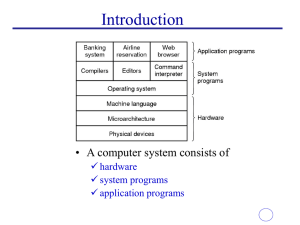
application programs
... some of the details of the underlying hardware for such I/O. All the user sees is that the I/O has been performed, without those details. Communications There are instances where processes need to communicate with each other to exchange information. It may be between processes running on the same ...
... some of the details of the underlying hardware for such I/O. All the user sees is that the I/O has been performed, without those details. Communications There are instances where processes need to communicate with each other to exchange information. It may be between processes running on the same ...
An Introduction to Operating Systems
... OS provides an environment where the user can conveniently run programs. The user does not have to worry about memory allocation or CPU scheduling. ¾ I/O Operations Each program requires input and produces output. The OS hides some of the details of the underlying hardware for such I/O. All the user ...
... OS provides an environment where the user can conveniently run programs. The user does not have to worry about memory allocation or CPU scheduling. ¾ I/O Operations Each program requires input and produces output. The OS hides some of the details of the underlying hardware for such I/O. All the user ...
Chapter 3: System Software
... Copy files Move files System/file backup Rename files Erase files ...
... Copy files Move files System/file backup Rename files Erase files ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.