ch04 - Computer Science
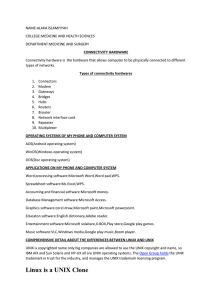
... Menu-driven interface (commands are chosen from on-screen lists) GUI (Graphical User Interfaces), pronounced “gooey” Mac OS was developed by Macintosh in 1984 using GUI. Microsoft Windows is now the most popular operating system. UNIX and Linux UNIX was developed at Bell Labs before pers ...
... Menu-driven interface (commands are chosen from on-screen lists) GUI (Graphical User Interfaces), pronounced “gooey” Mac OS was developed by Macintosh in 1984 using GUI. Microsoft Windows is now the most popular operating system. UNIX and Linux UNIX was developed at Bell Labs before pers ...
Unix Commands
... the permissions for a triplet. • We can do this by determining whether or not a permission is turned on or off. • If turned on, a permission gets a value of 1; if turned off, it gets a value of 0. ...
... the permissions for a triplet. • We can do this by determining whether or not a permission is turned on or off. • If turned on, a permission gets a value of 1; if turned off, it gets a value of 0. ...
APT 2040: OPERATING SYSTEMS Pre
... provides an understanding of the characteristics and the operating principles of the main hardware components of a computer system. In addition, the course covers the concepts and fundamentals of the operating systems. These fundamentals include process management, memory management, and device mana ...
... provides an understanding of the characteristics and the operating principles of the main hardware components of a computer system. In addition, the course covers the concepts and fundamentals of the operating systems. These fundamentals include process management, memory management, and device mana ...
Operating System Concepts
... • Some sophisticated Op.Systems allow the user to control the way the O.S. copes with tasks or jobs – The user has no direct interaction with the computer system but uses a series of instructions to alter the priority of the tasks ...
... • Some sophisticated Op.Systems allow the user to control the way the O.S. copes with tasks or jobs – The user has no direct interaction with the computer system but uses a series of instructions to alter the priority of the tasks ...
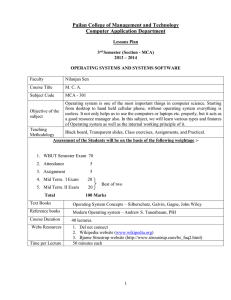
accounting for managers - Pailan College of Management and
... Methodology Assessment of the Students will be on the basis of the following weightage :- ...
... Methodology Assessment of the Students will be on the basis of the following weightage :- ...
Introduction to Distributed Systems
... and having the kernel return the desired result to the user process. Many distributed systems that are extensions of UNIX® use this approach because UNIX® itself has a large, monolithic kernel. Most distributed systems that have been designed from scratch use microkernel method. The microkernel is m ...
... and having the kernel return the desired result to the user process. Many distributed systems that are extensions of UNIX® use this approach because UNIX® itself has a large, monolithic kernel. Most distributed systems that have been designed from scratch use microkernel method. The microkernel is m ...
Slide 2: Operating System Overview
... user no longer has direct access to processor job is submitted to computer operator who batches them together and places them on an input device program branches back to the monitor when finished ...
... user no longer has direct access to processor job is submitted to computer operator who batches them together and places them on an input device program branches back to the monitor when finished ...
UNIX Operating System
... UNIX Operating System Journaling file system A journaling file system keeps track of the changes that will be made in a journal (usually a circular log in a dedicated area of the file system) before committing them to the main file system. In the event of a system crash or power failure, such file ...
... UNIX Operating System Journaling file system A journaling file system keeps track of the changes that will be made in a journal (usually a circular log in a dedicated area of the file system) before committing them to the main file system. In the event of a system crash or power failure, such file ...
Operating Systems - Computer Science
... user no longer has direct access to processor job is submitted to computer operator who batches them together and places them on an input device program branches back to the monitor when finished ...
... user no longer has direct access to processor job is submitted to computer operator who batches them together and places them on an input device program branches back to the monitor when finished ...
System Software - California State University, Fresno
... • Tracks are the concentric rings on a disk, these rings are divided by wedge-shaped sections called Sectors • Your system tries to save each file on a single track, when this is not possible the file is broken or Fragmented into smaller pieces and placed where space is available – After a while the ...
... • Tracks are the concentric rings on a disk, these rings are divided by wedge-shaped sections called Sectors • Your system tries to save each file on a single track, when this is not possible the file is broken or Fragmented into smaller pieces and placed where space is available – After a while the ...
pdf
... Unix focuses on a very simple process + I/O model Mach focused on a very basic / general VM model, then uses it to support Unix, Windows, and “native” services If Mach mostly is a VM infrastructure, was this the best way to do that? If Linux needed to extend Unix, was Unix simplicity as much of a wi ...
... Unix focuses on a very simple process + I/O model Mach focused on a very basic / general VM model, then uses it to support Unix, Windows, and “native” services If Mach mostly is a VM infrastructure, was this the best way to do that? If Linux needed to extend Unix, was Unix simplicity as much of a wi ...
PDF
... (e) Would it make sense for a webcam to use DMA or interrupt-based I/O? Why? Give an example device that could sensibly use the other form of I/O. 2. Processes Suppose we wished to write an operating system that doesn’t support time-sharing: it runs each process without interruption until it termina ...
... (e) Would it make sense for a webcam to use DMA or interrupt-based I/O? Why? Give an example device that could sensibly use the other form of I/O. 2. Processes Suppose we wished to write an operating system that doesn’t support time-sharing: it runs each process without interruption until it termina ...
History of OS
... What is an Operating System • It is an extended machine – Hides the messy details which must be performed – Presents user with a virtual machine, easier to use ...
... What is an Operating System • It is an extended machine – Hides the messy details which must be performed – Presents user with a virtual machine, easier to use ...
Chapter 1
... Mainframe operating systems Server operating systems Multiprocessor operating systems Personal computer operating systems Real-time operating systems Embedded operating systems Smart card operating systems ...
... Mainframe operating systems Server operating systems Multiprocessor operating systems Personal computer operating systems Real-time operating systems Embedded operating systems Smart card operating systems ...
Introduction
... 1.2 History of operating systems 1.3 The operating system zoo 1.4 Computer hardware review 1.5 Operating system concepts 1.6 System calls 1.7 Operating system structure ...
... 1.2 History of operating systems 1.3 The operating system zoo 1.4 Computer hardware review 1.5 Operating system concepts 1.6 System calls 1.7 Operating system structure ...
Chapter 1 Introduction
... Mainframe operating systems Server operating systems Multiprocessor operating systems Personal computer operating systems Real-time operating systems Embedded operating systems Smart card operating systems ...
... Mainframe operating systems Server operating systems Multiprocessor operating systems Personal computer operating systems Real-time operating systems Embedded operating systems Smart card operating systems ...
Introduction Chapter 1 Introduction What is an Operating System
... 1.2 History of operating systems 1.3 The operating system zoo 1.4 Computer hardware review 1.5 Operating system concepts 1.6 System calls 1.7 Operating system structure ...
... 1.2 History of operating systems 1.3 The operating system zoo 1.4 Computer hardware review 1.5 Operating system concepts 1.6 System calls 1.7 Operating system structure ...
ITS 225 (Operating Systems) Lecture Notes
... If nothing is happening (no programs are ready to run, no IO devices are waiting for service, and no users are making requests), then the system sits idle, waiting for an event. Events are signaled by interrupts. • Hardware interrupts: usually triggered when a device enables a line on the system bus ...
... If nothing is happening (no programs are ready to run, no IO devices are waiting for service, and no users are making requests), then the system sits idle, waiting for an event. Events are signaled by interrupts. • Hardware interrupts: usually triggered when a device enables a line on the system bus ...
PowerPoint XP
... Can represent simple or complex entities Can be implemented In the kernel as a driver As a user level process By remote servers ...
... Can represent simple or complex entities Can be implemented In the kernel as a driver As a user level process By remote servers ...
CS311 Introduction to Operating Systems I - Summer 2009
... different physical memory, different CPU usage statistics ...
... different physical memory, different CPU usage statistics ...
Introduction
... and what kinds of computer resources Protection and security - The owners of information stored in a multi-user or networked computer system may want to control use of that information, concurrent processes should not interfere with each other Protection involves ensuring that all access to system ...
... and what kinds of computer resources Protection and security - The owners of information stored in a multi-user or networked computer system may want to control use of that information, concurrent processes should not interfere with each other Protection involves ensuring that all access to system ...
UNIX Operating System Names
... The Linux kernel is a monolithic Unix-like computer operating system kernel. The Linux operating system is based on it and deployed on both traditional computer systems such as personal computers and servers, usually in the form of Linux distributions, and on various embedded devices such as routers ...
... The Linux kernel is a monolithic Unix-like computer operating system kernel. The Linux operating system is based on it and deployed on both traditional computer systems such as personal computers and servers, usually in the form of Linux distributions, and on various embedded devices such as routers ...
Advanced Operating Systems
... Provide resource needs of an application CPU, memory, device access ...
... Provide resource needs of an application CPU, memory, device access ...
Operating Systems
... File System: is the logical view that an OS provides so that users can manage data as a collection of files ...
... File System: is the logical view that an OS provides so that users can manage data as a collection of files ...
pdf
... Consider the various definitions of operating system. Next, consider whether the operating system should include applications such as Web browsers and mail programs. Argue both that it should and that it should not, and support your answers. Answer: Point. Applications such as web browsers and email ...
... Consider the various definitions of operating system. Next, consider whether the operating system should include applications such as Web browsers and mail programs. Argue both that it should and that it should not, and support your answers. Answer: Point. Applications such as web browsers and email ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.