MohamedAbdinurSahalMFKE2013ABS
... on the system performance in terms of delay, throughput and packet loss. The simulation tool to achieve the objectives is OPNET 14.5 Modular; we have designed two integration scenarios for Open and Loose coupling scheme and then compared that two integration schemes however result shows that loose c ...
... on the system performance in terms of delay, throughput and packet loss. The simulation tool to achieve the objectives is OPNET 14.5 Modular; we have designed two integration scenarios for Open and Loose coupling scheme and then compared that two integration schemes however result shows that loose c ...
Virtual Cyber Security Lab - Celtic-Plus
... Virtual Cyber Security Lab Uğur Çağal, Hakan Kılınç [email protected] ...
... Virtual Cyber Security Lab Uğur Çağal, Hakan Kılınç [email protected] ...
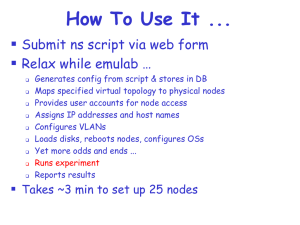
emulab.net: A Network Emulation and Distributed Systems Testbed
... Specify desired device and path properties ...
... Specify desired device and path properties ...
A Secure Intrusion - Detection System for Vulnerable Attacks in
... made it possible in many applications. Among all the contemporary wireless networks, Mobile Ad hoc Network (MANET) is one of the most important and unique applications. On the contrary to traditional network architecture, MANET does not require a fixed network infrastructure; every single node works ...
... made it possible in many applications. Among all the contemporary wireless networks, Mobile Ad hoc Network (MANET) is one of the most important and unique applications. On the contrary to traditional network architecture, MANET does not require a fixed network infrastructure; every single node works ...
Presentation Title Presentation Title Presentation Title
... • Predominant standards commonly used in WSN communications include: • WirelessHART (The wireless standard for process automation) • ISA100 (WirelessHART and ISA100.11a convered in a recent Control Engineering article • IEEE 1451 (IEEE 1451 is a set of Smart transducer interface standards developed ...
... • Predominant standards commonly used in WSN communications include: • WirelessHART (The wireless standard for process automation) • ISA100 (WirelessHART and ISA100.11a convered in a recent Control Engineering article • IEEE 1451 (IEEE 1451 is a set of Smart transducer interface standards developed ...
Information Security
... Using specialized VPN devices or built-in into a firewall If both your sites have Internet connectivity, they can be connected using VPN ...
... Using specialized VPN devices or built-in into a firewall If both your sites have Internet connectivity, they can be connected using VPN ...
Wireless Mesh Network (WMN)
... – size vs. performance, routing protocol • 802.11 share BW – multiple access techniques • TDMA – synchronization • CDMA - code control • CSMA/CA ...
... – size vs. performance, routing protocol • 802.11 share BW – multiple access techniques • TDMA – synchronization • CDMA - code control • CSMA/CA ...
EMBEDDED COMPUTATION MEETS THE WORLD WIDE WEB
... • Lookup service: When a device plugs in, it goes through an add-in protocol. (1) Discovery - The device first locates the lookup service (2) join-in - then uploads an object that implements all of its services' interfaces ...
... • Lookup service: When a device plugs in, it goes through an add-in protocol. (1) Discovery - The device first locates the lookup service (2) join-in - then uploads an object that implements all of its services' interfaces ...
Wi-Fi security
... STA can inject “extra” frames simply by transmitting them – Frames are not signed, so nothing prevents attackers from “borrowing” MAC address of legitimate STA ...
... STA can inject “extra” frames simply by transmitting them – Frames are not signed, so nothing prevents attackers from “borrowing” MAC address of legitimate STA ...
IEEE 802.11 Wireless LAN Draft Standard
... • The IEEE 802.16 standards family - broadband wireless wideband internet connection - wider coverage than any wired or wireless connection before • Wireless system have the capacity to address broad geographic areas without the expensive wired infrastructure • For example, a study made in Universit ...
... • The IEEE 802.16 standards family - broadband wireless wideband internet connection - wider coverage than any wired or wireless connection before • Wireless system have the capacity to address broad geographic areas without the expensive wired infrastructure • For example, a study made in Universit ...
Phoenix SIEM (Security Information and Event
... Director and CTO at Kenindus Limited . Holds a Bachelor of Science degree in Computer Information Management from Life University in Atlanta, Georgia and a Masters in Small Business and Entrepreneurship from Plymouth State in Plymouth, New Hampshire. I have more than 10 years experience in cyber sec ...
... Director and CTO at Kenindus Limited . Holds a Bachelor of Science degree in Computer Information Management from Life University in Atlanta, Georgia and a Masters in Small Business and Entrepreneurship from Plymouth State in Plymouth, New Hampshire. I have more than 10 years experience in cyber sec ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... software architecture of the player system, and discusses the design in detail. Today’s projector are connected to any device like computer, laptop, etc. using HDMI cable. So it becomes difficult to connect or project data from a device at a distance more than the length of HDMI cable. And it is als ...
... software architecture of the player system, and discusses the design in detail. Today’s projector are connected to any device like computer, laptop, etc. using HDMI cable. So it becomes difficult to connect or project data from a device at a distance more than the length of HDMI cable. And it is als ...
Information Security and its Implications on Everyday
... Technology isn’t perfect Probably won’t change significantly for the next 10 years E-crime on the rise “Genuine, widespread awareness of information security issues is the only practical way to counter attacks targeting computer users” http://www.noticebored.com/ It’s not easy, but a lot can be done ...
... Technology isn’t perfect Probably won’t change significantly for the next 10 years E-crime on the rise “Genuine, widespread awareness of information security issues is the only practical way to counter attacks targeting computer users” http://www.noticebored.com/ It’s not easy, but a lot can be done ...
Intrusion Detection
... information and systems. To address this challenge, SwRI enforces a configurable high-level security policy by automatically enhancing software applications through a complementary combination of static and dynamic data flow analysis. This approach enables precise, relevant and scalable tracking of ...
... information and systems. To address this challenge, SwRI enforces a configurable high-level security policy by automatically enhancing software applications through a complementary combination of static and dynamic data flow analysis. This approach enables precise, relevant and scalable tracking of ...
Wireless Broadband Router
... A high-end CPU (capable of processing as much as 80 times the throughput as earlier-generation broadband routers) makes it possible for the Wireless Broadband Router to handle multiple high-throughput media streams simultaneously, including standard and HDTVbased video programming. Networks can be s ...
... A high-end CPU (capable of processing as much as 80 times the throughput as earlier-generation broadband routers) makes it possible for the Wireless Broadband Router to handle multiple high-throughput media streams simultaneously, including standard and HDTVbased video programming. Networks can be s ...
Cell tower solutions for tier 2 service providers
... Term Evolution (LTE) services provide greater bandwidth for mobile devices and will compete with residential broadband services. The 4G LTE high-speed data technology is driving cell sites from traditional DS1 copper to fiber-optic Ethernet based transport. For these reasons, there is a growing busi ...
... Term Evolution (LTE) services provide greater bandwidth for mobile devices and will compete with residential broadband services. The 4G LTE high-speed data technology is driving cell sites from traditional DS1 copper to fiber-optic Ethernet based transport. For these reasons, there is a growing busi ...
Screened-host firewall
... The DMZ acts as a small isolated network for an organization’s public servers, bastion host information servers and modem pools. key benefits are – intruder must penetrate 3 separate devices and private network addresses are not disclosed to the internet plus internal systems do not have direct acce ...
... The DMZ acts as a small isolated network for an organization’s public servers, bastion host information servers and modem pools. key benefits are – intruder must penetrate 3 separate devices and private network addresses are not disclosed to the internet plus internal systems do not have direct acce ...
Wireless Local Area Networks
... Works in ISM band, share same frequency with microwave oven, Bluetooth, and others Security Current WEP algorithm is weak - usually not ON! Roaming No industry standard is available and propriety solution are not interoperable - especially with GSM Inter-operability Only few basic functional ...
... Works in ISM band, share same frequency with microwave oven, Bluetooth, and others Security Current WEP algorithm is weak - usually not ON! Roaming No industry standard is available and propriety solution are not interoperable - especially with GSM Inter-operability Only few basic functional ...
Gigamon - ForeScout
... platform lets you see and control what is connected to your network no matter the user or device. ForeScout’s real-time endpoint classification, policy assessment and threat remediation capabilities offer the means for organizations to apply strong access control policies, as well as find and fix en ...
... platform lets you see and control what is connected to your network no matter the user or device. ForeScout’s real-time endpoint classification, policy assessment and threat remediation capabilities offer the means for organizations to apply strong access control policies, as well as find and fix en ...
LGfL Tech Conference 2014P_V2
... How much of it you use is a choice… Sign in to Google services using LGfL USO Use automatically-created and managed accounts via most popular web browsers ...
... How much of it you use is a choice… Sign in to Google services using LGfL USO Use automatically-created and managed accounts via most popular web browsers ...
Security Tools
... Features tools for : • Ping - Click to Enlarge Ping - Use Ping to determine if a network device is reachable. • Traceroute - Use traceroute to trace the path to a network host or device. • Throughput - Click to Enlarge Throughput - Use Throughput to test the data speed on a connection with a remote ...
... Features tools for : • Ping - Click to Enlarge Ping - Use Ping to determine if a network device is reachable. • Traceroute - Use traceroute to trace the path to a network host or device. • Throughput - Click to Enlarge Throughput - Use Throughput to test the data speed on a connection with a remote ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.