security - Binus Repository
... security products on the market then you is less likely to suffer a security breach. • The Plate Spinner, or, too much to manage. The key to effective security is vision, the ability to monitor all areas simultaneously, set up alerts to irregular activity. • The Agoraphobic, or, too paranoid about w ...
... security products on the market then you is less likely to suffer a security breach. • The Plate Spinner, or, too much to manage. The key to effective security is vision, the ability to monitor all areas simultaneously, set up alerts to irregular activity. • The Agoraphobic, or, too paranoid about w ...
Ethics in Information Technology
... – Cracking is a form of hacking – Clearly criminal activity ...
... – Cracking is a form of hacking – Clearly criminal activity ...
the transitivity of trust problem in the interaction of android
... becoming increasingly common with the availability of affordable devices and data plans. Increasingly, the smart phones’ features are provided by focused applications that users can easily install from application market places. On the other hand, with tens of thousands of applications available, th ...
... becoming increasingly common with the availability of affordable devices and data plans. Increasingly, the smart phones’ features are provided by focused applications that users can easily install from application market places. On the other hand, with tens of thousands of applications available, th ...
Read the Datasheet
... As part of the VMware family of products, vFabric Hyperic provides best-in-class performance monitoring of applications running in virtualized environments. With its deep VMware vCenter™ integration, Hyperic monitors your entire application infrastructure inventory, from code components down to VMwa ...
... As part of the VMware family of products, vFabric Hyperic provides best-in-class performance monitoring of applications running in virtualized environments. With its deep VMware vCenter™ integration, Hyperic monitors your entire application infrastructure inventory, from code components down to VMwa ...
Combat a range of potential data leakage threats with these ultra
... Threat: Microprocessor malfunction or unanticipated software bugs causing data to flow between ports. Solution: Unidirectional data flow is enforced by hardware “data diodes” so data isolation doesn’t rely on software integrity. Threat: Malicious modification of microprocessor software causing data ...
... Threat: Microprocessor malfunction or unanticipated software bugs causing data to flow between ports. Solution: Unidirectional data flow is enforced by hardware “data diodes” so data isolation doesn’t rely on software integrity. Threat: Malicious modification of microprocessor software causing data ...
William Stallings, Cryptography and Network Security 3/e
... Consists of two systems: a packet-filtering router and a bastion host. The router is configured so that For traffic from the Internet, only IP packets destined for the bastion host are allowed in. For the traffic from the internal network, only IP packets from the bastion host are allowed to out. ...
... Consists of two systems: a packet-filtering router and a bastion host. The router is configured so that For traffic from the Internet, only IP packets destined for the bastion host are allowed in. For the traffic from the internal network, only IP packets from the bastion host are allowed to out. ...
CounterACT: Powerful, Automated Network Protection
... to say: “our network is perfectly safe – CounterACT’s automatic zero-day threat prevention provided us with the 24/7/365 protection we have come to expect and rely on!” Conficker (aka Downup, Downadup and Kido) is an aggressive worm that targets Windows-based systems. It’s been estimated that the bu ...
... to say: “our network is perfectly safe – CounterACT’s automatic zero-day threat prevention provided us with the 24/7/365 protection we have come to expect and rely on!” Conficker (aka Downup, Downadup and Kido) is an aggressive worm that targets Windows-based systems. It’s been estimated that the bu ...
Data Encryption Standard - gozips.uakron.edu
... From whom should data be protected? What costs are associated with security being breached and ...
... From whom should data be protected? What costs are associated with security being breached and ...
Lecture1
... - Difficult to be detected by the unsuspecting human 0 Steganalysis is about developing techniques that can analyze text, images, video and detect hidden messages - May use data mining techniques to detect hidden patters 0 Steganograophy makes the task of the Cyber crime expert difficult as he/she a ...
... - Difficult to be detected by the unsuspecting human 0 Steganalysis is about developing techniques that can analyze text, images, video and detect hidden messages - May use data mining techniques to detect hidden patters 0 Steganograophy makes the task of the Cyber crime expert difficult as he/she a ...
Multimedia Application Production
... Something you know Password or personal identification number (PIN) Something you have ID cards, smartcards, badges, keys, Something about you Unique physical characteristics such as fingerprints ...
... Something you know Password or personal identification number (PIN) Something you have ID cards, smartcards, badges, keys, Something about you Unique physical characteristics such as fingerprints ...
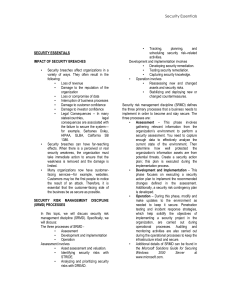
IMPACT OF SECURITY BREACHES
... rooms should be locked. Access to server rooms should be strictly controlled and logged. Some of the access control mechanisms that can be used include badges and biometrics. Access should be prearranged and authorized by a senior member of the staff. If dedicated server rooms do not exist, servers ...
... rooms should be locked. Access to server rooms should be strictly controlled and logged. Some of the access control mechanisms that can be used include badges and biometrics. Access should be prearranged and authorized by a senior member of the staff. If dedicated server rooms do not exist, servers ...
SAQ D Compliance Scott St. Aubin Senior Security Consultant QSA, CISM, CISSP
... • Wireless – Strong Encryption • WPA/WPA2 • NOT WEP (prohibited after June 30th) ...
... • Wireless – Strong Encryption • WPA/WPA2 • NOT WEP (prohibited after June 30th) ...
SRA Customized Web Portal | Secure Remote Access | SonicWALL
... Access policy management The personalized portal is a key element in controlling granular access for each end user. The policies that are created and enforced by the network administrator are reflected in the personalized portal, which reveals to the end user access to only those resources which the ...
... Access policy management The personalized portal is a key element in controlling granular access for each end user. The policies that are created and enforced by the network administrator are reflected in the personalized portal, which reveals to the end user access to only those resources which the ...
WHAT IS EC SECURITY? - Joseph H. Schuessler, PhD
... Pages created deliberately to trick the search engine into offering inappropriate, redundant, or poor-quality ...
... Pages created deliberately to trick the search engine into offering inappropriate, redundant, or poor-quality ...
Confidentiality
... The five main phases of an information security plan are as follows; 2.1 Inspection - The most important tasks in developing an Information Security Plan are identifying the key corporate functions, the capabilities they need, when they need those capabilities, and how they interact with other funct ...
... The five main phases of an information security plan are as follows; 2.1 Inspection - The most important tasks in developing an Information Security Plan are identifying the key corporate functions, the capabilities they need, when they need those capabilities, and how they interact with other funct ...
Slide 1
... • Necessary for moving data into MLS Applications • Transfers data from System High to Multi-Level Environment • Tactical Browser ...
... • Necessary for moving data into MLS Applications • Transfers data from System High to Multi-Level Environment • Tactical Browser ...
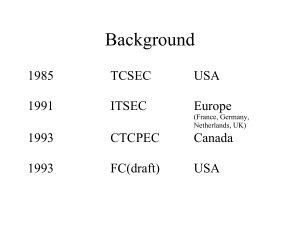
Common Criteria
... DefinitionsTarget of Evaluation (TOE) — An IT product or system and its associated administrator and user guidance documentation that is the subject of an evaluation. ...
... DefinitionsTarget of Evaluation (TOE) — An IT product or system and its associated administrator and user guidance documentation that is the subject of an evaluation. ...
Top 100 Network Security Tools
... connections. It is designed to be a reliable back-end tool that can be used directly or easily driven by other programs and scripts. At the same time, it is a feature-rich network debugging and exploration tool, since it can create almost any kind of connection you would need, including port binding ...
... connections. It is designed to be a reliable back-end tool that can be used directly or easily driven by other programs and scripts. At the same time, it is a feature-rich network debugging and exploration tool, since it can create almost any kind of connection you would need, including port binding ...
Windows XP Kernel Crash Analysis
... While examining NFS data availability in Network Appliance’s NetApp filers, Lancaster and Rowe attributed power failures and software failures as the largest contributors to downtime; operator failure contributions were negligible [LR01]. Thakur and Iyer examined failures in a network of 69 SunOS wo ...
... While examining NFS data availability in Network Appliance’s NetApp filers, Lancaster and Rowe attributed power failures and software failures as the largest contributors to downtime; operator failure contributions were negligible [LR01]. Thakur and Iyer examined failures in a network of 69 SunOS wo ...
Question Info
... 26. Your friend uses instant messaging to chat with friends. He wants to ensure that his instant messaging transactions are secure. Which of the following guidelines will you suggest? A. B. C. D. ...
... 26. Your friend uses instant messaging to chat with friends. He wants to ensure that his instant messaging transactions are secure. Which of the following guidelines will you suggest? A. B. C. D. ...
Protocol Overview
... • Kerberos is a network authentication protocol. It is designed to provide strong authentication for client/server applications by using secret-key cryptography. • Before a network connection is opened between two entities, Kerberos establishes a shared secret key through a Ticket Granting Server (T ...
... • Kerberos is a network authentication protocol. It is designed to provide strong authentication for client/server applications by using secret-key cryptography. • Before a network connection is opened between two entities, Kerberos establishes a shared secret key through a Ticket Granting Server (T ...
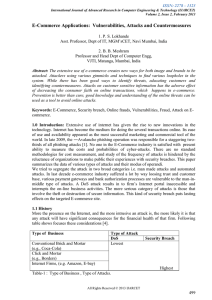
Survey of online attacks on E-Commerce sites
... Web based attacks are considered to be the greatest threat to the online business as it is related to confidentiality, availability, and integrity. The motive behind e-commerce attack is significantly different then other attacks; Web based attacks focus on an application itself and functions on lay ...
... Web based attacks are considered to be the greatest threat to the online business as it is related to confidentiality, availability, and integrity. The motive behind e-commerce attack is significantly different then other attacks; Web based attacks focus on an application itself and functions on lay ...
03-WAS Common Threats - Professional Data Management
... A repeatable hardening process that makes it fast and easy to deploy another environment that is properly locked down. Development, QA, and production environments should all be configured identically. This process should be automated to minimize the effort required to setup a new secure environment ...
... A repeatable hardening process that makes it fast and easy to deploy another environment that is properly locked down. Development, QA, and production environments should all be configured identically. This process should be automated to minimize the effort required to setup a new secure environment ...
Next-Generation Secure Computing Base
The Next-Generation Secure Computing Base (NGSCB) (codenamed Palladium and also known as Trusted Windows) is a cancelled software architecture designed by Microsoft which aimed to provide users of the Windows operating system with better privacy, security, and system integrity. NGSCB was the result of years of research and development within Microsoft to create a secure computing solution that equaled the security of closed architecture platforms, such as set-top boxes, while simultaneously preserving the backward compatibility, openness, and flexibility of the Windows operating system. The primary stated objective with NGSCB was to ""protect software from software.""Part of the Trustworthy Computing initiative when unveiled in 2002, NGSCB was expected to be integrated with the Windows Vista operating system, then known by its codename ""Longhorn."" NGSCB relied on hardware designed by members of the Trusted Computing Group to produce a parallel operation environment hosted by a new kernel called the ""Nexus"" that existed alongside Windows and provide new applications with features such as hardware-based process isolation, data encryption based on integrity measurements, authentication of a local or remote machine or software configuration, and encrypted paths for user authentication and graphics output. NGSCB would also facilitate the creation and distribution of rights management policies pertaining to the use of information.The technology was the subject of much controversy during its development, with critics contending that it could be used to impose restrictions on users, enforce vendor lock-in, and undermine fair use rights and open-source software. NGSCB was first demonstrated by Microsoft in 2003 at the Windows Hardware Engineering Conference before undergoing a revision in 2004 that would enable applications written prior to its development to benefit from its functionality. In 2005, reports stated that Microsoft would scale back its plans so that the company could ship its Windows Vista operating system by its target date of 2006. Development of NGSCB spanned almost a decade before its cancellation, one of the lengthiest development periods of a feature intended for the operating system.NGSCB differed from the technologies that Microsoft billed as pillars of Windows Vista during its development—Windows Presentation Foundation, Windows Communication Foundation, and WinFS—in that it was not built upon and did not prioritize .NET managed code during its development. While the technology has not fully materialized, aspects of NGSCB have emerged in Microsoft's BitLocker full disk encryption feature, which can optionally use the Trusted Platform Module to validate the integrity of boot and system files prior to operating system startup; the Measured Boot feature in Windows 8, the certificate attestation features in Windows 8.1, and the Device Guard feature of Windows 10.