Lecture 2
... • Several APs in a single area may be connected to a single hub or switch or they can use virtual LAN if the link=layer connection APs act as bridges APs are configured to be part of the ESS ...
... • Several APs in a single area may be connected to a single hub or switch or they can use virtual LAN if the link=layer connection APs act as bridges APs are configured to be part of the ESS ...
Interoperability Standards
... • Wildly successful because of ease of deployment, price • Moving to OFDM/MIMO (802.11n) ...
... • Wildly successful because of ease of deployment, price • Moving to OFDM/MIMO (802.11n) ...
Workstar iGuard
... records easily, thus cutting the processing time for jobs like payroll calculation from days to minutes. All the information is real-time information, instead of week-old or day-old data. In contrast, other systems must use dedicated computers running special proprietary software to retrieve the inf ...
... records easily, thus cutting the processing time for jobs like payroll calculation from days to minutes. All the information is real-time information, instead of week-old or day-old data. In contrast, other systems must use dedicated computers running special proprietary software to retrieve the inf ...
How to setup WPA Security with the Conceptronic C54APT Access...
... which it is connected to; it does pass on the data transparent. For configuring purposes you will have to have TCP/IP settings that match the TCP/IP settings of the Access Point 1. Change the settings of your network adapter to match the settings of the Access Point Go to Start .…. Control Panel ….. ...
... which it is connected to; it does pass on the data transparent. For configuring purposes you will have to have TCP/IP settings that match the TCP/IP settings of the Access Point 1. Change the settings of your network adapter to match the settings of the Access Point Go to Start .…. Control Panel ….. ...
SAQ D Compliance Scott St. Aubin Senior Security Consultant QSA, CISM, CISSP
... • Process to identify newly discovered vulnerabilities AND update configuration standards • Change control process – Document impact – Management sign-off – Testing of operational funcationality – Back-out procedures ...
... • Process to identify newly discovered vulnerabilities AND update configuration standards • Change control process – Document impact – Management sign-off – Testing of operational funcationality – Back-out procedures ...
Operating System Security Fundamentals
... Public Key Infrastructures (PKI): User keeps a private key Authentication firm holds a public key Encrypt and decrypt data using both keys ...
... Public Key Infrastructures (PKI): User keeps a private key Authentication firm holds a public key Encrypt and decrypt data using both keys ...
IT Security Policy
... (DMZ) separate from the internal District network. Segmentation may be achieved via firewall, router, virtual local area network (VLAN), or similar network access control device which does not allow internet traffic to access any internal system without first passing through a DMZ or network device ...
... (DMZ) separate from the internal District network. Segmentation may be achieved via firewall, router, virtual local area network (VLAN), or similar network access control device which does not allow internet traffic to access any internal system without first passing through a DMZ or network device ...
Advanced Computer Networks
... Wireless Networks and Mobile IP: Infrastructure of Wireless Networks, Wireless LAN Technologies. IEK1: S02.11 Wireless Standard, Cellular Networks, Mobile IP, Wireless Mesh Networks (WMNs) - Optical Networks and WDM Systems: Overview of Optical Networks, Basic Optical Networking Devices, Large-Scale ...
... Wireless Networks and Mobile IP: Infrastructure of Wireless Networks, Wireless LAN Technologies. IEK1: S02.11 Wireless Standard, Cellular Networks, Mobile IP, Wireless Mesh Networks (WMNs) - Optical Networks and WDM Systems: Overview of Optical Networks, Basic Optical Networking Devices, Large-Scale ...
ppt
... Multiple types of service Variety of networks Management of resources Cost-effective Low entry-cost Accountability for resources Where is security? ...
... Multiple types of service Variety of networks Management of resources Cost-effective Low entry-cost Accountability for resources Where is security? ...
Detection of Vampire Attack in Wireless Adhoc Network
... Abstract: Mobile ad-hoc network is an infrastructure-less network in which the routing operation play important role in route discovery between communicating nodes. Due to infrastructure-less characteristic of ad-hoc network, it has different issues like routing, MAC layer, security etc. One of them ...
... Abstract: Mobile ad-hoc network is an infrastructure-less network in which the routing operation play important role in route discovery between communicating nodes. Due to infrastructure-less characteristic of ad-hoc network, it has different issues like routing, MAC layer, security etc. One of them ...
Understanding Network Technology
... The course is delivered online via the SCTE virtual classroom over 16 weeks or 4 months, during which participants view web based course materials and complete assessments (quizzes) at a time that is convenient for them. Participants can contact the instructor when they have questions. Participants ...
... The course is delivered online via the SCTE virtual classroom over 16 weeks or 4 months, during which participants view web based course materials and complete assessments (quizzes) at a time that is convenient for them. Participants can contact the instructor when they have questions. Participants ...
Network Security
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
AUROREAN™ POLICY SERVER 7000 AND 3000 SERIES Data Sheet
... Server defines dialing characteristics, access rights, administrative elements, security settings, cost policies and system-wide VPN parameters. Policies are checked and updated during every VPN session, then locked down and enforced in the VPN client. Aurorean Policy Server can be securely administ ...
... Server defines dialing characteristics, access rights, administrative elements, security settings, cost policies and system-wide VPN parameters. Policies are checked and updated during every VPN session, then locked down and enforced in the VPN client. Aurorean Policy Server can be securely administ ...
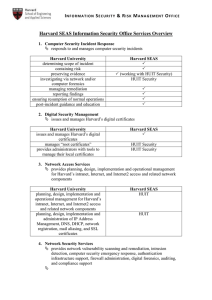
Harvard SEAS Information Security Office Services Overview
... (working with HUIT Security) HUIT Security ...
... (working with HUIT Security) HUIT Security ...
NetworkSecurity
... 3 Third generation - application layer: also known as proxy based firewalls. The key benefit is that it can "understand" certain applications and protocols (such as File Transfer Protocol, DNS or web browsing), and can detect whether an unwanted protocol is being sneaked through on a non-standard po ...
... 3 Third generation - application layer: also known as proxy based firewalls. The key benefit is that it can "understand" certain applications and protocols (such as File Transfer Protocol, DNS or web browsing), and can detect whether an unwanted protocol is being sneaked through on a non-standard po ...
Securing Distribution Automation
... CyberSecurity Coordination Task Group as one of the issues that needs to be addressed for Smart Grid security. While there exist many enterprise-level products for password management, to our knowledge there are none that have been designed to meet the requirements of distributed field devices. Typi ...
... CyberSecurity Coordination Task Group as one of the issues that needs to be addressed for Smart Grid security. While there exist many enterprise-level products for password management, to our knowledge there are none that have been designed to meet the requirements of distributed field devices. Typi ...
From DS
... Ad hoc wireless network (cont) • Nodes within an ad-hoc network can communicate if they are within each other’s radio range other nodes can forward frames ...
... Ad hoc wireless network (cont) • Nodes within an ad-hoc network can communicate if they are within each other’s radio range other nodes can forward frames ...
Unified Services Routers - D-Link
... ActiveX, and cookies, or to block URLs by keyword. Dynamic web content ...
... ActiveX, and cookies, or to block URLs by keyword. Dynamic web content ...
Teldat H1 Rail - BidNet Management
... Centralized router management through TeldaGES or third party platforms EN 50155 and other train-related certifications ...
... Centralized router management through TeldaGES or third party platforms EN 50155 and other train-related certifications ...
IEEE 802.11 architecture
... its “cell”. The channel is selected from the set that is allowed in the ...
... its “cell”. The channel is selected from the set that is allowed in the ...
TECHNOLOGY-DRIVEN METRICS
... S/W does not report system error messages directly Automated testing includes static code analyzers and automated web scanning. Configurations include application firewalls and hardened databases. Metric: An attack on the software generates a log/email within 24 hours (or less). Automated ...
... S/W does not report system error messages directly Automated testing includes static code analyzers and automated web scanning. Configurations include application firewalls and hardened databases. Metric: An attack on the software generates a log/email within 24 hours (or less). Automated ...
ws-security-framewor..
... schemes will be vital Track emerging XML security specifications Don’t throw away the organization’s existing security infrastructure Plan to implement end-to-end security ...
... schemes will be vital Track emerging XML security specifications Don’t throw away the organization’s existing security infrastructure Plan to implement end-to-end security ...
notes
... containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication [Chapter 8] will typically run DHCP to get IP address in AP’s subnet Wireless, Mobile Networks ...
... containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication [Chapter 8] will typically run DHCP to get IP address in AP’s subnet Wireless, Mobile Networks ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.