Security - Ingate Systems
... • Authenticating information that allows voice access to Call Control and UC Applications • VoIP Security covers a variety of computer networks, both public and private, that are used in everyday jobs conducting transactions and communications among businesses, government agencies and individuals. ...
... • Authenticating information that allows voice access to Call Control and UC Applications • VoIP Security covers a variety of computer networks, both public and private, that are used in everyday jobs conducting transactions and communications among businesses, government agencies and individuals. ...
Internal Networks and Physical Attacks
... GFI LANguard Security Event Log Monitor is a host-based intrusion detection system primarily designed to monitor Windows-based networks for security breaches in real-time, but with enhanced flexibility to meet many other monitoring needs. GFI LANguard continuously scans the security event logs of al ...
... GFI LANguard Security Event Log Monitor is a host-based intrusion detection system primarily designed to monitor Windows-based networks for security breaches in real-time, but with enhanced flexibility to meet many other monitoring needs. GFI LANguard continuously scans the security event logs of al ...
Avaya™ G700 Media Gateway Security - Issue 1.0
... 10) Record and monitor to whom and when access is granted. 11) Access to the LAN should also be restricted via access control list on the Routers and Firewalls. 12) It is recommended that customers configure their firewalls and routers to restrict Avaya remote access to only Avaya IP address endpoin ...
... 10) Record and monitor to whom and when access is granted. 11) Access to the LAN should also be restricted via access control list on the Routers and Firewalls. 12) It is recommended that customers configure their firewalls and routers to restrict Avaya remote access to only Avaya IP address endpoin ...
Introduction
... universally accepted definition. Researchers often give their own spin to IA, usually reflecting their own concerns. In these slides, are several different views of IA, including the DoD view (above), Herrmann’s view (below), and Blyth and Kovacich’s view (below). Be able to compare and contrast the ...
... universally accepted definition. Researchers often give their own spin to IA, usually reflecting their own concerns. In these slides, are several different views of IA, including the DoD view (above), Herrmann’s view (below), and Blyth and Kovacich’s view (below). Be able to compare and contrast the ...
HSARPA Cyber Security R&D
... destined for any service or port in a target machine in order to prevent the spread of destructive code through networks and applications. These technologies should focus on detecting “zero day attacks”, the first appearance of malicious code for which no known defense has been constructed. 23 Septe ...
... destined for any service or port in a target machine in order to prevent the spread of destructive code through networks and applications. These technologies should focus on detecting “zero day attacks”, the first appearance of malicious code for which no known defense has been constructed. 23 Septe ...
Network Security Policy in the Work Place
... upload malware programs on the company’s systems. • This incident could have been avoided with proper network security auditing and planning measures. This is one of the many examples of how important network security policy can be in businesses and organizations. ...
... upload malware programs on the company’s systems. • This incident could have been avoided with proper network security auditing and planning measures. This is one of the many examples of how important network security policy can be in businesses and organizations. ...
Fujitsu`s Security Technology Based on Practical Knowledge
... centrally managed for a unified security system. Information on security incident response has been rolled out to overseas operations so that countermeasures can be executed swiftly after a security threat is detected. A new issue emerged while implementing these measures of security reinforcement. ...
... centrally managed for a unified security system. Information on security incident response has been rolled out to overseas operations so that countermeasures can be executed swiftly after a security threat is detected. A new issue emerged while implementing these measures of security reinforcement. ...
DATASHEET Malwarebytes Endpoint Security
... Simplifies endpoint security management and identifies vulnerable endpoints. Streamlines endpoint security deployment and maximizes IT management resources. ...
... Simplifies endpoint security management and identifies vulnerable endpoints. Streamlines endpoint security deployment and maximizes IT management resources. ...
Authentication and Access Control
... of the 21st century Involves using someone’s personal information, such as social security numbers, to establish bank or credit card accounts that are then left unpaid, leaving the victim with the debts and destroy their credit rating National, state, and local legislation continues to be enacte ...
... of the 21st century Involves using someone’s personal information, such as social security numbers, to establish bank or credit card accounts that are then left unpaid, leaving the victim with the debts and destroy their credit rating National, state, and local legislation continues to be enacte ...
Introduction
... Power and responsibility – Personnel responsible for security often don’t have power to enforce security. CSC 682: Advanced Computer Security ...
... Power and responsibility – Personnel responsible for security often don’t have power to enforce security. CSC 682: Advanced Computer Security ...
Principles of Computer Security
... – Filter undesirable content – Filter malicious code such as browser hijacking attempts ...
... – Filter undesirable content – Filter malicious code such as browser hijacking attempts ...
Whitepaper: Network Penetration Testing
... networks can personify polar differences in characters. It can vary from remote system & password compromise, web server, database, network service, network device, directory and miscellaneous non-configuration to information disclosure to weak cryptography. This array of vulnerabilities propel the ...
... networks can personify polar differences in characters. It can vary from remote system & password compromise, web server, database, network service, network device, directory and miscellaneous non-configuration to information disclosure to weak cryptography. This array of vulnerabilities propel the ...
Introduction to Information Security Chapter N
... and for stealing information from a network Social engineering: using social skills to convince people to reveal access credentials or other valuable information to attacker ...
... and for stealing information from a network Social engineering: using social skills to convince people to reveal access credentials or other valuable information to attacker ...
Introduction to Information Security Chapter N
... and for stealing information from a network Social engineering: using social skills to convince people to reveal access credentials or other valuable information to attacker ...
... and for stealing information from a network Social engineering: using social skills to convince people to reveal access credentials or other valuable information to attacker ...
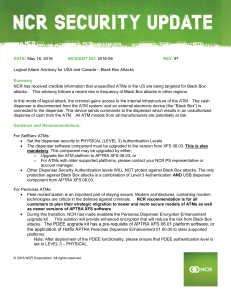
Logical attack advisory for U.S. and Canada
... dispenser is disconnected from the ATM system, and an external electronic device (the “Black Box”) is connected to the dispenser. This device sends commands to the dispenser which results in an unauthorized dispense of cash from the ATM. All ATM models from all manufacturers are potentially at risk. ...
... dispenser is disconnected from the ATM system, and an external electronic device (the “Black Box”) is connected to the dispenser. This device sends commands to the dispenser which results in an unauthorized dispense of cash from the ATM. All ATM models from all manufacturers are potentially at risk. ...
C06.InformationSecur.. - SIUE Computer Science
... Identity theft is the criminal act of stealing information about a person to assume that person’s identity to commit fraud or other crimes. People can protect themselves from identity theft by being cautious with their personal information ...
... Identity theft is the criminal act of stealing information about a person to assume that person’s identity to commit fraud or other crimes. People can protect themselves from identity theft by being cautious with their personal information ...
Chapter 13
... Virtual private networks (VPNs)—use public Internet to carry information but remains private Encryption—scramble communications Authentication—ensure information remains untampered with and comes from legitimate source Access control—verify identity of anyone using network Prentice Hall, 2002 ...
... Virtual private networks (VPNs)—use public Internet to carry information but remains private Encryption—scramble communications Authentication—ensure information remains untampered with and comes from legitimate source Access control—verify identity of anyone using network Prentice Hall, 2002 ...
security - Binus Repository
... security products on the market then you is less likely to suffer a security breach. • The Plate Spinner, or, too much to manage. The key to effective security is vision, the ability to monitor all areas simultaneously, set up alerts to irregular activity. • The Agoraphobic, or, too paranoid about w ...
... security products on the market then you is less likely to suffer a security breach. • The Plate Spinner, or, too much to manage. The key to effective security is vision, the ability to monitor all areas simultaneously, set up alerts to irregular activity. • The Agoraphobic, or, too paranoid about w ...
chapter13
... Virtual private networks (VPNs)—use public Internet to carry information but remains private Encryption—scramble communications Authentication—ensure information remains untampered with and comes from legitimate source Access control—verify identity of anyone using network Prentice Hall, 2002 ...
... Virtual private networks (VPNs)—use public Internet to carry information but remains private Encryption—scramble communications Authentication—ensure information remains untampered with and comes from legitimate source Access control—verify identity of anyone using network Prentice Hall, 2002 ...
Future of Cyber Security and the Issue of Cyber warfare: A
... In May 2014, The U.S. the Justice Department unsealed an indictment of five members of Unit 61398 of the Chinese People’s Liberation Army, charging them with hacking into the computer networks of Westinghouse Electric, U.S. Steel Corp., and other companies. Shanghai-based Unit 61398 is the cyber div ...
... In May 2014, The U.S. the Justice Department unsealed an indictment of five members of Unit 61398 of the Chinese People’s Liberation Army, charging them with hacking into the computer networks of Westinghouse Electric, U.S. Steel Corp., and other companies. Shanghai-based Unit 61398 is the cyber div ...
Important Concepts.
... Active; difficult to prevent , for preventing its require physical protection of all communication facilities all times. ...
... Active; difficult to prevent , for preventing its require physical protection of all communication facilities all times. ...
Information Security Incident Management
... •Information Security Policies: - It is a management statement that information security is important - It provide direction by establishing a set of clearlyarticulated business rules to help people make decision when using or managing information assets - It is uniquely tailored to your organizatio ...
... •Information Security Policies: - It is a management statement that information security is important - It provide direction by establishing a set of clearlyarticulated business rules to help people make decision when using or managing information assets - It is uniquely tailored to your organizatio ...
What Cyber Criminals Know Most People Don`t?
... IDC defines managed security services as "the around-the-clock remote management or monitoring of IT security functions delivered via remote security operations centers (SOCs), not through personnel onsite." The rise in frequency and complexity of attacks and the need for increasingly sophisticated ...
... IDC defines managed security services as "the around-the-clock remote management or monitoring of IT security functions delivered via remote security operations centers (SOCs), not through personnel onsite." The rise in frequency and complexity of attacks and the need for increasingly sophisticated ...
Systeemanalyse in Ontwerpprojecten
... management procedures, identification of risks from a third party, user training, physical entry controls, backing-up of data, clear desk/screen policy, controls against malicious software, user registration, forcing correct use of passwords, intrusion detection, system recovery procedures • Securit ...
... management procedures, identification of risks from a third party, user training, physical entry controls, backing-up of data, clear desk/screen policy, controls against malicious software, user registration, forcing correct use of passwords, intrusion detection, system recovery procedures • Securit ...
National Initiative For Cybersecurity Education (NICE)
... NICE will “enhance the overall cybersecurity posture of the United States by accelrating the availability of educational and training resources designed to improve the cyber behavior, skills, and knowledge of every segment of the population.” NIST, as the interagency lead for NICE, will promote the ...
... NICE will “enhance the overall cybersecurity posture of the United States by accelrating the availability of educational and training resources designed to improve the cyber behavior, skills, and knowledge of every segment of the population.” NIST, as the interagency lead for NICE, will promote the ...
Airport security
Airport security refers to the techniques and methods used in protecting passengers, staff and aircraft which use the airports from accidental/malicious harm, crime and other threats.