Introduction to UNIX/Linux - gozips.uakron.edu
... Executes more than one program at a time for a user It can run several programs in the background while users are working on another task in the foreground ...
... Executes more than one program at a time for a user It can run several programs in the background while users are working on another task in the foreground ...
Module 3: Operating
... A virtual-machine system is a perfect vehicle for operating-systems research and development. System development is done on the virtual machine, instead of on a physical machine and so does not disrupt normal system operation. The virtual machine concept is difficult to implement due to the effo ...
... A virtual-machine system is a perfect vehicle for operating-systems research and development. System development is done on the virtual machine, instead of on a physical machine and so does not disrupt normal system operation. The virtual machine concept is difficult to implement due to the effo ...
Ceng 334 - Operating Systems
... to speed up the process (one pass instead of two) for large memories When page daemon runs, it first clears the R bit at the front hand, and then checks the R bit at the back hand, after which it advances both hands Each time the page daemon runs, the hands rotate less than a full revolution, the am ...
... to speed up the process (one pass instead of two) for large memories When page daemon runs, it first clears the R bit at the front hand, and then checks the R bit at the back hand, after which it advances both hands Each time the page daemon runs, the hands rotate less than a full revolution, the am ...
Best-Effort Multimedia Networking Outline
... Memory Management CPU Scheduling Process Management Device Management Hardware ...
... Memory Management CPU Scheduling Process Management Device Management Hardware ...
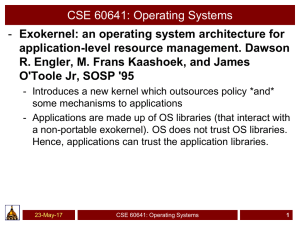
PPT - Surendar Chandra
... • Traditional Operating Systems manage lower level details and perform resource allocation. They are designed to be portable. Hence, they define interfaces (e.g. system calls). Abstractions add overhead and so the OS is general purpose but not optimized for a specific scenario – Data bases - need ac ...
... • Traditional Operating Systems manage lower level details and perform resource allocation. They are designed to be portable. Hence, they define interfaces (e.g. system calls). Abstractions add overhead and so the OS is general purpose but not optimized for a specific scenario – Data bases - need ac ...
Operating Systems
... interface, and execute and provide services for applications software. Keep in mind, however, that much of the work of an operating system is hidden from the user. In particular, the first listed function, managing the computer's resources, is taken care of without the user being aware of the detail ...
... interface, and execute and provide services for applications software. Keep in mind, however, that much of the work of an operating system is hidden from the user. In particular, the first listed function, managing the computer's resources, is taken care of without the user being aware of the detail ...
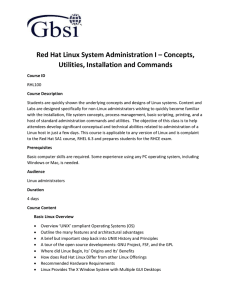
Red Hat Linux System Administration I – Concepts
... Labs are designed specifically for non-Linux administrators wishing to quickly become familiar with the installation, file system concepts, process management, basic scripting, printing, and a host of standard administration commands and utilities. The objective of this class is to help attendees de ...
... Labs are designed specifically for non-Linux administrators wishing to quickly become familiar with the installation, file system concepts, process management, basic scripting, printing, and a host of standard administration commands and utilities. The objective of this class is to help attendees de ...
Operating Systems CSLO - Barbara Hecker
... (25 points) Select one of the following essay topics. Write a 2-3 page (double-spaced) essay on your selected topic. You must provide your own writing and cannot include portions cut-n-pasted from the internet or other sources. Topic selections: (Select one) 1. What is an operating system? What func ...
... (25 points) Select one of the following essay topics. Write a 2-3 page (double-spaced) essay on your selected topic. You must provide your own writing and cannot include portions cut-n-pasted from the internet or other sources. Topic selections: (Select one) 1. What is an operating system? What func ...
Introduction to OS - EECG Toronto
... I was working all night before the lab deadline, and my code was not working fully, and I was so tired that I lost my judgment, and ended up copying code. I heard that other students had raised their mark on the tester by copying code, or by subverting the marker, and I was really mad that others wo ...
... I was working all night before the lab deadline, and my code was not working fully, and I was so tired that I lost my judgment, and ended up copying code. I heard that other students had raised their mark on the tester by copying code, or by subverting the marker, and I was really mad that others wo ...
Operating Systems
... added burden of ensuring that they are not compromised by malicious (or incompetent) parties: Breach of confidentiality is an attack that discovers information (such as passwords) that the attacker isn’t normally allowed to see Escalation of privileges is an attack that inappropriately grants superu ...
... added burden of ensuring that they are not compromised by malicious (or incompetent) parties: Breach of confidentiality is an attack that discovers information (such as passwords) that the attacker isn’t normally allowed to see Escalation of privileges is an attack that inappropriately grants superu ...
Introduction
... – Programs written by different developers cannot communicate unless use common standard – Middleware applied to a software masking the heterogeneity of hardware & software ...
... – Programs written by different developers cannot communicate unless use common standard – Middleware applied to a software masking the heterogeneity of hardware & software ...
CSNB334 Advanced Operating Systems Course Introduction
... Do your work individually and use the group for first level discussions. All lab solutions need to be demonstrated in the lab. No marks will be given if a lab solution is submitted without giving a ...
... Do your work individually and use the group for first level discussions. All lab solutions need to be demonstrated in the lab. No marks will be given if a lab solution is submitted without giving a ...
unit-1-The-UNIX-Operating-System
... UNIX treats input/output devices like ordinary files. The source or destination for file input and output is easily controlled through a UNIX design feature called redirection. Utilities UNIX provides a rich library of utilities that can be use to increase user productivity. ...
... UNIX treats input/output devices like ordinary files. The source or destination for file input and output is easily controlled through a UNIX design feature called redirection. Utilities UNIX provides a rich library of utilities that can be use to increase user productivity. ...
2. Operating System Structure
... The shell then either waits for the process to finish or runs the process in the background. In background, the shell immediately requests another command. The user is free to ask the shell to run other programs. When the process is done, it executes an exit() system call to terminate. exit() retur ...
... The shell then either waits for the process to finish or runs the process in the background. In background, the shell immediately requests another command. The user is free to ask the shell to run other programs. When the process is done, it executes an exit() system call to terminate. exit() retur ...
Fall 2008 Term - Computer Science
... phones, watches, and Ipods). Although there are variations (different versions) of Unix, each provides fundamentally the same set of commands and tools. 4. Many variations of UNIX are open source. Thus, you can obtain the actual source code for the operating system and see exactly how it works. If f ...
... phones, watches, and Ipods). Although there are variations (different versions) of Unix, each provides fundamentally the same set of commands and tools. 4. Many variations of UNIX are open source. Thus, you can obtain the actual source code for the operating system and see exactly how it works. If f ...
Introduction
... • Of course, since they are not really files, some degree of compromise is necessary. Some system calls don’t really make sense for device files. And a system call (ioctl()) was added which doesn’t make sense for regular files. • Sometimes they are not real devices, but what are called pseudo-device ...
... • Of course, since they are not really files, some degree of compromise is necessary. Some system calls don’t really make sense for device files. And a system call (ioctl()) was added which doesn’t make sense for regular files. • Sometimes they are not real devices, but what are called pseudo-device ...
The Unix Philosophy
... job which creates other jobs such as scheduling tasks, etc). Running many processes at the same time can allow many users to connect to and use the computer resources at the same time (This concept is referred to as "multitasking"). The Unix file system allows users to share or restrict access to th ...
... job which creates other jobs such as scheduling tasks, etc). Running many processes at the same time can allow many users to connect to and use the computer resources at the same time (This concept is referred to as "multitasking"). The Unix file system allows users to share or restrict access to th ...
Linux - Rock Fort Networks
... any other operating system.[citation needed] It is a leading operating system on servers and other big iron systems such as mainframe computers and supercomputers. Although not released until 1992 due to legal complications, development of 386BSD, from which NetBSD, OpenBSD and FreeBSD descended, ...
... any other operating system.[citation needed] It is a leading operating system on servers and other big iron systems such as mainframe computers and supercomputers. Although not released until 1992 due to legal complications, development of 386BSD, from which NetBSD, OpenBSD and FreeBSD descended, ...
networking operating system
... single-user system except for the communication and shared resources bit; so let us now define a few of the relevant network O/S concepts: Requests > this is any petition from a user; could be for a file to be opened, or an output device to act on this job, not that one, or sending a message to anot ...
... single-user system except for the communication and shared resources bit; so let us now define a few of the relevant network O/S concepts: Requests > this is any petition from a user; could be for a file to be opened, or an output device to act on this job, not that one, or sending a message to anot ...
Operating-System Structure
... approach in that the primary module has only core functions and knowledge of how to load and communicate with other modules; but it is more efficient, because modules do not need to invoke message passing in order to communicate. ...
... approach in that the primary module has only core functions and knowledge of how to load and communicate with other modules; but it is more efficient, because modules do not need to invoke message passing in order to communicate. ...
OUTLINE - Bilkent University
... Windows File Systems • include FAT which is File Allocate Table. • File Allocate Table is a partially -patented file system -developed by Microsoft -for MS-DOS and versions of Microsoft Windows. • a cluster is the unit of disk space allocation for files and directories. • Fragmentation is a alloca ...
... Windows File Systems • include FAT which is File Allocate Table. • File Allocate Table is a partially -patented file system -developed by Microsoft -for MS-DOS and versions of Microsoft Windows. • a cluster is the unit of disk space allocation for files and directories. • Fragmentation is a alloca ...
ppt
... – Defined as ability to write source code so that it can run on two or more types of machines – Requires use of a different compiler/loader and library for each type of machine ...
... – Defined as ability to write source code so that it can run on two or more types of machines – Requires use of a different compiler/loader and library for each type of machine ...
2. OS Components
... Behind the scenes, the functions that make up an API typically invoke the actual system calls on behalf of the application programmer. For example, the Windows function CreateProcess() (which unsurprisingly is used to create a new process) actually invokes the NTCreateProcess() system call in the Wi ...
... Behind the scenes, the functions that make up an API typically invoke the actual system calls on behalf of the application programmer. For example, the Windows function CreateProcess() (which unsurprisingly is used to create a new process) actually invokes the NTCreateProcess() system call in the Wi ...
Operating Systems Operating Systems Operating Systems
... In a monolithic kernel nearly all OS functionality is contained in a single software module. “… the ‘Big Mess’. The structure is that there is no ...
... In a monolithic kernel nearly all OS functionality is contained in a single software module. “… the ‘Big Mess’. The structure is that there is no ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.