Chapter 6 slides, Computer Networking, 3rd edition
... host: must associate with an AP scans channels, listening for beacon frames containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication [Chapter 8] will typically run DHCP to get IP address in AP’s ...
... host: must associate with an AP scans channels, listening for beacon frames containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication [Chapter 8] will typically run DHCP to get IP address in AP’s ...
computer security - GH Raisoni Polytechnic, Nagpur
... A message is to be transferred from one party to another via Internet. Sender & receiver are principals of transaction and must cooperate for exchange to take place. An information channel is established by defining a route through Internet from source to destination with the help of communication p ...
... A message is to be transferred from one party to another via Internet. Sender & receiver are principals of transaction and must cooperate for exchange to take place. An information channel is established by defining a route through Internet from source to destination with the help of communication p ...
Centre for Defence Communications and Information Networking
... Data Information Link (TADIL) technologies and the prediction of Quality of Service in both link and networked environments. ...
... Data Information Link (TADIL) technologies and the prediction of Quality of Service in both link and networked environments. ...
Chapter 1. Introduction to Data Communications
... • The limits of what users have access to on a network are determined by user profiles assigned to each user account by the net manager. • The profile specifies access details such as what data and network resources a user can access and the type of access (e.g., read, write, create, delete). • Most ...
... • The limits of what users have access to on a network are determined by user profiles assigned to each user account by the net manager. • The profile specifies access details such as what data and network resources a user can access and the type of access (e.g., read, write, create, delete). • Most ...
Chapter 5
... Domain Name System • Convert user-friendly name into their IP address • domain name: any registered, valid name with ICANN • resolving the domain name: the process of changing a name into its IP address – ICANN has 13 computer as root servers for maintaining a list of IP addresses of servers to res ...
... Domain Name System • Convert user-friendly name into their IP address • domain name: any registered, valid name with ICANN • resolving the domain name: the process of changing a name into its IP address – ICANN has 13 computer as root servers for maintaining a list of IP addresses of servers to res ...
Network Security
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
Interceptor™ Optical Network Security System Design Guide
... Uncontrolled access areas (UCAs) are any areas where there are no physical access controls, allowing free and unrestricted access to the immediate population or to the general public. A PDS is always required for any unencrypted classified network deployments in or through a UCA. Frequently, an orga ...
... Uncontrolled access areas (UCAs) are any areas where there are no physical access controls, allowing free and unrestricted access to the immediate population or to the general public. A PDS is always required for any unencrypted classified network deployments in or through a UCA. Frequently, an orga ...
Chapter 08
... Use the PGP and GPG data-encryption utilities Describe different ways in which cryptography is applied to make computer systems more secure ...
... Use the PGP and GPG data-encryption utilities Describe different ways in which cryptography is applied to make computer systems more secure ...
mod_8_study_guide_without_answers
... others are accessing at the same time? Activity: Advantages and Disadvantages of Networking 8.2 Describe Types of Networks 8.2.1 Describe a LAN ...
... others are accessing at the same time? Activity: Advantages and Disadvantages of Networking 8.2 Describe Types of Networks 8.2.1 Describe a LAN ...
Objectives Network Structure Network Structure Network Structure
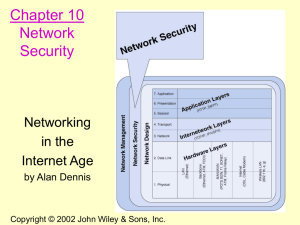
... Using a layered model helps in the design of complex multi-use, multi-vendor networks Benefits include – assists in protocol design – fosters competition between vendors – changes in one layer do not affect other layers – provides a common language There are two important models – ISO Referenc ...
... Using a layered model helps in the design of complex multi-use, multi-vendor networks Benefits include – assists in protocol design – fosters competition between vendors – changes in one layer do not affect other layers – provides a common language There are two important models – ISO Referenc ...
Quality of Service Guarantee on 802.11 Networks
... token maintenance protocol there is no single point of failure in the network and hosts can join and leave the the ring at any time. This was the scheme used in [1] and it worked well in the context of shared Ethernet segments, where all hosts can communicate with each other directly. In the context ...
... token maintenance protocol there is no single point of failure in the network and hosts can join and leave the the ring at any time. This was the scheme used in [1] and it worked well in the context of shared Ethernet segments, where all hosts can communicate with each other directly. In the context ...
Introducing Network Standards
... Adapter Driver: Controls network interface hardware; works in MAC sublayer and moves frames between protocol stack and interface hardware Protocol Manager: Controls activity between protocol stack and MAC ...
... Adapter Driver: Controls network interface hardware; works in MAC sublayer and moves frames between protocol stack and interface hardware Protocol Manager: Controls activity between protocol stack and MAC ...
Cross-layer Design for Wireless Networks
... allocate this bandwidth in a dynamic manner among various data users. For instance, time could be divided into fixed size time-slots and users could be allocated time-slots in a dynamic manner. The simplest scheduling algorithm is the round robin mechanism, where users are periodically allocated slo ...
... allocate this bandwidth in a dynamic manner among various data users. For instance, time could be divided into fixed size time-slots and users could be allocated time-slots in a dynamic manner. The simplest scheduling algorithm is the round robin mechanism, where users are periodically allocated slo ...
CAN1102-2009-10-S1-exampaper
... The IEEE 802 series of standards describe both the Physical and Data Link layers of their respective technologies. Two important standards are 802.3 and 802.5, respectively known as CSMA/CD (Ethernet) and Token Ring. i. Explain how CSMA/CD operates and describe how Ethernet deals with ...
... The IEEE 802 series of standards describe both the Physical and Data Link layers of their respective technologies. Two important standards are 802.3 and 802.5, respectively known as CSMA/CD (Ethernet) and Token Ring. i. Explain how CSMA/CD operates and describe how Ethernet deals with ...
Cybrotech software tools
... in a running network, not affecting other modules. CyBro may also be connected and running. IEX Loader opens hex files only, binary files are not supported. Sending new program (or new NAD) will also set serial number, if the present value is not valid (zero for new devices, FFxxxxxx for older devic ...
... in a running network, not affecting other modules. CyBro may also be connected and running. IEX Loader opens hex files only, binary files are not supported. Sending new program (or new NAD) will also set serial number, if the present value is not valid (zero for new devices, FFxxxxxx for older devic ...
Networking concepts and hardware
... 48-bit unique addresses hard wired in NICs (280 trillion) 12 hex numbers, e.g. 00-A0-C9-9F-00-07 first three identify company, Intel in the example how to see: IPconfig, or System Information ...
... 48-bit unique addresses hard wired in NICs (280 trillion) 12 hex numbers, e.g. 00-A0-C9-9F-00-07 first three identify company, Intel in the example how to see: IPconfig, or System Information ...
Solution: Virtual Private Network (VPN)
... • The driving force for VPN is the requirement to make more secure information communication and to decrease the communication cost • IPSec is the mostly used protocols for VPN ...
... • The driving force for VPN is the requirement to make more secure information communication and to decrease the communication cost • IPSec is the mostly used protocols for VPN ...
Acadia - IT, Sligo
... With 4 CAT5 cables in every data termination point in the rooms, extra computers or other devices can be used in the classrooms as needed ACLs provide very strong security : students in the curriculum network cannot get into administrator network Use of VLAN’s provide internal security Troubleshooti ...
... With 4 CAT5 cables in every data termination point in the rooms, extra computers or other devices can be used in the classrooms as needed ACLs provide very strong security : students in the curriculum network cannot get into administrator network Use of VLAN’s provide internal security Troubleshooti ...
Suraj September 14, 2013 The Genius Hour: Day 1/2 Hackers: a
... Packet sniffer: is an application that captures data packets, whi0.ch can be used to capture passwords and other data in transit over the network. Spoofing Attack: a spoofing attack involves one program, system, or website successfully masquerading as another by falsifying data and thereby being tre ...
... Packet sniffer: is an application that captures data packets, whi0.ch can be used to capture passwords and other data in transit over the network. Spoofing Attack: a spoofing attack involves one program, system, or website successfully masquerading as another by falsifying data and thereby being tre ...
Document
... • Mobility: Allows locating them in the best place for receiving a more powerful signal. • May be used in any host. Only a USB port is needed. • If it is neccessary, they may pass from a host to another (only driver installation is needed) Disadvantages • Much more unstable than Wi-Fi PCI Cards. • ...
... • Mobility: Allows locating them in the best place for receiving a more powerful signal. • May be used in any host. Only a USB port is needed. • If it is neccessary, they may pass from a host to another (only driver installation is needed) Disadvantages • Much more unstable than Wi-Fi PCI Cards. • ...
Chap 3
... The primary purpose of DoS attacks is to steal vital information. (T/F) Name three types of DoS attack. The ping of death works based on using very large ICMP packets that must be fragmented to send and when reassembled are too large for the receiver’s buffer. (T/F) How can a router stop packets fro ...
... The primary purpose of DoS attacks is to steal vital information. (T/F) Name three types of DoS attack. The ping of death works based on using very large ICMP packets that must be fragmented to send and when reassembled are too large for the receiver’s buffer. (T/F) How can a router stop packets fro ...
Doc
... Duties Included: Support users in HQ as well as worldwide. Build\patch and maintain stable operating environment with a variety of applications. Backup Tape Management using Veritas and Amanda. Telecomm Installation, management and administration. Network Security, WAN & LAN management. Designed and ...
... Duties Included: Support users in HQ as well as worldwide. Build\patch and maintain stable operating environment with a variety of applications. Backup Tape Management using Veritas and Amanda. Telecomm Installation, management and administration. Network Security, WAN & LAN management. Designed and ...
Securing the infrastructure-international reflections
... Bringing broadband to the majority of citizens Fibre offers the fastest speeds at the greatest cost (suitable for high demand users); wireless is the cheapest and fastest way to reach universal broadband coverage. Fibre Wireless > Optical fibre offers broadband connections up to 100Mb/s > Fibre is ...
... Bringing broadband to the majority of citizens Fibre offers the fastest speeds at the greatest cost (suitable for high demand users); wireless is the cheapest and fastest way to reach universal broadband coverage. Fibre Wireless > Optical fibre offers broadband connections up to 100Mb/s > Fibre is ...
Document
... Denial of Service An attack specifically designed to prevent the normal functioning of a system and thereby to prevent lawful access to the system by authorized users. Hackers can cause denial of service attacks by destroying or modifying data or by overloading the system's servers until service t ...
... Denial of Service An attack specifically designed to prevent the normal functioning of a system and thereby to prevent lawful access to the system by authorized users. Hackers can cause denial of service attacks by destroying or modifying data or by overloading the system's servers until service t ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.