Computer Security And The Law: What You Can Do To Protect
... According to NIST, “risk management is the process of identifying risk, assessing risk, and taking steps to reduce risk to an acceptable level.”[17] It is important that organizations determine what is acceptable and begin the process of managing risks to the accepted level so as to minimize loss or ...
... According to NIST, “risk management is the process of identifying risk, assessing risk, and taking steps to reduce risk to an acceptable level.”[17] It is important that organizations determine what is acceptable and begin the process of managing risks to the accepted level so as to minimize loss or ...
Chapter 1
... Critical Characteristics of Information (continued) Confidentiality is when information is protected from exposure to unauthorized entities Integrity is when information remains whole, complete, and uncorrupted Utility of information is quality or state of having value for some end purpose; i ...
... Critical Characteristics of Information (continued) Confidentiality is when information is protected from exposure to unauthorized entities Integrity is when information remains whole, complete, and uncorrupted Utility of information is quality or state of having value for some end purpose; i ...
A Survey of BGP Security: Issues and Solutions
... Verify Routes Before/After Accepting Them Verify Entire Route/First Hop/Not At All ...
... Verify Routes Before/After Accepting Them Verify Entire Route/First Hop/Not At All ...
Oracle9i Security
... environments by defining the protocol for interaction between provisioning service components and agents representing provisioned services. ...
... environments by defining the protocol for interaction between provisioning service components and agents representing provisioned services. ...
Course Overview - Cyber Security Lab
... reveal information, such as the location and identity of communication hosts, or the frequency and length of data being exchanged, which might be useful in guessing the nature of the communication that is taking place. Passive attacks are difficult to detect because traffic is still sent and receive ...
... reveal information, such as the location and identity of communication hosts, or the frequency and length of data being exchanged, which might be useful in guessing the nature of the communication that is taking place. Passive attacks are difficult to detect because traffic is still sent and receive ...
Secure_Email_and_Web_Browsing_SEC
... ► Malicious Program wish to run as admin ► The program asks you for permission to run…don’t allow it! ...
... ► Malicious Program wish to run as admin ► The program asks you for permission to run…don’t allow it! ...
Control Panel Security
... While any control panel in a public area is at risk, those located in impoverished neighborhoods, and areas with high crime rates are most susceptible to theft, causing system downtime and added costs, if not properly secured. Other at-risk locations include those without adequate lighting, sites hi ...
... While any control panel in a public area is at risk, those located in impoverished neighborhoods, and areas with high crime rates are most susceptible to theft, causing system downtime and added costs, if not properly secured. Other at-risk locations include those without adequate lighting, sites hi ...
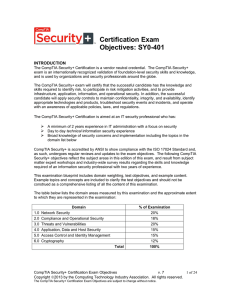
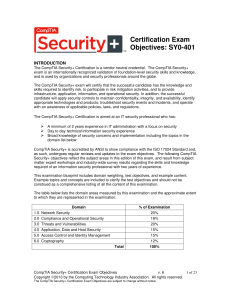
CompTIA Security (SY0-401)
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
Red Teaming: The Art of Ethical Hacking
... The term “hacker” was initially used for skilled computer enthusiasts that could “hack” their way through technical problems. Today, hackers pose one of the principal threats against our information infrastructure by exploiting vulnerabilities in code and circumventing security measures. Hacking use ...
... The term “hacker” was initially used for skilled computer enthusiasts that could “hack” their way through technical problems. Today, hackers pose one of the principal threats against our information infrastructure by exploiting vulnerabilities in code and circumventing security measures. Hacking use ...
Security and Availability of Client Data
... Adobe obtains consumer background check reports for employment purposes. The specific nature and scope of the report that Adobe typically seeks includes inquiries regarding educational background; work history; court records, including criminal conviction record; and references obtained from profess ...
... Adobe obtains consumer background check reports for employment purposes. The specific nature and scope of the report that Adobe typically seeks includes inquiries regarding educational background; work history; court records, including criminal conviction record; and references obtained from profess ...
Principals of Information Security, Fourth Edition
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
Certification Exam Objectives: SY0-401
... • Risks associated with Cloud Computing and Virtualization • Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
... • Risks associated with Cloud Computing and Virtualization • Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
Chapter 2
... Upon completion of this material, you should be able to: Recognize that organizations have a business need for information security Understand that a successful information security program is the responsibility of both an organization’s general management and IT management Identify the threat ...
... Upon completion of this material, you should be able to: Recognize that organizations have a business need for information security Understand that a successful information security program is the responsibility of both an organization’s general management and IT management Identify the threat ...
Chapter 2
... Upon completion of this material, you should be able to: Recognize that organizations have a business need for information security Understand that a successful information security program is the responsibility of both an organization’s general management and IT management Identify the threat ...
... Upon completion of this material, you should be able to: Recognize that organizations have a business need for information security Understand that a successful information security program is the responsibility of both an organization’s general management and IT management Identify the threat ...
Firewalls: An Effective Solution for Internet Security
... which the connection has originated. By sending these packets to the destination host, the originating host's connection is dropped, and the attacker picks up the connection. Another Internet security threat is network snooping, in which attackers install programs that copy packets traversing networ ...
... which the connection has originated. By sending these packets to the destination host, the originating host's connection is dropped, and the attacker picks up the connection. Another Internet security threat is network snooping, in which attackers install programs that copy packets traversing networ ...
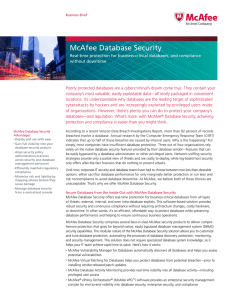
McAfee Database Security Solution Brief
... McAfee Database Activity Monitoring Protect business-critical databases in real time across all threat vectors—without downtime. McAfee Database Activity Monitoring provides real-time visibility into all database activity, including local privileged user access and sophisticated attacks from within ...
... McAfee Database Activity Monitoring Protect business-critical databases in real time across all threat vectors—without downtime. McAfee Database Activity Monitoring provides real-time visibility into all database activity, including local privileged user access and sophisticated attacks from within ...
Open resource
... Establish working relationship and rapport with State and local area CISOs in the region represented Coordinate with Federal personnel within region to integrate cyber security response and assessment perspectives (i.e., with PSAs, FEMA, Federal LE, etc) Coordinate cyber and communications incident ...
... Establish working relationship and rapport with State and local area CISOs in the region represented Coordinate with Federal personnel within region to integrate cyber security response and assessment perspectives (i.e., with PSAs, FEMA, Federal LE, etc) Coordinate cyber and communications incident ...
Speech Title Here
... How skilled must an attacker be to exploit the vulnerability? users A Affected How many users would be affected by a successful exploit? D Discoverability How likely is it that an attacker will know the vulnerability exists? ...
... How skilled must an attacker be to exploit the vulnerability? users A Affected How many users would be affected by a successful exploit? D Discoverability How likely is it that an attacker will know the vulnerability exists? ...
Principals of Information Security, Fourth Edition
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
SMALL FIRMS CYBERSECURITY GUIDANCE
... Study, research firm Ponemon Institute reported that smaller organizations incur a higher per capita cost than larger organizations ($1,564 and $371, respectively) due to cyber attacks.2 The SEC and FINRA have also begun examinations of cybersecurity preparedness among broker-dealers. As a result, i ...
... Study, research firm Ponemon Institute reported that smaller organizations incur a higher per capita cost than larger organizations ($1,564 and $371, respectively) due to cyber attacks.2 The SEC and FINRA have also begun examinations of cybersecurity preparedness among broker-dealers. As a result, i ...
AISE PoIS4E_PP_ch02_48
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
... • Upon completion of this material, you should be able to: – Demonstrate that organizations have a business need for information security – Explain why a successful information security program is the responsibility of both an organization’s general management and IT management ...
layered security.
... Information Technology – Reports to CFO Chief Security and Privacy Officer CSPO ...
... Information Technology – Reports to CFO Chief Security and Privacy Officer CSPO ...
Introduction
... 99 Compliance with applicable laws, regulations, and industry standards around the world, governing digital transactions and electronic signatures 99 Dedicated chief legal officer and chief technology officer that ensure DocuSign and our products align with the latest legal and technology trends 99 ...
... 99 Compliance with applicable laws, regulations, and industry standards around the world, governing digital transactions and electronic signatures 99 Dedicated chief legal officer and chief technology officer that ensure DocuSign and our products align with the latest legal and technology trends 99 ...
Airport security
Airport security refers to the techniques and methods used in protecting passengers, staff and aircraft which use the airports from accidental/malicious harm, crime and other threats.