CISSP Guide to Security Essentials, Ch4
... will not be altered by high inputs and outputs • In other words, activities at a higher security level cannot be detected (and will not interfere with) at lower security levels – Prevents data leaking through "covert channels" – Link Ch 9d ...
... will not be altered by high inputs and outputs • In other words, activities at a higher security level cannot be detected (and will not interfere with) at lower security levels – Prevents data leaking through "covert channels" – Link Ch 9d ...
Votenet Security Infrastructure
... constituents that your elections are secure and reliable, enabling them to participate without concern that their personal information, voting choices, or other data will be improperly accessed or used. Our team at Votenet Solutions understands the importance of security in maintaining constituent t ...
... constituents that your elections are secure and reliable, enabling them to participate without concern that their personal information, voting choices, or other data will be improperly accessed or used. Our team at Votenet Solutions understands the importance of security in maintaining constituent t ...
evesecures9
... When the DRAM chips were cooled to liquid nitrogen temperatures, the Princeton group observed decay rates of 0.17 percent after 60 minutes without power. ...
... When the DRAM chips were cooled to liquid nitrogen temperatures, the Princeton group observed decay rates of 0.17 percent after 60 minutes without power. ...
ppt 2
... • This is all achieved by hardware, not the OS • TrustZone architecture provides a secure hardware base for many OS like embedded Linux and Windows CE ...
... • This is all achieved by hardware, not the OS • TrustZone architecture provides a secure hardware base for many OS like embedded Linux and Windows CE ...
Authentication and Remote Access
... • Users are assigned a set of roles that they can perform. • Each role is assigned the access permissions needed to carry out its function. • Simplifies access control: people who need the same level of access are assigned to the same role, instead of having to give them all permission individually. ...
... • Users are assigned a set of roles that they can perform. • Each role is assigned the access permissions needed to carry out its function. • Simplifies access control: people who need the same level of access are assigned to the same role, instead of having to give them all permission individually. ...
Auditing Corporate Information Security
... • Wrong passwords limit and reset • Password structure and duration • Discuss logging of all access to all confidential information • Discuss physical access restrictions and logs • Discuss your router and firewall configurations • Discuss the setup of the DMZ • Discuss the security configuration of ...
... • Wrong passwords limit and reset • Password structure and duration • Discuss logging of all access to all confidential information • Discuss physical access restrictions and logs • Discuss your router and firewall configurations • Discuss the setup of the DMZ • Discuss the security configuration of ...
Cutting Edge VoIP Security Issues Color
... DHCP, DNS, TFTP, etc. DHCP exhaustion is an example, where a hacker uses up all the IP addresses, denying service to VoIP phones ...
... DHCP, DNS, TFTP, etc. DHCP exhaustion is an example, where a hacker uses up all the IP addresses, denying service to VoIP phones ...
Network Security Policy: In the Work Place
... company from functioning? The answers to these questions identify network assets in a wide range. These include critical databases, vital applications, personal data, shared network storage, e-mail servers, and web servers. Network security policies must consider all entities that deal with your net ...
... company from functioning? The answers to these questions identify network assets in a wide range. These include critical databases, vital applications, personal data, shared network storage, e-mail servers, and web servers. Network security policies must consider all entities that deal with your net ...
lecture 1 - Philadelphia University
... Intrusion points are areas that provide an access point to your ...
... Intrusion points are areas that provide an access point to your ...
Licens
... •Demand of IP based services generates the demand for more and more IP addresses. Present available IPv4 addresses are insufficient to cater the demand in near future. •On one side IP based network provides the flexibility to deliver various services however on other side generates the security thre ...
... •Demand of IP based services generates the demand for more and more IP addresses. Present available IPv4 addresses are insufficient to cater the demand in near future. •On one side IP based network provides the flexibility to deliver various services however on other side generates the security thre ...
Student Intern Objectives
... cellblock will only be under direct supervision and in low risk situations. Direct contact with prisoners is prohibited. b. Courtroom Security Objective is to learn the proper procedures for producing a federal prisoner in court and the role of the USMS in federal court proceedings. The student will ...
... cellblock will only be under direct supervision and in low risk situations. Direct contact with prisoners is prohibited. b. Courtroom Security Objective is to learn the proper procedures for producing a federal prisoner in court and the role of the USMS in federal court proceedings. The student will ...
XML: Part - Houston Community College System
... directory immediately after a certificate is issued or revoked so users can refer to this directory to see changes • Can provide the information in a publicly accessible directory, called a Certificate Repository (CR) • Some organizations set up a Registration Authority (RA) to handle some CA, tasks ...
... directory immediately after a certificate is issued or revoked so users can refer to this directory to see changes • Can provide the information in a publicly accessible directory, called a Certificate Repository (CR) • Some organizations set up a Registration Authority (RA) to handle some CA, tasks ...
Integrate and Accelerate Endpoint Threat Defense
... To combat these threats, security administrators are looking for new methods to keep their endpoints—and data—safe. Even worse, explosive growth in endpoints and mobility have opened new potential attack vectors for cybercriminals and new places for malware to hide. In attempt to head off every pote ...
... To combat these threats, security administrators are looking for new methods to keep their endpoints—and data—safe. Even worse, explosive growth in endpoints and mobility have opened new potential attack vectors for cybercriminals and new places for malware to hide. In attempt to head off every pote ...
CSC 482/582: Computer Security
... Advanced means the attacker can conduct attacks ranging from publicly available exploits to research new vulnerabilities and develop custom exploits. Persistent means the attacker has a mission; they are not opportunistic intruders and will not stop attacking and find easier targets if they counter ...
... Advanced means the attacker can conduct attacks ranging from publicly available exploits to research new vulnerabilities and develop custom exploits. Persistent means the attacker has a mission; they are not opportunistic intruders and will not stop attacking and find easier targets if they counter ...
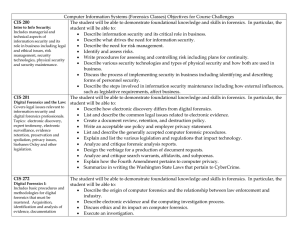
Computer Information Systems (Forensics Classes) Objectives for
... various protocols, responding to attacks on FTP, HTTP, DNS, HTTPS and SSH with advanced attack detection ...
... various protocols, responding to attacks on FTP, HTTP, DNS, HTTPS and SSH with advanced attack detection ...
DCN-7-Network_Security
... –Issued to organizations or individuals by an agency called: •Certification authority (CA). –Examples: »Thawte »VeriSign »Entrust »Equifax Secure ...
... –Issued to organizations or individuals by an agency called: •Certification authority (CA). –Examples: »Thawte »VeriSign »Entrust »Equifax Secure ...
Mainline How Secure Are You K12 Security Preseo Rev 1
... • Children's Internet Protection Act (CIPA) 2000 – CIPA requires schools and libraries using E-Rate discounts to operate "a technology protection measure with respect to any of its computers with Internet access that protects against access through such computers to visual depictions that are obscen ...
... • Children's Internet Protection Act (CIPA) 2000 – CIPA requires schools and libraries using E-Rate discounts to operate "a technology protection measure with respect to any of its computers with Internet access that protects against access through such computers to visual depictions that are obscen ...
II.I Selected Database Issues: 1
... server. It intercepts all requests to the Web server to see if it can fulfill them itself if not then it forwards them on. two main purposes: 1. Improve Performance: It saves the results of all requests for a certain amount of time. Much faster. 2. Filter requests: an organisation may want to preven ...
... server. It intercepts all requests to the Web server to see if it can fulfill them itself if not then it forwards them on. two main purposes: 1. Improve Performance: It saves the results of all requests for a certain amount of time. Much faster. 2. Filter requests: an organisation may want to preven ...
Security management
... • A baseline refers to a point n time that is used as a comparison for future changes • Baselines are used to define minimum level of protection that is required • In security, specific baselines can be defined per system type which indicates the necessary setting and the level of protection require ...
... • A baseline refers to a point n time that is used as a comparison for future changes • Baselines are used to define minimum level of protection that is required • In security, specific baselines can be defined per system type which indicates the necessary setting and the level of protection require ...
CSCI6268L37
... Foundations of Network and Computer Security John Black Lecture #36 Dec 11th 2009 ...
... Foundations of Network and Computer Security John Black Lecture #36 Dec 11th 2009 ...
Design and Implementation of Security Operating System based on
... Ensures that a trusted process only gets the security privilege that meets the requirement of its task. Discretionary access control: Uses ACL defined by user to implement access control of resources.
Mandatory access control:
Manages system resources by classifying them ...
... Ensures that a trusted process only gets the security privilege that meets the requirement of its task. Discretionary access control: Uses ACL defined by user to implement access control of resources.
What is Security?
... computer science, business management, information studies, and engineering. It involves the creation of a state in which information and data are secure. In this model, Kizza - Guide to Computer Network information or data ...
... computer science, business management, information studies, and engineering. It involves the creation of a state in which information and data are secure. In this model, Kizza - Guide to Computer Network information or data ...
Security Management and Operations
... firefighting with problems and incidents. Instead of controlling security matters, they are being “controlled” by the fuss from their daily chores. Good security management should at least include the elements of understanding the risk exposure of an organization, building a sound governance to mana ...
... firefighting with problems and incidents. Instead of controlling security matters, they are being “controlled” by the fuss from their daily chores. Good security management should at least include the elements of understanding the risk exposure of an organization, building a sound governance to mana ...
Lazy Garbage Collection of Recovery State for Fault – Tolerant
... Buffer overflow occurs when a program or process tries to store more data in a buffer than it was intended to hold Buffer overflows are exploited to change the flow of a program in execution Buffer overflows are by far the most commonly exploited bug on the linux/unix Operating systems ...
... Buffer overflow occurs when a program or process tries to store more data in a buffer than it was intended to hold Buffer overflows are exploited to change the flow of a program in execution Buffer overflows are by far the most commonly exploited bug on the linux/unix Operating systems ...
Airport security
Airport security refers to the techniques and methods used in protecting passengers, staff and aircraft which use the airports from accidental/malicious harm, crime and other threats.