HSARPA Cyber Security R&D
... and rigorous scientific methodologies for developing and testing next-generation defensive cyber security technology The goal is to create, operate, and support a researcher-andvendor-neutral experimental infrastructure that is open to a wide community of users and produce scientifically rigorous te ...
... and rigorous scientific methodologies for developing and testing next-generation defensive cyber security technology The goal is to create, operate, and support a researcher-andvendor-neutral experimental infrastructure that is open to a wide community of users and produce scientifically rigorous te ...
Chapter 5 Protection of Information Assets
... privacy risk and the options available for mitigating that risk ...
... privacy risk and the options available for mitigating that risk ...
Linux+ Guide to Linux Certification
... – Cracking (malicious hacking) causes system’s owner and users to question the validity of system’s data – Unethical use of technology is clearly the wrong thing to do ...
... – Cracking (malicious hacking) causes system’s owner and users to question the validity of system’s data – Unethical use of technology is clearly the wrong thing to do ...
Page PDF - Utah Valley University
... installation methods and troubleshooting, hardware device installation and management, storage management, disaster recovery planning and management. Aids the student in the development, understanding, and working knowledge of the Windows networking framework including peer-to-peer, workgroups, user ...
... installation methods and troubleshooting, hardware device installation and management, storage management, disaster recovery planning and management. Aids the student in the development, understanding, and working knowledge of the Windows networking framework including peer-to-peer, workgroups, user ...
Glossary of Terms, Abbreviations, and Acronyms
... Technique or technology (either software or hardware) for encrypting all stored data on a device (for example, a hard disk or flash drive). Alternatively, FileLevel Encryption or Column-Level Database Encryption is used to encrypt contents of specific files or columns. ...
... Technique or technology (either software or hardware) for encrypting all stored data on a device (for example, a hard disk or flash drive). Alternatively, FileLevel Encryption or Column-Level Database Encryption is used to encrypt contents of specific files or columns. ...
Security & Cryptography
... Sending Gateway determines a packet needs to be encrypted Sending Gateway opens an IKE session with the Receiving gateway- this step defines the IKE SA Diffie-Hellman key exchange uses hashing of a certificate or shared secret to authenticate each gateway, and sets up a public/private data exchange ...
... Sending Gateway determines a packet needs to be encrypted Sending Gateway opens an IKE session with the Receiving gateway- this step defines the IKE SA Diffie-Hellman key exchange uses hashing of a certificate or shared secret to authenticate each gateway, and sets up a public/private data exchange ...
II.I Selected Database Issues: 1
... Works by using private key to encrypt data that is transferred over SSL connection. (see http://developer.netscape.com/tech/security/ssl/howitworks.html ) Layered between application-level protocols such as HTTP and TCP/IP transport-level protocol. Thus, may be used for other application-level proto ...
... Works by using private key to encrypt data that is transferred over SSL connection. (see http://developer.netscape.com/tech/security/ssl/howitworks.html ) Layered between application-level protocols such as HTTP and TCP/IP transport-level protocol. Thus, may be used for other application-level proto ...
Authentication and Access Control
... • Can be achieved by both hardware and software means • Hardware key loggers are commercially available devices which come in three types: – Inline devices that are attached to the keyboard cable – Devices installed inside standard keyboards – Keyboards that contain the key logger already built-in ...
... • Can be achieved by both hardware and software means • Hardware key loggers are commercially available devices which come in three types: – Inline devices that are attached to the keyboard cable – Devices installed inside standard keyboards – Keyboards that contain the key logger already built-in ...
Security Analysis of a Single Sign
... privacy in the scheme as a malicious service provider is able to recover the credential of a legal user. The other attack, an “impersonation attack without credentials,” demonstrates how an outside attacker may be able to freely make use of resources and services offered by service providers, since ...
... privacy in the scheme as a malicious service provider is able to recover the credential of a legal user. The other attack, an “impersonation attack without credentials,” demonstrates how an outside attacker may be able to freely make use of resources and services offered by service providers, since ...
OWASP`s Ten Most Critical Web Application Security Vulnerabilities
... Be extremely careful storing keys, certs, and passwords Rethink whether you need to store the information Don’t store user passwords – use a hash like SHA-256 ...
... Be extremely careful storing keys, certs, and passwords Rethink whether you need to store the information Don’t store user passwords – use a hash like SHA-256 ...
PowerPoint
... What are example types of application programs What do operating systems do How do compilers work The relationship between hardware and software ...
... What are example types of application programs What do operating systems do How do compilers work The relationship between hardware and software ...
Internet Security
... A dedicated gateway machine with special security precautions on it, used to service outside network, especially Internet connections and dial-in lines. The idea is to protect a cluster of more loosely administered machines hidden behind it... ...
... A dedicated gateway machine with special security precautions on it, used to service outside network, especially Internet connections and dial-in lines. The idea is to protect a cluster of more loosely administered machines hidden behind it... ...
Sun Microsystems
... Microsystems, Inc. to its position as a leading provider of industrial-strength hardware, software and services that make the Net work. Sun can be found in more than 100 countries and on the World Wide Web at http://sun.com. BUSINESS CHALLENGE The virtual enterprise is quickly becoming a reality as ...
... Microsystems, Inc. to its position as a leading provider of industrial-strength hardware, software and services that make the Net work. Sun can be found in more than 100 countries and on the World Wide Web at http://sun.com. BUSINESS CHALLENGE The virtual enterprise is quickly becoming a reality as ...
Auditing Corporate Information Security
... Reduce your stress levels Most likely, it’s not your first audit experience • If you are the CISO, then you have already been through an audit. • Your audit results should get better with time. • If there were recommendations on your last audit, make sure you have remedied the exceptions • Try to ...
... Reduce your stress levels Most likely, it’s not your first audit experience • If you are the CISO, then you have already been through an audit. • Your audit results should get better with time. • If there were recommendations on your last audit, make sure you have remedied the exceptions • Try to ...
Mainline How Secure Are You K12 Security Preseo Rev 1
... protection measure with respect to any of its computers with Internet access that protects against access through such computers to visual depictions that are obscene, child pornography, or harmful to minors..." Such a technology protection measure must be employed "during any use of such computers ...
... protection measure with respect to any of its computers with Internet access that protects against access through such computers to visual depictions that are obscene, child pornography, or harmful to minors..." Such a technology protection measure must be employed "during any use of such computers ...
Firewalls
... How to configure Windows Firewall • Although blocking unsolicited requests is good… • Sometimes you may want to allow access to your computer. • Examples are Instant Messengers, and some video games may require that other computers connect to your computer. ...
... How to configure Windows Firewall • Although blocking unsolicited requests is good… • Sometimes you may want to allow access to your computer. • Examples are Instant Messengers, and some video games may require that other computers connect to your computer. ...
EE-EmbeddedOperatingSystems-II
... Ref: http://developer.android.com/reference/org/apache/http/package-summary.html http://developer.android.com/reference/javax/net/ssl/package-summary.html http://www.ibm.com/developerworks/opensource/library/x-android/index.html ...
... Ref: http://developer.android.com/reference/org/apache/http/package-summary.html http://developer.android.com/reference/javax/net/ssl/package-summary.html http://www.ibm.com/developerworks/opensource/library/x-android/index.html ...
Systeemanalyse in Ontwerpprojecten
... used (old software that has not being patched): see e.g. www.nessus.org • Packet sniffers (or protocol analyzers) look at the content of incoming/outgoing IP-packets: see e.g. www.ethereal.com, e.g. look for passwords May 5, 2017 ...
... used (old software that has not being patched): see e.g. www.nessus.org • Packet sniffers (or protocol analyzers) look at the content of incoming/outgoing IP-packets: see e.g. www.ethereal.com, e.g. look for passwords May 5, 2017 ...
Chapter 3 - Faculty Personal Homepage
... Objectives (continued) • What are some characteristics of common computer criminals, including their objectives, available resources, willingness to accept risk, and frequency of attack? • What are the key elements of a multilayer process for managing security vulnerabilities, based on the concept ...
... Objectives (continued) • What are some characteristics of common computer criminals, including their objectives, available resources, willingness to accept risk, and frequency of attack? • What are the key elements of a multilayer process for managing security vulnerabilities, based on the concept ...
The Taidoor Campaign: An In-Depth Analysis
... Figure 1. File properties of the .TMP of the malicious executable file The main purpose of the dropped binary file is to install an RC4-encrypted executable file, specifically in the .data segment, in the memory space of a known Windows Service Process. If the registry, HKLM\SOFTWARE\McAfee, is foun ...
... Figure 1. File properties of the .TMP of the malicious executable file The main purpose of the dropped binary file is to install an RC4-encrypted executable file, specifically in the .data segment, in the memory space of a known Windows Service Process. If the registry, HKLM\SOFTWARE\McAfee, is foun ...
Security - Ingate Systems
... • Authenticating information that allows voice access to Call Control and UC Applications • VoIP Security covers a variety of computer networks, both public and private, that are used in everyday jobs conducting transactions and communications among businesses, government agencies and individuals. ...
... • Authenticating information that allows voice access to Call Control and UC Applications • VoIP Security covers a variety of computer networks, both public and private, that are used in everyday jobs conducting transactions and communications among businesses, government agencies and individuals. ...
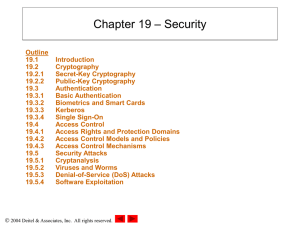
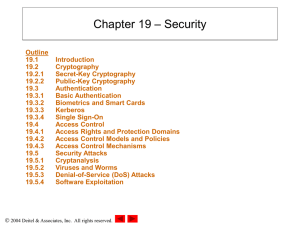
Chapter 19: Security
... code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access rights as the application it attacked – Depending on the user and application, the attacker may gain access to the entire system ...
... code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access rights as the application it attacked – Depending on the user and application, the attacker may gain access to the entire system ...
Important Concepts.
... Assurance that data received are exactly as sent by an authorized entity. (i.e., contain no modification, insertion, deletion, or replay). Data integrity can be maintained through the use of various error checking methods and validation procedures. Data integrity and data security are related te ...
... Assurance that data received are exactly as sent by an authorized entity. (i.e., contain no modification, insertion, deletion, or replay). Data integrity can be maintained through the use of various error checking methods and validation procedures. Data integrity and data security are related te ...
Chapter 19: Security - Murray State University
... code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access rights as the application it attacked – Depending on the user and application, the attacker may gain access to the entire system ...
... code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access rights as the application it attacked – Depending on the user and application, the attacker may gain access to the entire system ...
Next-Generation Secure Computing Base
The Next-Generation Secure Computing Base (NGSCB) (codenamed Palladium and also known as Trusted Windows) is a cancelled software architecture designed by Microsoft which aimed to provide users of the Windows operating system with better privacy, security, and system integrity. NGSCB was the result of years of research and development within Microsoft to create a secure computing solution that equaled the security of closed architecture platforms, such as set-top boxes, while simultaneously preserving the backward compatibility, openness, and flexibility of the Windows operating system. The primary stated objective with NGSCB was to ""protect software from software.""Part of the Trustworthy Computing initiative when unveiled in 2002, NGSCB was expected to be integrated with the Windows Vista operating system, then known by its codename ""Longhorn."" NGSCB relied on hardware designed by members of the Trusted Computing Group to produce a parallel operation environment hosted by a new kernel called the ""Nexus"" that existed alongside Windows and provide new applications with features such as hardware-based process isolation, data encryption based on integrity measurements, authentication of a local or remote machine or software configuration, and encrypted paths for user authentication and graphics output. NGSCB would also facilitate the creation and distribution of rights management policies pertaining to the use of information.The technology was the subject of much controversy during its development, with critics contending that it could be used to impose restrictions on users, enforce vendor lock-in, and undermine fair use rights and open-source software. NGSCB was first demonstrated by Microsoft in 2003 at the Windows Hardware Engineering Conference before undergoing a revision in 2004 that would enable applications written prior to its development to benefit from its functionality. In 2005, reports stated that Microsoft would scale back its plans so that the company could ship its Windows Vista operating system by its target date of 2006. Development of NGSCB spanned almost a decade before its cancellation, one of the lengthiest development periods of a feature intended for the operating system.NGSCB differed from the technologies that Microsoft billed as pillars of Windows Vista during its development—Windows Presentation Foundation, Windows Communication Foundation, and WinFS—in that it was not built upon and did not prioritize .NET managed code during its development. While the technology has not fully materialized, aspects of NGSCB have emerged in Microsoft's BitLocker full disk encryption feature, which can optionally use the Trusted Platform Module to validate the integrity of boot and system files prior to operating system startup; the Measured Boot feature in Windows 8, the certificate attestation features in Windows 8.1, and the Device Guard feature of Windows 10.