* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Topic 2: Lesson 3 Intro to Firewalls
Proxy server wikipedia , lookup
Mobile security wikipedia , lookup
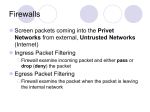
Wireless security wikipedia , lookup
Computer security wikipedia , lookup
Computer and network surveillance wikipedia , lookup
Denial-of-service attack wikipedia , lookup
Network tap wikipedia , lookup
Cybercrime countermeasures wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
Unix security wikipedia , lookup
Topic 2: Lesson 3 Intro to Firewalls Summary 1 Basic questions What is a firewall? What can a firewall do? What is packet filtering? What is proxying? What is stateful packet filtering? Compare network layer firewalls and application layer firewalls. Enumerate the benefits of a firewall Enumerate the limitations of a firewall 2 What is a firewall? Protect internal network from outside threats creates choke point from outside of network mechanism that permits access control between two or more networks come in various forms: hardware and software, usually a combination 3 What can a firewall do? keep outsiders from breaking in keep insiders from exposing valuable data enable secure communication between networks Firewall protects both direction Firewall can proxy an Internet service block services known to be problematic 4 What is packet filtering? One of the three types of firewall technology determines whether a packet can be accepted or not based on IP address, port number, protocol type spoofed with IP or port # filtering, doesn’t look at contents firewall sets up rule set, verifies packets with header information what is inside a packet header: – source IP, destination IP, protocol, source port, destination port, size of packet, sequence # Can viruses or Trojans attack a firewall? – Yes, vulnerabilities in firewalls that can be exploited – previous employer, viruses disable firewalls 5 What is proxying? use a proxy server as an intermediary between two servers. Communication sent between the proxy and internal hides real IP address from whoever you are communicating to does logging and access control based on policy, takes requests for user in group don’t permit traffic between networks 6 What is stateful packet filtering? across b/w functionality of packet filtering and firewalls provides more security checks inspects first packet, adds entry to state table state table= tabulates state of the system, state is how you define it to be . State is connections being made updated after valid connections are made. Follow-up packets for new connections use that table for verification. use valid host to transmit malicious code Does state table have an expiration time? Session time, start and termination time- time window, beyond the connection ends Does termination expire instantaneously- depends based on configured session time; How does it determine if first packet is valid - for efficiency, if you spoof original packet, not sure 7 Compare network layer firewalls and application layer firewalls. app layer firewalls block traffic based on what application u are using – network layer examine addressing and others network layer firewalls are faster but do less inspection can just block port rather than app? – ports used by app can change most firewalls include aspects of both firewall can be strengthened by changing firmware example of network is packet filtering and example of application layer is proxying 8 Enumerate the benefits of a firewall cost benefits of firewall make economic sense, inexpensive and high rewards enforce organizational security policies enable logging of connections and data logs produced can give valuable information about the network help prevent net security issues from spreading across network segments firewalls are only as useful as the unified security policy which is defined 9 Enumerate the limitations of a firewall firewalls cant protect against malicious inside attacks not too effective against dialup susceptible to IP spoofing stop attacks at network level, so many attacks which they cannot block cant prevent against Trojans, viruses, etc can be compromised like any other part of the network exploit problems in e-mail for DOS attacks only as good as updates- need security updates/firmware cant protect against vulnerable protocols- TCP/IP, http, etc If you are greedy, you will eat the honey in the pot 10