Chapter 04 - Regis University: Academic Web Server for Faculty
... Each piece can have its own access rights. A segment has a name and an offset value. ...
... Each piece can have its own access rights. A segment has a name and an offset value. ...
Ch. 3 - Installation
... computer is recognized on the Internet In Linux, the hostname can exist on more than computer, it only uses IP addresses for communication ...
... computer is recognized on the Internet In Linux, the hostname can exist on more than computer, it only uses IP addresses for communication ...
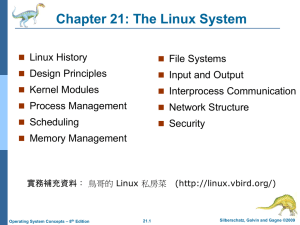
Components of a Linux System
... Kernel code executes in kernel mode with full access to all the physical resources of the computer Implemented as a single, monolithic binary. All kernel code and data structures are kept in the same single address space, so that no context switches are necessary for system calls or hardware interru ...
... Kernel code executes in kernel mode with full access to all the physical resources of the computer Implemented as a single, monolithic binary. All kernel code and data structures are kept in the same single address space, so that no context switches are necessary for system calls or hardware interru ...
7 Operating Systems
... provides supports for other programs. For example, it is responsible for loading other programs into memory for execution. However, the operating system itself is a program that needs to be loaded into the memory and be run. How is this dilemma solved? The solution is a two-stage process. A very sma ...
... provides supports for other programs. For example, it is responsible for loading other programs into memory for execution. However, the operating system itself is a program that needs to be loaded into the memory and be run. How is this dilemma solved? The solution is a two-stage process. A very sma ...
1 - OoCities
... 17. [L2] What is the purpose of I/O Channels in a sophisticated I/O subsystem? a. Match speeds of a fast device with multiple slower devices: Buffer and retransmit. b. Increase system reliability through cross connection. An I/O subsystem handles the transmission of data to and from I/O devices once ...
... 17. [L2] What is the purpose of I/O Channels in a sophisticated I/O subsystem? a. Match speeds of a fast device with multiple slower devices: Buffer and retransmit. b. Increase system reliability through cross connection. An I/O subsystem handles the transmission of data to and from I/O devices once ...
Chapter 1
... systems hides the user the details of underlying hardware for the I/O. All the user sees is that the I/O has been performed without any details. So the operating system by providing I/O makes it convenient for the users to run programs. For reasons of efficiency and protection, users cannot control ...
... systems hides the user the details of underlying hardware for the I/O. All the user sees is that the I/O has been performed without any details. So the operating system by providing I/O makes it convenient for the users to run programs. For reasons of efficiency and protection, users cannot control ...
File
... I/O operations – since user programs cannot execute I/O operations directly, the operating system must provide some means to perform I/O. File-system manipulation – program capability to read, write, create, and delete files. Communications – exchange of information between processes executing eithe ...
... I/O operations – since user programs cannot execute I/O operations directly, the operating system must provide some means to perform I/O. File-system manipulation – program capability to read, write, create, and delete files. Communications – exchange of information between processes executing eithe ...
Chapter 21: The Linux System Objectives 21.1 History (不考) Linux 2.0
... Linus Torvalds, with the major design goal of UNIX compatibility ...
... Linus Torvalds, with the major design goal of UNIX compatibility ...
System software - Information Technology
... – When a program wants to display some output, the user program executes some system call that displays the data ...
... – When a program wants to display some output, the user program executes some system call that displays the data ...
2.01
... Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS Simplest: pass the parameters in registers In some cases, may be more parameters than registers Parameters stored in a block, or table, in memory, and address of block p ...
... Exact type and amount of information vary according to OS and call Three general methods used to pass parameters to the OS Simplest: pass the parameters in registers In some cases, may be more parameters than registers Parameters stored in a block, or table, in memory, and address of block p ...
Slides - CSE
... – Any user process can modify the protection state at its discretion. – User processes can access and modify kernels through special file systems (e.g., /proc, /kmem.) – Any root user process can modify any aspect of the protection system ...
... – Any user process can modify the protection state at its discretion. – User processes can access and modify kernels through special file systems (e.g., /proc, /kmem.) – Any root user process can modify any aspect of the protection system ...
operating system
... provides supports for other programs. For example, it is responsible for loading other programs into memory for execution. However, the operating system itself is a program that needs to be loaded into the memory and be run. How is this dilemma solved? The solution is a two-stage process. A very sma ...
... provides supports for other programs. For example, it is responsible for loading other programs into memory for execution. However, the operating system itself is a program that needs to be loaded into the memory and be run. How is this dilemma solved? The solution is a two-stage process. A very sma ...
Document
... provides supports for other programs. For example, it is responsible for loading other programs into memory for execution. However, the operating system itself is a program that needs to be loaded into the memory and be run. How is this dilemma solved? The solution is a two-stage process. A very sma ...
... provides supports for other programs. For example, it is responsible for loading other programs into memory for execution. However, the operating system itself is a program that needs to be loaded into the memory and be run. How is this dilemma solved? The solution is a two-stage process. A very sma ...
Chapter 6 Introduction to Network Operating Systems
... runs on many different computers and was first released in 1991. • Linux is portable, which means versions can be found running on name brand or clone PCs. • Linux offers many features adopted from other versions of UNIX. ...
... runs on many different computers and was first released in 1991. • Linux is portable, which means versions can be found running on name brand or clone PCs. • Linux offers many features adopted from other versions of UNIX. ...
DOS - InfoShare.tk
... The DOS kernel initializes its tables and sets up various work areas. It sets up the interrupt vector table. It then loads and executes the device drivers. These driver function determine device status, perform necessary hardware initialization and set up vectors for any external hardware interrupts ...
... The DOS kernel initializes its tables and sets up various work areas. It sets up the interrupt vector table. It then loads and executes the device drivers. These driver function determine device status, perform necessary hardware initialization and set up vectors for any external hardware interrupts ...
The SAS System for the UNIX Environment
... began working on version 32V. Version 32V was an early implementation for the VAX':" When memory paging was added, it was renamed 3BSD. Earlier work at Berkeley produced extensions such as the vi text editor, the C shell, and the relational data base INGRESS. These efforts were conducted by Berkeley ...
... began working on version 32V. Version 32V was an early implementation for the VAX':" When memory paging was added, it was renamed 3BSD. Earlier work at Berkeley produced extensions such as the vi text editor, the C shell, and the relational data base INGRESS. These efforts were conducted by Berkeley ...
int_unix - Pablo Manalastas, PhD
... The shell program /bin/sh accepts commands typed by the user and causes the execution of those commands. It is the go-between the user and the facilities of the Unix kernel. Some of its functions are: Filename completion – you supply a pattern and the shell gets all files that fit the pattern; ...
... The shell program /bin/sh accepts commands typed by the user and causes the execution of those commands. It is the go-between the user and the facilities of the Unix kernel. Some of its functions are: Filename completion – you supply a pattern and the shell gets all files that fit the pattern; ...
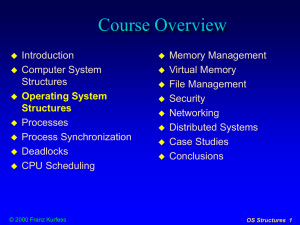
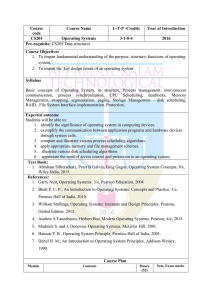
CS204 Operating Systems
... 1. To impart fundamental understanding of the purpose, structure, functions of operating system. 2. To impart the key design issues of an operating system Syllabus Basic concepts of Operating System, its structure, Process management, inter-process communication, process synchronization, CPU Schedul ...
... 1. To impart fundamental understanding of the purpose, structure, functions of operating system. 2. To impart the key design issues of an operating system Syllabus Basic concepts of Operating System, its structure, Process management, inter-process communication, process synchronization, CPU Schedul ...
Slide 1
... Operating System (cont’d) In general, there is one narrow usage and a broader usage Narrow usage: Only the parts that deal directly with the hardware, and very low level features (i.e. the kernel) Broader usage: Also includes system software. What is “system software” depends on the nature of ...
... Operating System (cont’d) In general, there is one narrow usage and a broader usage Narrow usage: Only the parts that deal directly with the hardware, and very low level features (i.e. the kernel) Broader usage: Also includes system software. What is “system software” depends on the nature of ...
Operating Systems
... Operating System as a Resource Manager Operating systems allow multiple programs to run at the same time Resource management includes multiplexing (sharing) resources Allocating disk space and keeping track of who is using which disk blocks is a typical operating system resource management task. ...
... Operating System as a Resource Manager Operating systems allow multiple programs to run at the same time Resource management includes multiplexing (sharing) resources Allocating disk space and keeping track of who is using which disk blocks is a typical operating system resource management task. ...
ppt
... • The file system interface defines standard operations: – file (or directory) creation and deletion – manipulation of files and directories (read, write, extend, ...
... • The file system interface defines standard operations: – file (or directory) creation and deletion – manipulation of files and directories (read, write, extend, ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.