Top Five DNS Security Attack Risks and How to Avoid Them
... Engineering Task Force (IETF) specifications for securing certain kinds of information provided by the Domain Name System (DNS) as used on Internet Protocol (IP) networks. It is a set of extensions to DNS which provide origin authentication of DNS data, authenticated denial of existence, and data in ...
... Engineering Task Force (IETF) specifications for securing certain kinds of information provided by the Domain Name System (DNS) as used on Internet Protocol (IP) networks. It is a set of extensions to DNS which provide origin authentication of DNS data, authenticated denial of existence, and data in ...
Chapter 3
... by a virus or by adware, but a scan doesn't reveal anything. The solution might lie in a rootkit. A Rootkit is a technology which hides itself and other programs and prevents their detection. ...
... by a virus or by adware, but a scan doesn't reveal anything. The solution might lie in a rootkit. A Rootkit is a technology which hides itself and other programs and prevents their detection. ...
Iris Scanning.pdf
... Identifying individuals using their distinct physical or behavior characteristics. ...
... Identifying individuals using their distinct physical or behavior characteristics. ...
Devireddy
... TKIP resolves the key reuse in WEP by providing 128 bit “temporal key” in a dynamic way for securing data. It uses the same RC4 algorithm as WEP does and it is not considered as a long term solution. ...
... TKIP resolves the key reuse in WEP by providing 128 bit “temporal key” in a dynamic way for securing data. It uses the same RC4 algorithm as WEP does and it is not considered as a long term solution. ...
Apply encryption to network and system security
... unauthorized people or systems. Encryption involves scrambling data so that it needs to be unscrambled, or decrypted, to be read. Encryption can be applied to data in storage (file systems, media, etc) or in transit via network or Internet connections. Encryption can be useful to achieve appropriate ...
... unauthorized people or systems. Encryption involves scrambling data so that it needs to be unscrambled, or decrypted, to be read. Encryption can be applied to data in storage (file systems, media, etc) or in transit via network or Internet connections. Encryption can be useful to achieve appropriate ...
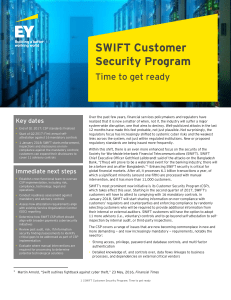
SWIFT Customer Security Program
... between itself and its customers, including on suspected fraudulent activity, effective preventive and detective measures, and leading practices and innovations on cyber defenses. It will maintain an up-to-date malware inventory and curate an information sharing community. Enhance SWIFT-related tool ...
... between itself and its customers, including on suspected fraudulent activity, effective preventive and detective measures, and leading practices and innovations on cyber defenses. It will maintain an up-to-date malware inventory and curate an information sharing community. Enhance SWIFT-related tool ...
PCI Compliance Without Compensating Controls – How to Take Ulf Mattsson
... • Meet the intent and rigor of the original PCI DSS requirement. • Provide a similar level of defense as the original PCI DSS requirement, such that the compensating control sufficiently offsets the risk that the original PCI DSS requirement was designed to defend against. • Be “above and beyond” ot ...
... • Meet the intent and rigor of the original PCI DSS requirement. • Provide a similar level of defense as the original PCI DSS requirement, such that the compensating control sufficiently offsets the risk that the original PCI DSS requirement was designed to defend against. • Be “above and beyond” ot ...
GSI Credential Management with MyProxy
... Emerging NCSA Security R&D NSF CyberSecurity Summit September 28th, 2004 ...
... Emerging NCSA Security R&D NSF CyberSecurity Summit September 28th, 2004 ...
CISCO Secure Intrusion Detection System
... 1. Alarm Display and Logging When a sensor detects an attack, it sends an alarm to the event management platform. On the event management platform, a graphical user interface (GUI) displays these alarms in real time, color-coding each alarm based on its severity. This display provides a quick indic ...
... 1. Alarm Display and Logging When a sensor detects an attack, it sends an alarm to the event management platform. On the event management platform, a graphical user interface (GUI) displays these alarms in real time, color-coding each alarm based on its severity. This display provides a quick indic ...
Build a Metadata Driven ETL Platform by
... tasks. While SQL Server Business Intelligence Development Studio is very effective for designing individual and simple ETL packages, for large data warehousing systems with hundreds of packages, it is very labor intensive and error prone to develop, test, deploy, and maintain a large number of SSIS ...
... tasks. While SQL Server Business Intelligence Development Studio is very effective for designing individual and simple ETL packages, for large data warehousing systems with hundreds of packages, it is very labor intensive and error prone to develop, test, deploy, and maintain a large number of SSIS ...
white paper - Nuage Networks
... NSG supports a non-privileged account. Default password changed after first login. Password login can be disabled and SSH authentication used instead. In addition, access can be restricted for a specific set of source IP addresses. ...
... NSG supports a non-privileged account. Default password changed after first login. Password login can be disabled and SSH authentication used instead. In addition, access can be restricted for a specific set of source IP addresses. ...
Firewall Toolkit (FWTK)
... It was first released in October of 1993. The key technology of FWTK was used to create the first version of the Gauntlet firewall. FWTK is still available at http://www.fwtk.org, but has not been updated for many years. ...
... It was first released in October of 1993. The key technology of FWTK was used to create the first version of the Gauntlet firewall. FWTK is still available at http://www.fwtk.org, but has not been updated for many years. ...
Virtualization - WordPress.com
... issues when it comes to virtualization. Certain privilegedmode instructions do not trap, and can return different results based upon the mode. For example, the x86 STR instruction retrieves the security state, but the value returned is based upon the particular requester's privilege level. This is p ...
... issues when it comes to virtualization. Certain privilegedmode instructions do not trap, and can return different results based upon the mode. For example, the x86 STR instruction retrieves the security state, but the value returned is based upon the particular requester's privilege level. This is p ...
Virtualization
... issues when it comes to virtualization. Certain privilegedmode instructions do not trap, and can return different results based upon the mode. For example, the x86 STR instruction retrieves the security state, but the value returned is based upon the particular requester's privilege level. This is p ...
... issues when it comes to virtualization. Certain privilegedmode instructions do not trap, and can return different results based upon the mode. For example, the x86 STR instruction retrieves the security state, but the value returned is based upon the particular requester's privilege level. This is p ...
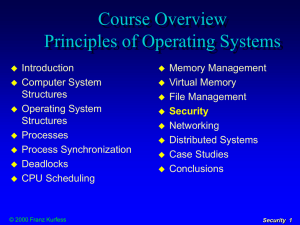
Security
... processing system used by the bank to be prepared for unpleasant situations at work, she leaves an entry point into the system she’s fired for security violations after she’s fired, she gains access via modem, transfers a large amount of money to an account on a Caribbean island, and erases al ...
... processing system used by the bank to be prepared for unpleasant situations at work, she leaves an entry point into the system she’s fired for security violations after she’s fired, she gains access via modem, transfers a large amount of money to an account on a Caribbean island, and erases al ...
Chapter 4
... MIT’s Athena project provides centralized private-key third-party authentication in a distributed network ...
... MIT’s Athena project provides centralized private-key third-party authentication in a distributed network ...
Cryptanalysis of Stream Cipher
... 128-bit state information The overall differential probability of the forgery attack against AEGIS increases But the differential probability that a difference propagates through 5 AES rounds is not affected ...
... 128-bit state information The overall differential probability of the forgery attack against AEGIS increases But the differential probability that a difference propagates through 5 AES rounds is not affected ...
PCI Self-Assessment Questionnaire
... completion or compliance with the questionnaire will prevent security breaches or losses, and disclaims any responsibility or liability for any security breaches or losses incurred, whether the recommendation of Self-Assessment Questionnaire has been implemented or not. ...
... completion or compliance with the questionnaire will prevent security breaches or losses, and disclaims any responsibility or liability for any security breaches or losses incurred, whether the recommendation of Self-Assessment Questionnaire has been implemented or not. ...
Control Panel Security
... Securing an enclosure may be as simple as replacing a standard key hole with inserts that have alternative key shapes, such as square bits, triangular holes, and Daimler or Fiat shapes. Changing the shape of the key prevents entry with standard keys and tools, forcing the user to know what lock is i ...
... Securing an enclosure may be as simple as replacing a standard key hole with inserts that have alternative key shapes, such as square bits, triangular holes, and Daimler or Fiat shapes. Changing the shape of the key prevents entry with standard keys and tools, forcing the user to know what lock is i ...
Joshua White - Everis Inc.
... Joshua White Director of CyOON Research and Development “Cyber Operations for Optical Networks” [email protected] Everis Inc http://www.EverisInc.com ...
... Joshua White Director of CyOON Research and Development “Cyber Operations for Optical Networks” [email protected] Everis Inc http://www.EverisInc.com ...
How to Detect Zero-Day Malware And Limit Its Impact
... administrators to potential problems and takes action to isolate the computer, says Steven Sprague, CEO of software vendor Wave Systems. A microchip installed on the motherboard, TPM can store encryption keys, password information and specific configuration information. ...
... administrators to potential problems and takes action to isolate the computer, says Steven Sprague, CEO of software vendor Wave Systems. A microchip installed on the motherboard, TPM can store encryption keys, password information and specific configuration information. ...
lesson05 - Seneca - School of Information & Communications
... • By default, two NPS Network Policies are preconfigured in Windows Server 2008. • The first default policy is Connections To Microsoft Routing And Remote Access Server, which is configured to match every remote access connection to the Routing and Remote Access service. • When Routing and Remote Ac ...
... • By default, two NPS Network Policies are preconfigured in Windows Server 2008. • The first default policy is Connections To Microsoft Routing And Remote Access Server, which is configured to match every remote access connection to the Routing and Remote Access service. • When Routing and Remote Ac ...
256 Bit Key — Is It Big Enough?
... able to combine proven and robust cryptography with low cost and ease of use in the typical microprocessor-based application. Virtually all security devices contain some sort of secret along with a cryptographic processing element. Generally, the secret can never be read from the device; rather, the ...
... able to combine proven and robust cryptography with low cost and ease of use in the typical microprocessor-based application. Virtually all security devices contain some sort of secret along with a cryptographic processing element. Generally, the secret can never be read from the device; rather, the ...
SecuROM™ Disc Check
... casual copies, digital cloning is the most widely used piracy method. Therefore, it represents the biggest threat to your business. SecuROM™ ensures only legitimate users with an original disc can use your software. SecuROM™ protected applications can only be launched with an original disc. Emulatio ...
... casual copies, digital cloning is the most widely used piracy method. Therefore, it represents the biggest threat to your business. SecuROM™ ensures only legitimate users with an original disc can use your software. SecuROM™ protected applications can only be launched with an original disc. Emulatio ...
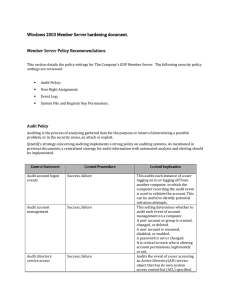
Server hardening - Cisco Security Solutions
... Audits each instance of a user logging on to, logging off from, or making a network connection to the computer recording the audit event. Useful for forensics purposes. Audits the event of a user accessing an object that has its own system ACLs specified. The object also requires auditing settings t ...
... Audits each instance of a user logging on to, logging off from, or making a network connection to the computer recording the audit event. Useful for forensics purposes. Audits the event of a user accessing an object that has its own system ACLs specified. The object also requires auditing settings t ...
Next-Generation Secure Computing Base
The Next-Generation Secure Computing Base (NGSCB) (codenamed Palladium and also known as Trusted Windows) is a cancelled software architecture designed by Microsoft which aimed to provide users of the Windows operating system with better privacy, security, and system integrity. NGSCB was the result of years of research and development within Microsoft to create a secure computing solution that equaled the security of closed architecture platforms, such as set-top boxes, while simultaneously preserving the backward compatibility, openness, and flexibility of the Windows operating system. The primary stated objective with NGSCB was to ""protect software from software.""Part of the Trustworthy Computing initiative when unveiled in 2002, NGSCB was expected to be integrated with the Windows Vista operating system, then known by its codename ""Longhorn."" NGSCB relied on hardware designed by members of the Trusted Computing Group to produce a parallel operation environment hosted by a new kernel called the ""Nexus"" that existed alongside Windows and provide new applications with features such as hardware-based process isolation, data encryption based on integrity measurements, authentication of a local or remote machine or software configuration, and encrypted paths for user authentication and graphics output. NGSCB would also facilitate the creation and distribution of rights management policies pertaining to the use of information.The technology was the subject of much controversy during its development, with critics contending that it could be used to impose restrictions on users, enforce vendor lock-in, and undermine fair use rights and open-source software. NGSCB was first demonstrated by Microsoft in 2003 at the Windows Hardware Engineering Conference before undergoing a revision in 2004 that would enable applications written prior to its development to benefit from its functionality. In 2005, reports stated that Microsoft would scale back its plans so that the company could ship its Windows Vista operating system by its target date of 2006. Development of NGSCB spanned almost a decade before its cancellation, one of the lengthiest development periods of a feature intended for the operating system.NGSCB differed from the technologies that Microsoft billed as pillars of Windows Vista during its development—Windows Presentation Foundation, Windows Communication Foundation, and WinFS—in that it was not built upon and did not prioritize .NET managed code during its development. While the technology has not fully materialized, aspects of NGSCB have emerged in Microsoft's BitLocker full disk encryption feature, which can optionally use the Trusted Platform Module to validate the integrity of boot and system files prior to operating system startup; the Measured Boot feature in Windows 8, the certificate attestation features in Windows 8.1, and the Device Guard feature of Windows 10.