ch15
... transaction may not be serializable – it may find some records inserted by a transaction but not find others. Read committed — only committed records can be read, but ...
... transaction may not be serializable – it may find some records inserted by a transaction but not find others. Read committed — only committed records can be read, but ...
File
... Is characterized by a large number of short online transactions (INSERT, UPDATE, DELETE). The main emphasis for OLTP systems is put on very fast query processing, maintaining database in multi-access environments and an effectiveness measured by number of transactions per second. ...
... Is characterized by a large number of short online transactions (INSERT, UPDATE, DELETE). The main emphasis for OLTP systems is put on very fast query processing, maintaining database in multi-access environments and an effectiveness measured by number of transactions per second. ...
Distributed Database Management System
... Mixed method uses both approaches. Fragments must not violate the following properties: . completeness: each information in a relation must be contained at least in a fragment; . correctness: the entire information must be obtained by summing all fragments. The distributed database design is based o ...
... Mixed method uses both approaches. Fragments must not violate the following properties: . completeness: each information in a relation must be contained at least in a fragment; . correctness: the entire information must be obtained by summing all fragments. The distributed database design is based o ...
Database Intrusion Detection with Automated Recovery
... In addition to the medium level of security, even the recovery can be automated. Recovery Phase In automated recovery rollback the database to the state just before the intrusion. Create a transaction dependency graph beginning from the malicious transaction. Use this graph to redo all the ben ...
... In addition to the medium level of security, even the recovery can be automated. Recovery Phase In automated recovery rollback the database to the state just before the intrusion. Create a transaction dependency graph beginning from the malicious transaction. Use this graph to redo all the ben ...
Chapter 17: Parallel Databases
... • Division of relation r into fragments r1, r2, …, rn which contain sufficient information to reconstruct relation r. • Horizontal fragmentation: each tuple of r is assigned to one or more fragments • Vertical fragmentation: the schema for relation r is split into several smaller schemas – All schem ...
... • Division of relation r into fragments r1, r2, …, rn which contain sufficient information to reconstruct relation r. • Horizontal fragmentation: each tuple of r is assigned to one or more fragments • Vertical fragmentation: the schema for relation r is split into several smaller schemas – All schem ...
Transaction Time - UCLA Computer Science
... Set of tuples: Generally used for transaction time, to timestamp a set of tuples inserted or modified by a transaction. ...
... Set of tuples: Generally used for transaction time, to timestamp a set of tuples inserted or modified by a transaction. ...
Realisation of Active Multidatabases by Extending Standard
... displayed, modified and written back. The GTM is the vital modul for proper and secure integration of the autonomous local database systems (LDBS). Applications can transmit global queries to the GTM, which distributes them to the appropiate LDBSs, organizes the results and returns those to the appl ...
... displayed, modified and written back. The GTM is the vital modul for proper and secure integration of the autonomous local database systems (LDBS). Applications can transmit global queries to the GTM, which distributes them to the appropiate LDBSs, organizes the results and returns those to the appl ...
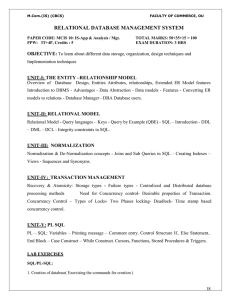
(4) RDBMS: Relational Data Base Management System
... 4. Creation of forms for the case study assigned. 5. Creation of reports based on different queries 6. Creation password and security features of applications 7. Usage of locking table locking, facilities in applications NOTE: (i) Use Case Studies such as Library Information System, Pay roll system, ...
... 4. Creation of forms for the case study assigned. 5. Creation of reports based on different queries 6. Creation password and security features of applications 7. Usage of locking table locking, facilities in applications NOTE: (i) Use Case Studies such as Library Information System, Pay roll system, ...
Transactions Transactions Transaction Concept Example of Fund
... be serializable – it may find some records inserted by a transaction but not find others. reads of record may return different (but committed) values. ...
... be serializable – it may find some records inserted by a transaction but not find others. reads of record may return different (but committed) values. ...
Introduction to Persistent Storage, Concurrency Control and
... Note: Aborts can be transaction generated or imposed by the Database System. ABORT wipes out all transaction effects (on the database or users) Causes? System failure in the middle of a transaction, The Database System discovers it has returned an incorrect value to the transaction. Execution of a t ...
... Note: Aborts can be transaction generated or imposed by the Database System. ABORT wipes out all transaction effects (on the database or users) Causes? System failure in the middle of a transaction, The Database System discovers it has returned an incorrect value to the transaction. Execution of a t ...
Detecting Intrusions in Databases
... intrusions with the feedback mechanism. There is no damage containment or recovery. This allows user to formulate a proper security perimeter with all possible transactions listed in the user access graph while also been aware of the security. 2. Medium In the medium level we provide the low level o ...
... intrusions with the feedback mechanism. There is no damage containment or recovery. This allows user to formulate a proper security perimeter with all possible transactions listed in the user access graph while also been aware of the security. 2. Medium In the medium level we provide the low level o ...
OODB
... Versant Version 6.0 Concurrency Persistent locks support long transactions. Short locks are also provided for shorter transactions. “No-locks” for optimistic locking. ...
... Versant Version 6.0 Concurrency Persistent locks support long transactions. Short locks are also provided for shorter transactions. “No-locks” for optimistic locking. ...
Orphaned MSDTC transactions (-2 spids).
... only option was to restart SQL Server to clear those locks. Spids with a value of -2 are orphaned distributed transactions. What’s an orphaned distributed transaction? In a nutshell, it’s a distributed transaction for which the transactional state is unknown. A distributed transaction is a database ...
... only option was to restart SQL Server to clear those locks. Spids with a value of -2 are orphaned distributed transactions. What’s an orphaned distributed transaction? In a nutshell, it’s a distributed transaction for which the transactional state is unknown. A distributed transaction is a database ...
Document
... Trigger-based protocols “Check” constraints on tables “Assertion” constraints on database as a whole Basic form: ...
... Trigger-based protocols “Check” constraints on tables “Assertion” constraints on database as a whole Basic form: ...
Transaction Processing and Management in Distributed Database
... distributed transaction contains statements that access more than one node. A distributed transaction is a transaction that includes one or more statements that, individually or as a group, update data on two or more distinct nodes of a distributed database. 4. Two-Phase Commit of transaction in Dis ...
... distributed transaction contains statements that access more than one node. A distributed transaction is a transaction that includes one or more statements that, individually or as a group, update data on two or more distinct nodes of a distributed database. 4. Two-Phase Commit of transaction in Dis ...
Recovery - Dr Gordon Russell
... with ‘COMMIT’ apply the data part of the log to the database. 4. If a log entry for a transaction ends with anything other than COMMIT, do nothing for that transaction. 5. flush the data to the disk, and then truncate the log to zero. 6. the process or reapplying transaction from the log is sometime ...
... with ‘COMMIT’ apply the data part of the log to the database. 4. If a log entry for a transaction ends with anything other than COMMIT, do nothing for that transaction. 5. flush the data to the disk, and then truncate the log to zero. 6. the process or reapplying transaction from the log is sometime ...
Transactions
... If the user is informed about the commit he/she can be sure that all changes performed by T are installed in the DB. A transaction might abort (or be aborted by the DBMS) after executing some actions. In this case the DBMS undoes all modifications so far. After the abort the DB state is as if the ...
... If the user is informed about the commit he/she can be sure that all changes performed by T are installed in the DB. A transaction might abort (or be aborted by the DBMS) after executing some actions. In this case the DBMS undoes all modifications so far. After the abort the DB state is as if the ...
Transactions
... copy only after the transaction reaches partial commit and all updated pages have been flushed to disk. in case transaction fails, old consistent copy pointed to by db_pointer can be used, and the shadow copy can be deleted. ...
... copy only after the transaction reaches partial commit and all updated pages have been flushed to disk. in case transaction fails, old consistent copy pointed to by db_pointer can be used, and the shadow copy can be deleted. ...
Chap.10
... – Allows concurrent transactions to access same row • Requires use of different fields (attributes) within the row Database Systems, 8th Edition ...
... – Allows concurrent transactions to access same row • Requires use of different fields (attributes) within the row Database Systems, 8th Edition ...
Transaction Management Overview
... If a transaction Ti is aborted, all its actions have to be undone. Not only that, if Tj reads an object last written by Ti, Tj must be aborted as well! Most systems avoid such cascading aborts by releasing a transaction’s locks only at commit time. ...
... If a transaction Ti is aborted, all its actions have to be undone. Not only that, if Tj reads an object last written by Ti, Tj must be aborted as well! Most systems avoid such cascading aborts by releasing a transaction’s locks only at commit time. ...
Distributed Database
... Must provide the following transparencies : – Transaction transparency? – Distribution transparency? – Failure transparency? – Performance transparency? – Heterogeneity transparency? ...
... Must provide the following transparencies : – Transaction transparency? – Distribution transparency? – Failure transparency? – Performance transparency? – Heterogeneity transparency? ...
CSc-340 10a
... Extension to test for view serializability has cost exponential in the size of the precedence graph. ...
... Extension to test for view serializability has cost exponential in the size of the precedence graph. ...
Overview of Transaction Management
... Each transaction must leave the database in a consistent state if the DB is consistent when the transaction begins. • DBMS will enforce some ICs, depending on the ICs declared in ...
... Each transaction must leave the database in a consistent state if the DB is consistent when the transaction begins. • DBMS will enforce some ICs, depending on the ICs declared in ...
CUSTOMER_CODE SMUDE DIVISION_CODE SMUDE
... Describe the transaction processing concepts. A transaction is an atomic unit comprising one or more SQL statements. A transaction begins with the first executable statement and ends when it is committed or rolled back. Single user versus multiuser systems – A DBMS is used if at most one user can us ...
... Describe the transaction processing concepts. A transaction is an atomic unit comprising one or more SQL statements. A transaction begins with the first executable statement and ends when it is committed or rolled back. Single user versus multiuser systems – A DBMS is used if at most one user can us ...